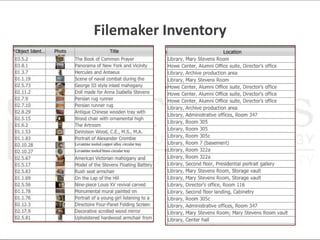
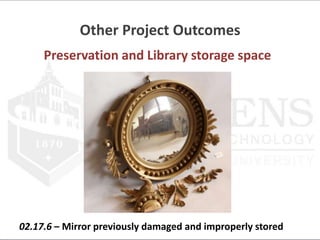
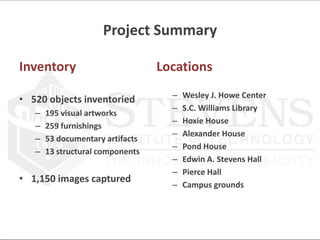
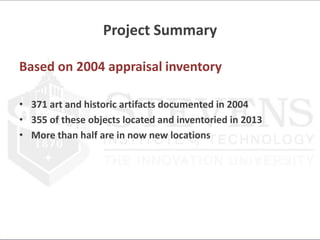
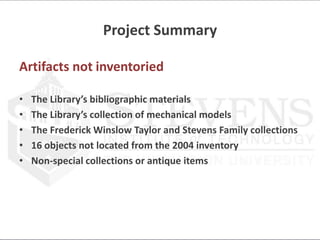
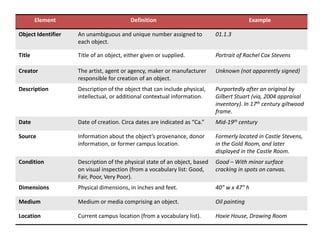
The project inventoried over 500 artifacts, artworks, and furnishings across Stevens Institute of Technology's campus. Photographic documentation was completed for over 1,150 objects. The inventory provides location information and descriptions to create an accessible record for preservation and research. Next steps include oral histories, additional provenance research, preservation activities, and inventorying remaining collections. The findings will transition to an online database for improved access and discovery of Stevens' special collections.





![Inventory Process
Unique ID number
The Moon and Stars
01.4.1
[sequential #]
Visual work
Mobile
scw_01.4.1_1.jpg](https://image.slidesharecdn.com/stevenspresentation-130716104256-phpapp01/85/Stevens-presentation-11-320.jpg)