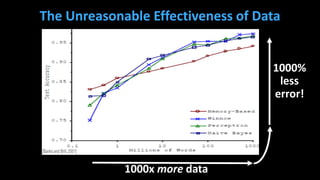
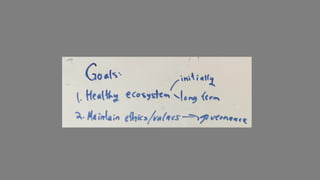
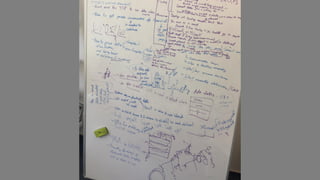
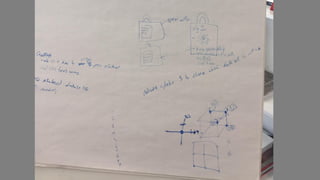
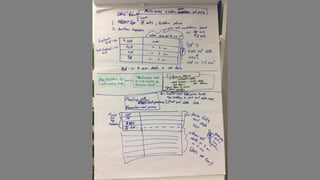
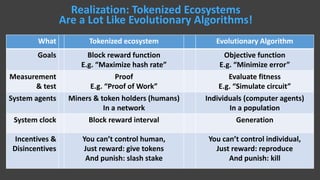
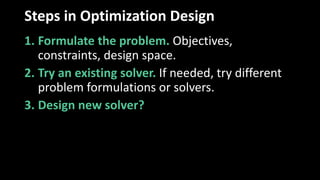
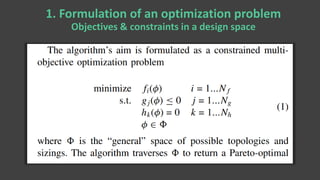
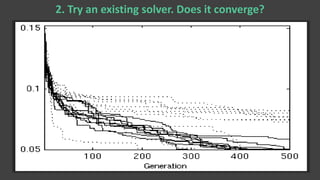
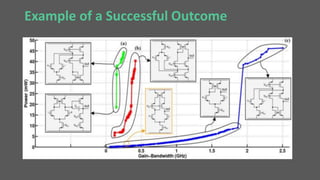
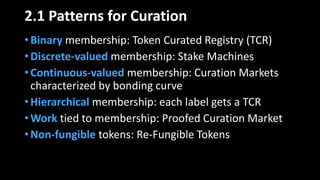
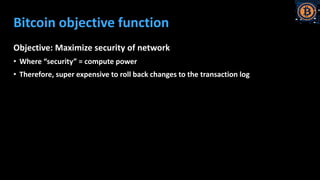
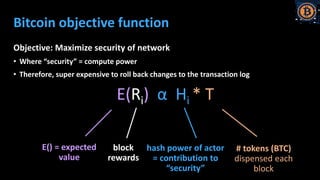
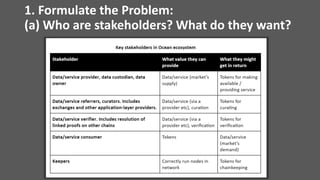
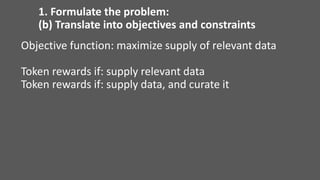
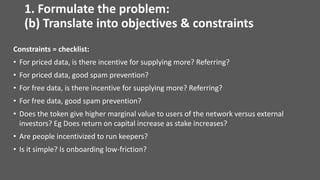
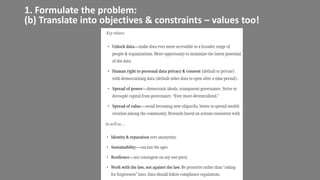
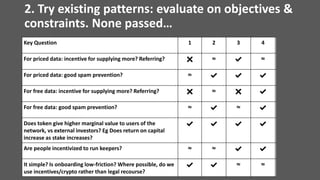
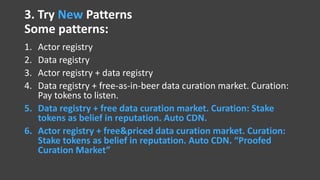
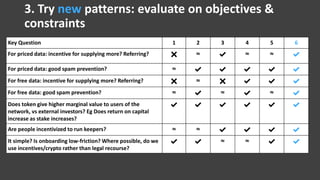
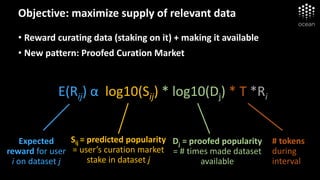
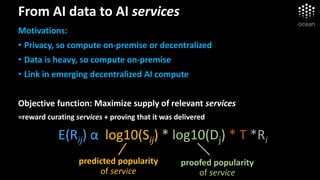
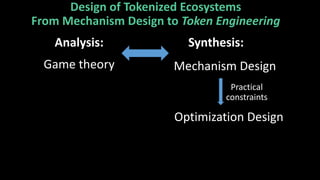
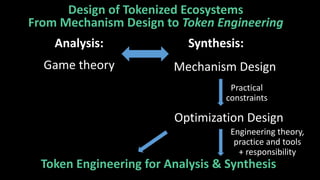
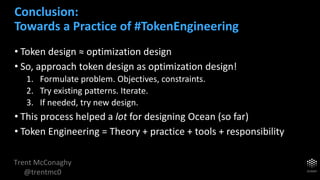
The document discusses the concept of token engineering, emphasizing the importance of structuring incentives through tokenized ecosystems akin to evolutionary algorithms. It outlines a systematic approach for token design, which includes problem formulation, testing existing solutions, and designing new patterns based on objectives and constraints. Overall, it suggests that treating token design as an optimization problem can improve the effectiveness of decentralized networks.