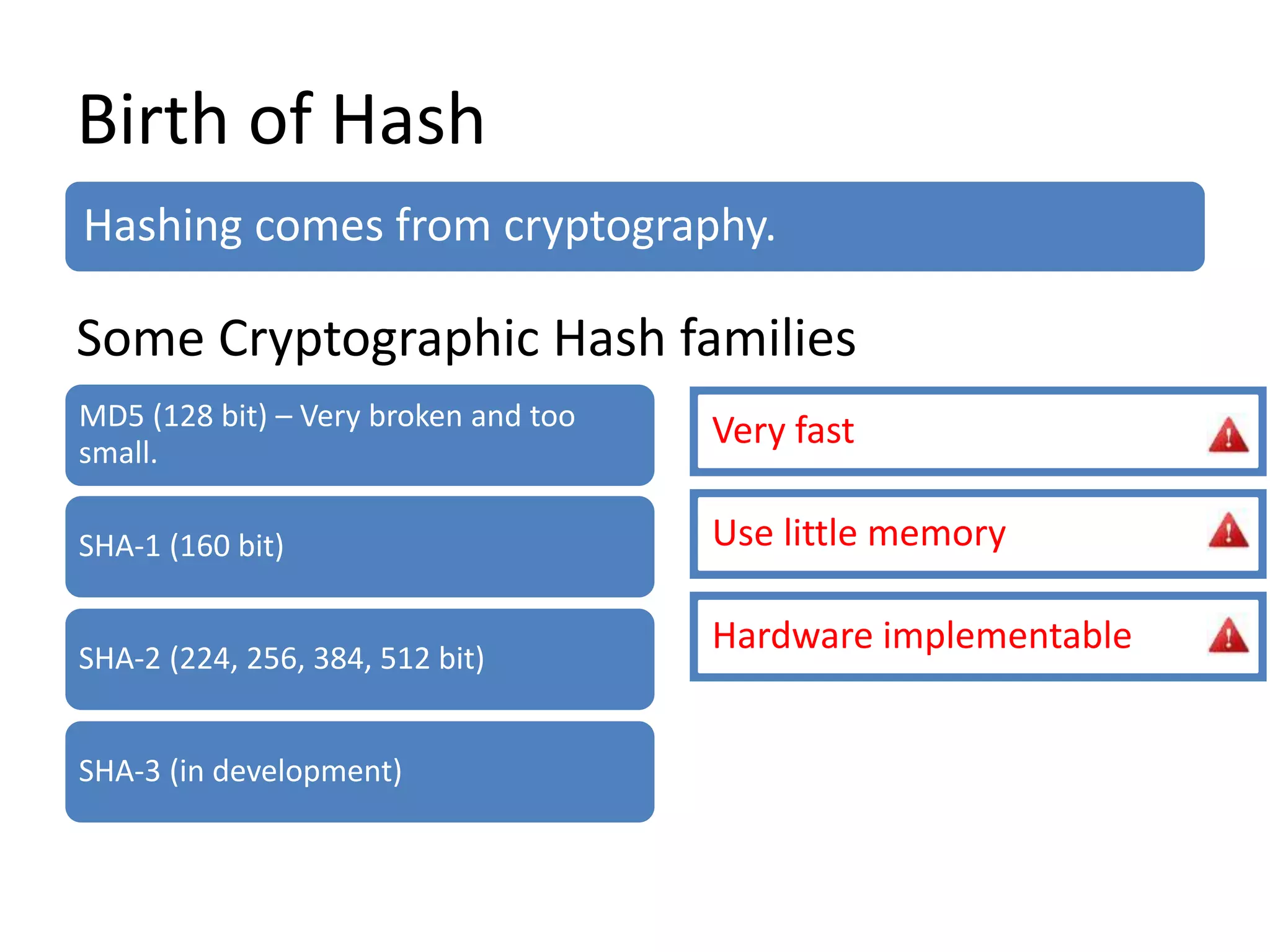
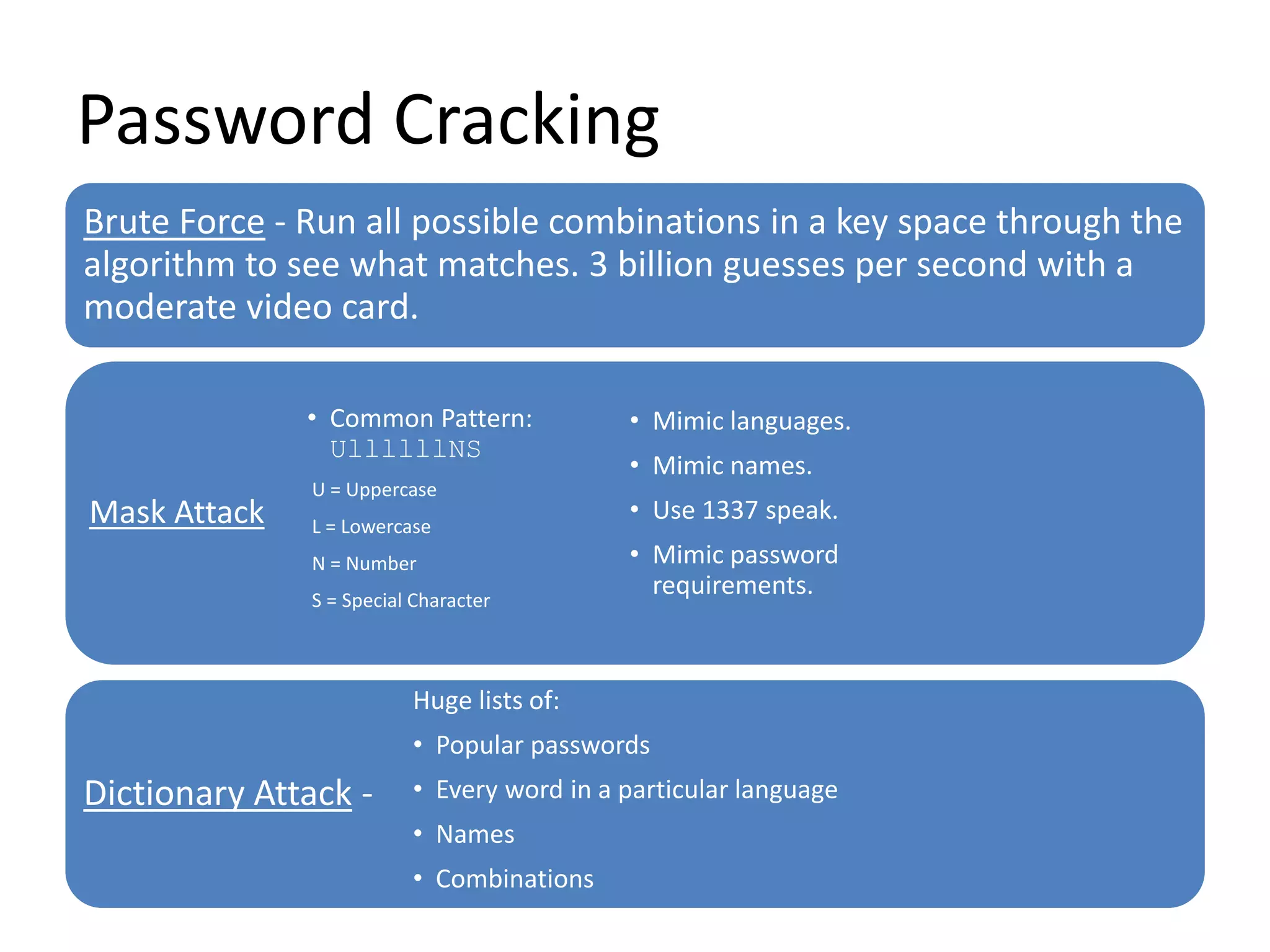
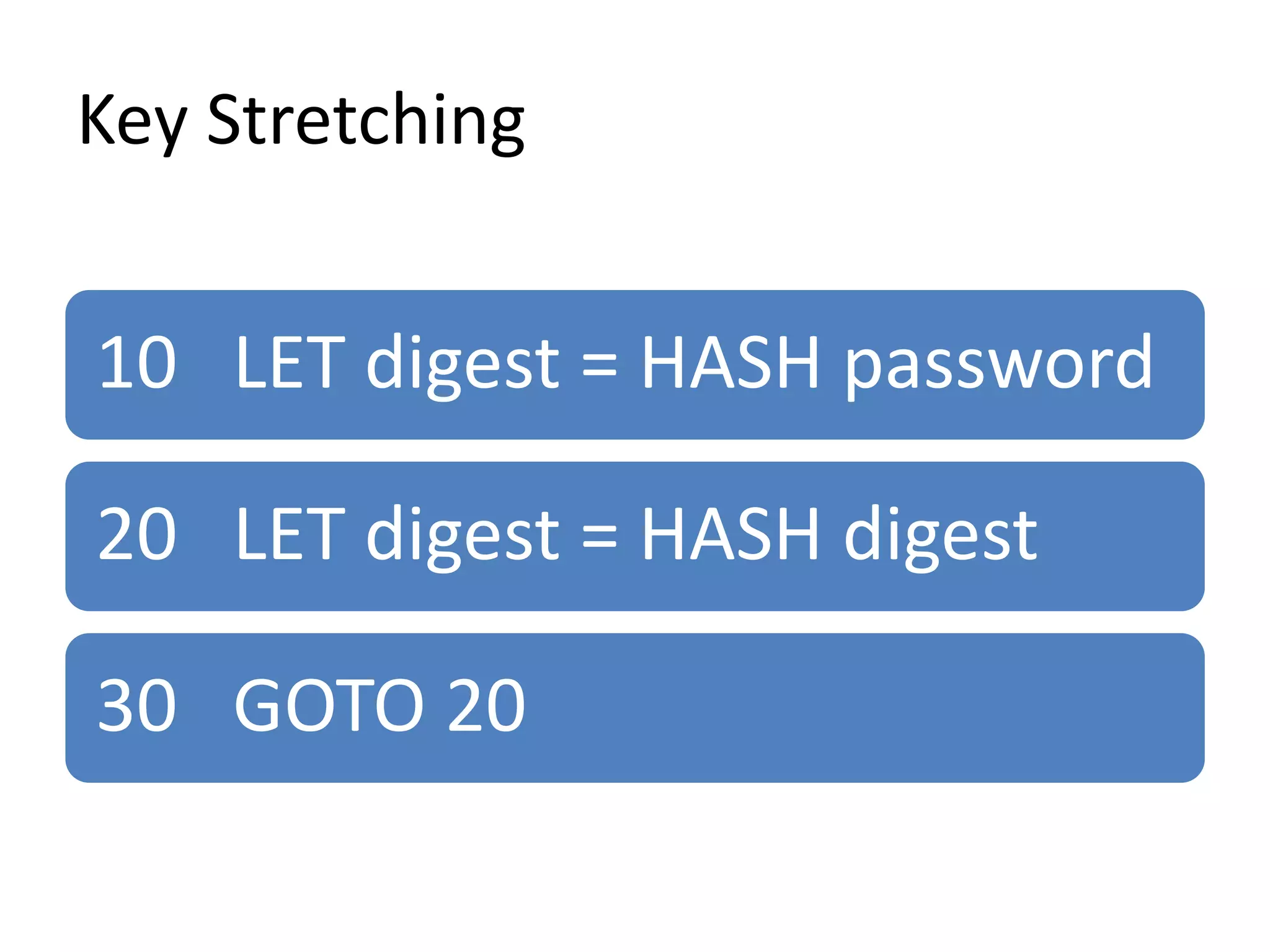
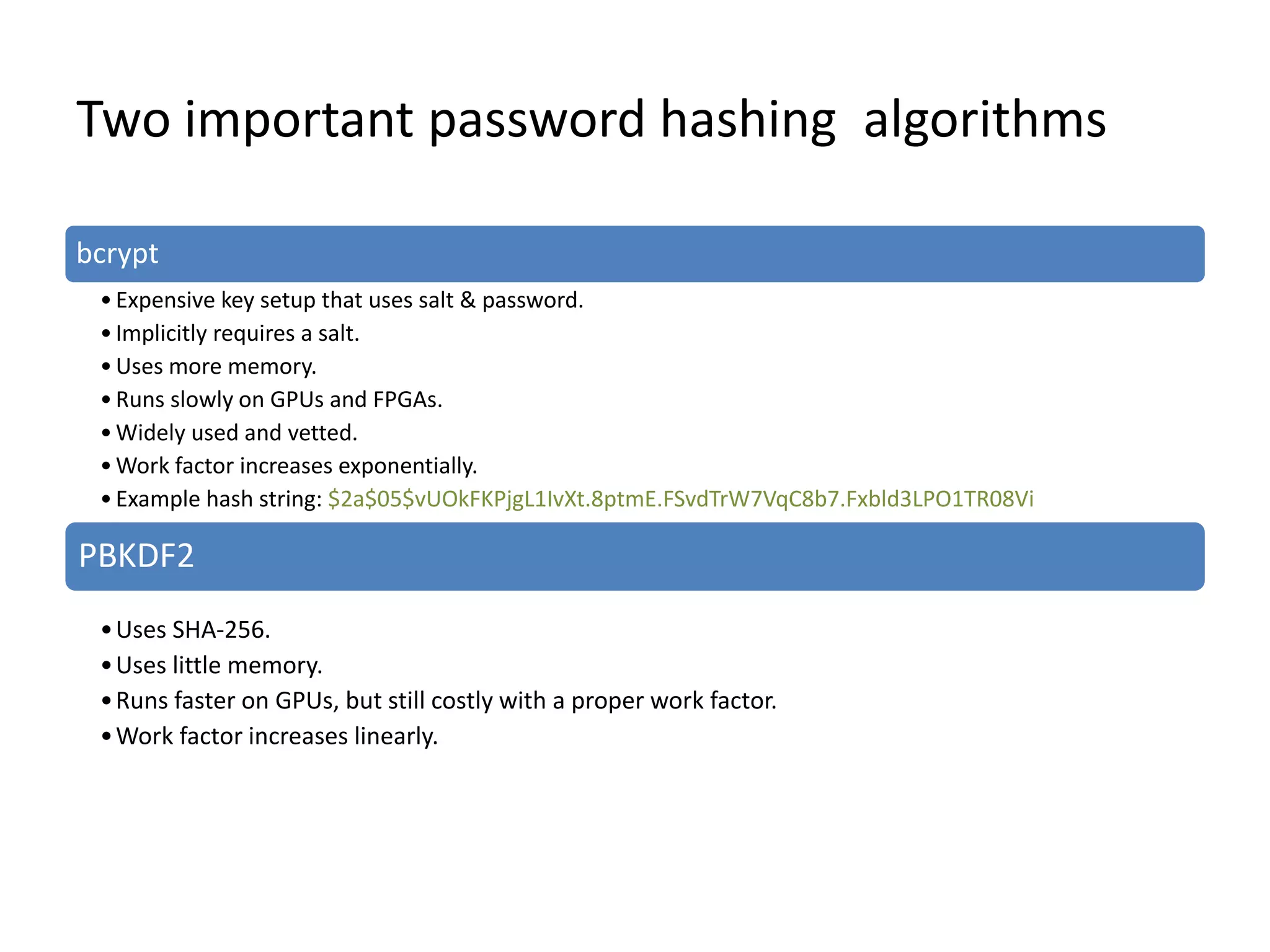
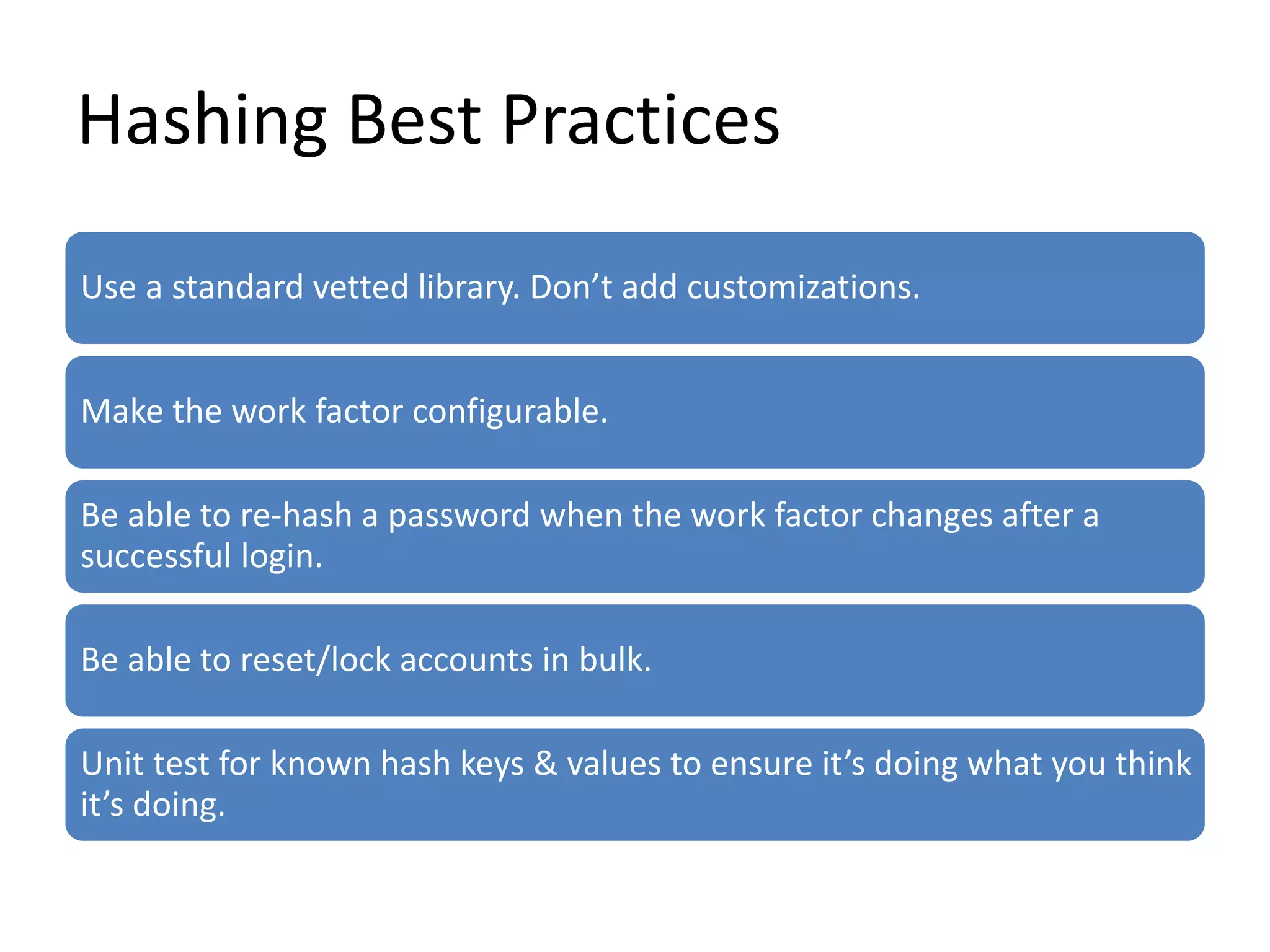
This document discusses techniques for securely storing passwords using hashing and preventing cracking. It recommends using algorithms like bcrypt and PBKDF2 that include salts and key stretching to make passwords very difficult to brute force or dictionary attack by requiring extensive time and computing resources. The document provides examples of hashing best practices and measures organizations and users can take to better protect against leaks and unauthorized access.