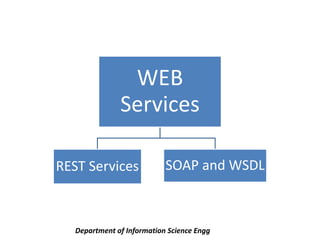
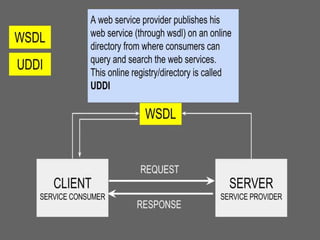
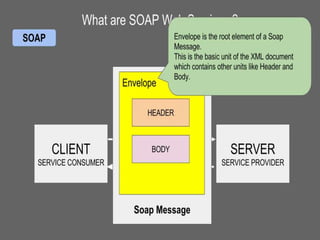
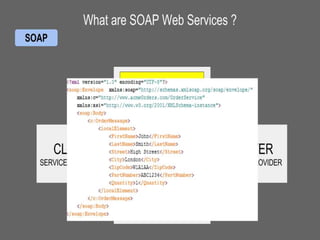
Web services allow applications to communicate over the World Wide Web. They convert applications into web-based applications that can publish functions for others to access globally. Common protocols for web services include SOAP, which uses XML messages over HTTP, and REST. WSDL describes web services by defining how they can be called, expected parameters, return data structures, and more. SOAP is a standard protocol that uses XML to exchange information for remote method calls over the internet in a platform-independent way.