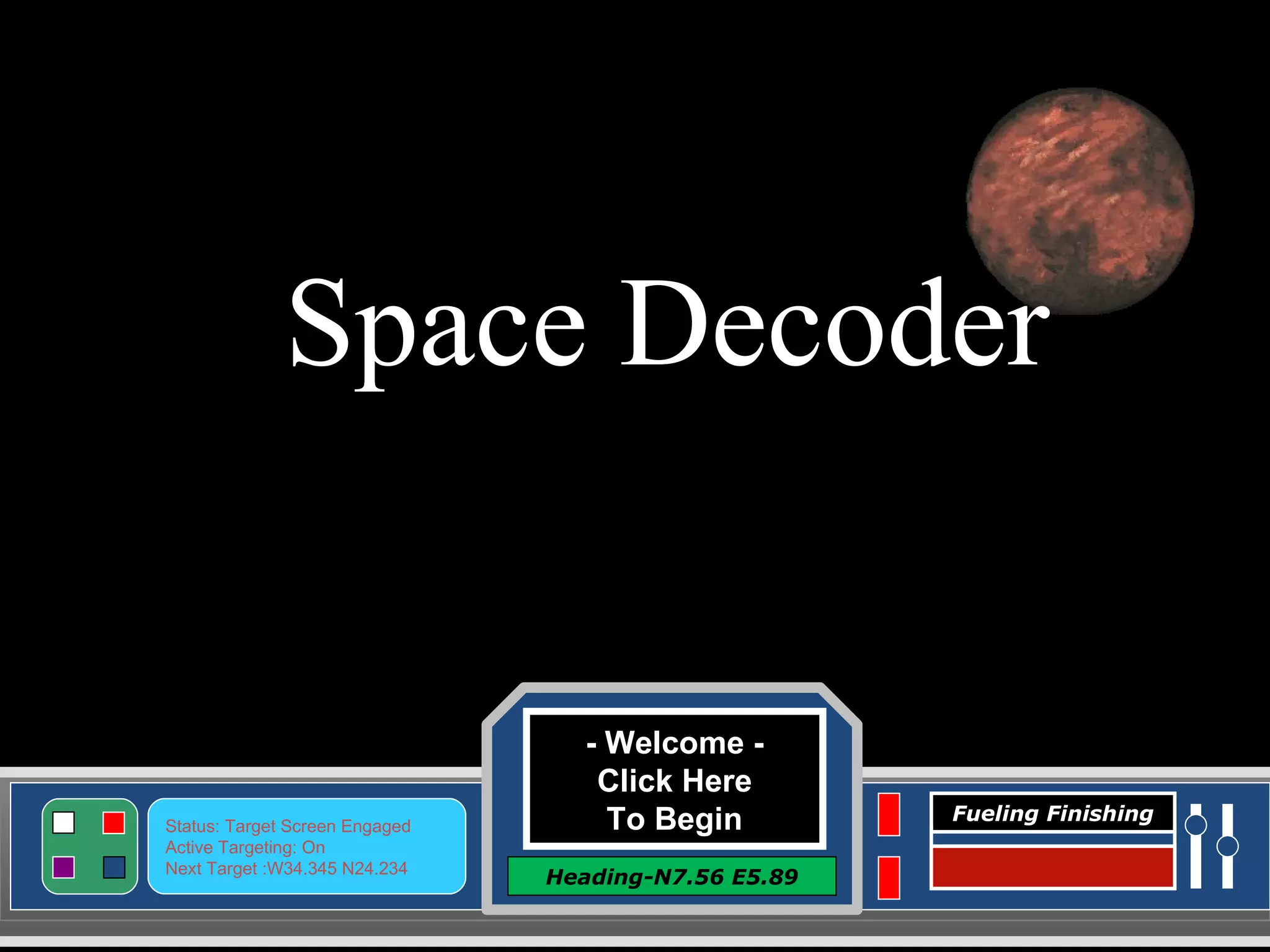
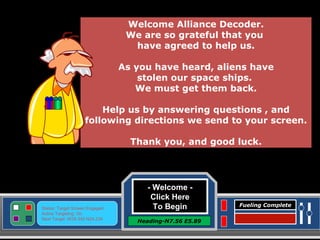
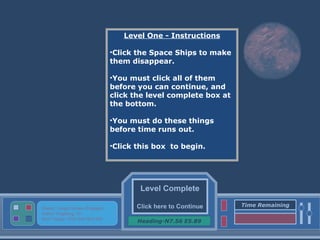
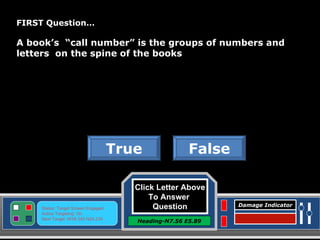
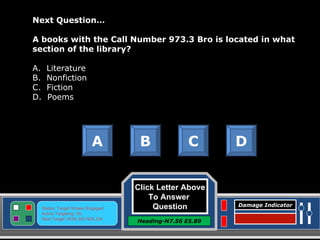
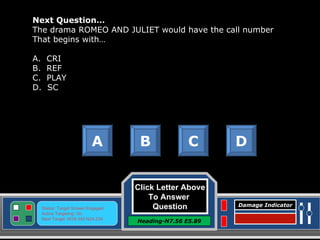
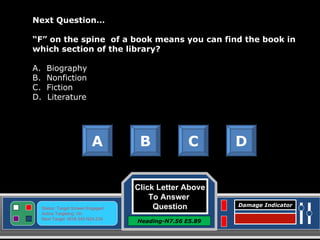
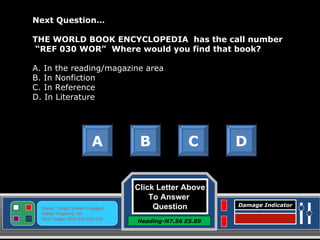
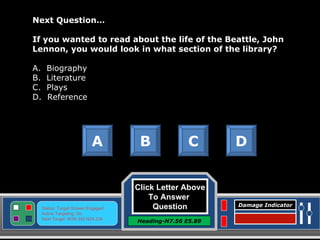
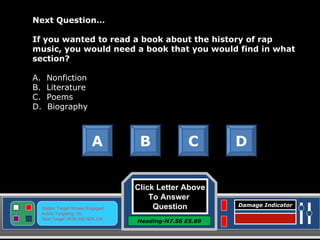
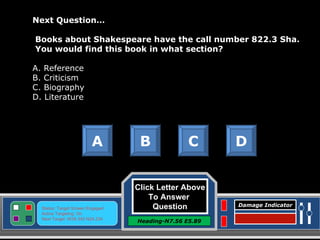
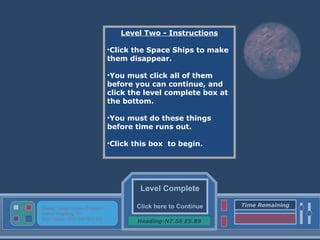
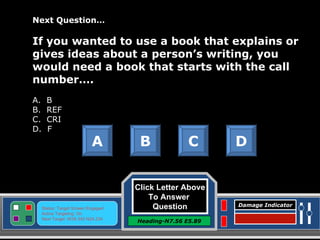
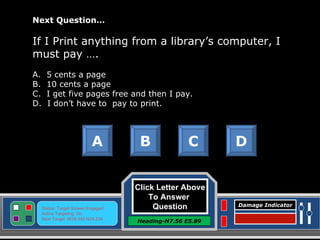
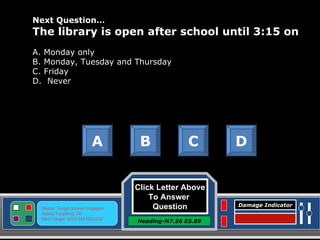
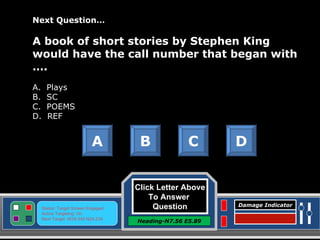
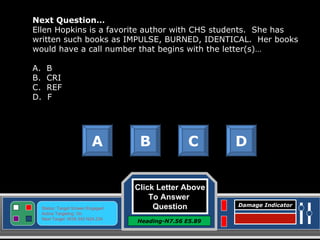
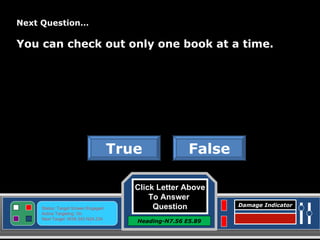
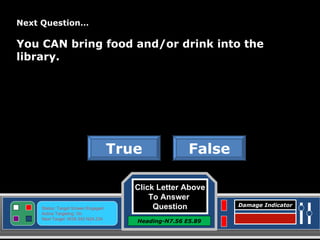
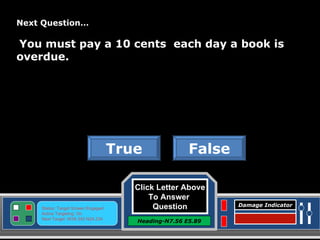
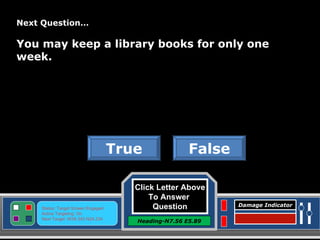
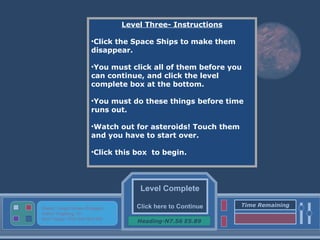
The document appears to be instructions for an interactive space-themed game or simulation. It guides the player through multiple levels where they must click on space ships before time runs out to complete the level. It also includes multiple choice questions about library organization and rules that the player must answer correctly. The overarching goal seems to be helping aliens retrieve stolen spaceships by completing levels and answering questions correctly.