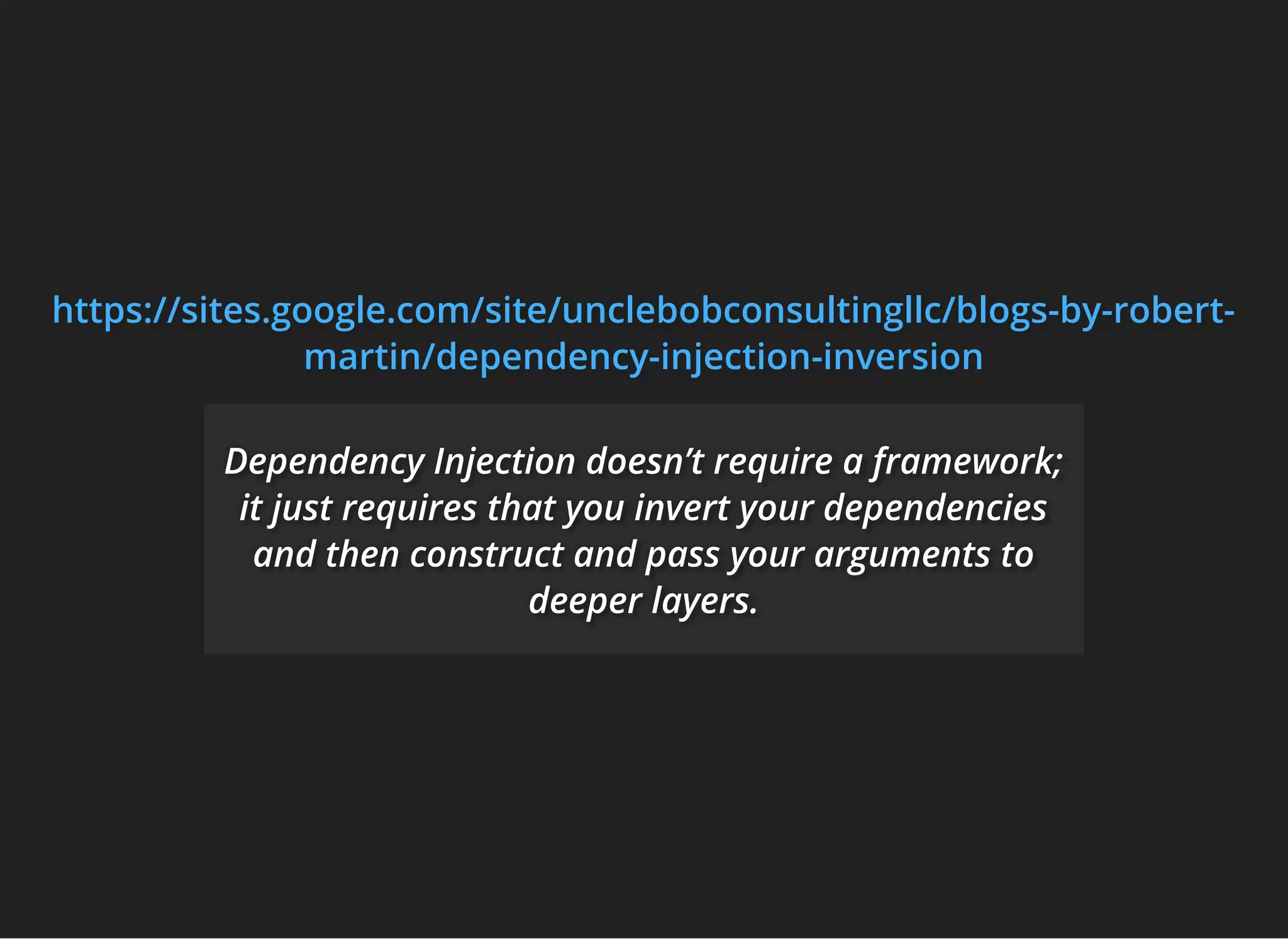
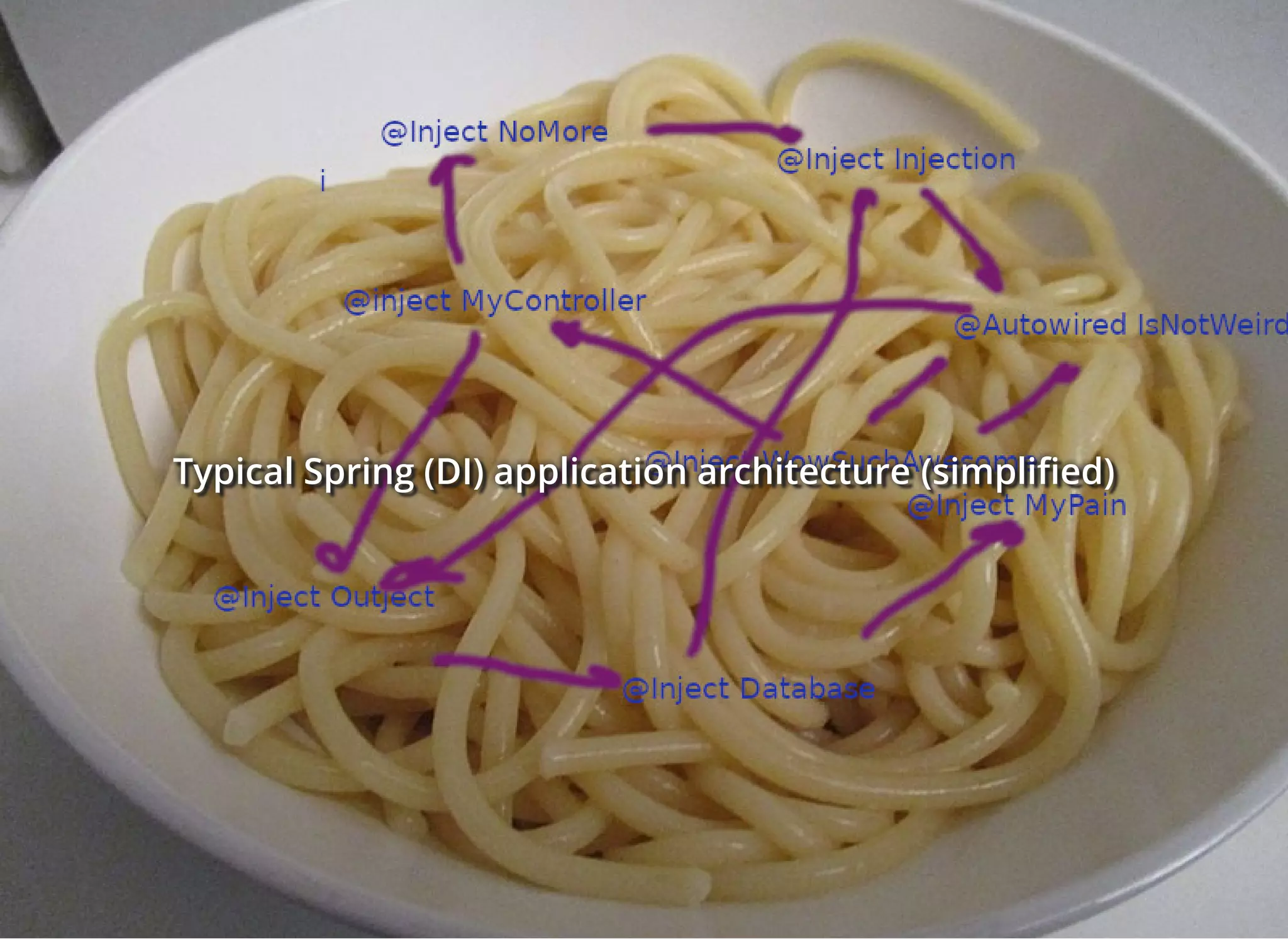
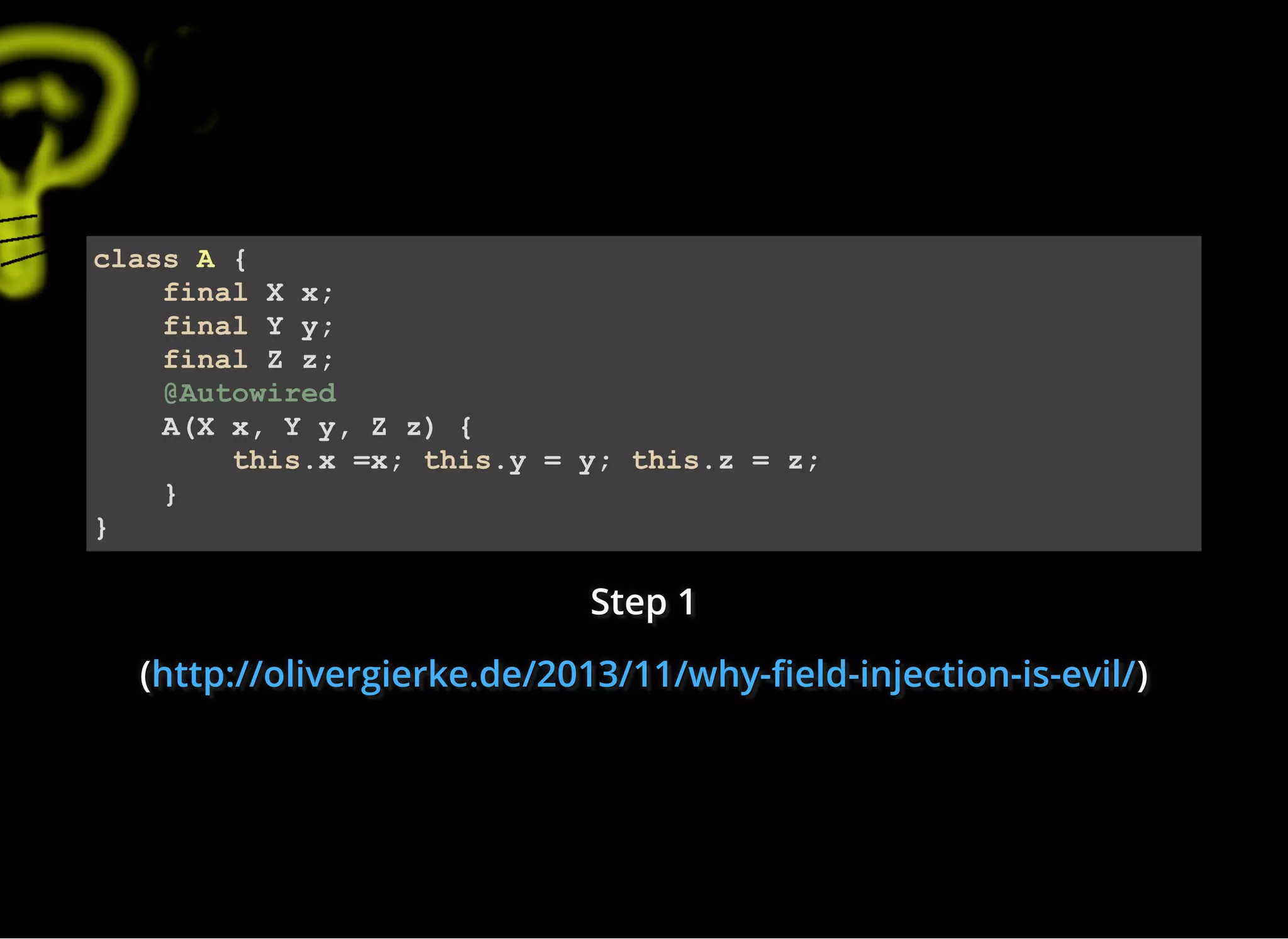
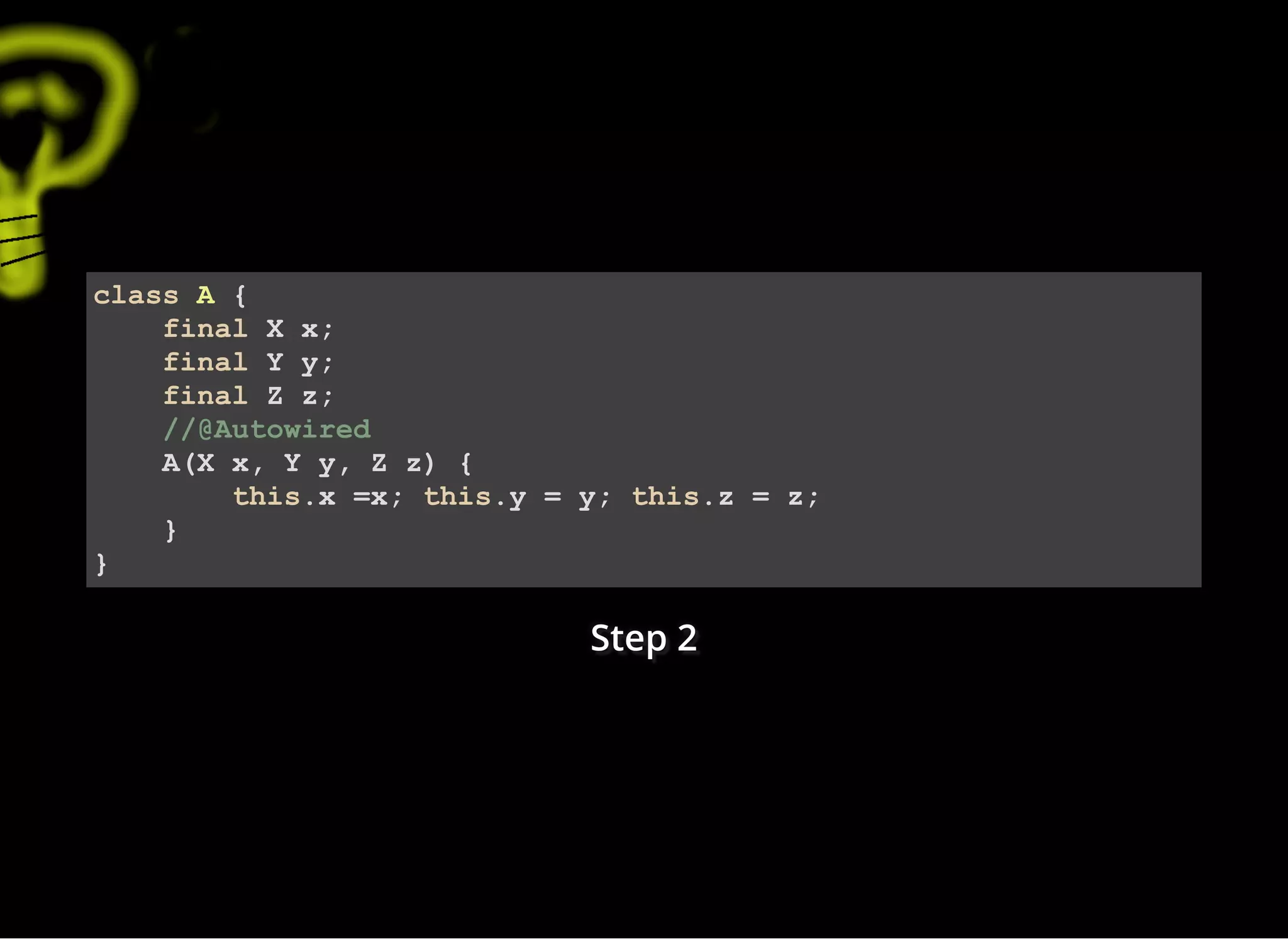
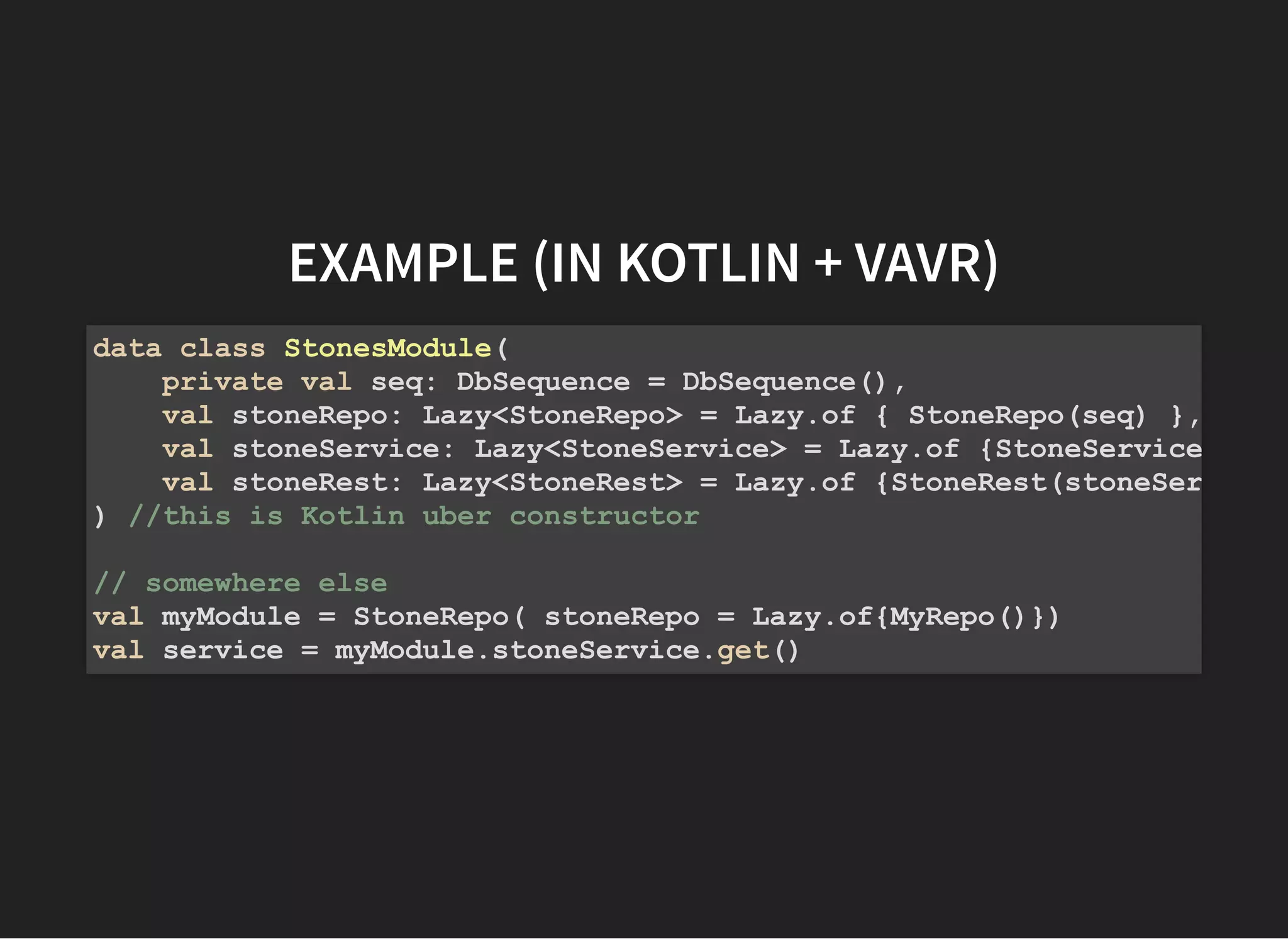
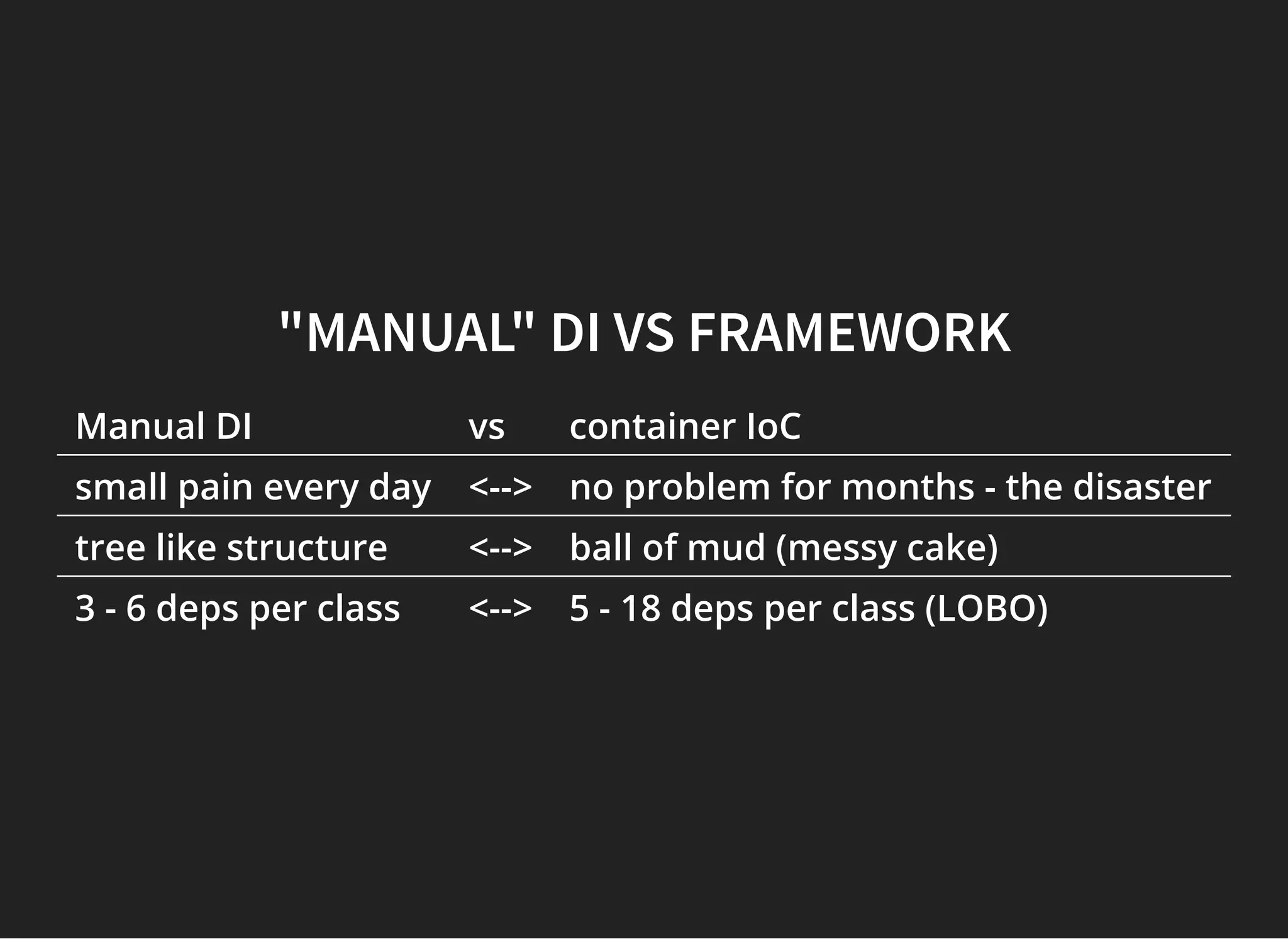
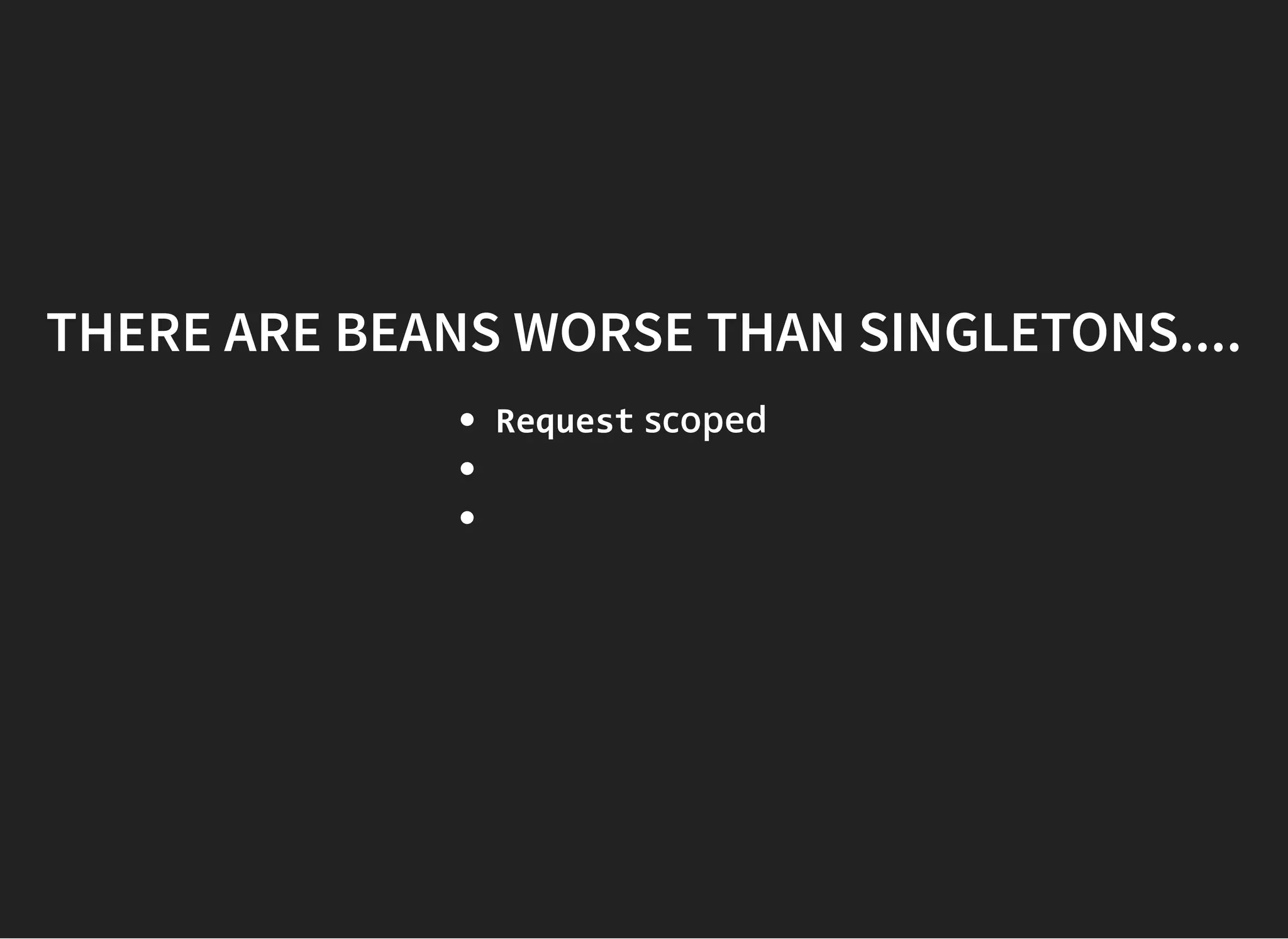
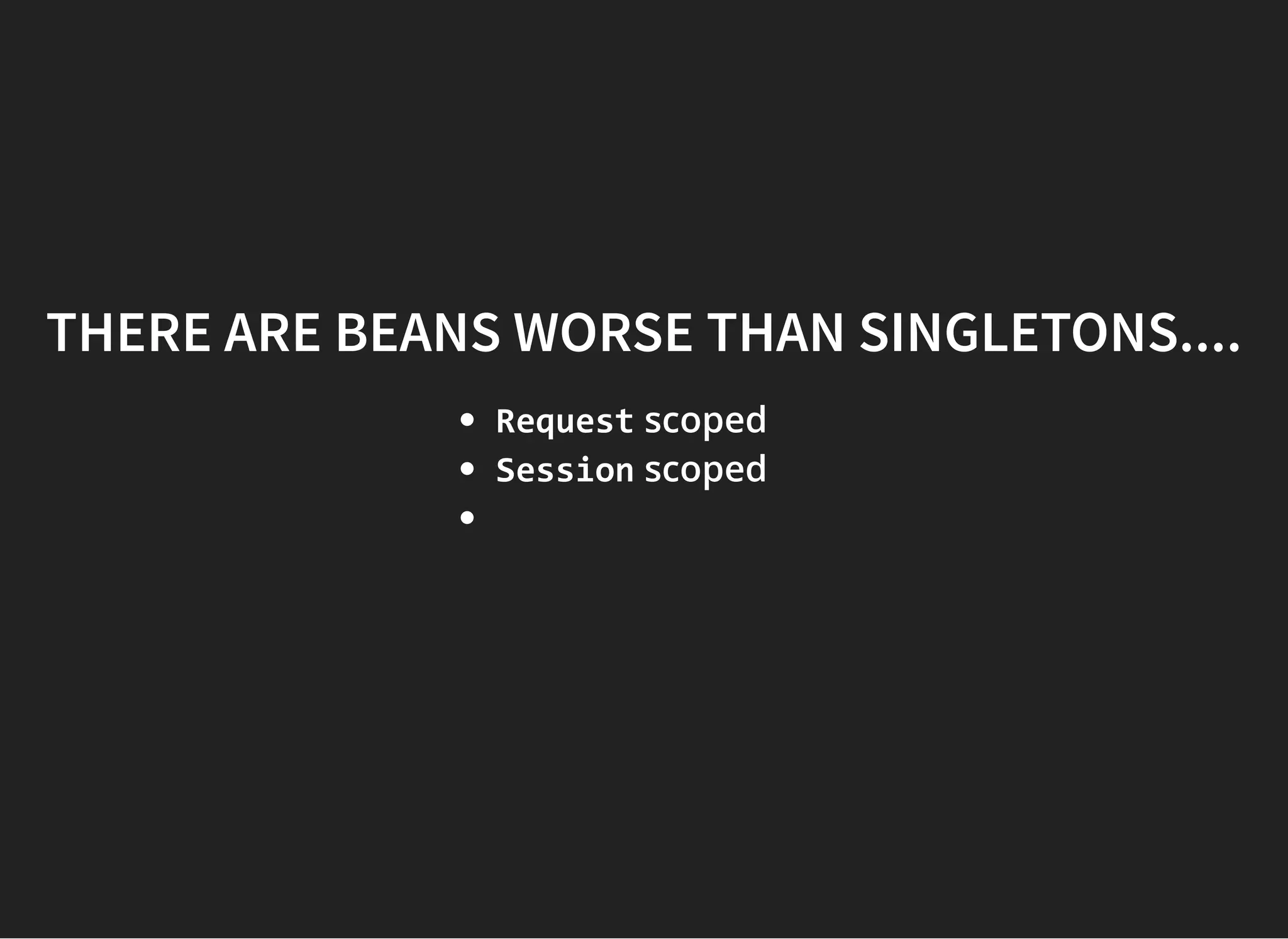
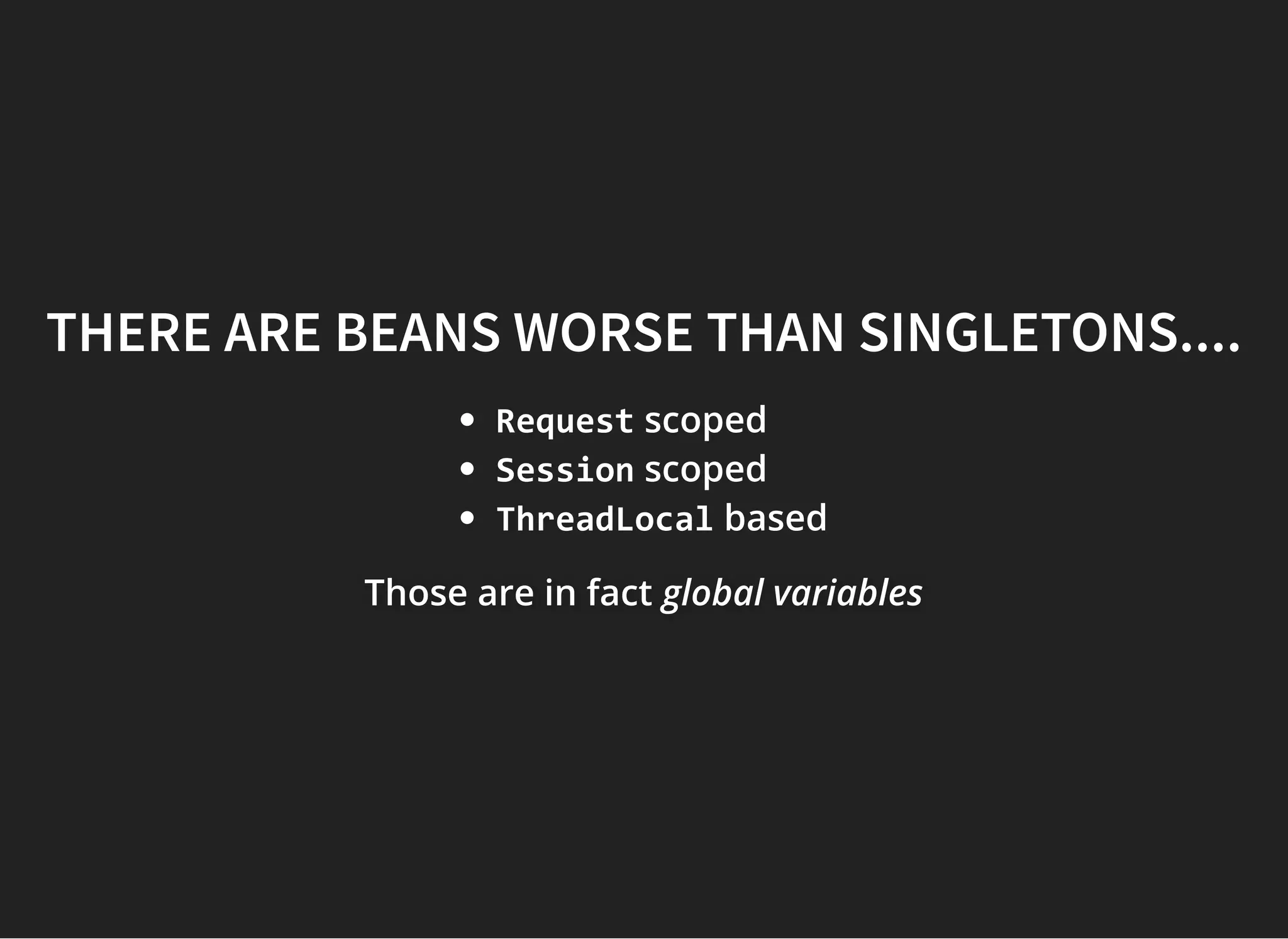
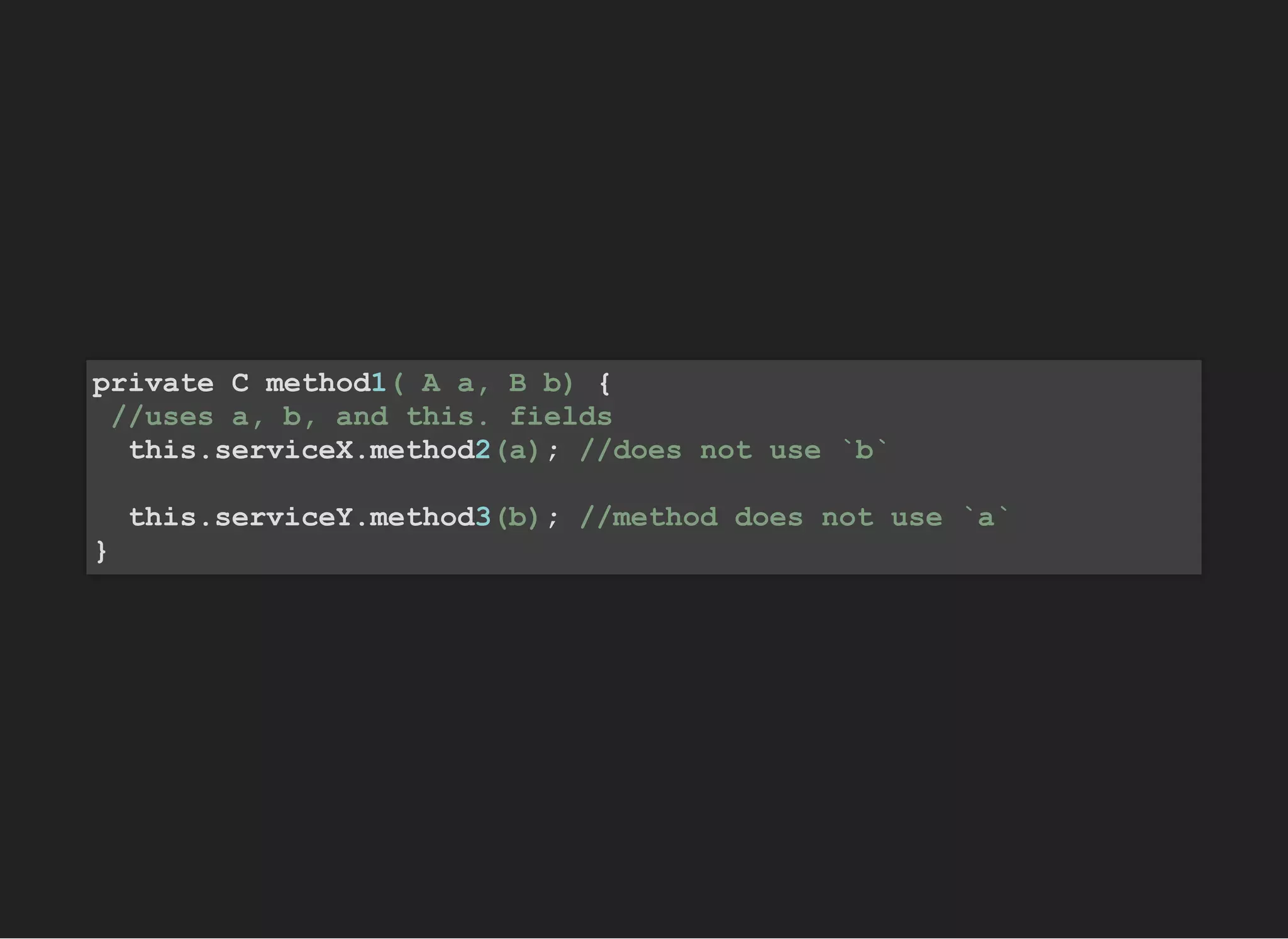
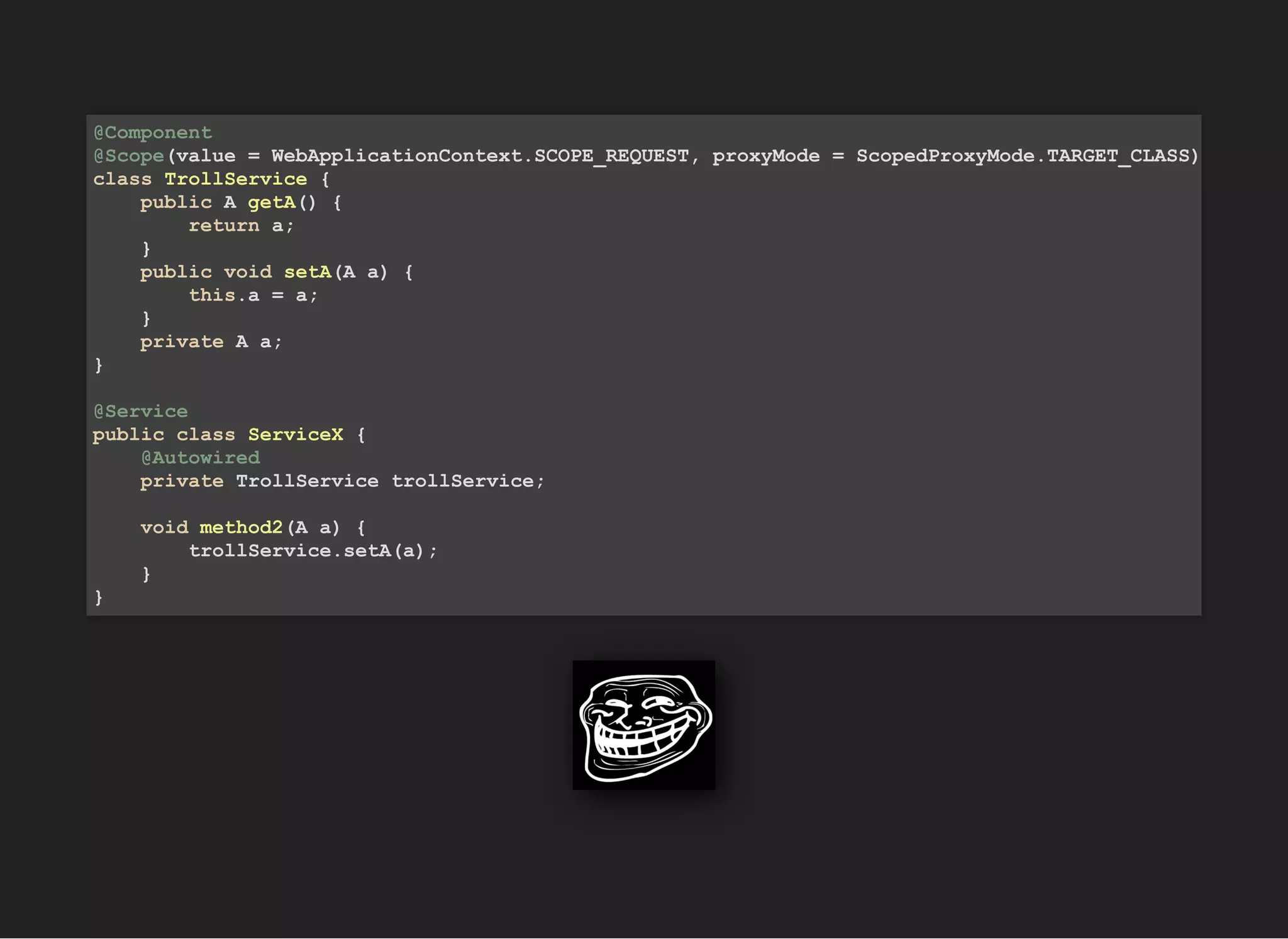
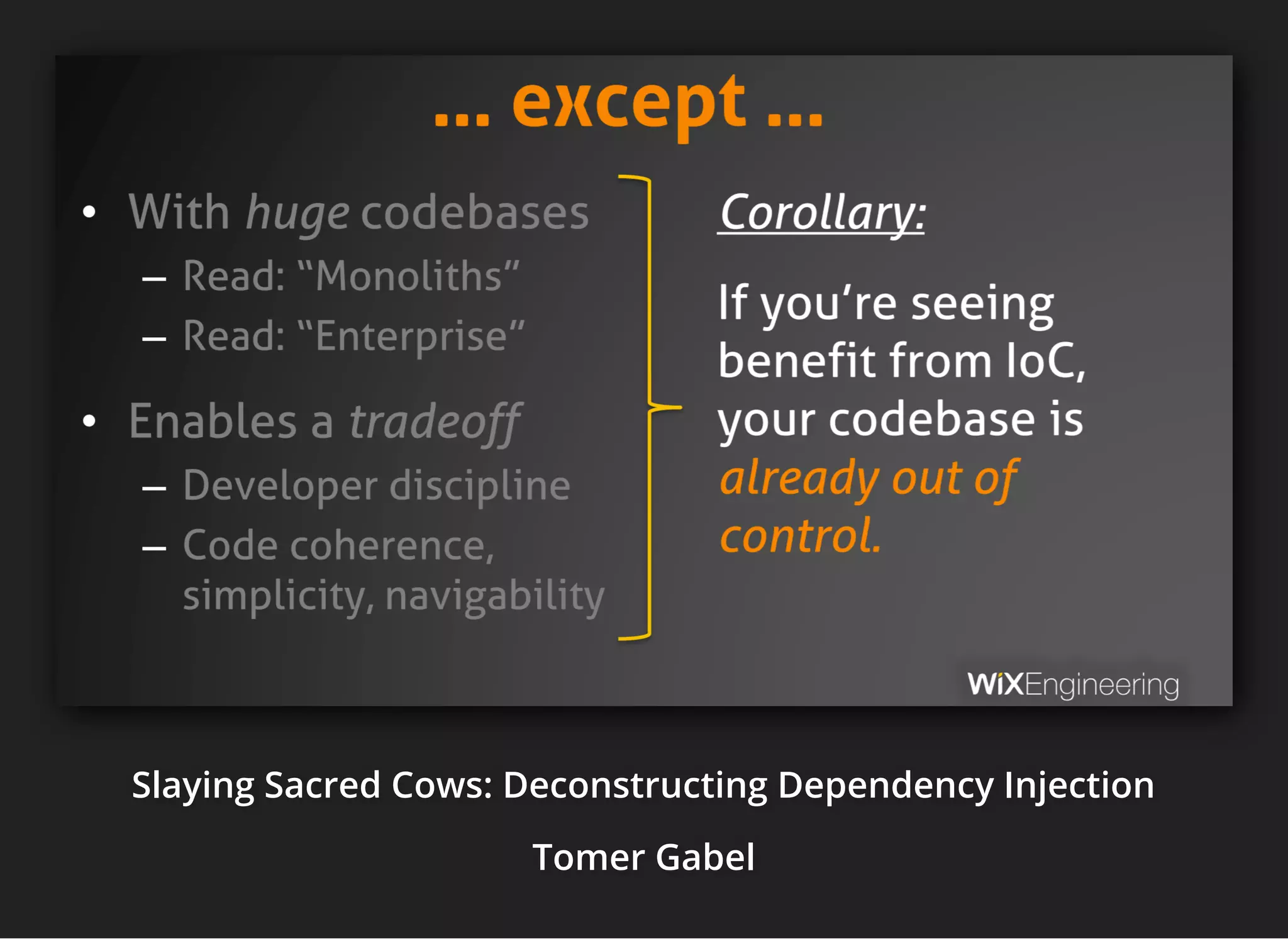
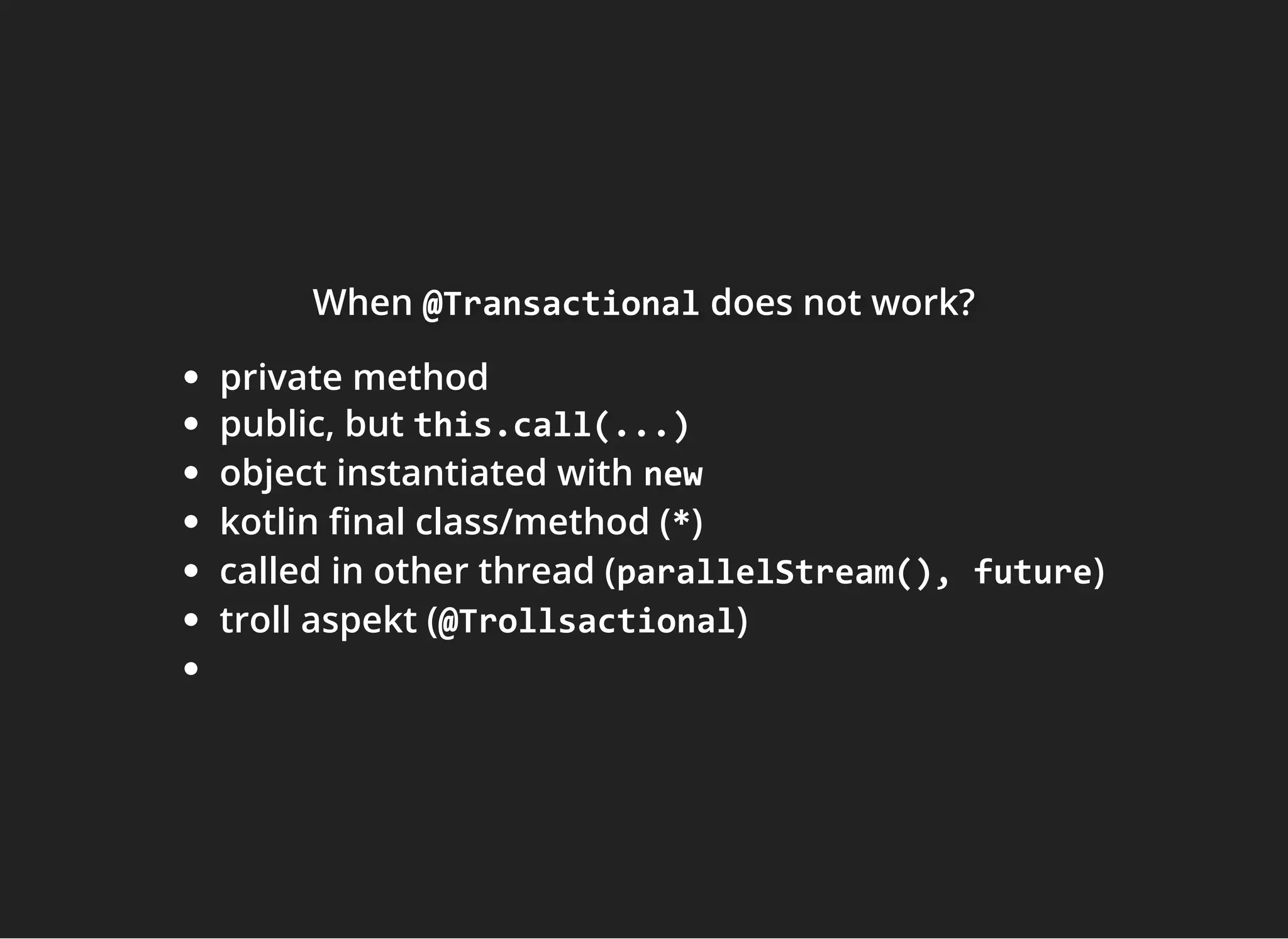
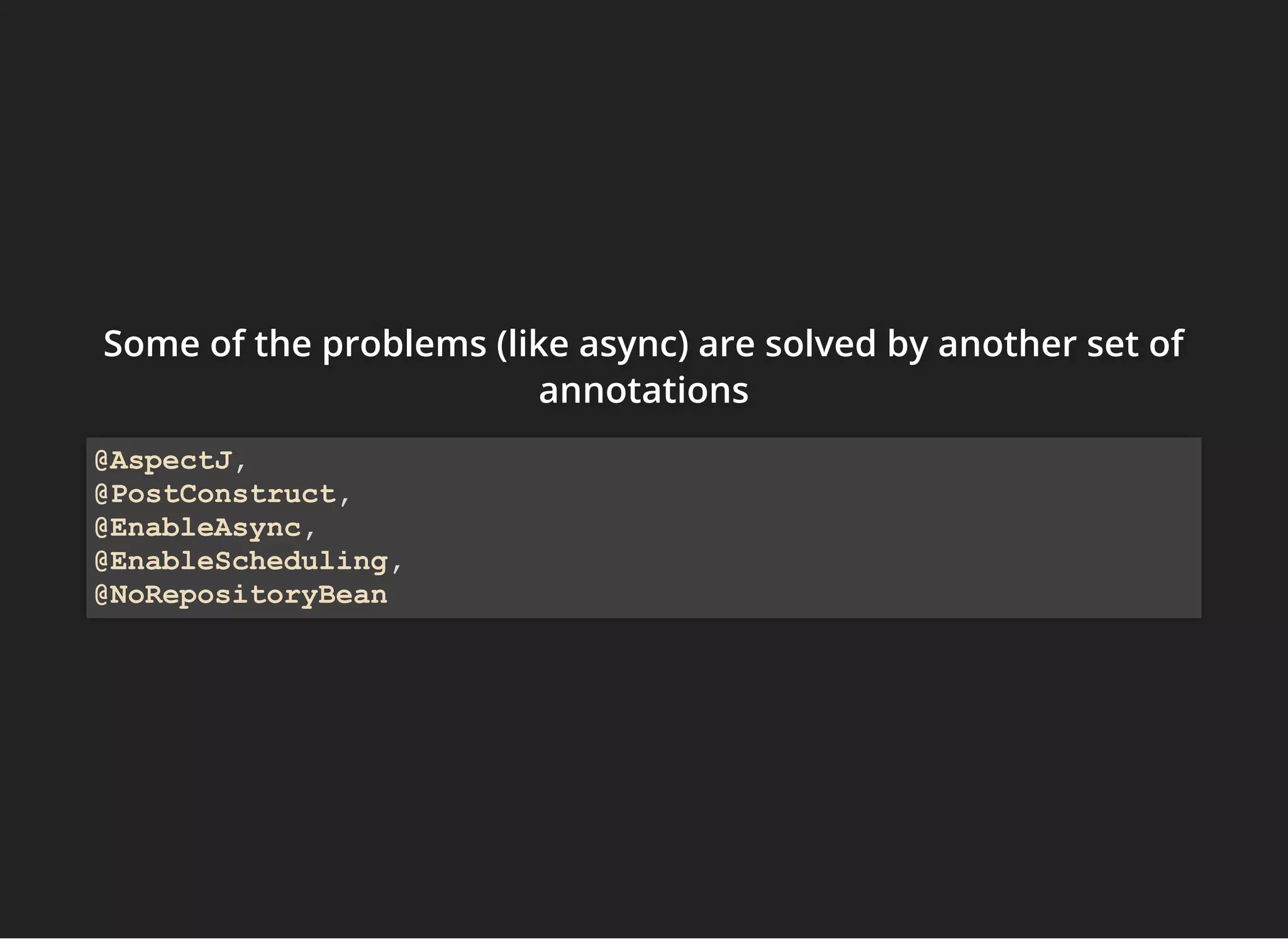
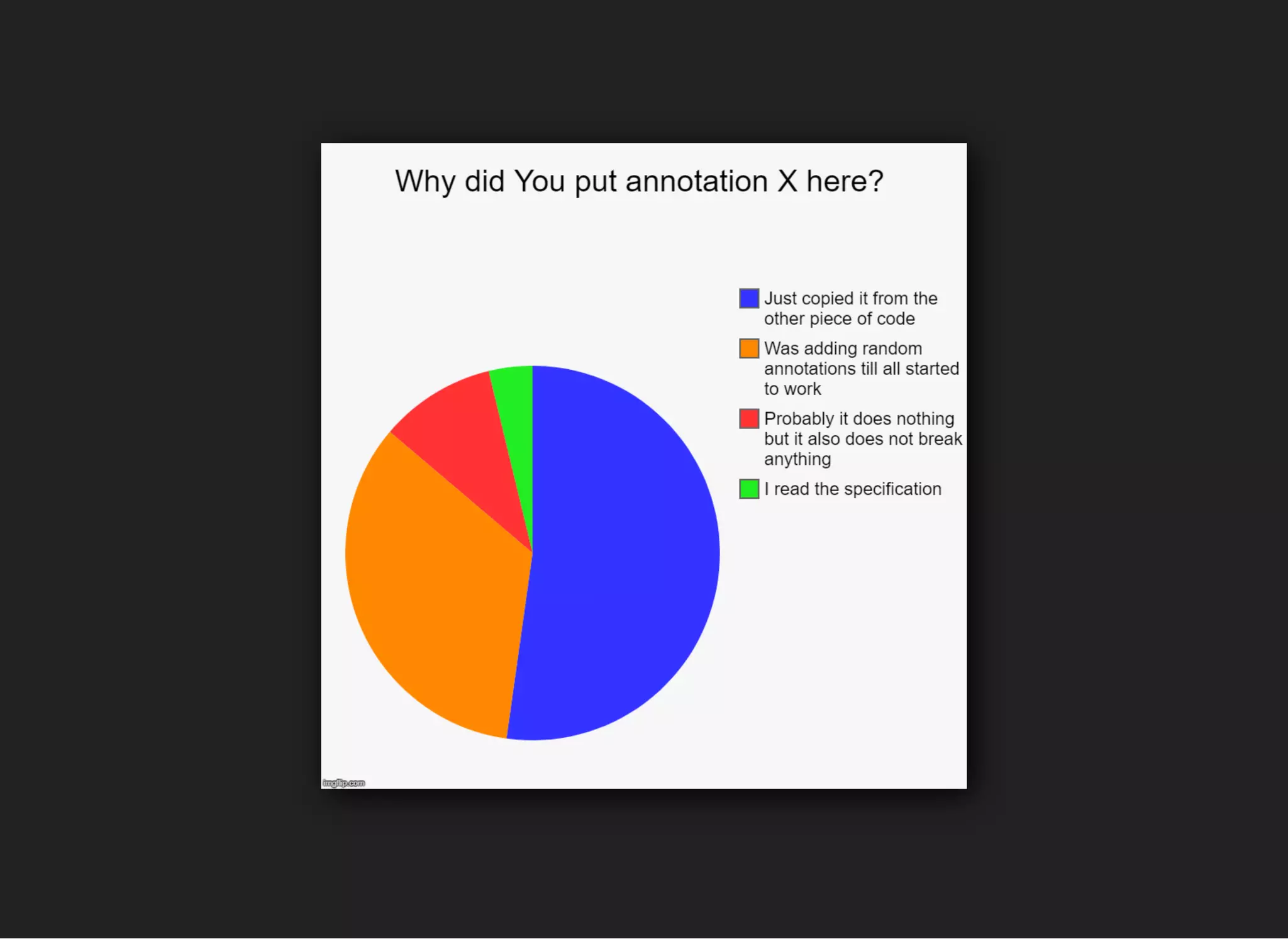
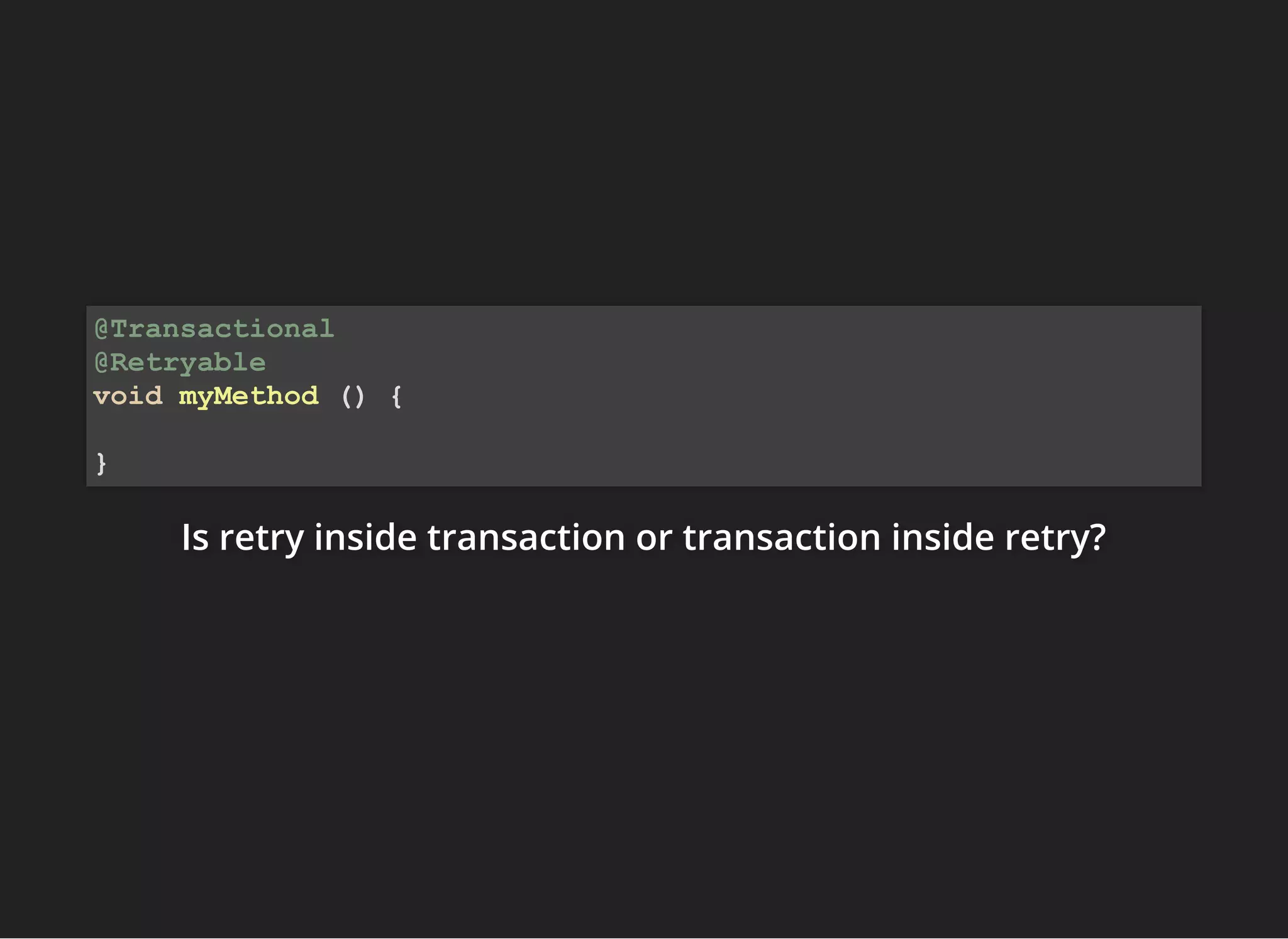
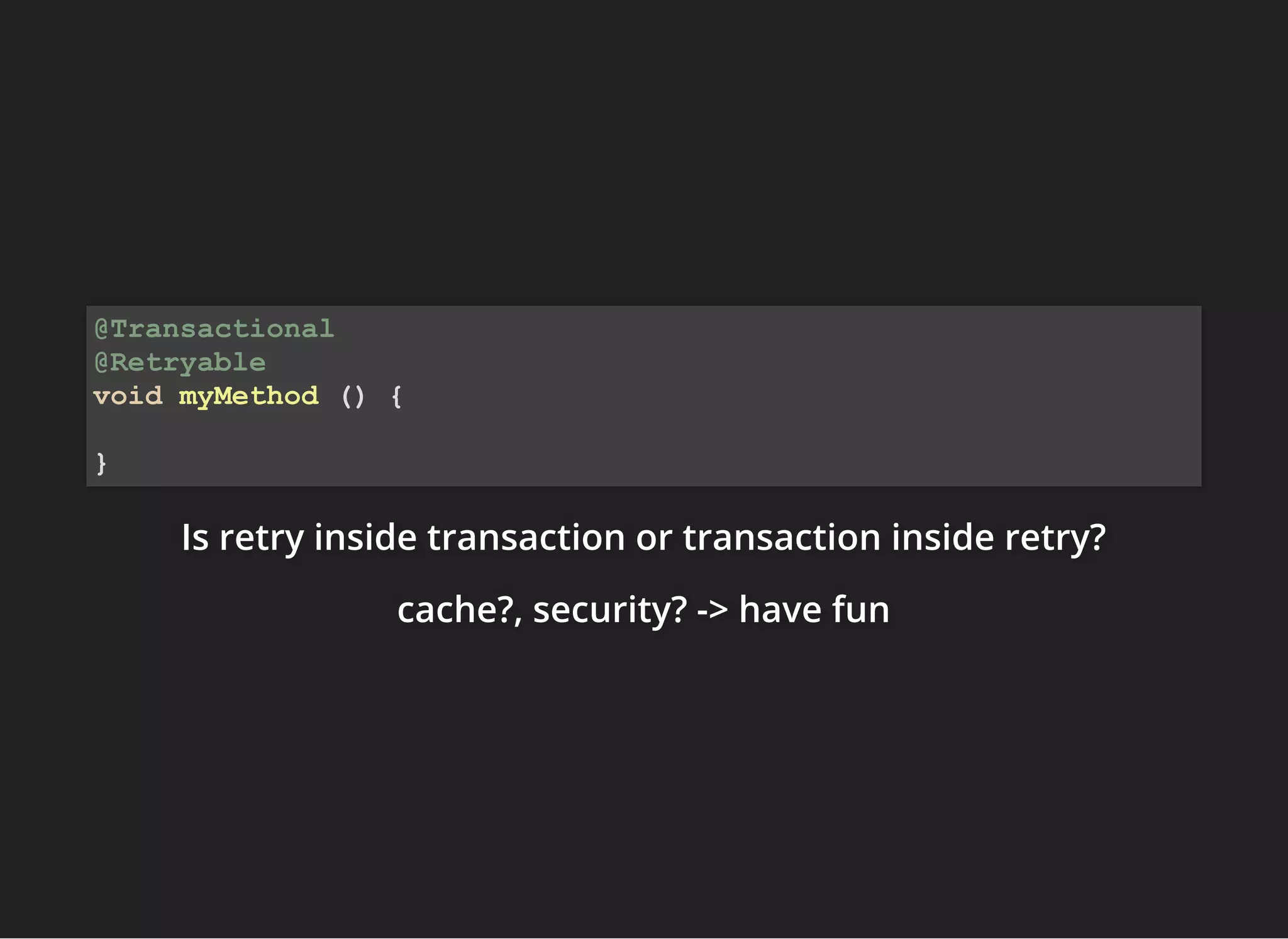
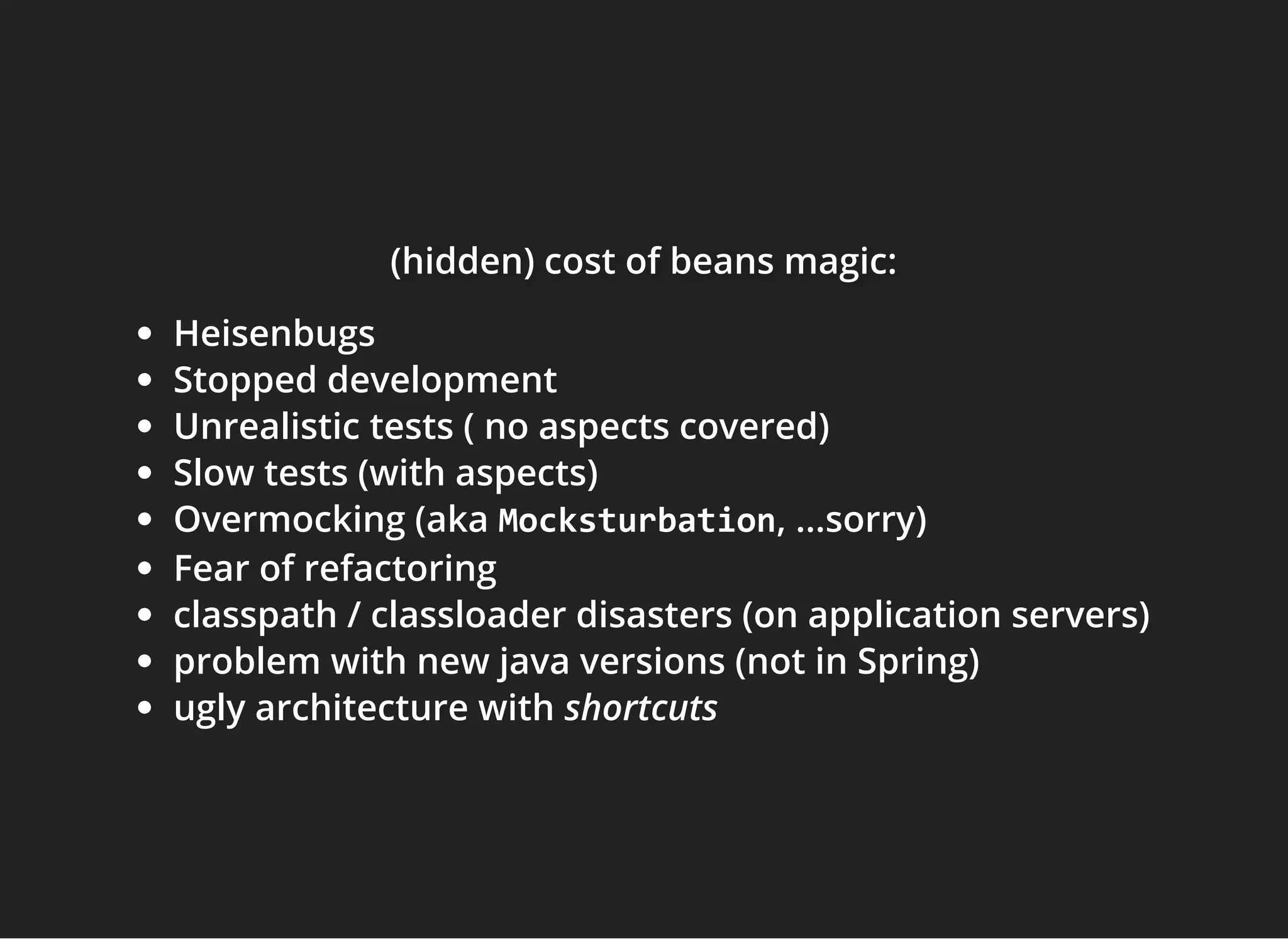
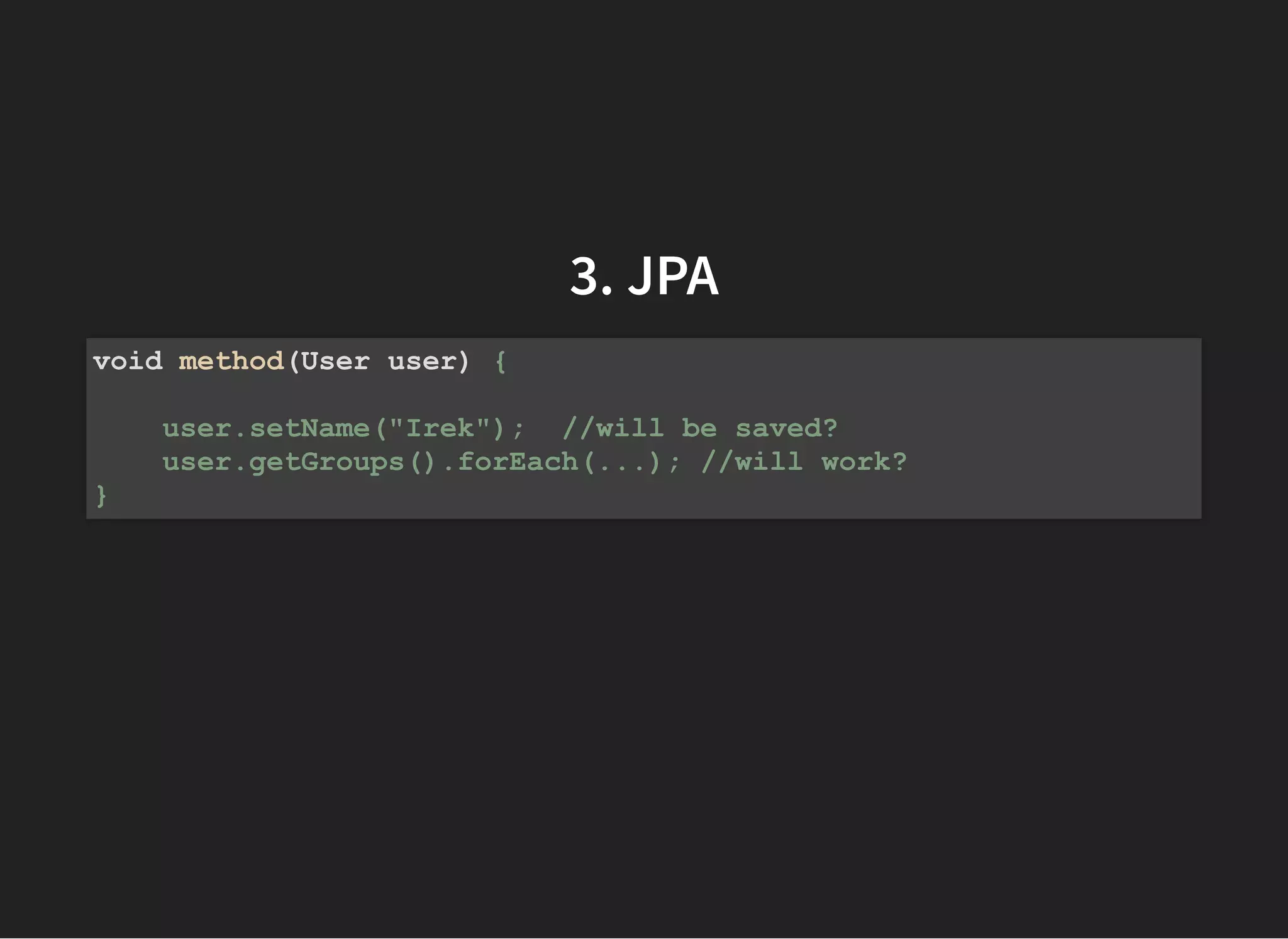
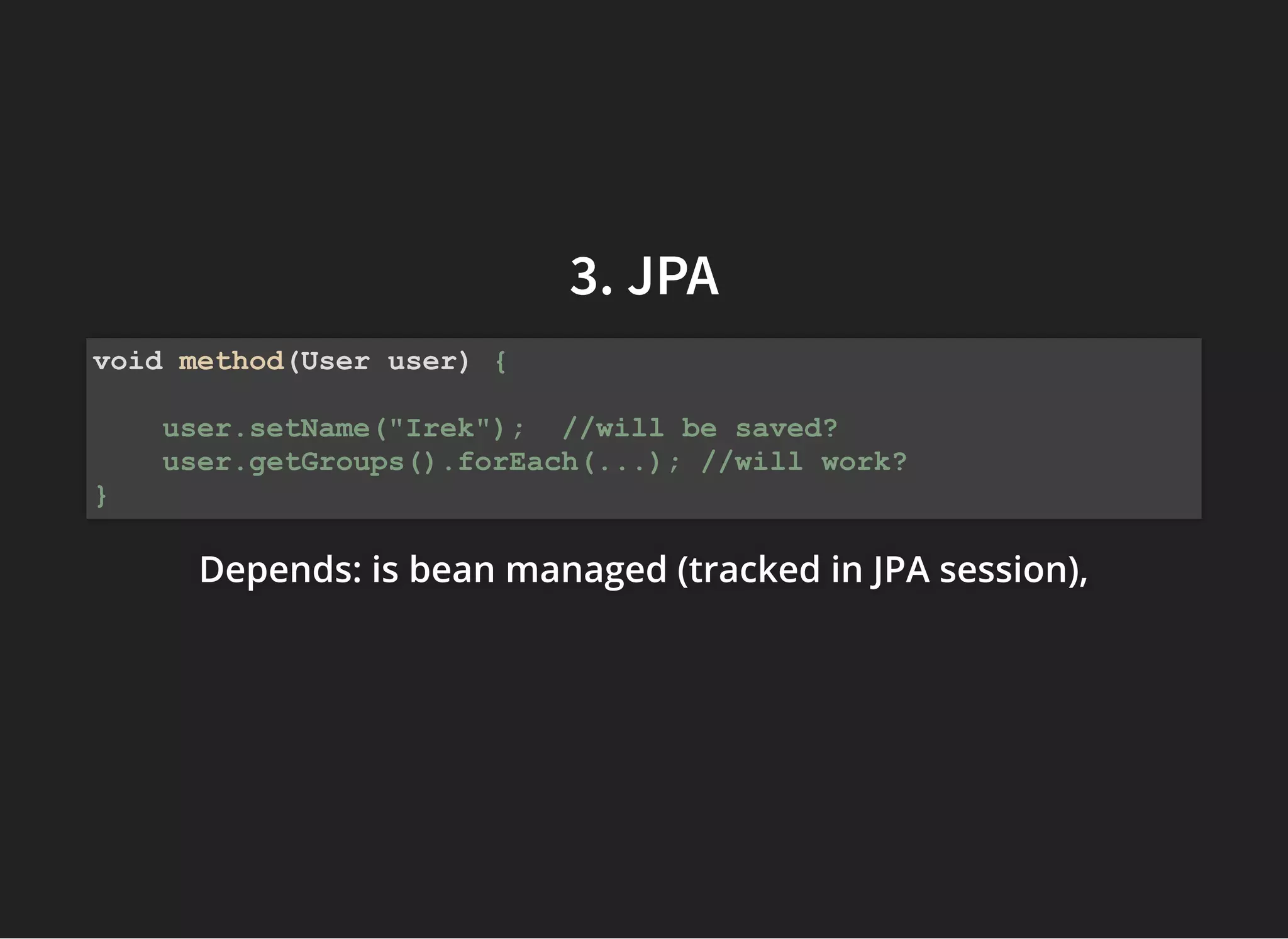
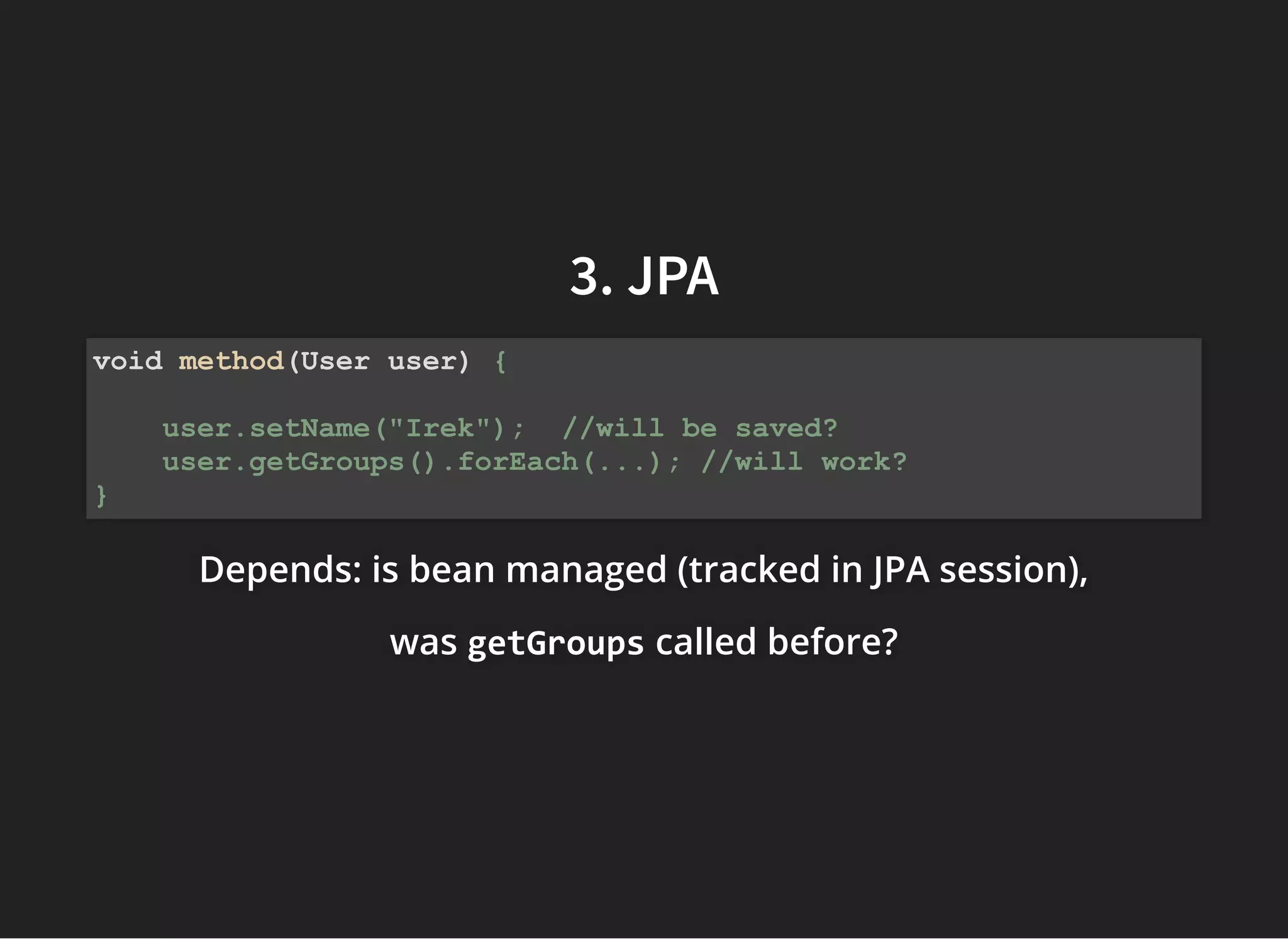
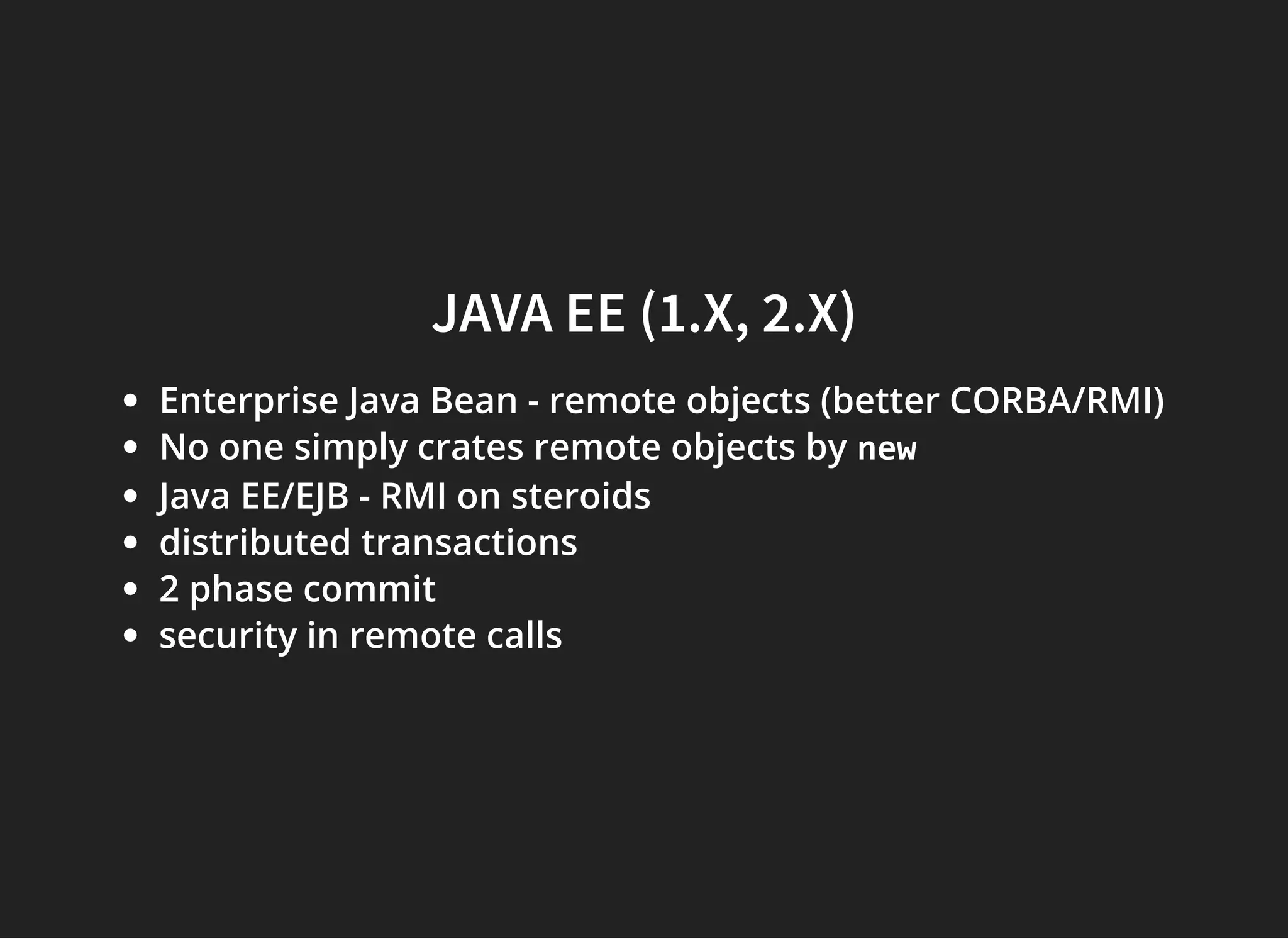
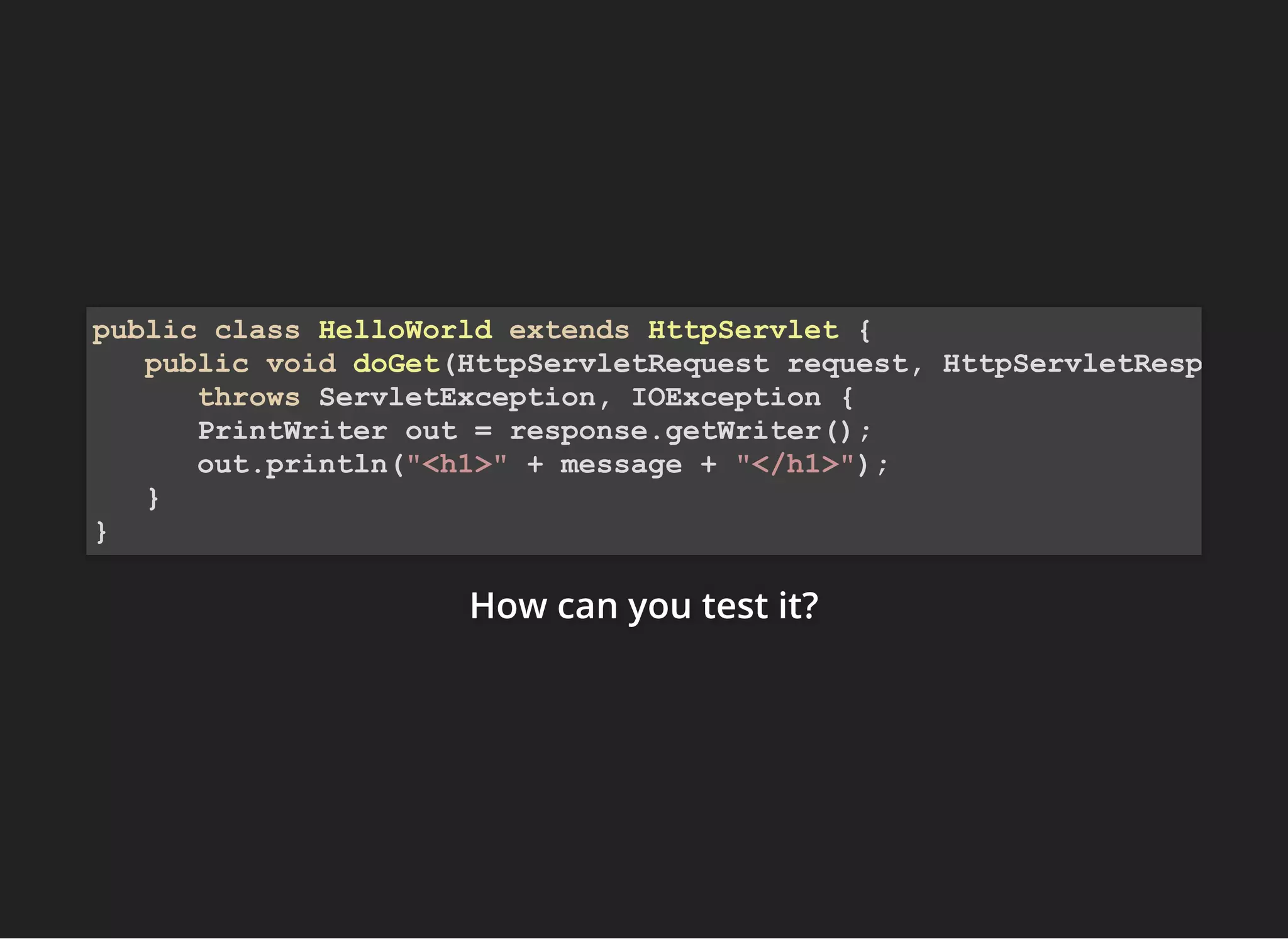
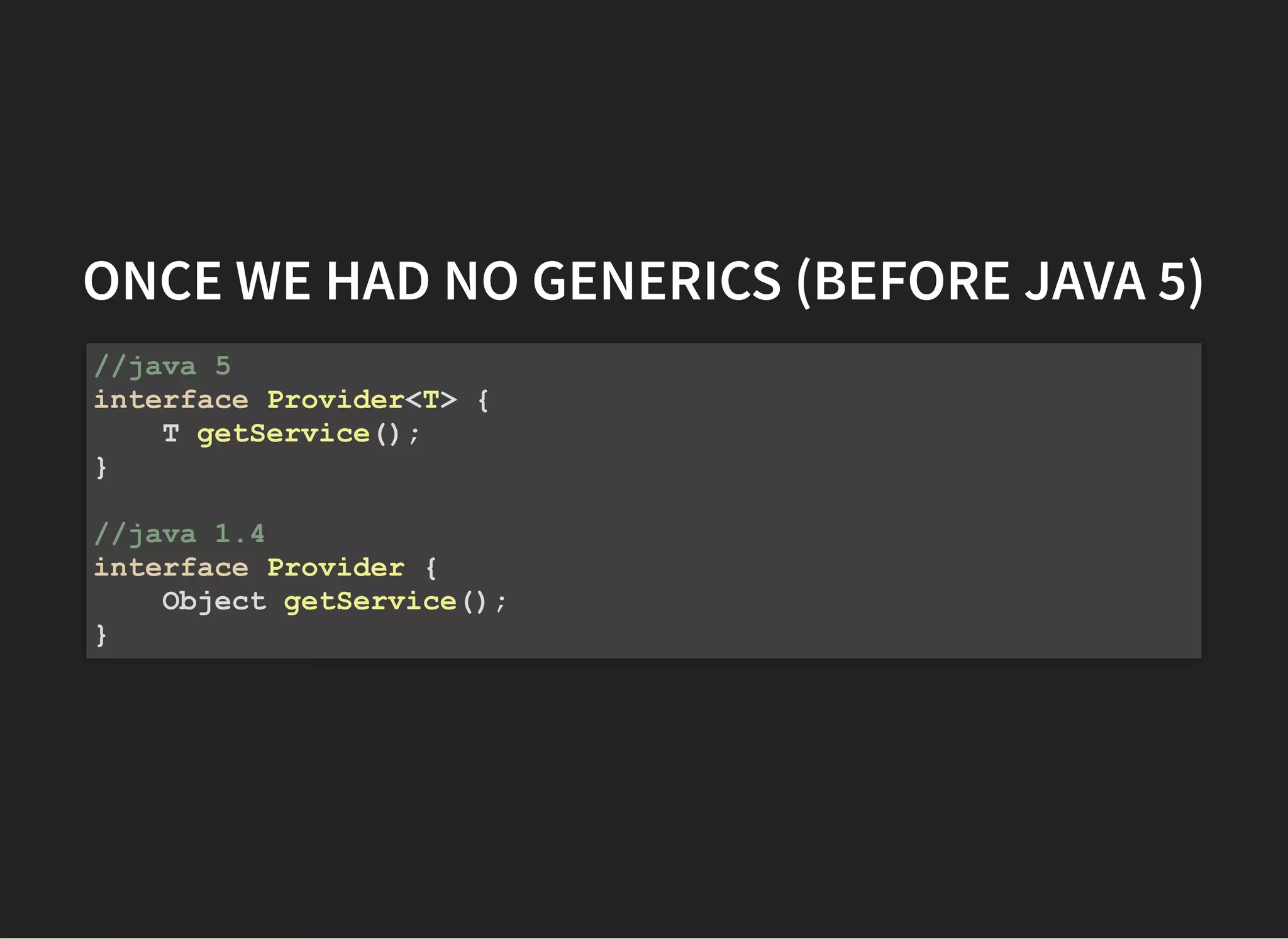
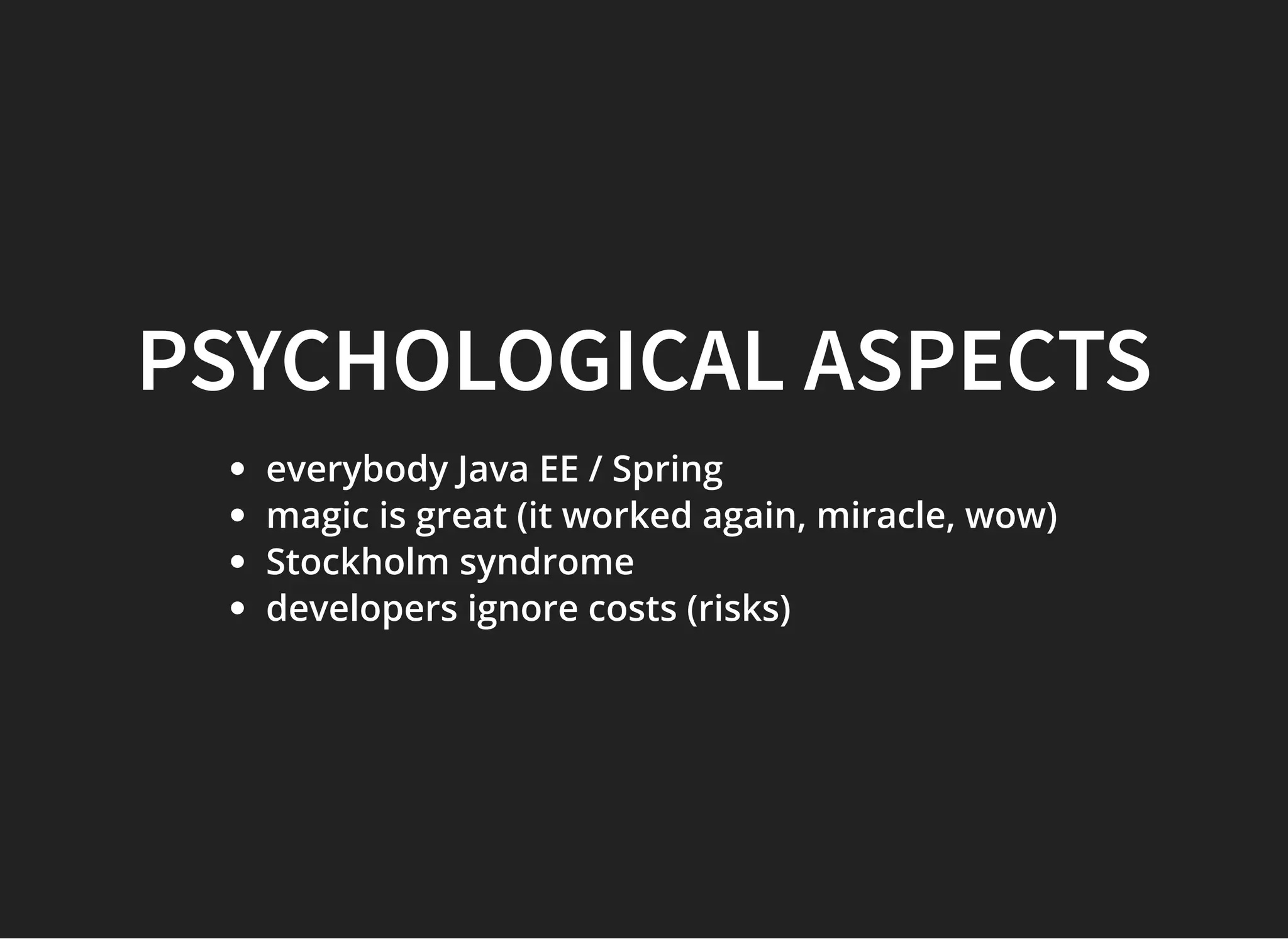
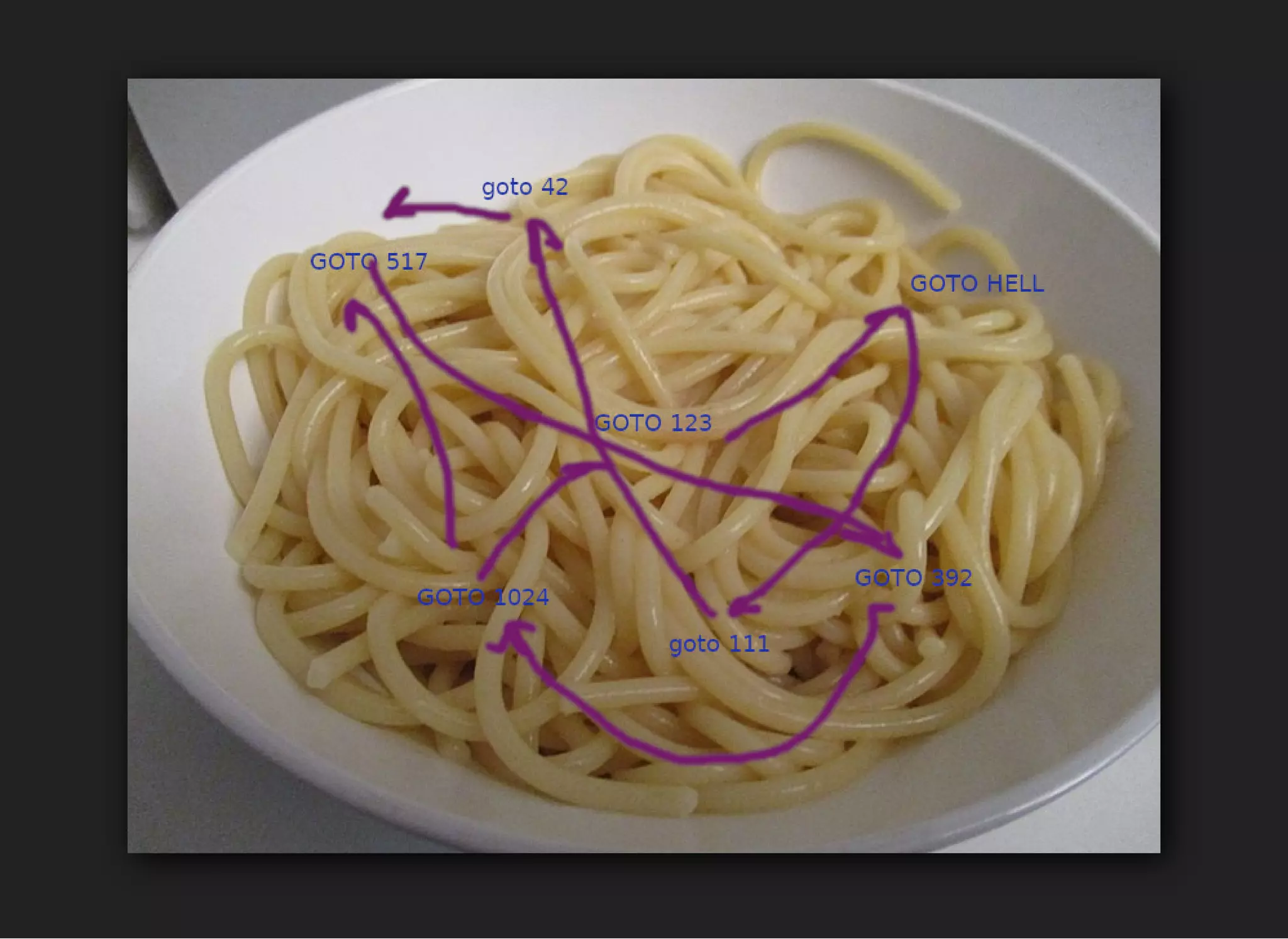
The document discusses the experiences and opinions of Jarek Ratajski, a software developer, on Java EE and Spring framework, emphasizing the challenges of concurrency, security, and performance in coding. It critiques the use of 'goto' statements and dependency injection in programming, suggesting they can complicate code architecture and create technical debt. The discussion also touches upon the conception of beans in Java and their limitations in software design.

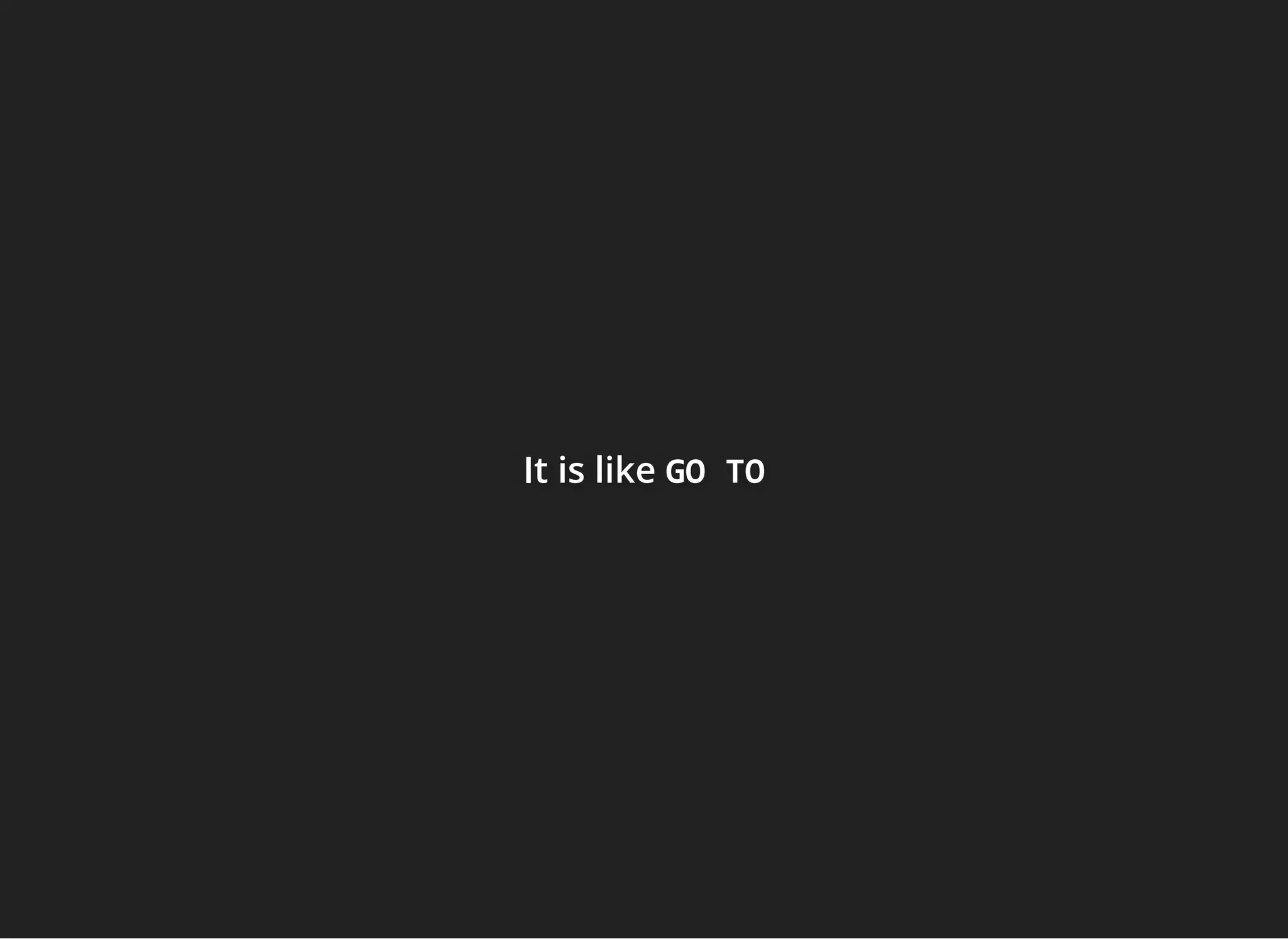
![somesomesome C# .NetC# .NetC# .Net code presented to proove howcode presented to proove howcode presented to proove how COOLCOOLCOOL goto is (at polishgoto is (at polishgoto is (at polish
4programmers message board)4programmers message board)4programmers message board)
private static bool TryParseSByteD(ReadOnlySpan<byte> source, out sbyte value, out int bytesConsumed)
{
if (source.Length < 1)
goto FalseExit;
int sign = 1;
int index = 0;
int num = source[index];
if (num == '-')
{
sign = -1;
index++;
if ((uint)index >= (uint)source.Length)
goto FalseExit;
num = source[index];
}
else if (num == '+')
{
index++;
if ((uint)index >= (uint)source.Length)
goto FalseExit;
num = source[index];
}
int answer = 0;
if (ParserHelpers.IsDigit(num))
{
if (num == '0')
{
do
{
index++;
if ((uint)index >= (uint)source.Length)
goto Done;
num = source[index];
} while (num == '0');
if (!ParserHelpers.IsDigit(num))
goto Done;
}
answer = num - '0';
index++;
if ((uint)index >= (uint)source.Length)
goto Done;
num = source[index];
if (!ParserHelpers.IsDigit(num))
goto Done;
index++;
answer = 10 * answer + num - '0';
// Potential overflow
if ((uint)index >= (uint)source.Length)
goto Done;
num = source[index];](https://image.slidesharecdn.com/springgoodpart-191130132652/75/Spring-CDI-Jakarta-EE-good-parts-23-2048.jpg)
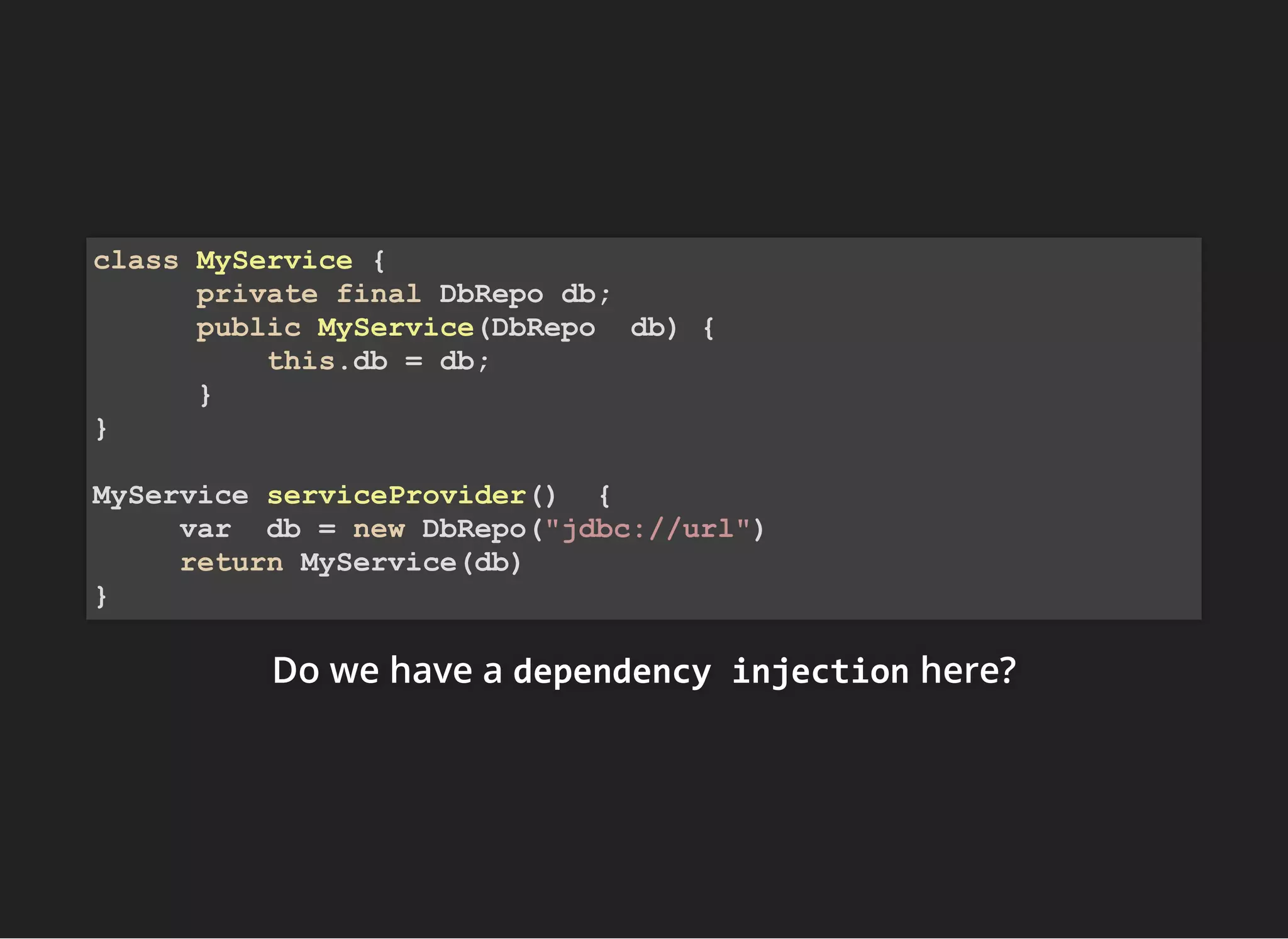
![WikipediaWikipediaWikipedia
In software engineering, dependency injection is aIn software engineering, dependency injection is aIn software engineering, dependency injection is a
technique whereby one object supplies thetechnique whereby one object supplies thetechnique whereby one object supplies the
dependencies of another object. A "dependency" isdependencies of another object. A "dependency" isdependencies of another object. A "dependency" is
an object that can be used, for example a service.an object that can be used, for example a service.an object that can be used, for example a service.
Instead of a client specifying which service it willInstead of a client specifying which service it willInstead of a client specifying which service it will
use, something tells the client what service to use.use, something tells the client what service to use.use, something tells the client what service to use.
The "injection" refers to the passing of a dependencyThe "injection" refers to the passing of a dependencyThe "injection" refers to the passing of a dependency
(a service) into the object (a client) that would use it.(a service) into the object (a client) that would use it.(a service) into the object (a client) that would use it.
The service is made part of the client's state.[1]The service is made part of the client's state.[1]The service is made part of the client's state.[1]
Passing the service to the client, rather thanPassing the service to the client, rather thanPassing the service to the client, rather than
allowing a client to build or nd the service, is theallowing a client to build or nd the service, is theallowing a client to build or nd the service, is the
fundamental requirement of the pattern.fundamental requirement of the pattern.fundamental requirement of the pattern.](https://image.slidesharecdn.com/springgoodpart-191130132652/75/Spring-CDI-Jakarta-EE-good-parts-49-2048.jpg)