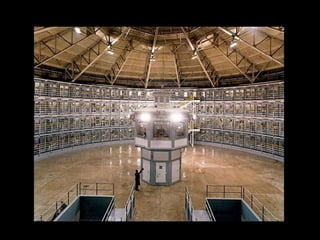
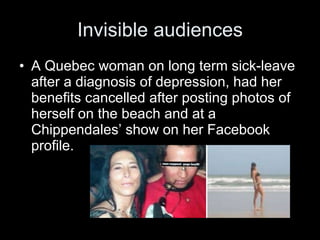
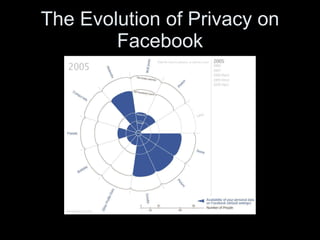
This document discusses the evolution of surveillance from the 18th century to today. It analyzes how surveillance has changed from public punishment to more invisible internalized discipline. A key concept discussed is Jeremy Bentham's Panopticon model of surveillance, which aims to induce self-surveillance through the perception of constant monitoring. Modern surveillance takes many forms like CCTV, loyalty cards, electronic tags, and social media use, which can blur public and private boundaries and enable new forms of social sorting and control.