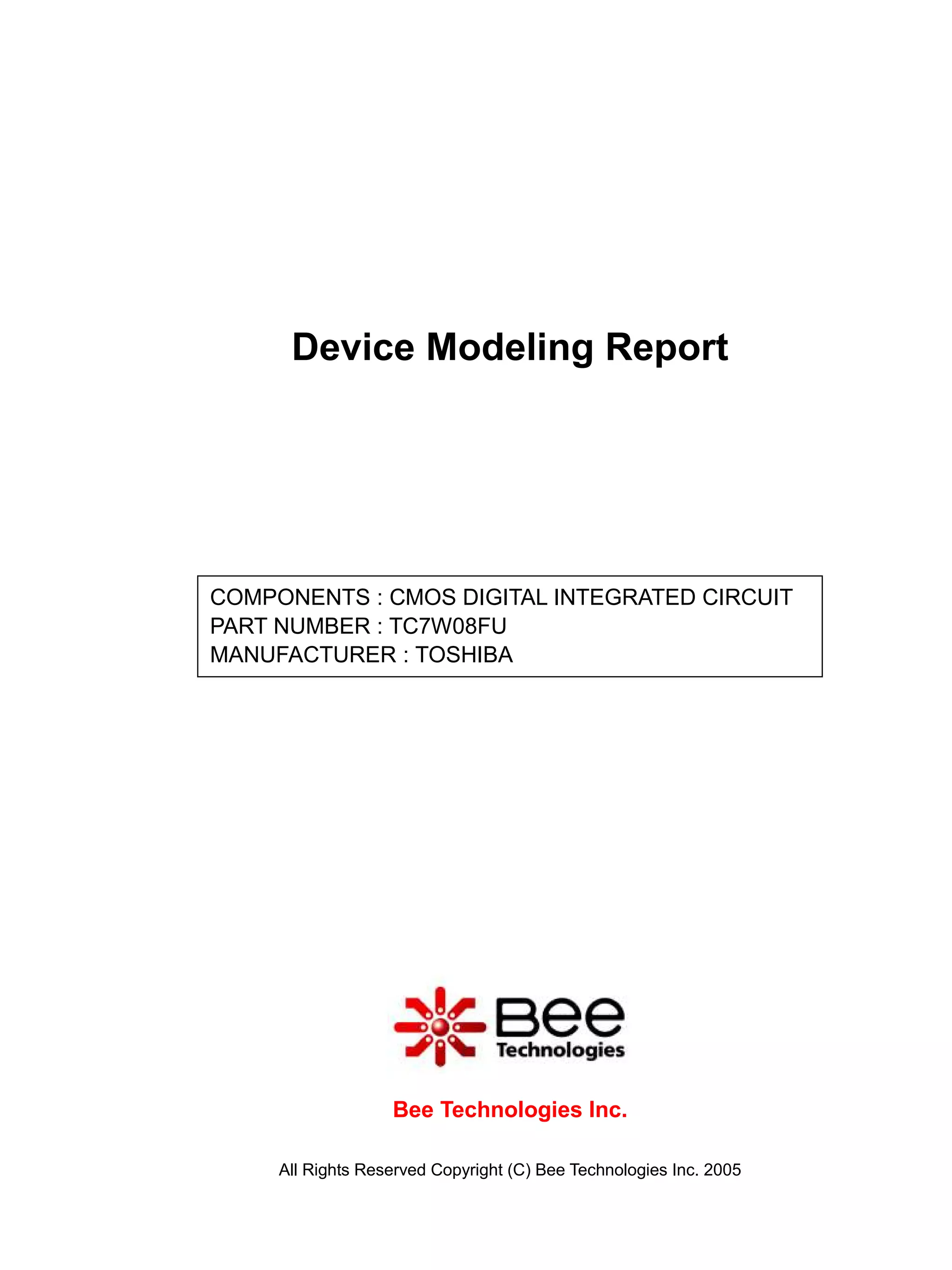
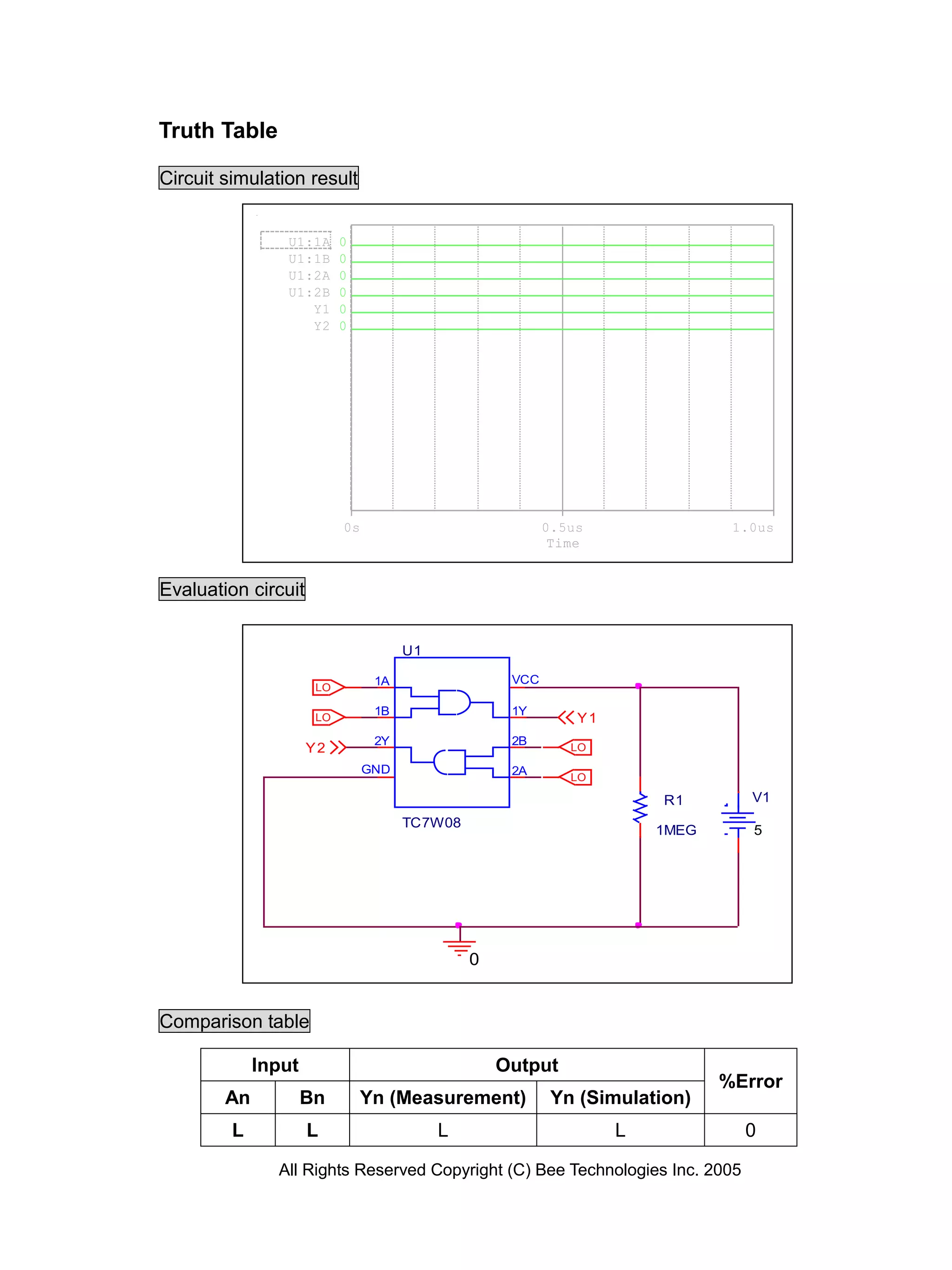
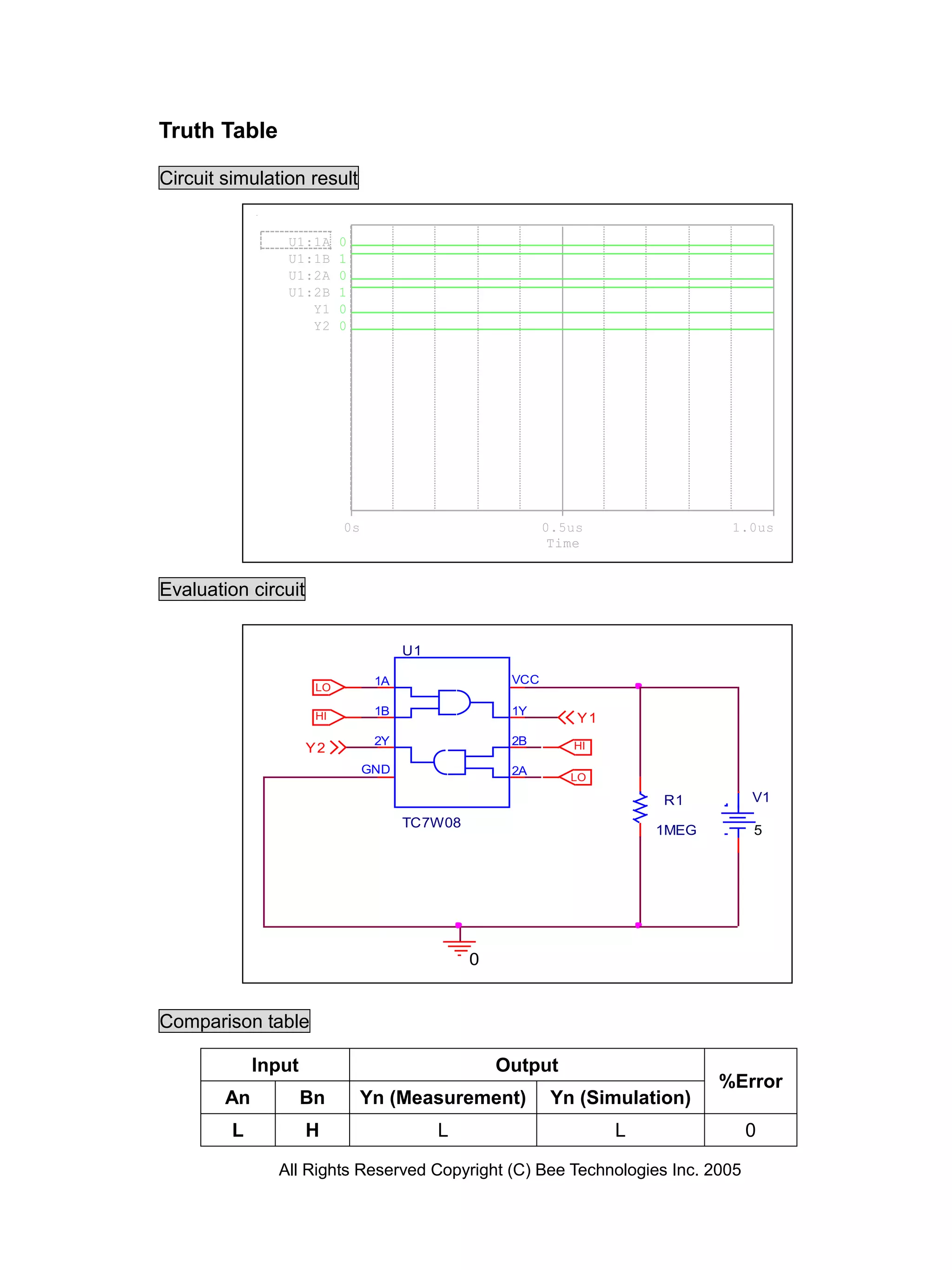
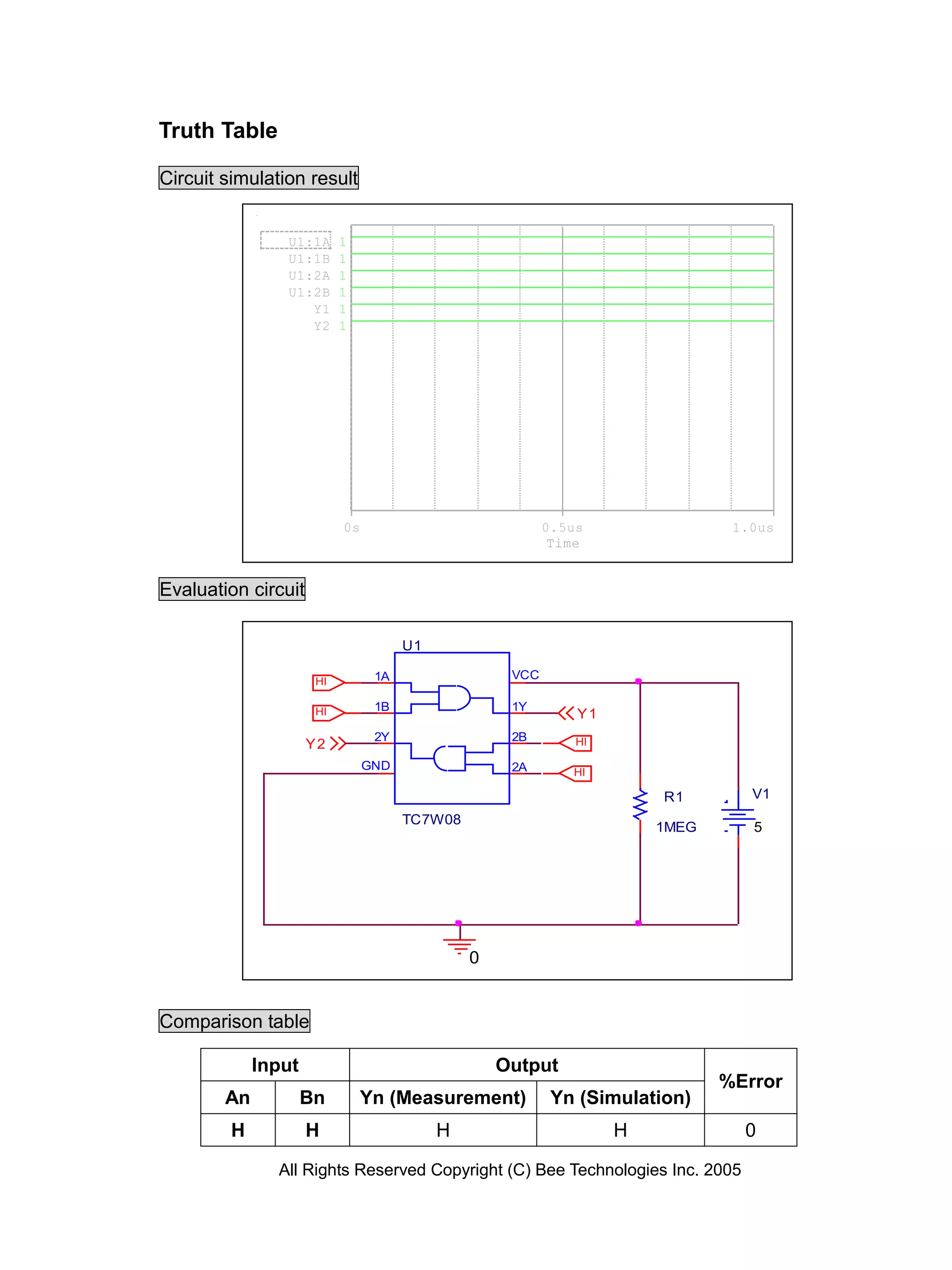
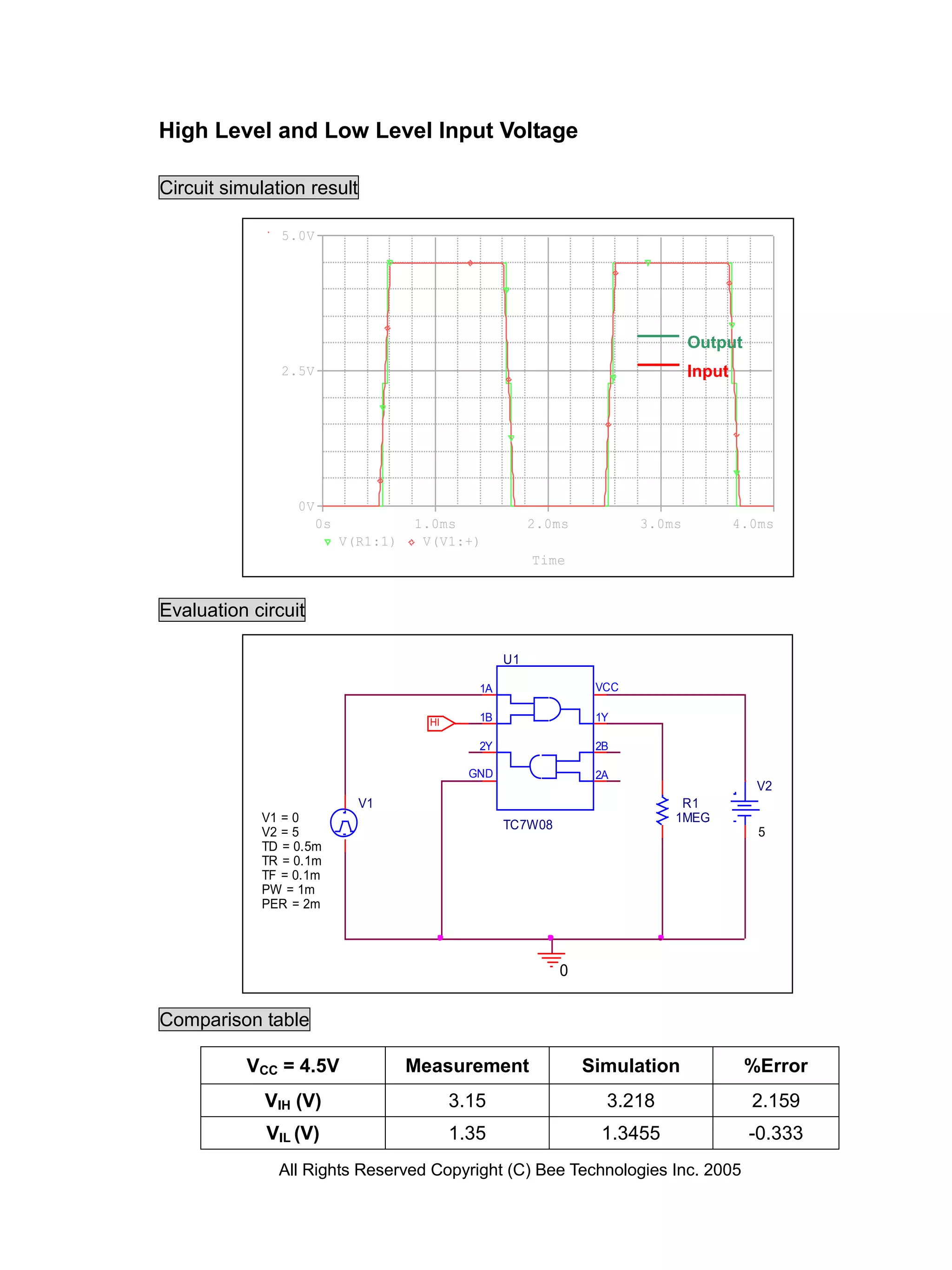
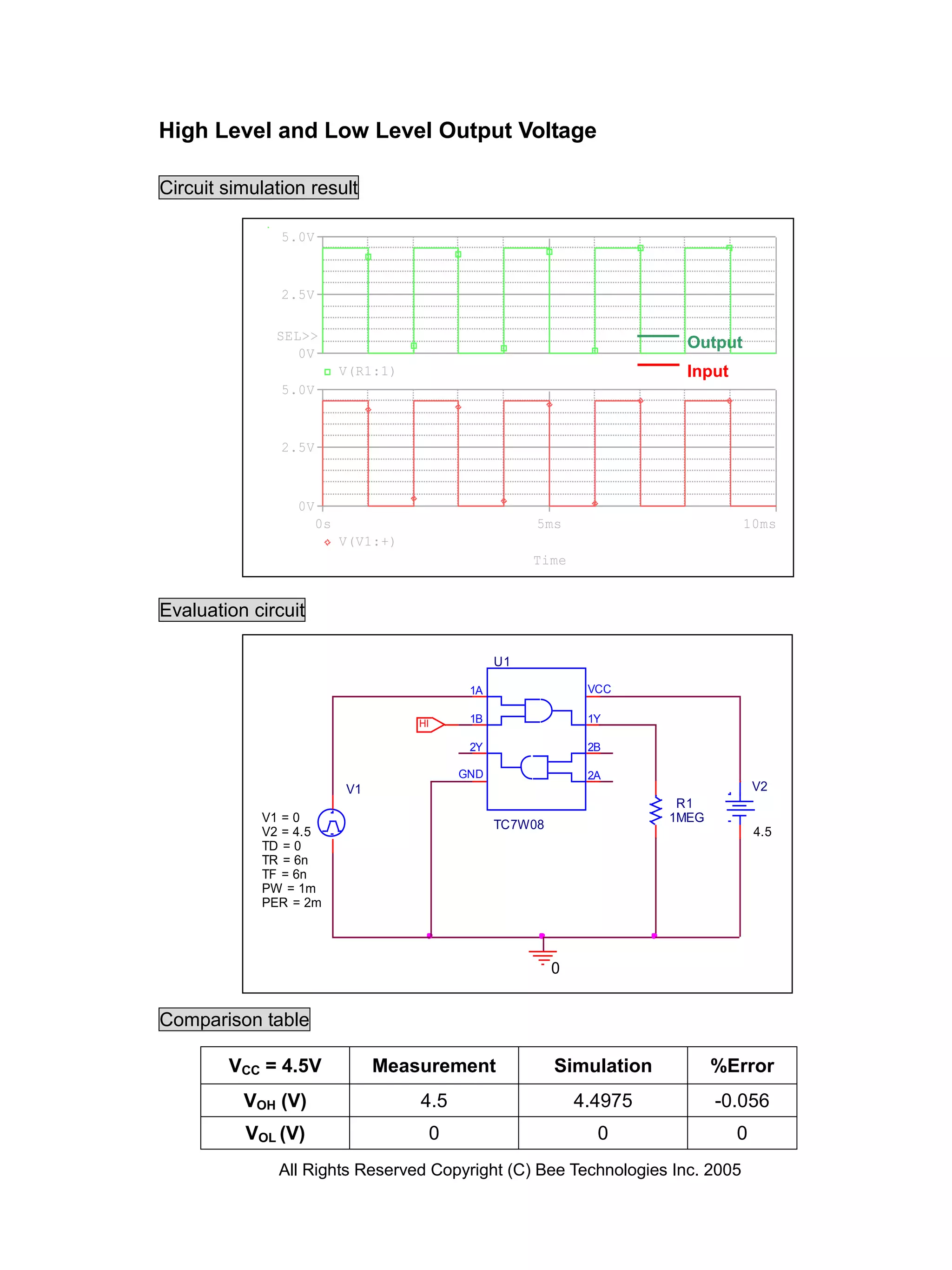
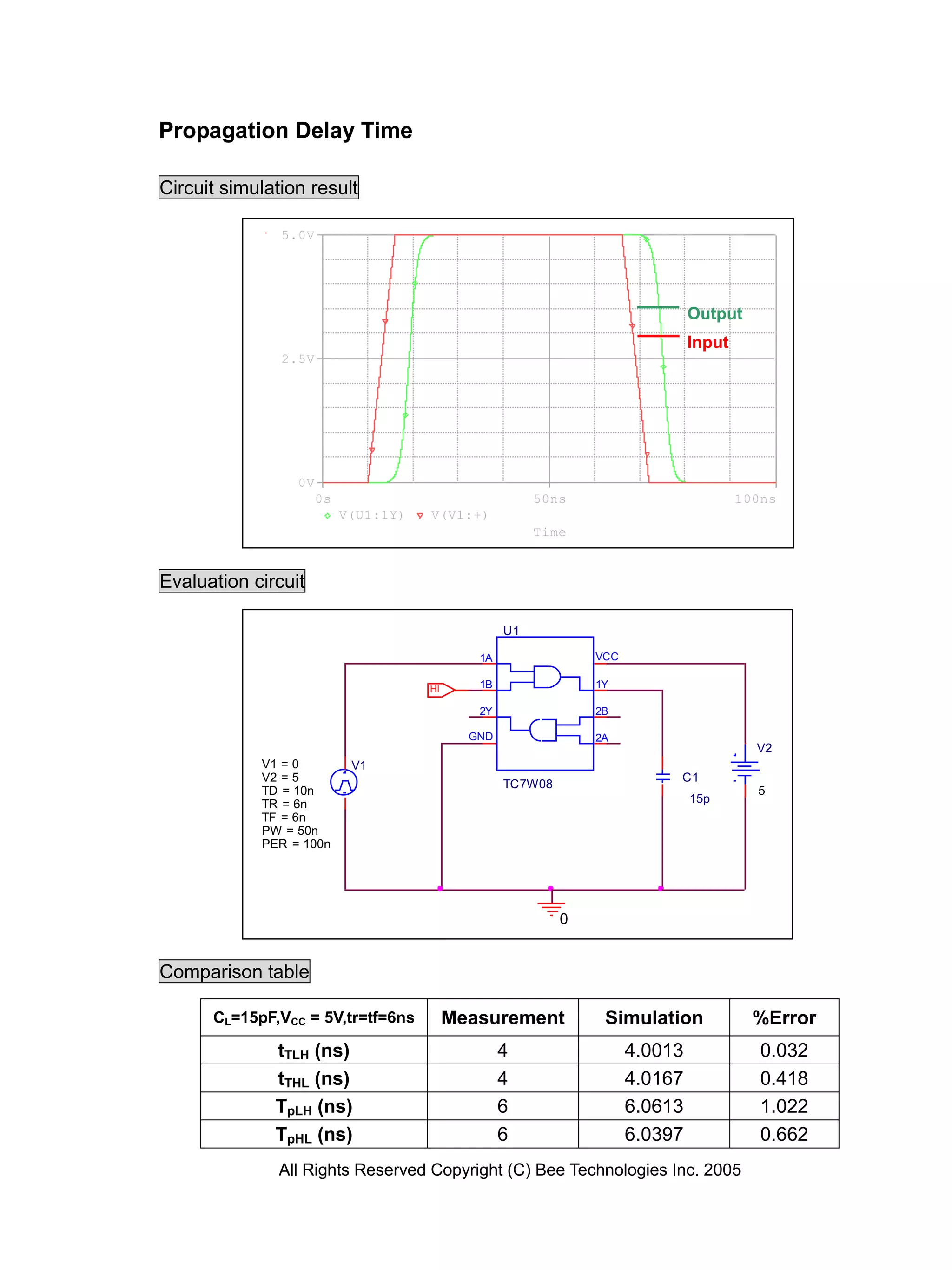
The document is a device modeling report for a CMOS digital integrated circuit, TC7W08FU, from Toshiba Bee Technologies Inc. It includes various truth tables, circuit simulation results, comparisons between measurements and simulations, and details on voltage levels and propagation delays. The report summarizes input-output characteristics and error percentages relevant to circuit performance.