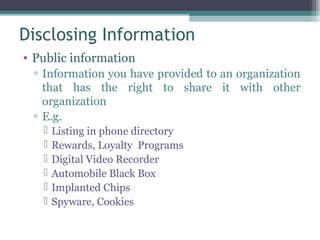
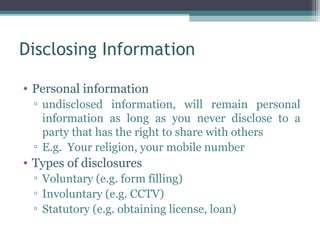
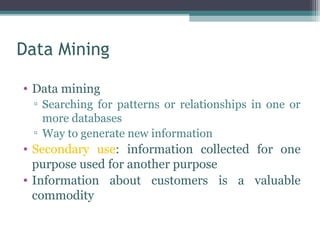
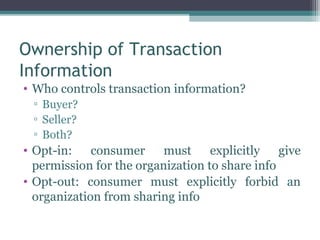
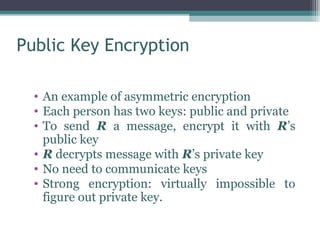
This document provides an overview of privacy and related concepts from an ethics perspective. It defines privacy as allowing individuals some level of control over access to their personal information and physical selves. The document discusses perspectives on privacy, ways technology can compromise privacy, and benefits and harms of privacy. It also covers topics like trusting relationships, disclosing information, data mining, identity theft, and encryption. The learning outcomes are to explain privacy perspectives, describe how technology impacts privacy, and apply ethics to privacy issues.