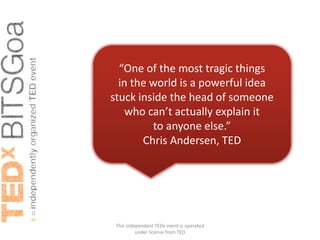
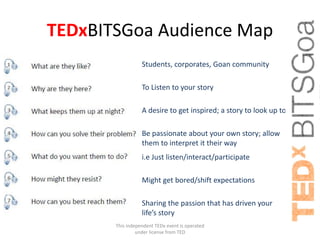
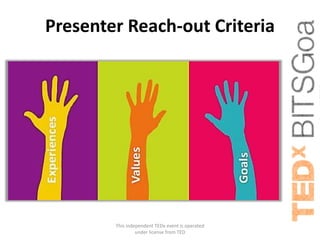
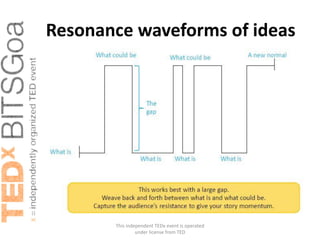
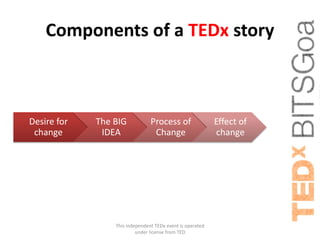
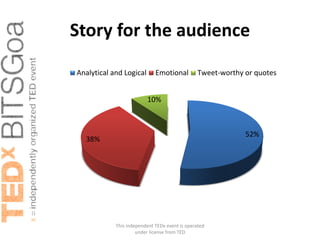
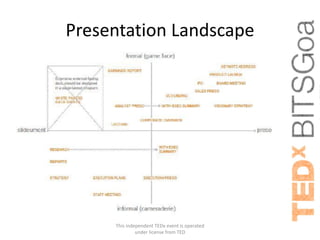
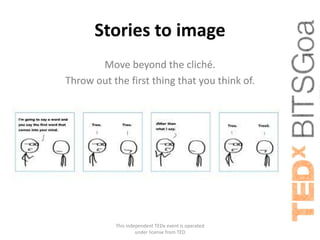
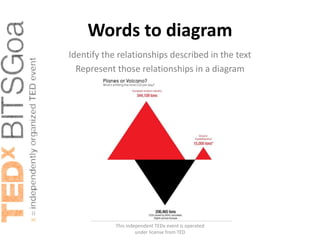
This document provides guidance for speakers at an upcoming TEDx event at BITS Pilani, KK Birla Goa Campus. It discusses how to effectively share ideas with an audience by knowing your listeners, telling a story rather than just providing information, engaging the audience emotionally and with memorable quotes, and using visual aids like slides intentionally to enhance the message rather than just decorate. It also provides tips on effective public speaking like writing for the ear, maintaining high energy, connecting to the theme and other speakers, owning the stage, enjoying yourself, and keeping messages concise with clear signposts.