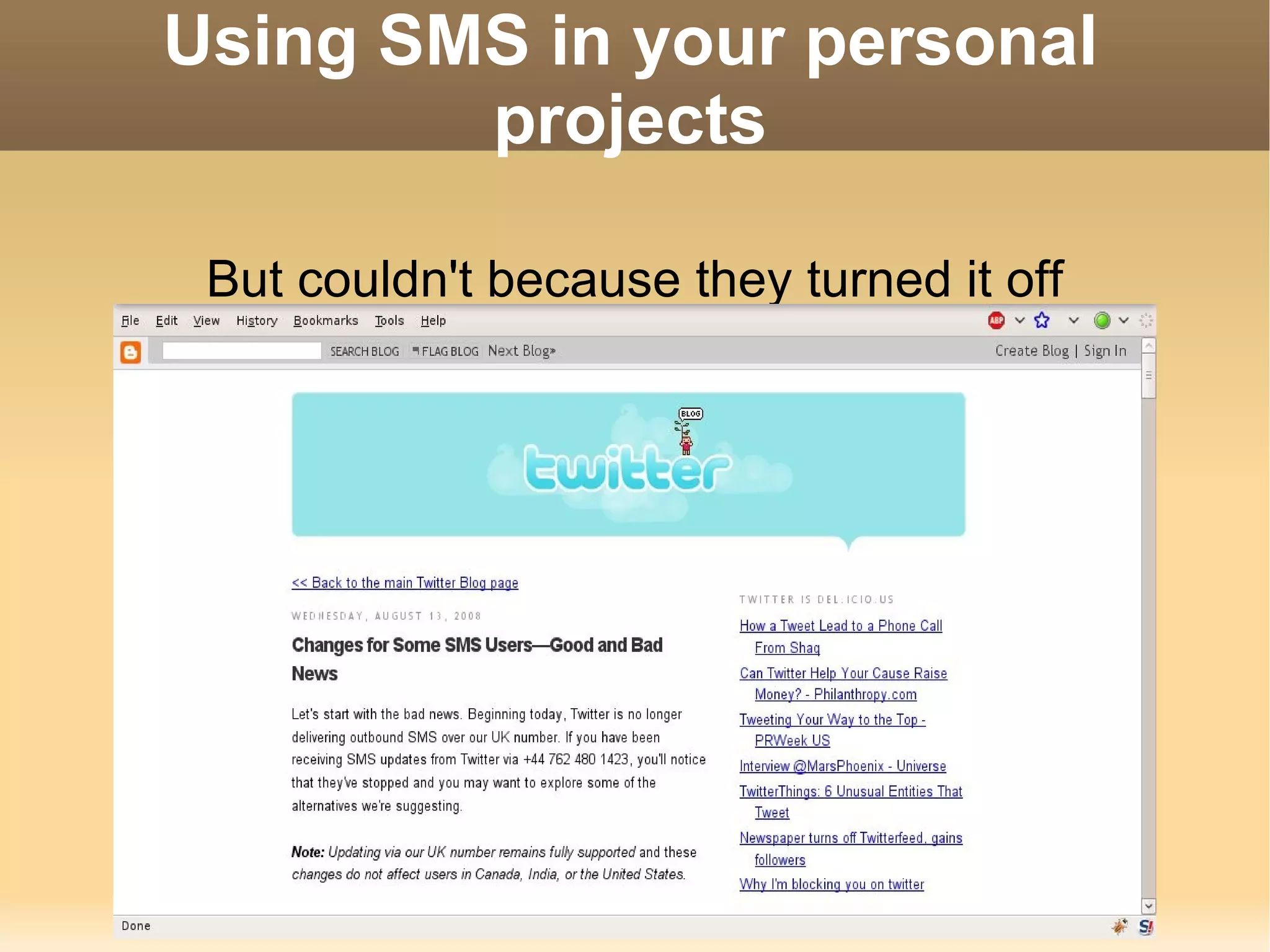
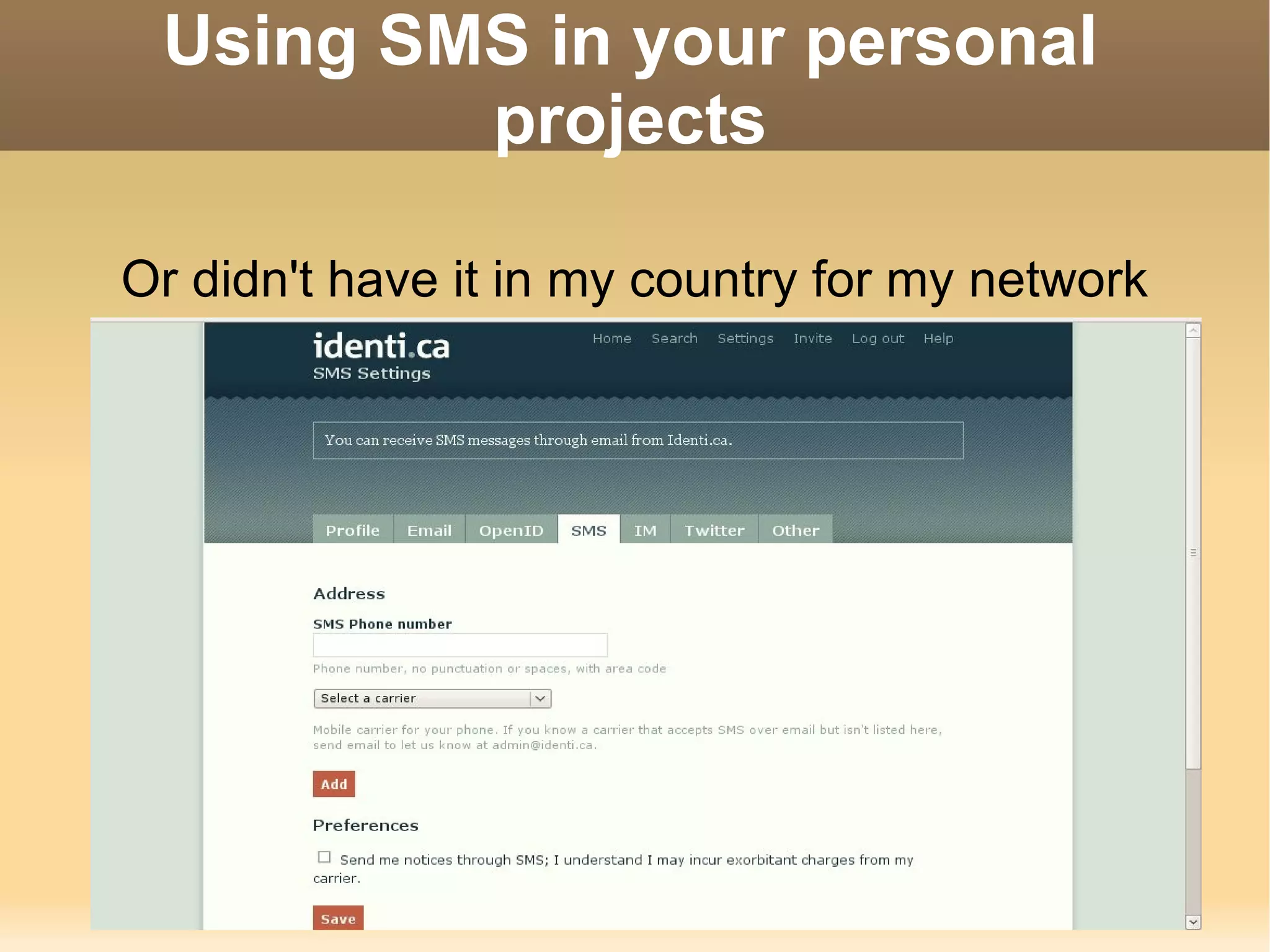
The document discusses how to integrate SMS messaging into personal projects, particularly focusing on the creation of a tool called smstolaconica for sending and receiving messages to microblogging sites. The author shares insights on using mobile phones as modems, learning SMS protocols, and implementing the code within PHP scripts. The source code is available on SourceForge, and the necessary hardware and software requirements are provided.