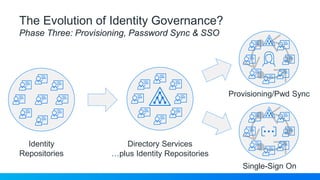
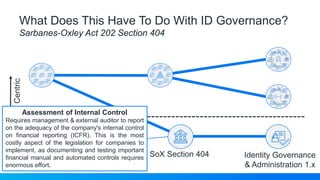
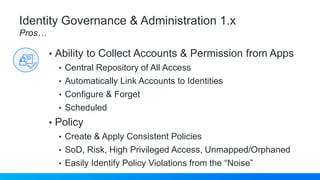
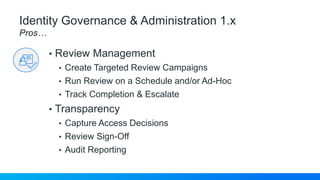
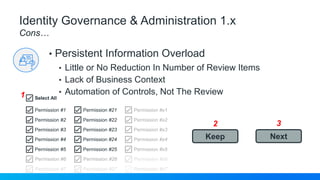
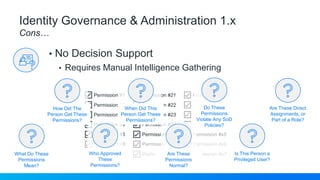
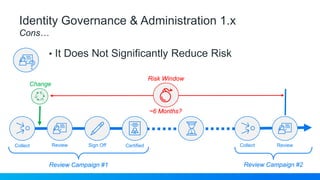
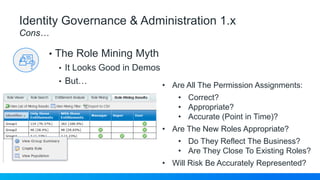
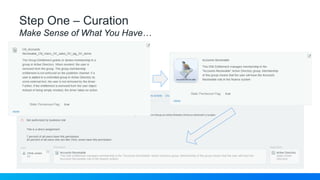
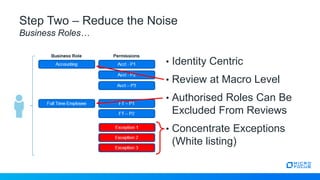
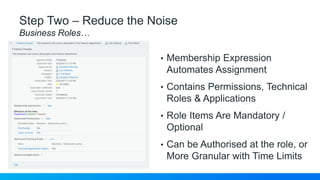
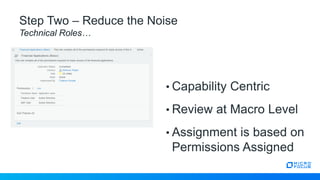
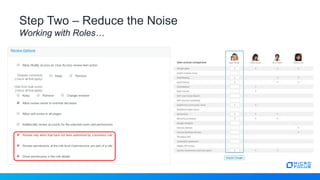
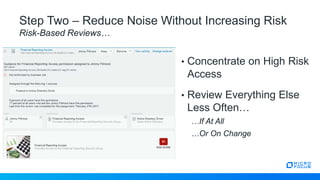
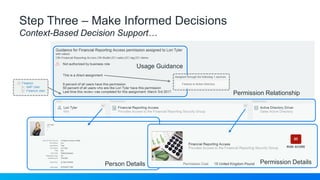
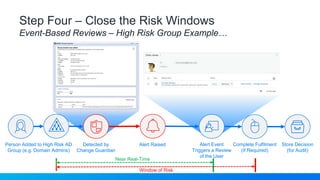
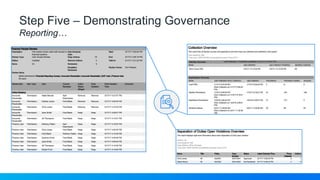
The document outlines the evolution and challenges of identity governance, particularly through the lens of the Sarbanes-Oxley Act, emphasizing the need for efficient management of access controls and permissions. It contrasts traditional identity governance methods with next-generation approaches that aim to reduce information overload and improve risk management through automation and context-based decision support. Five steps for effective identity governance are proposed, focusing on curation, noise reduction, informed decision-making, risk closure, and governance demonstration.