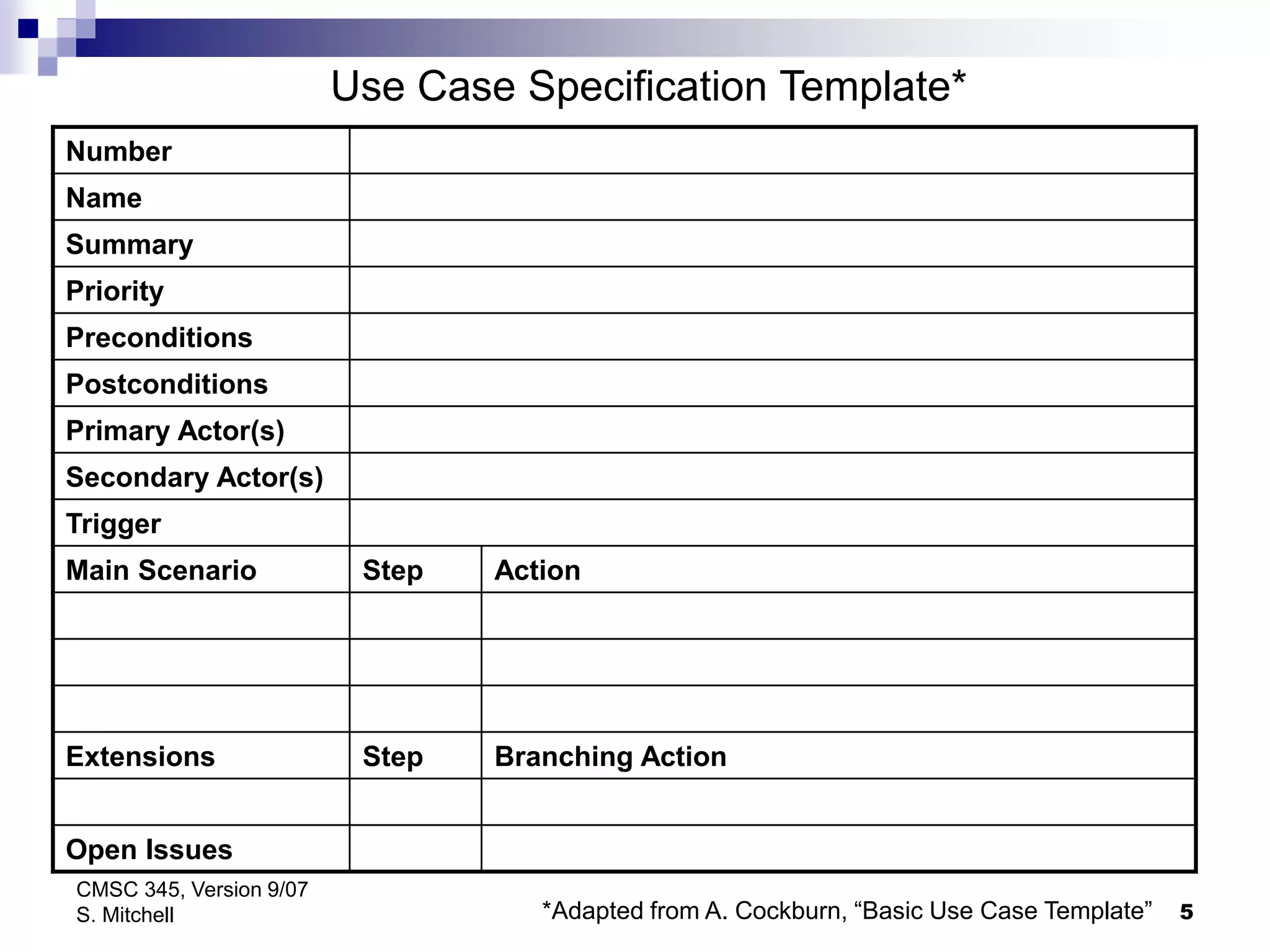
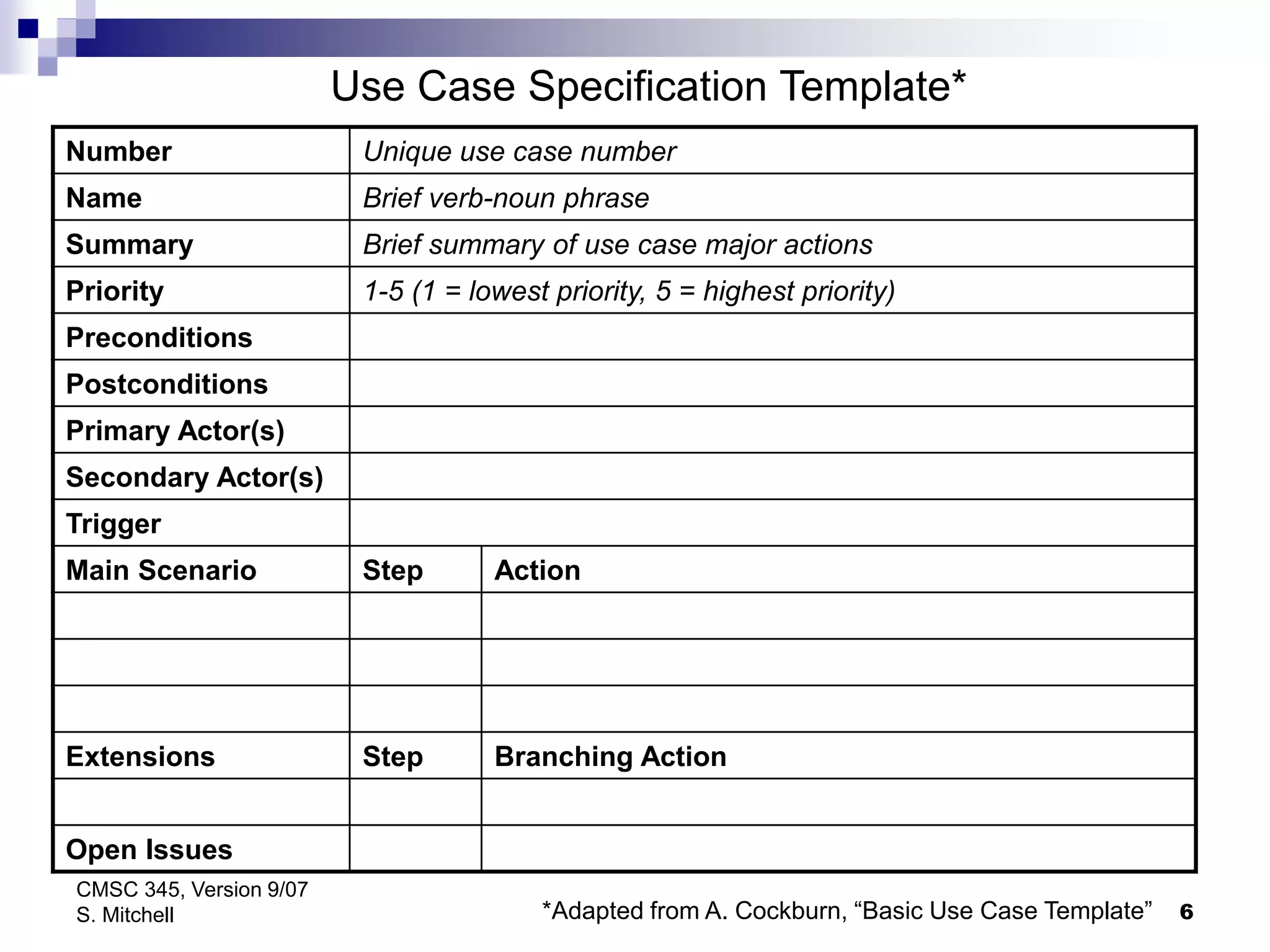
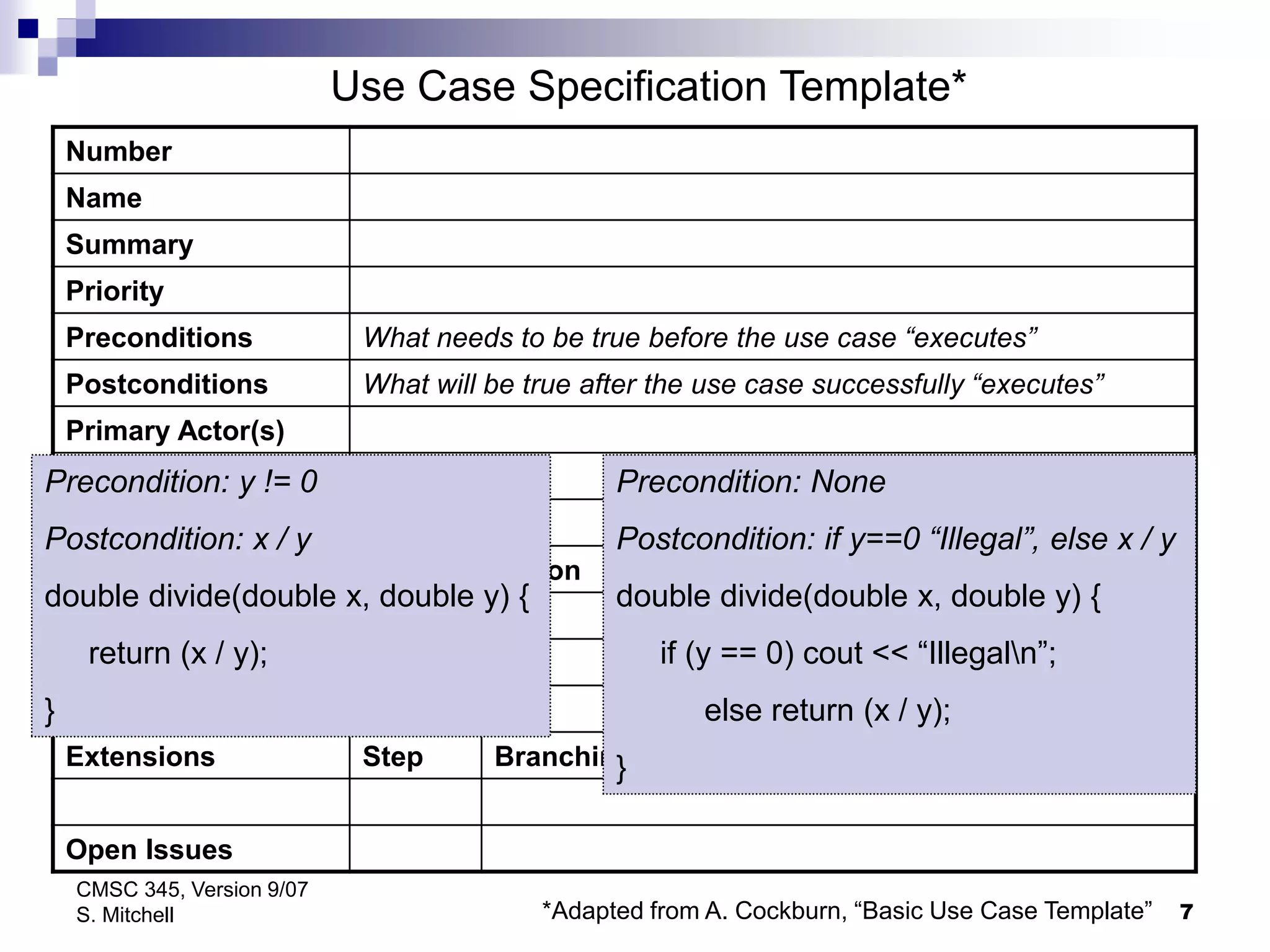
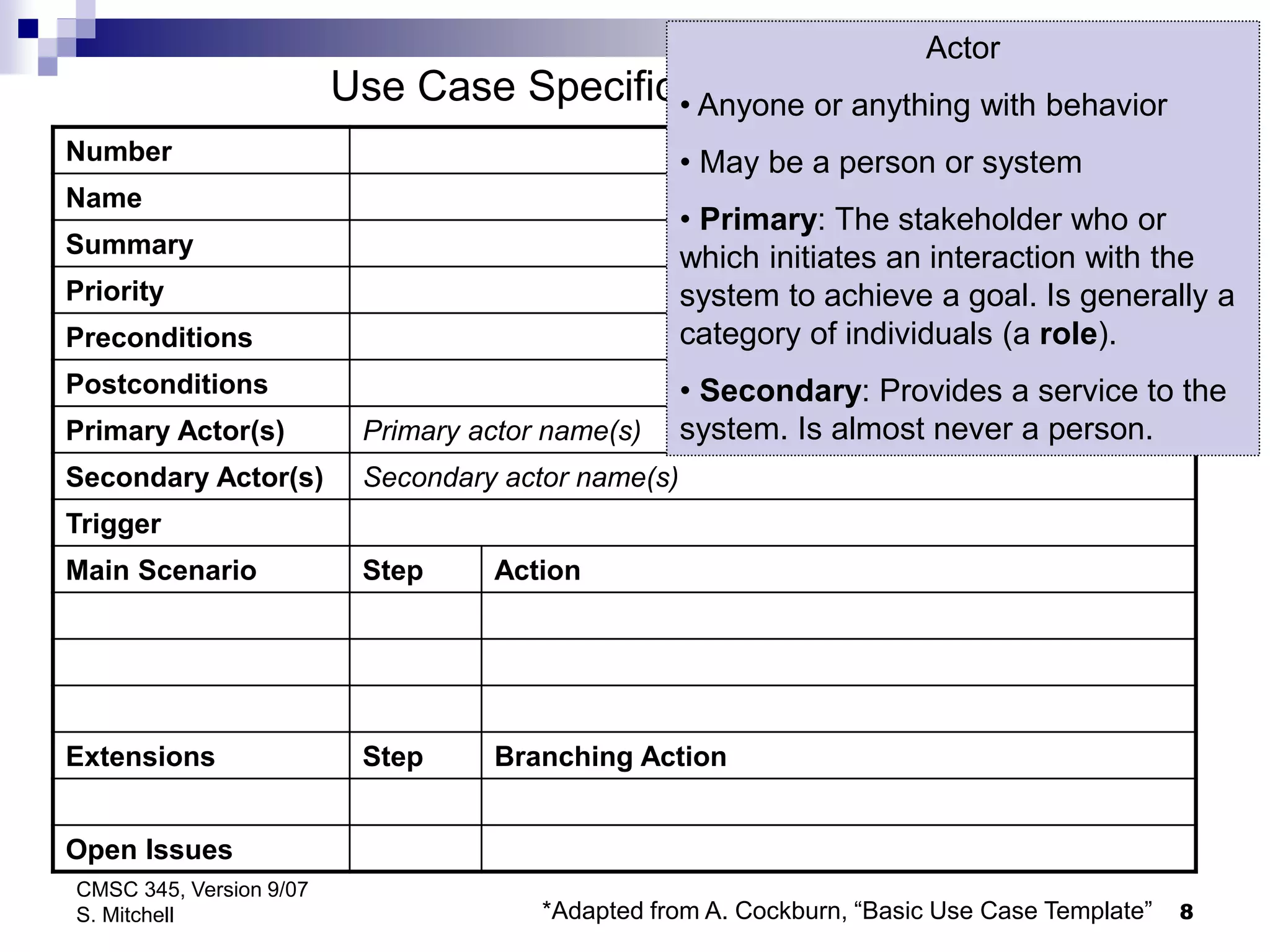
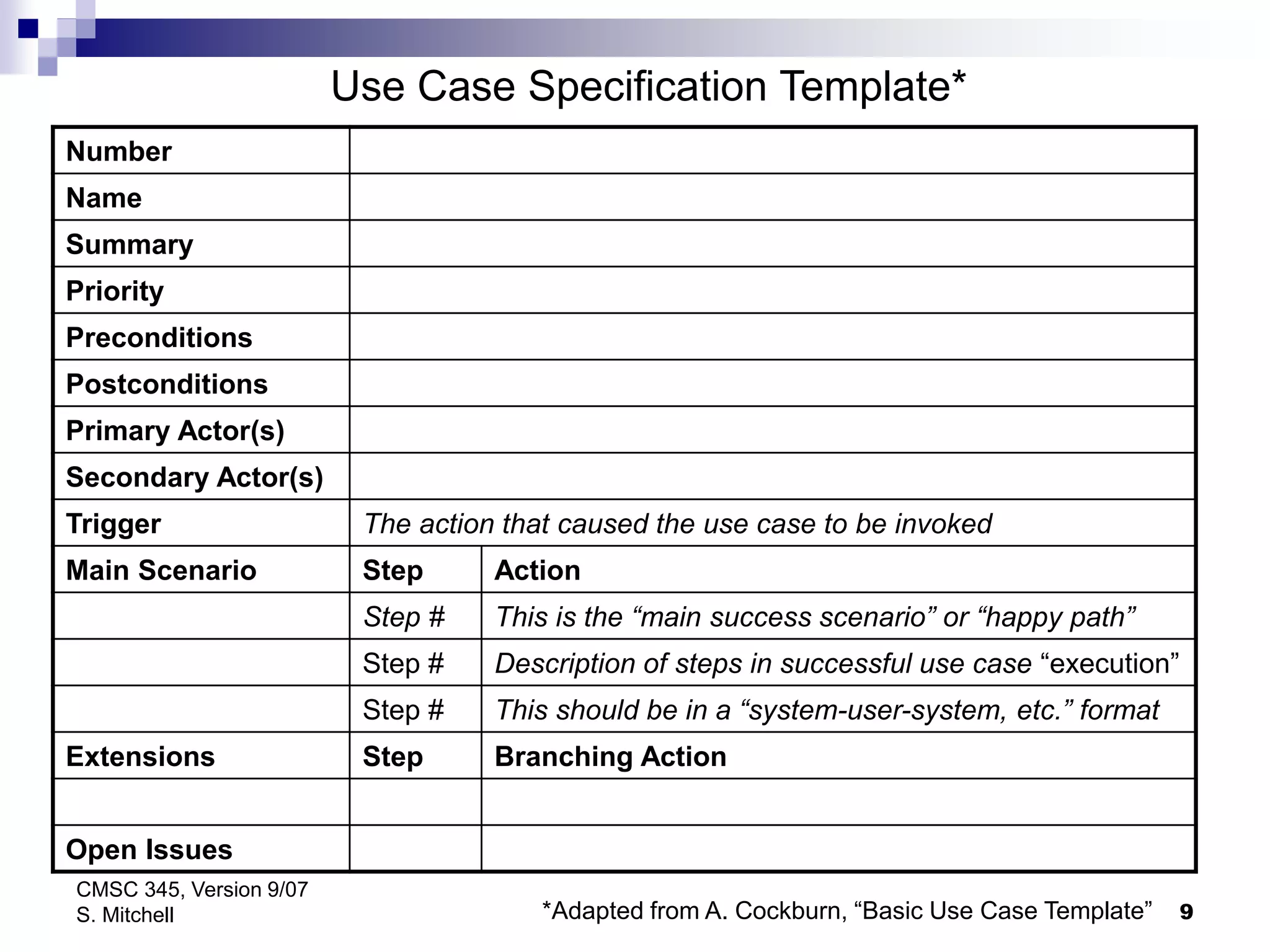
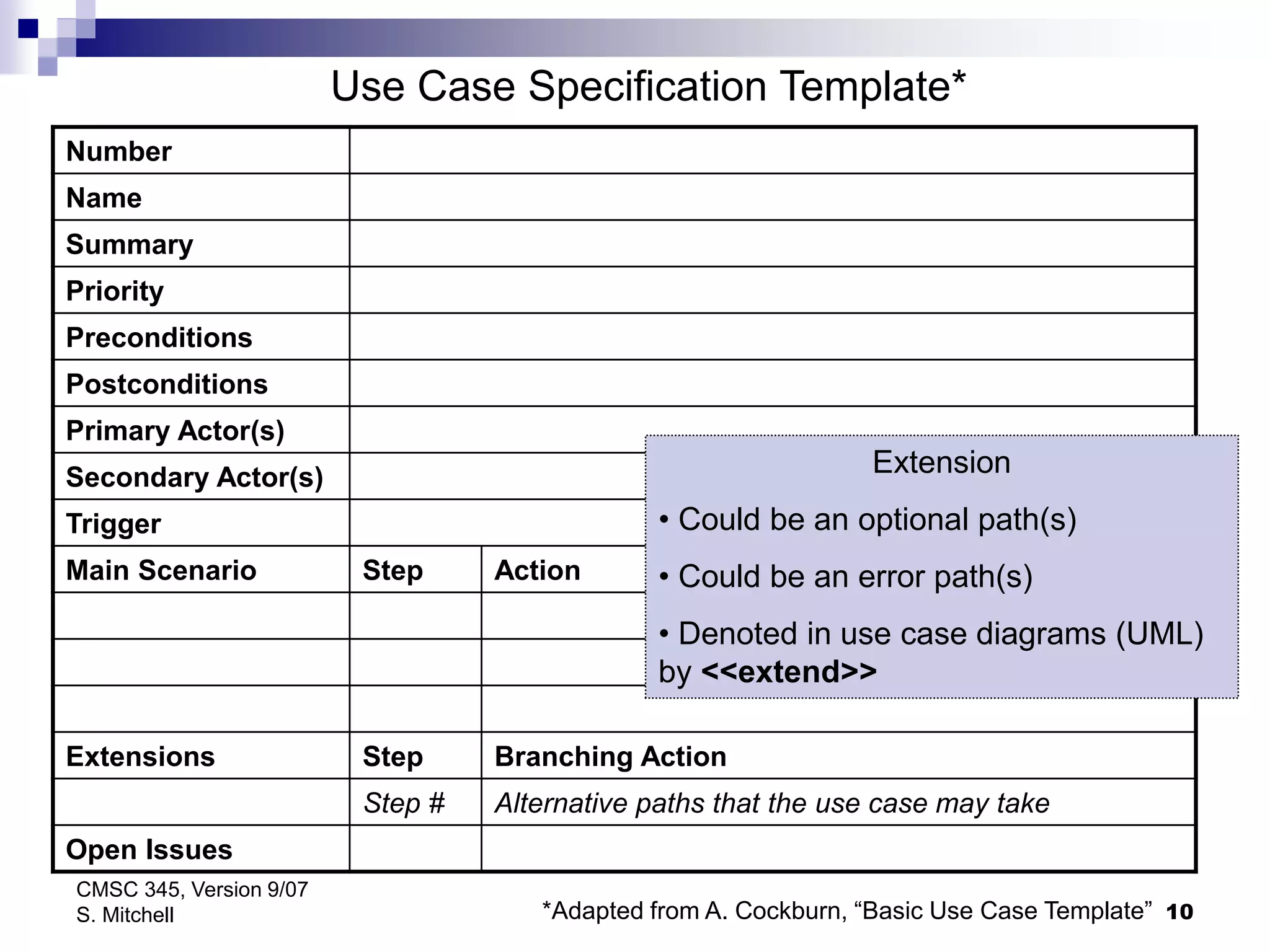
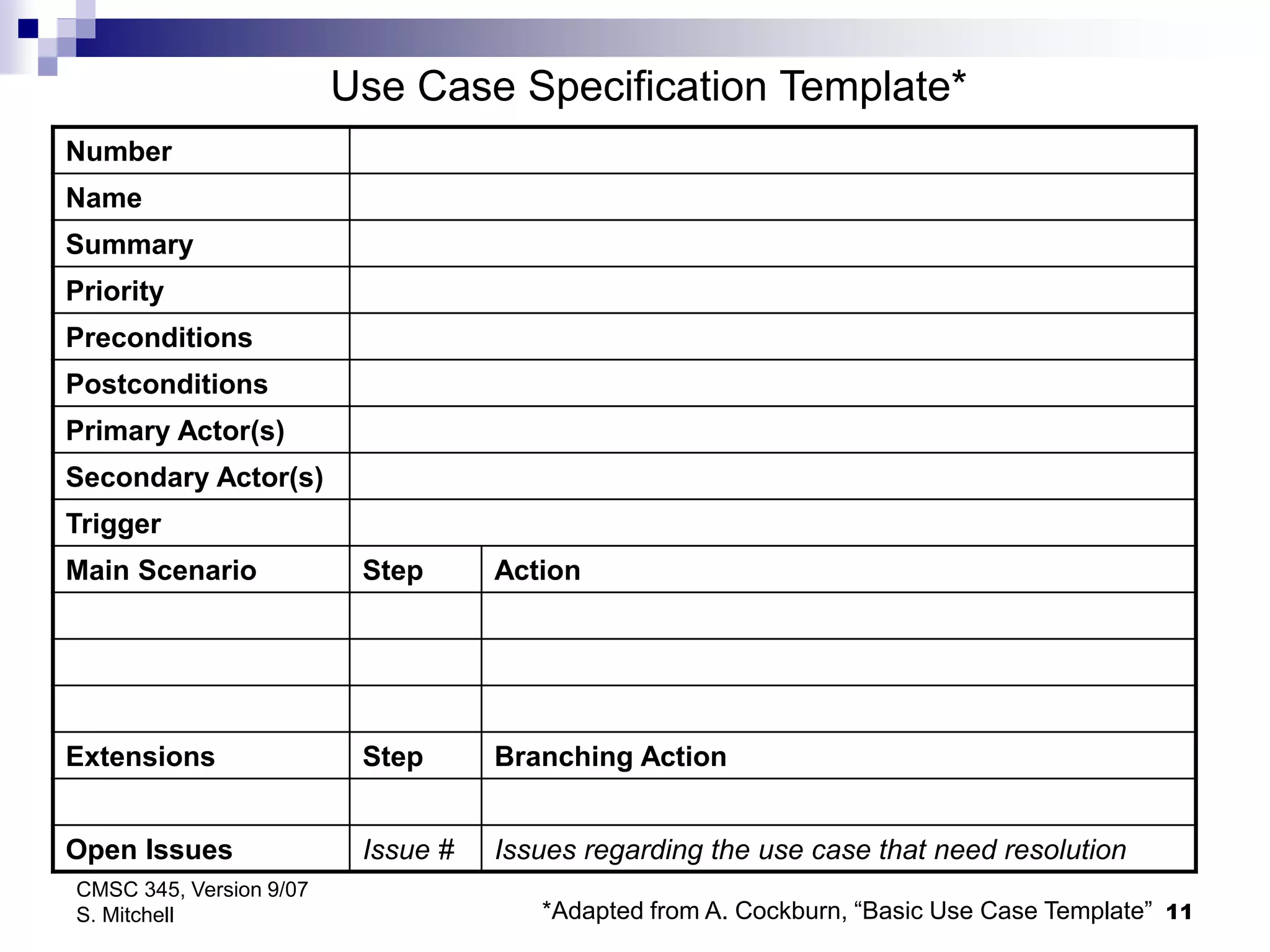
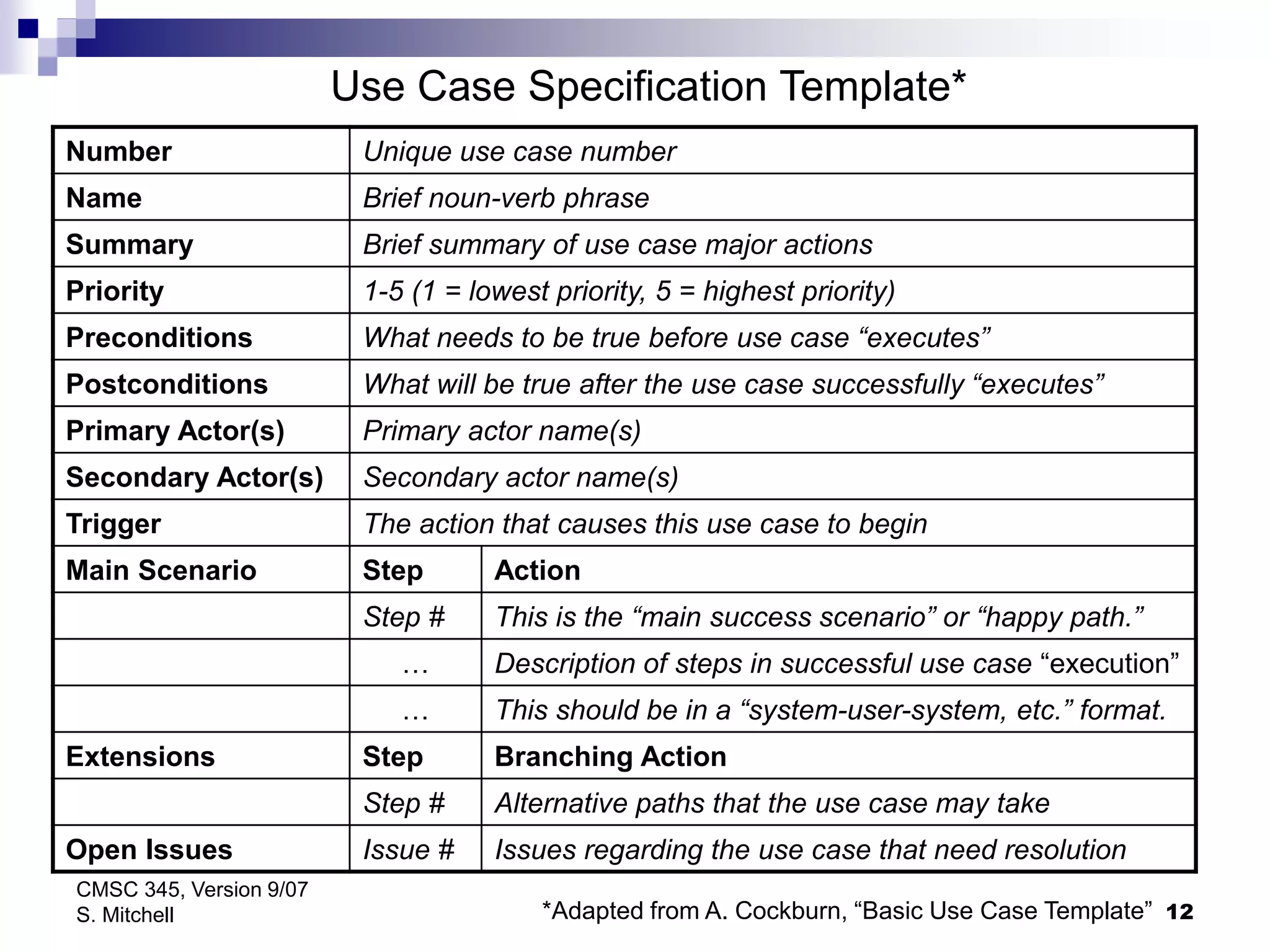
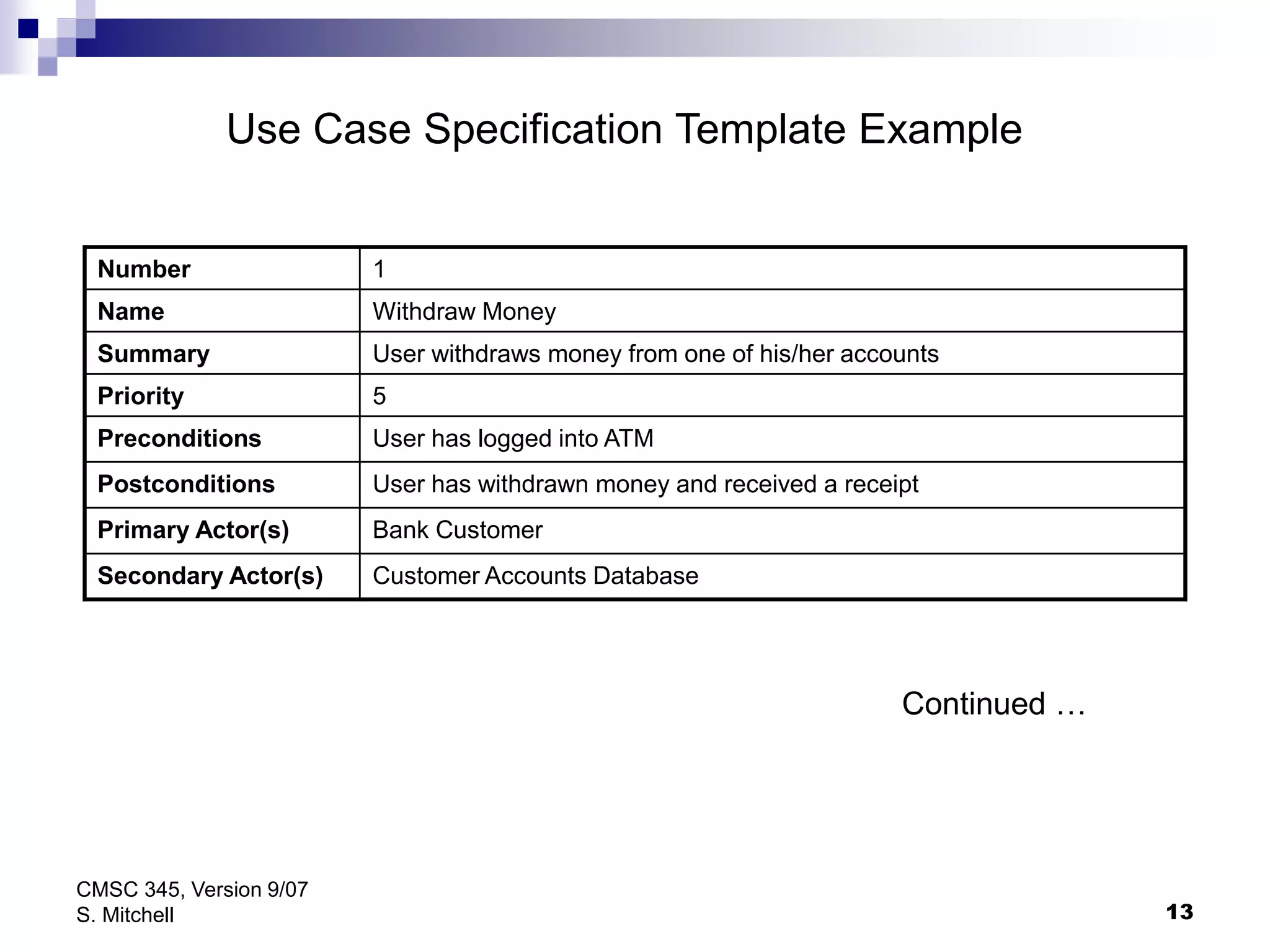
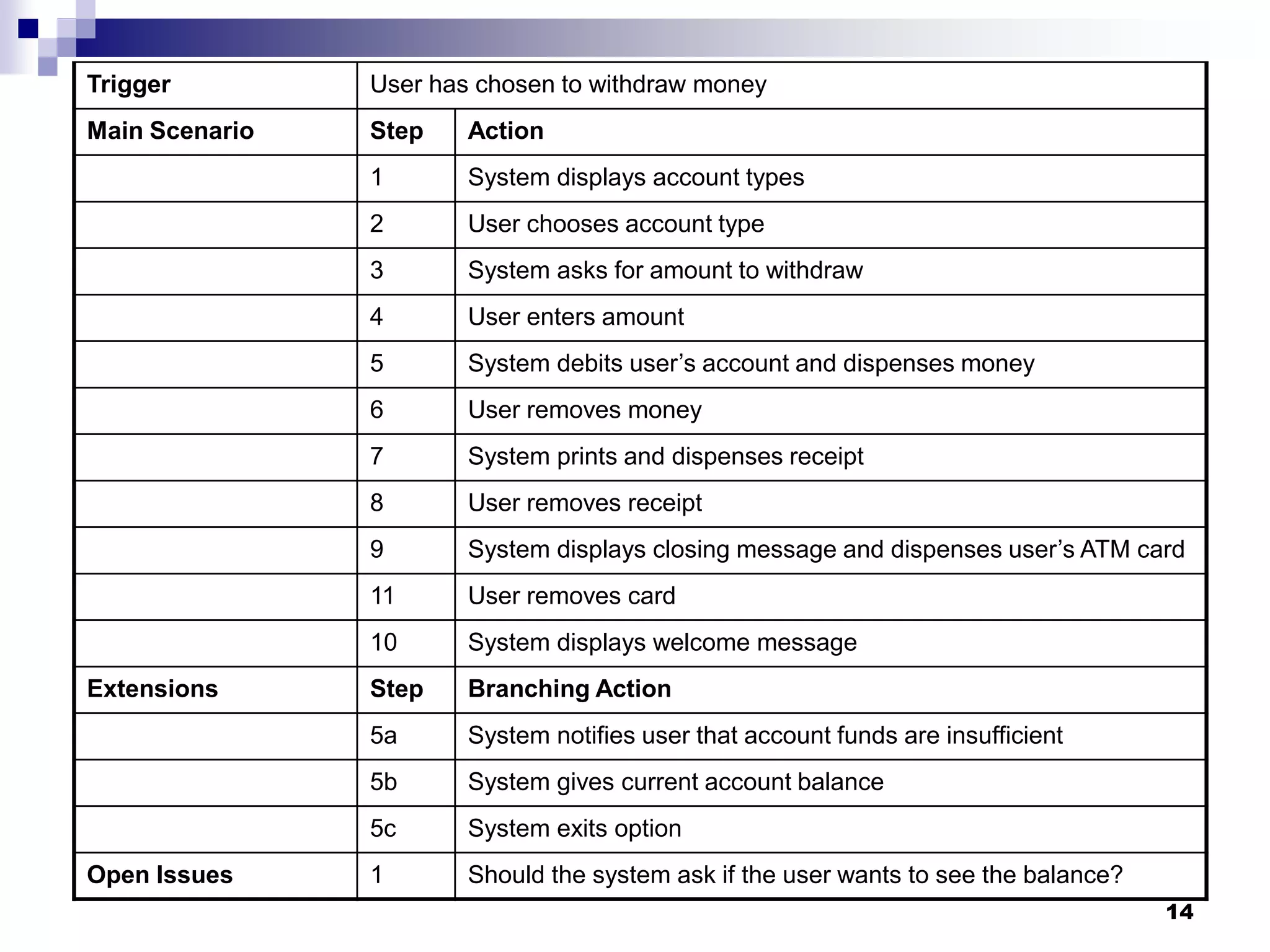
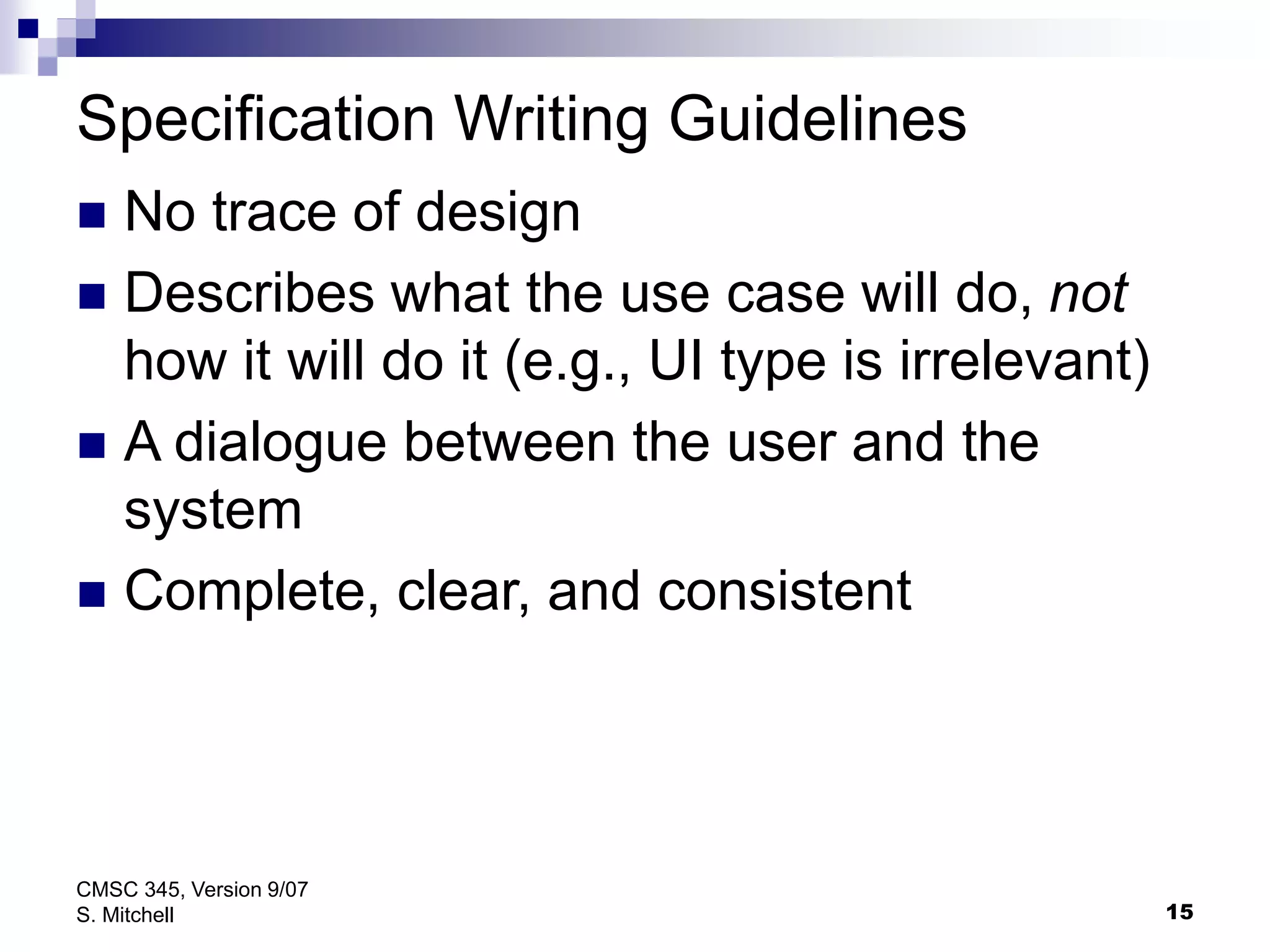
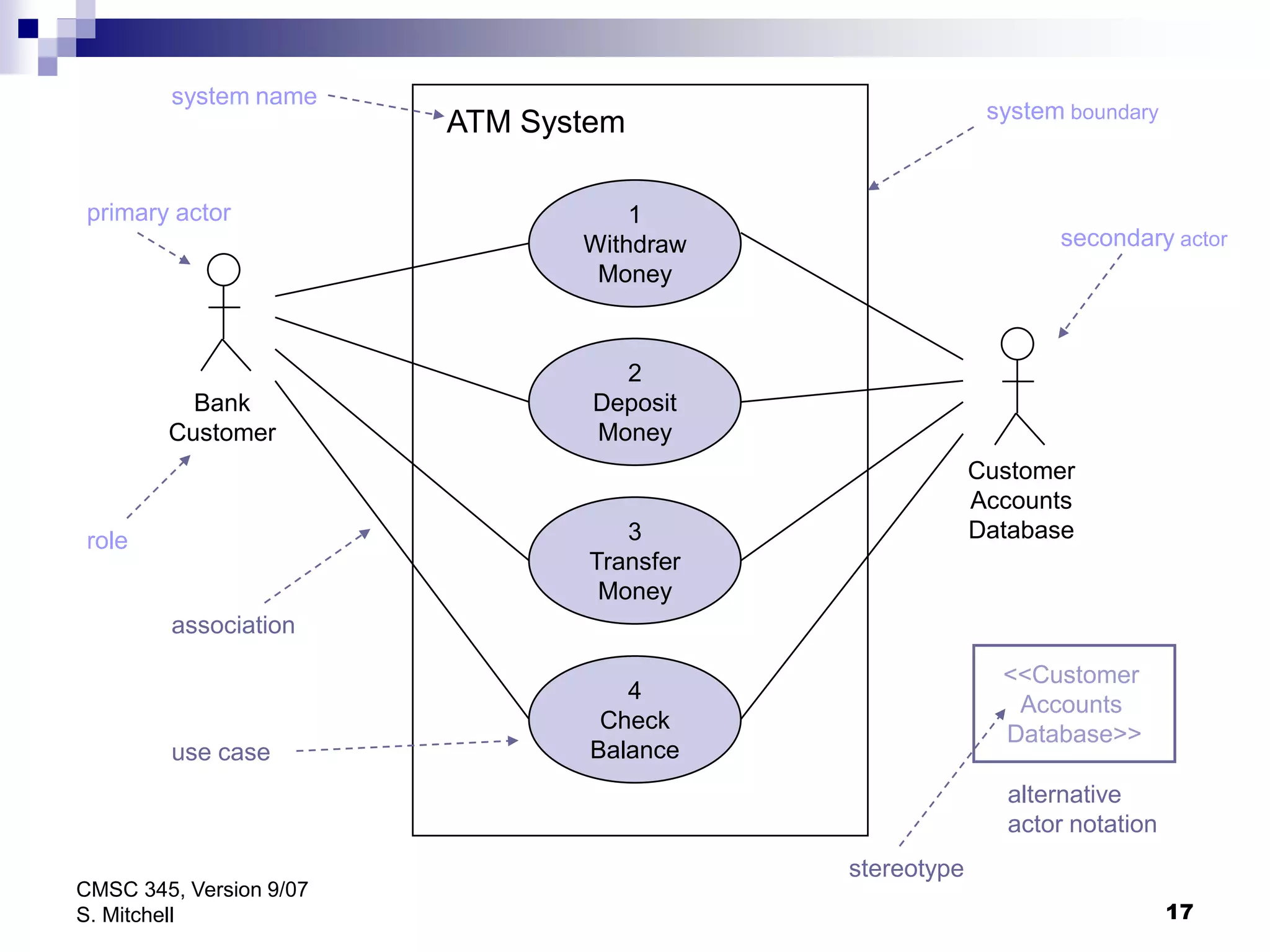
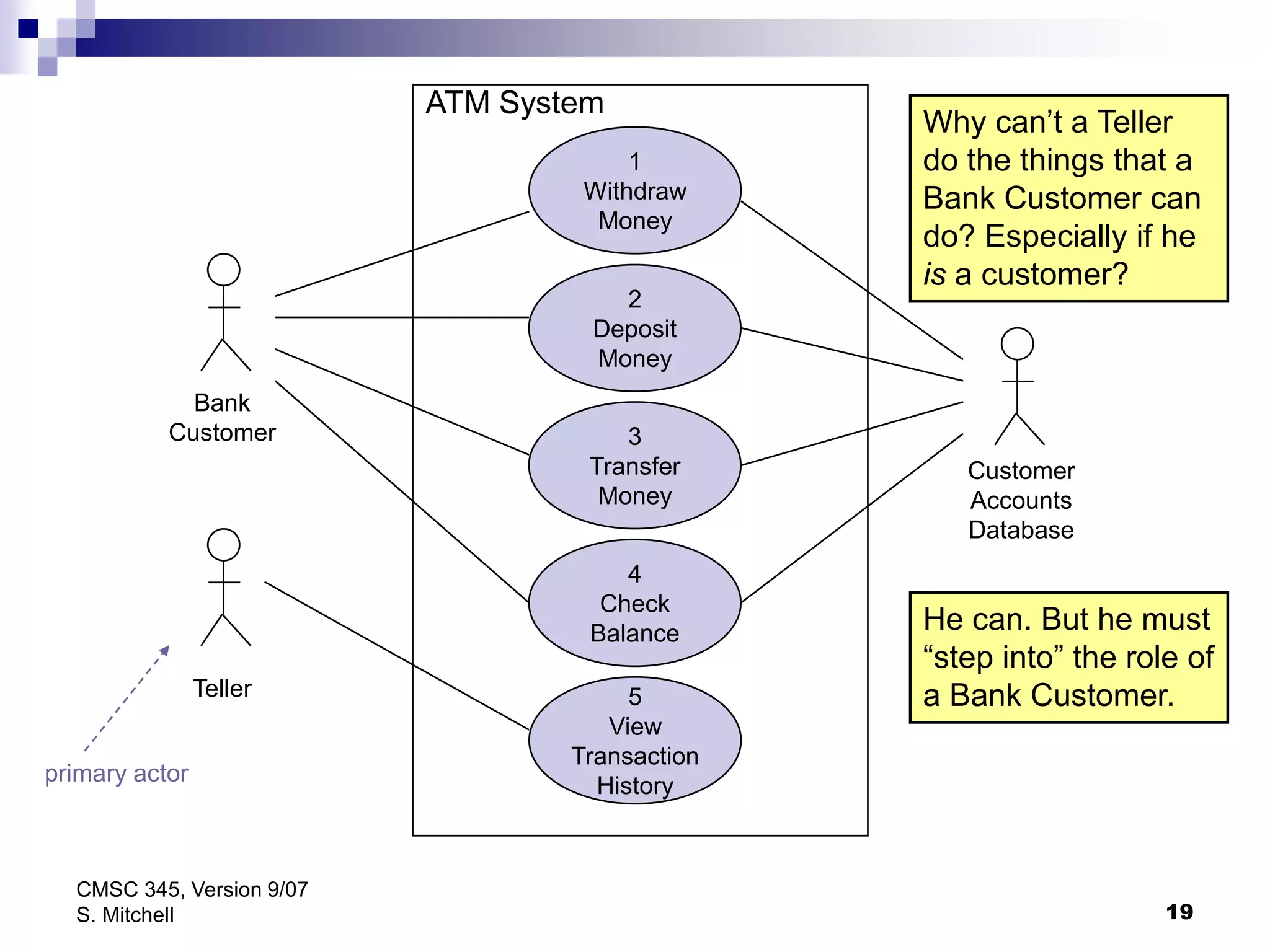
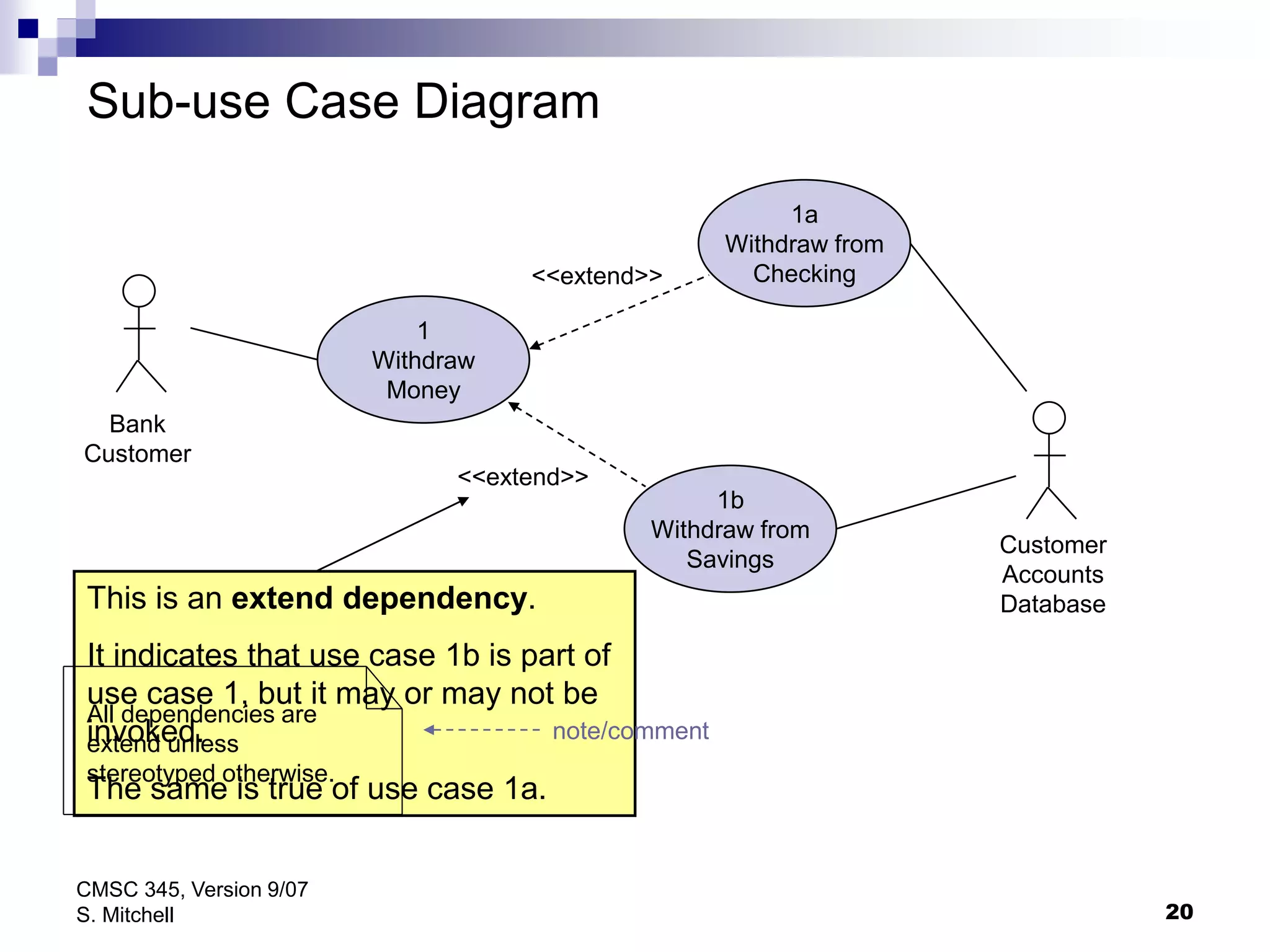
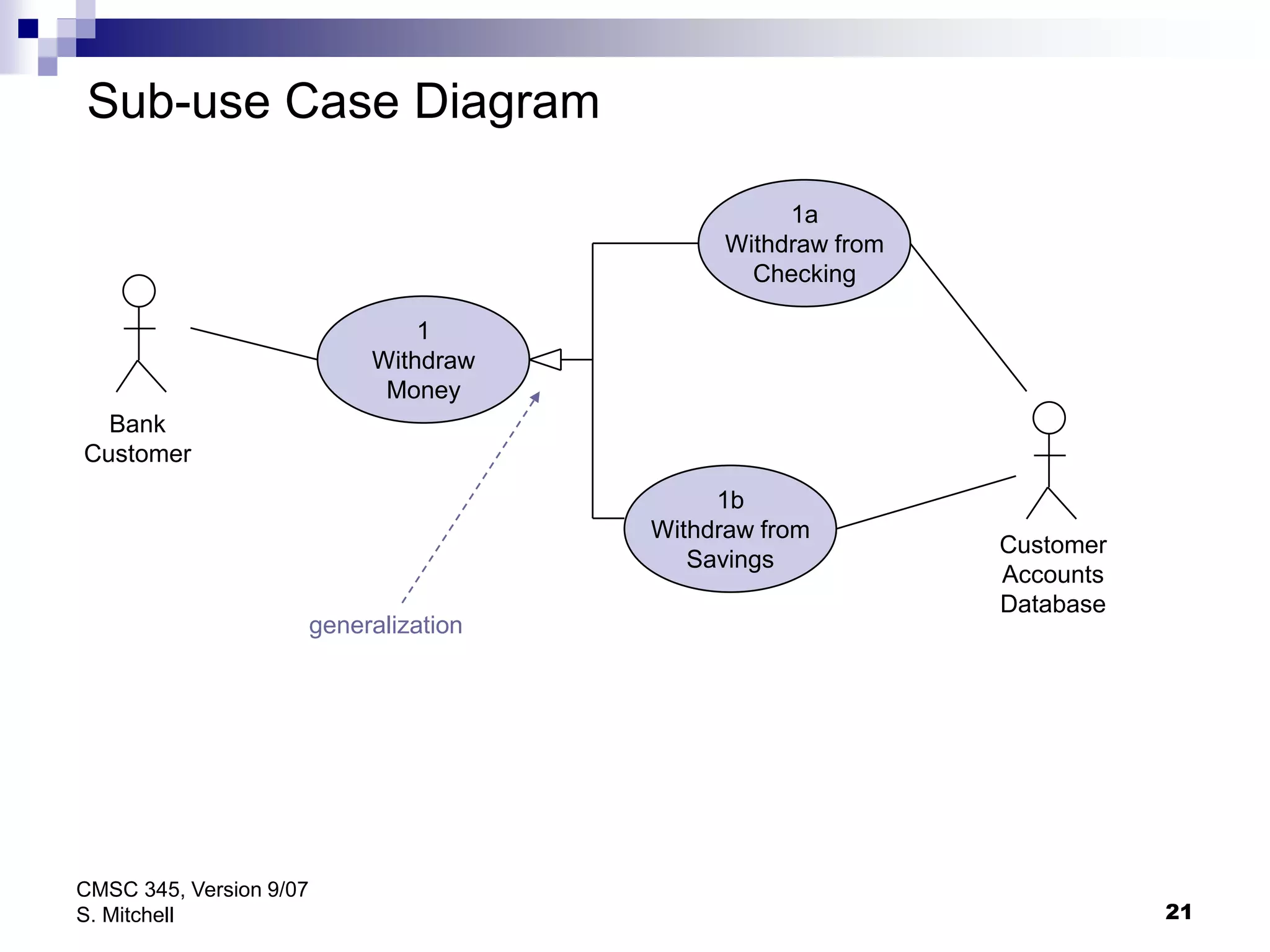
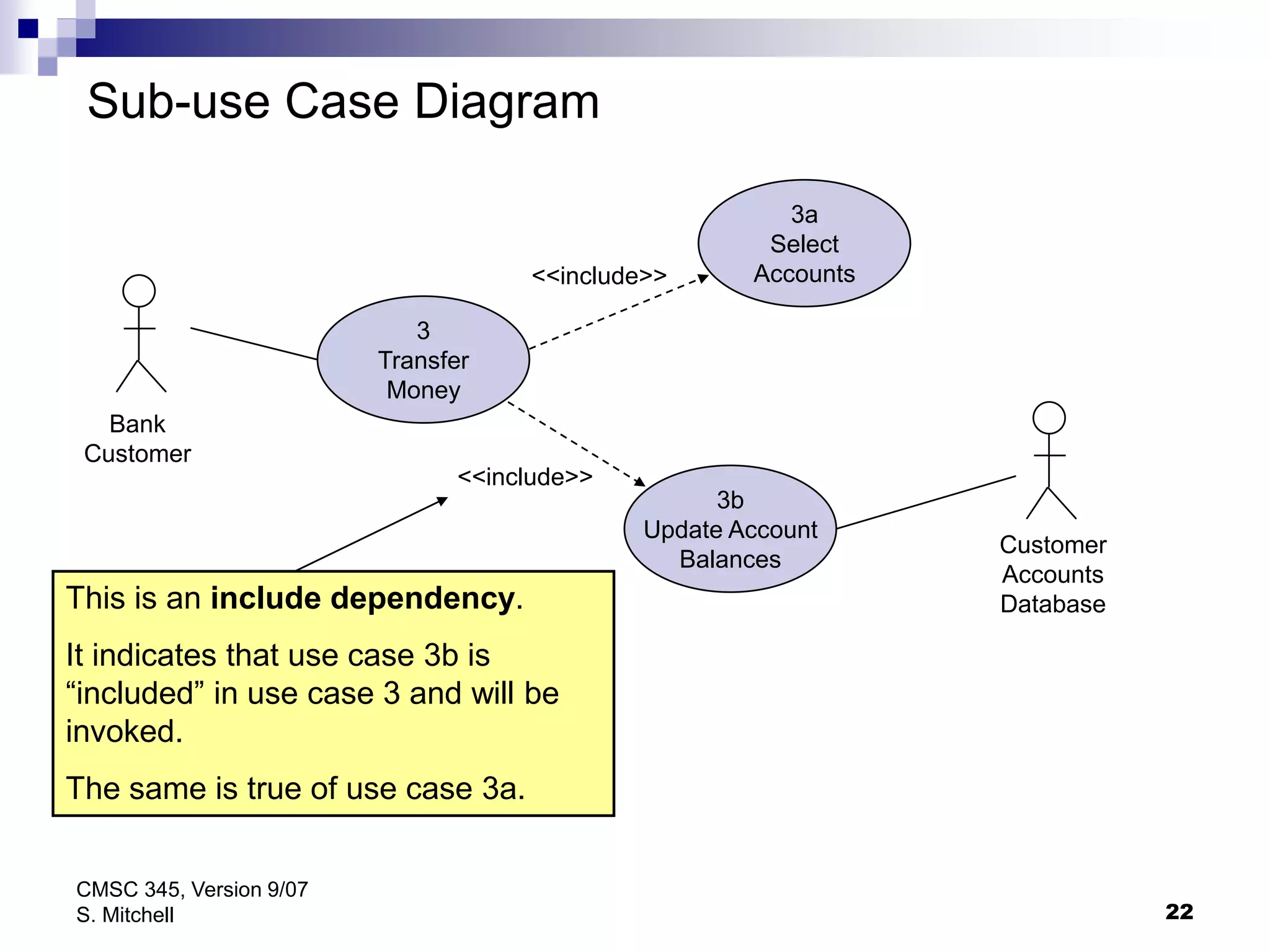
This document provides an overview of use cases, including their history, definition, components, notation, and use in conjunction with the Unified Modeling Language (UML). It describes the key elements of a use case specification template and explains how to write use case specifications and diagram actor and use case relationships.