Embed presentation



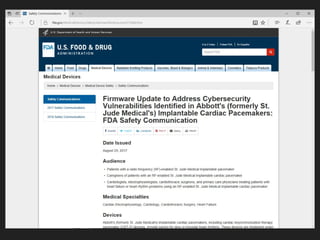
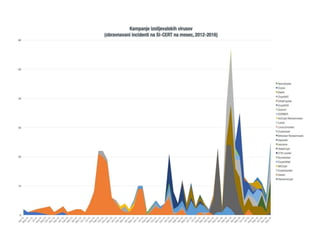


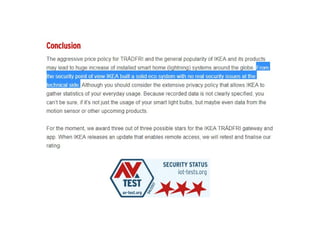
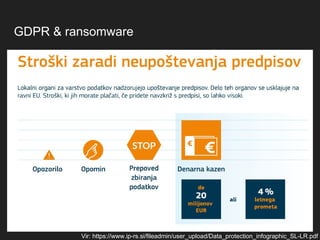




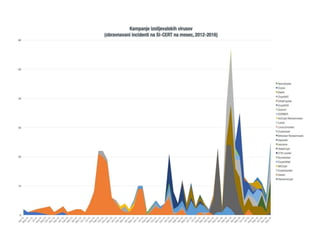
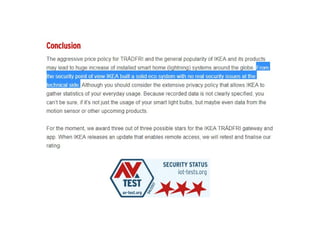
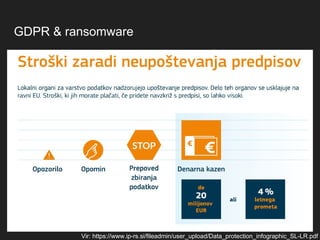
The document discusses IoT ransomware, referencing a meetup held on September 13, 2017, by Tadej Hren from SI-CERT. It identifies stakeholders who can take action against ransomware, including users, manufacturers, and the government. Additionally, it provides links to resources on GDPR and ransomware.