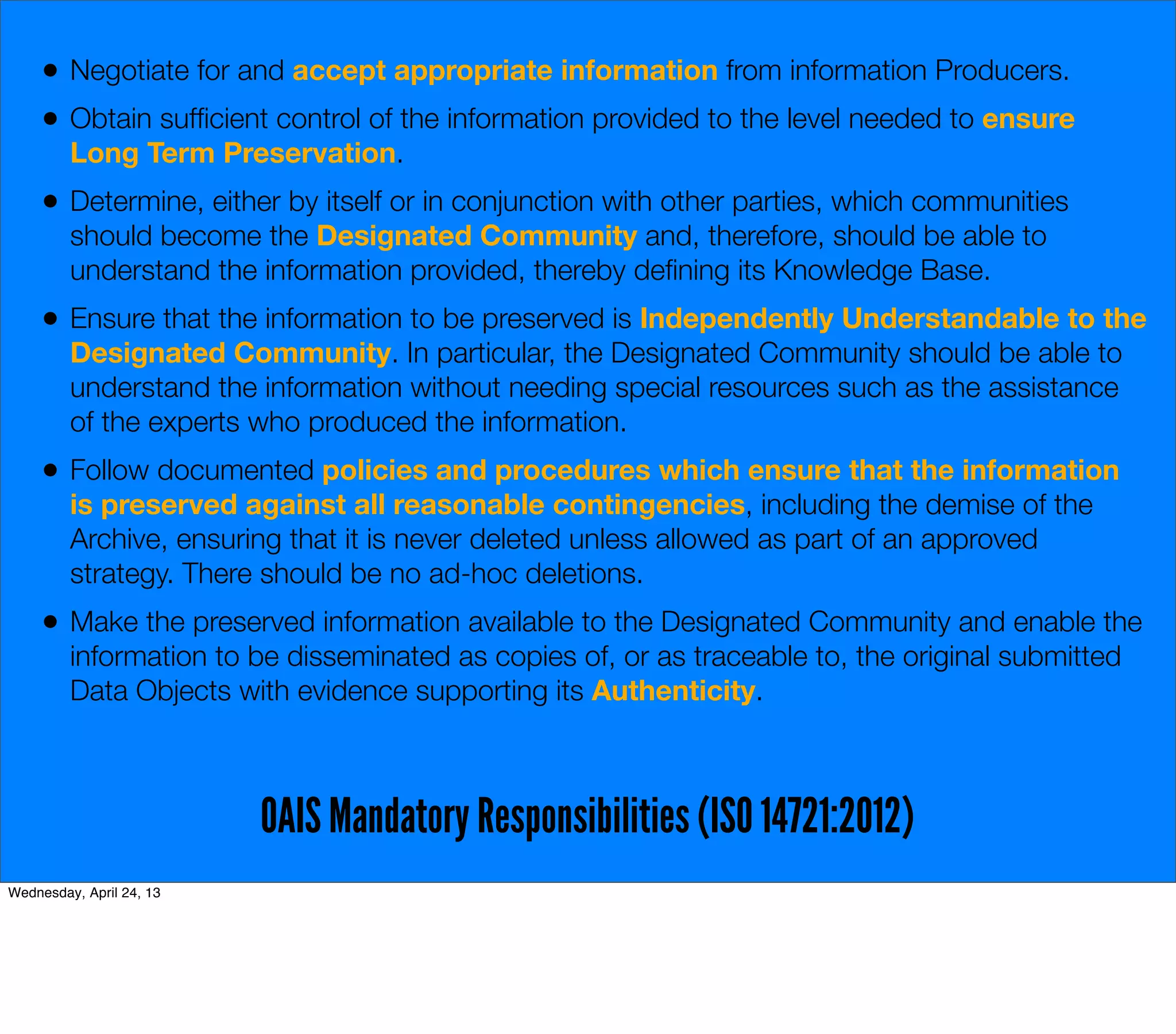
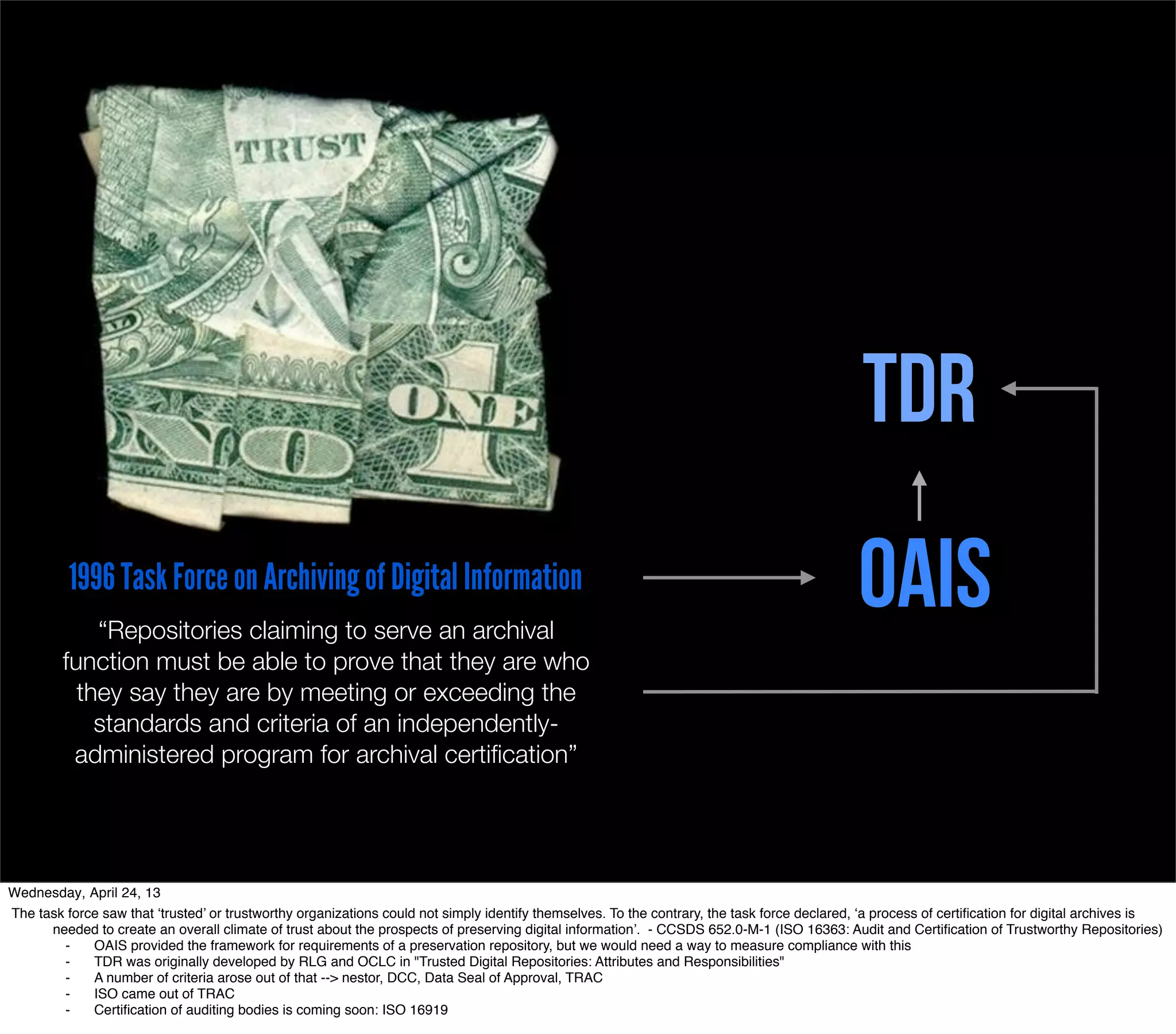
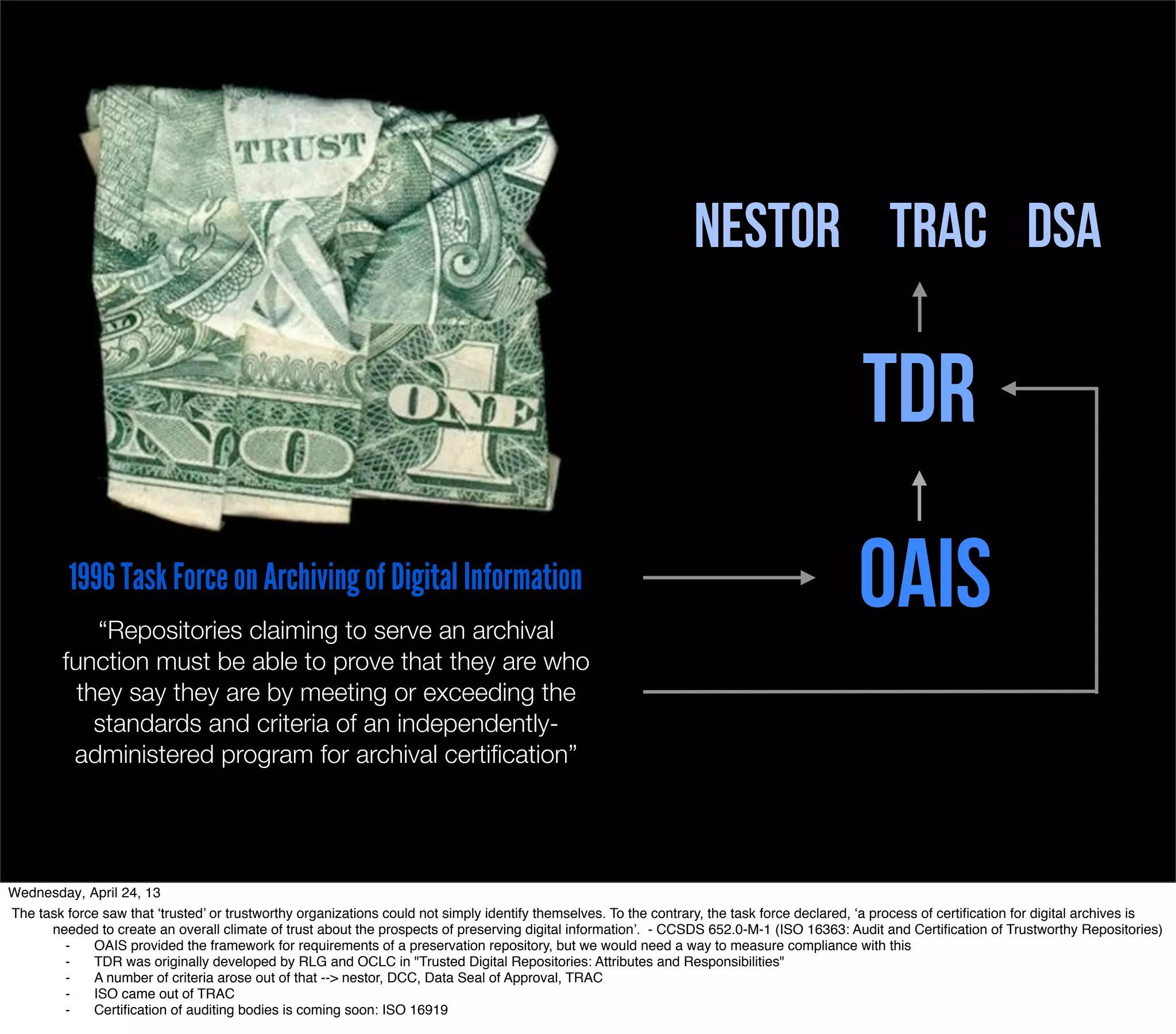
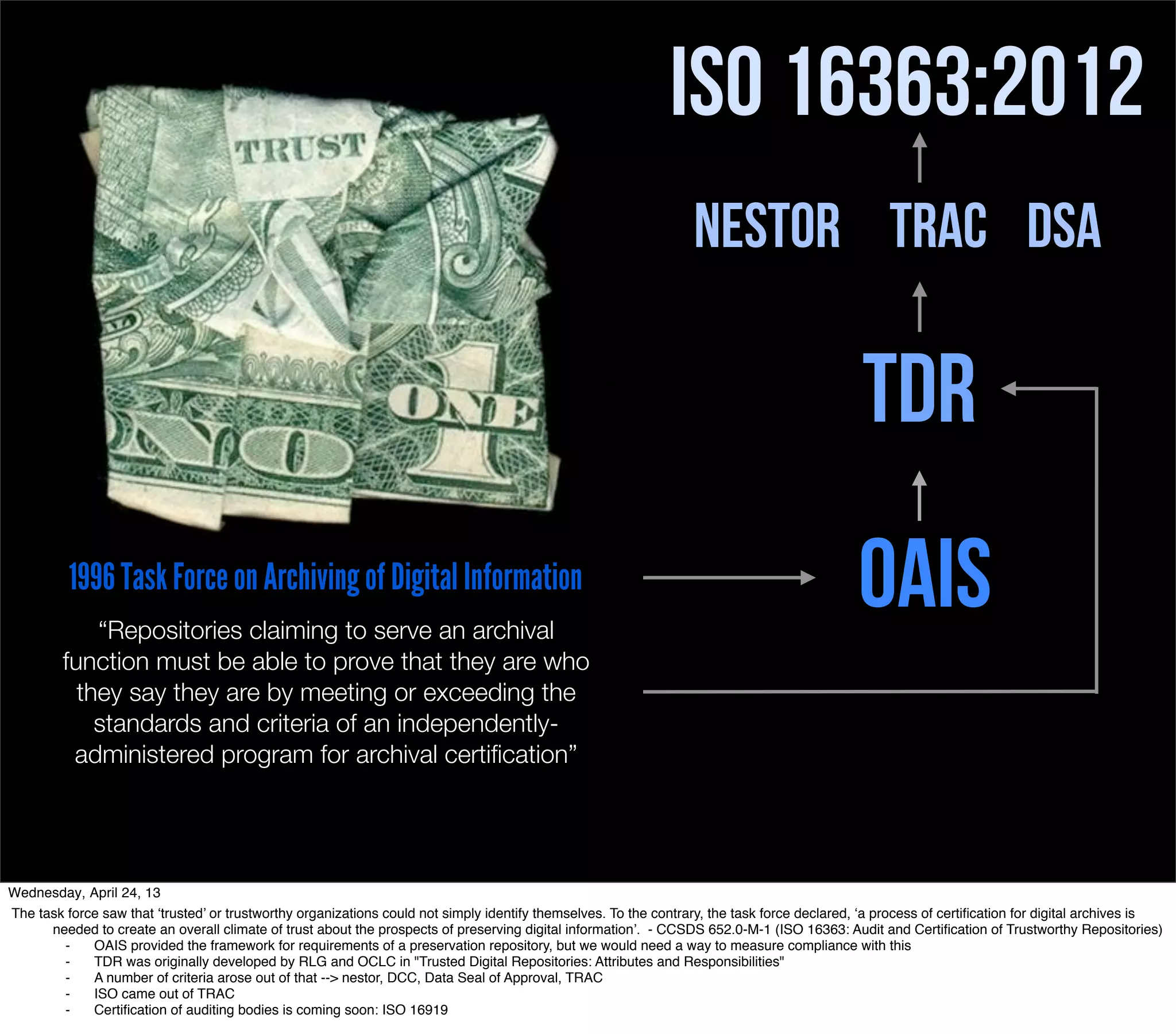
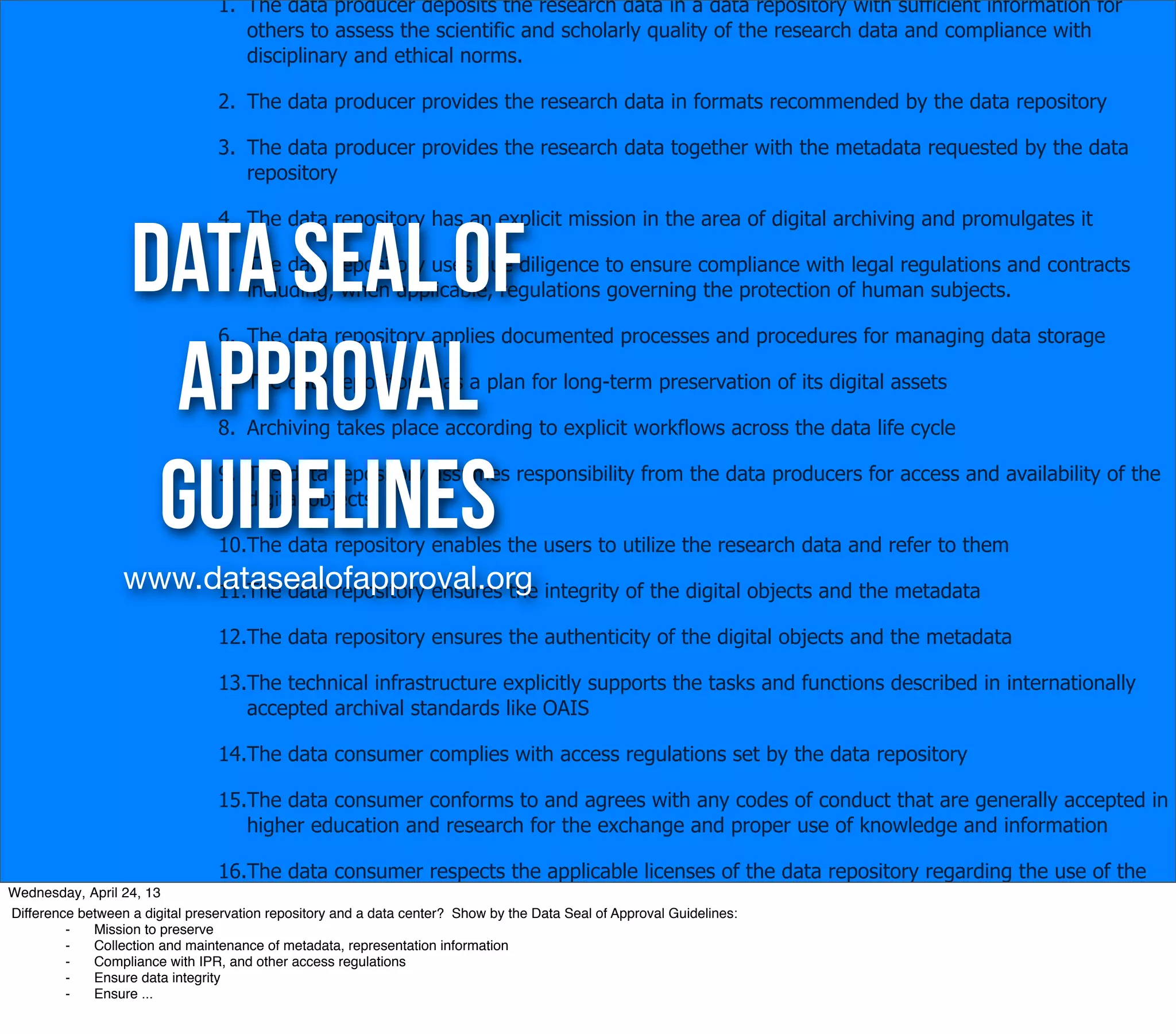
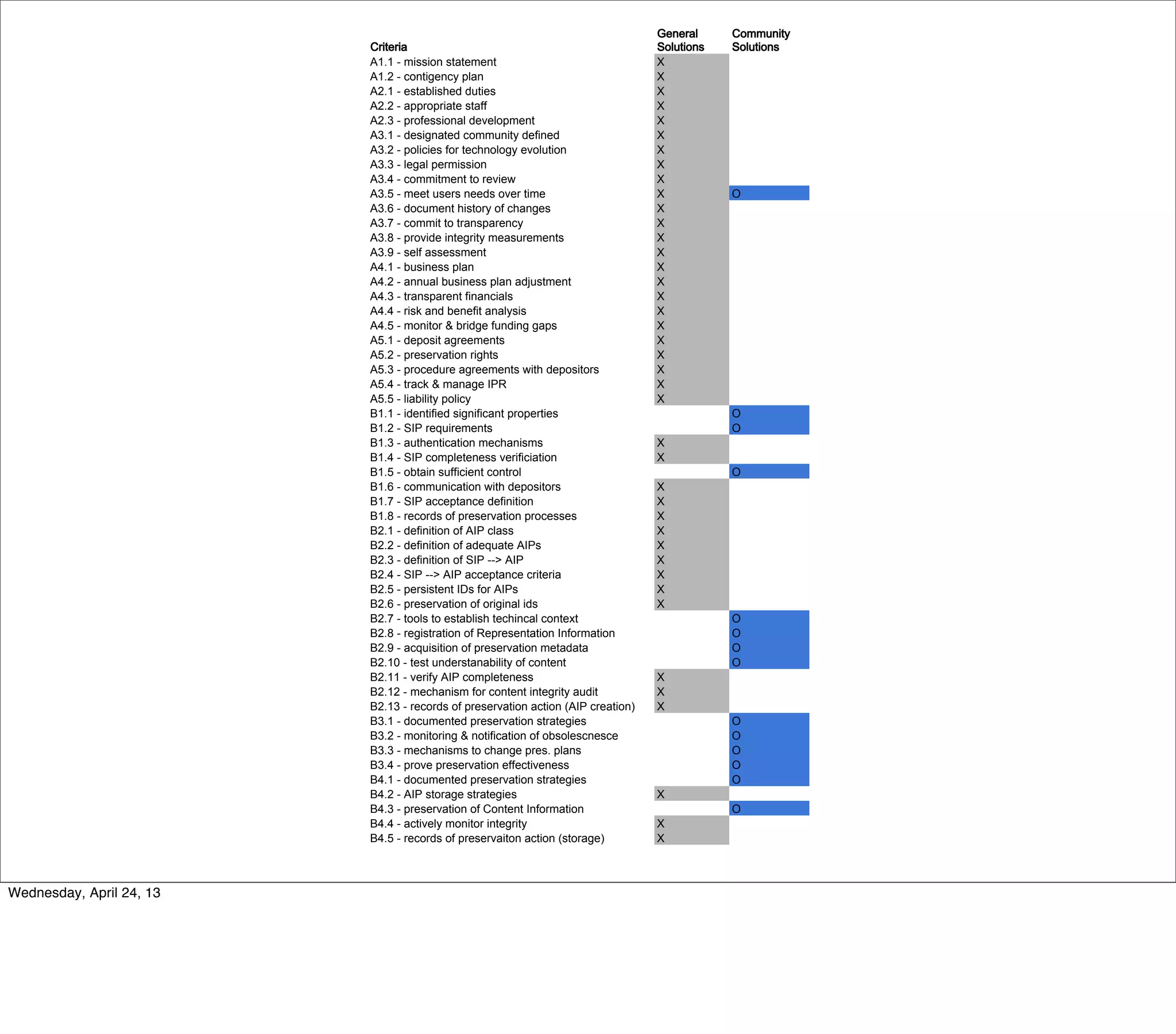
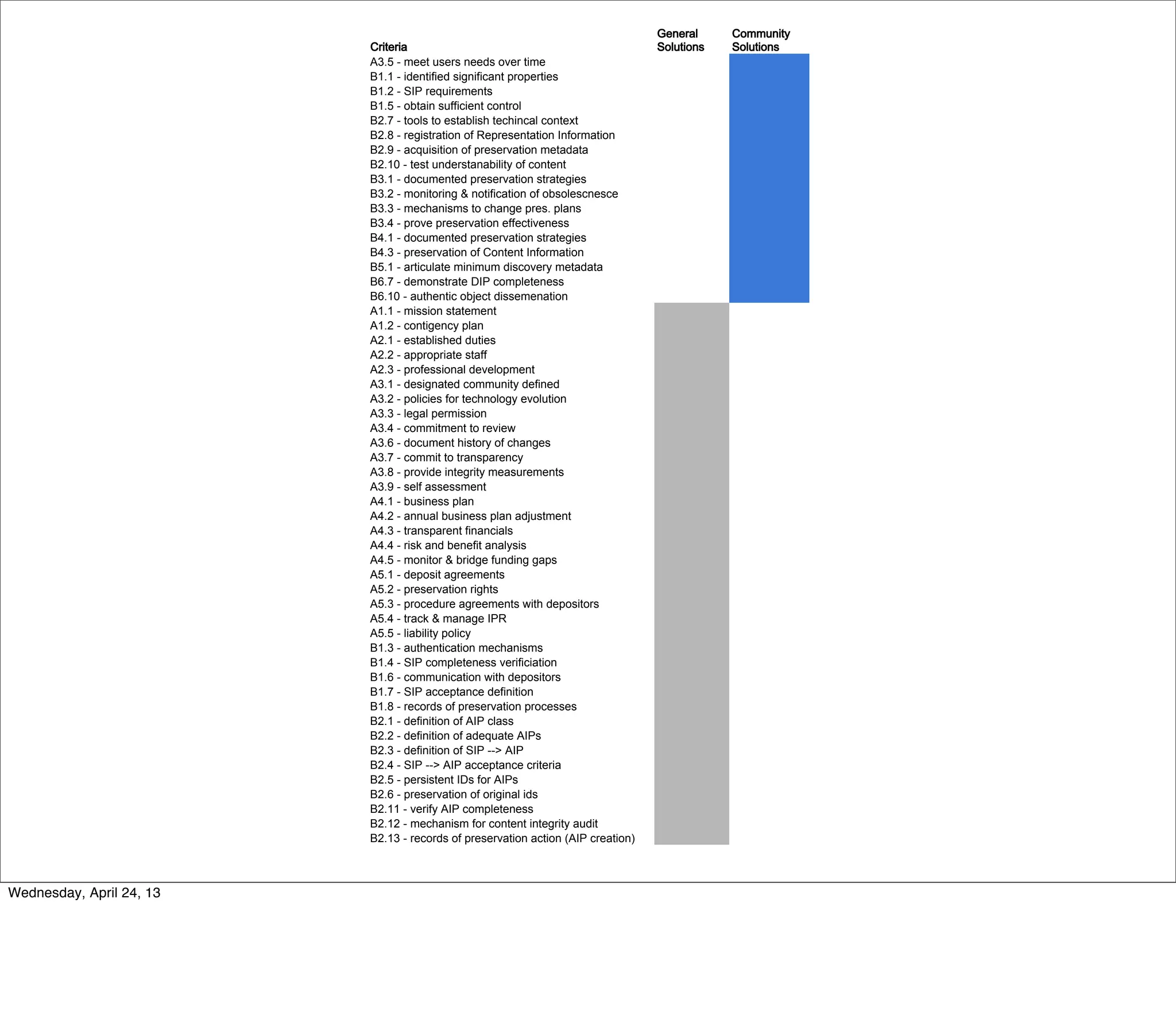
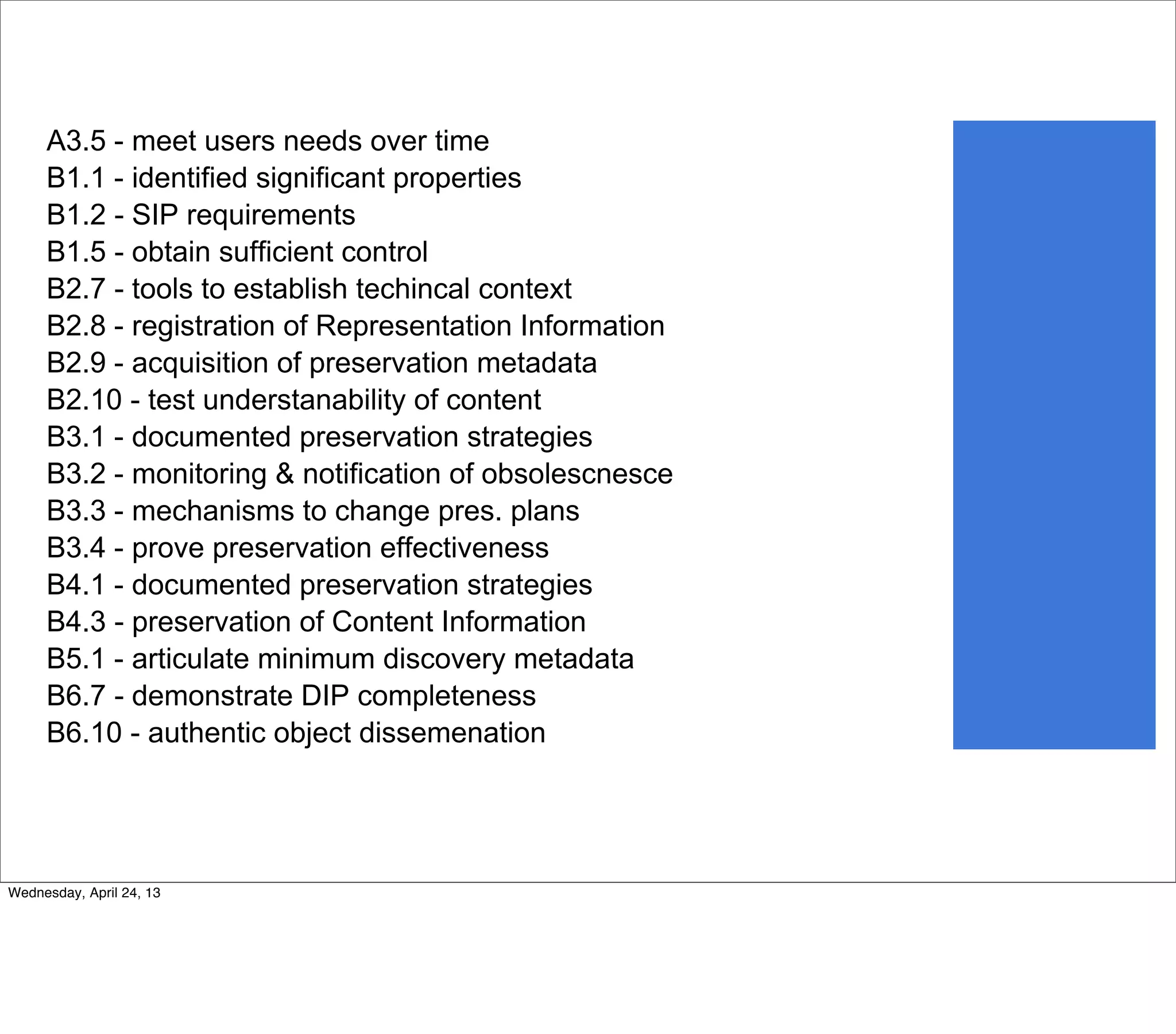
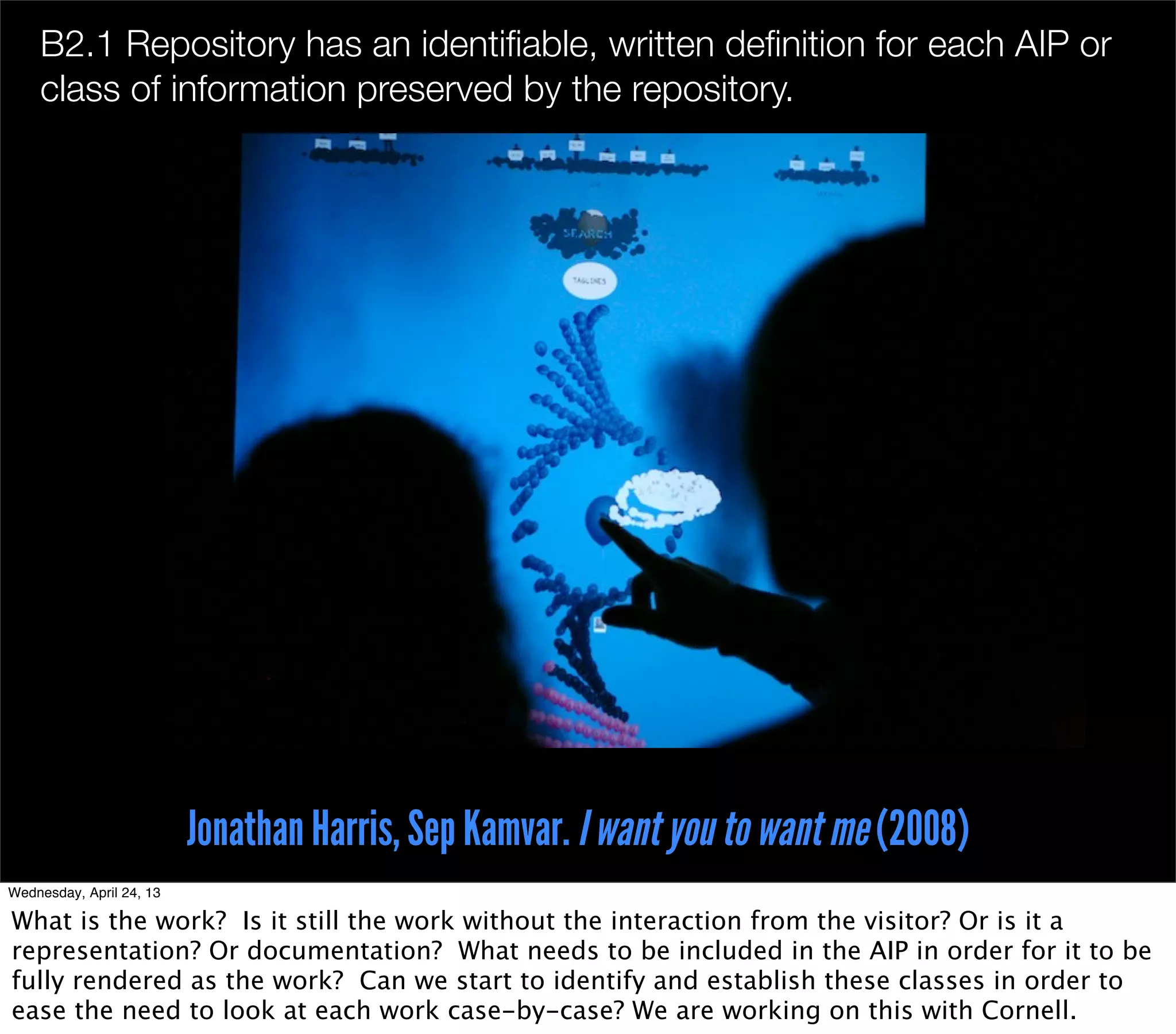
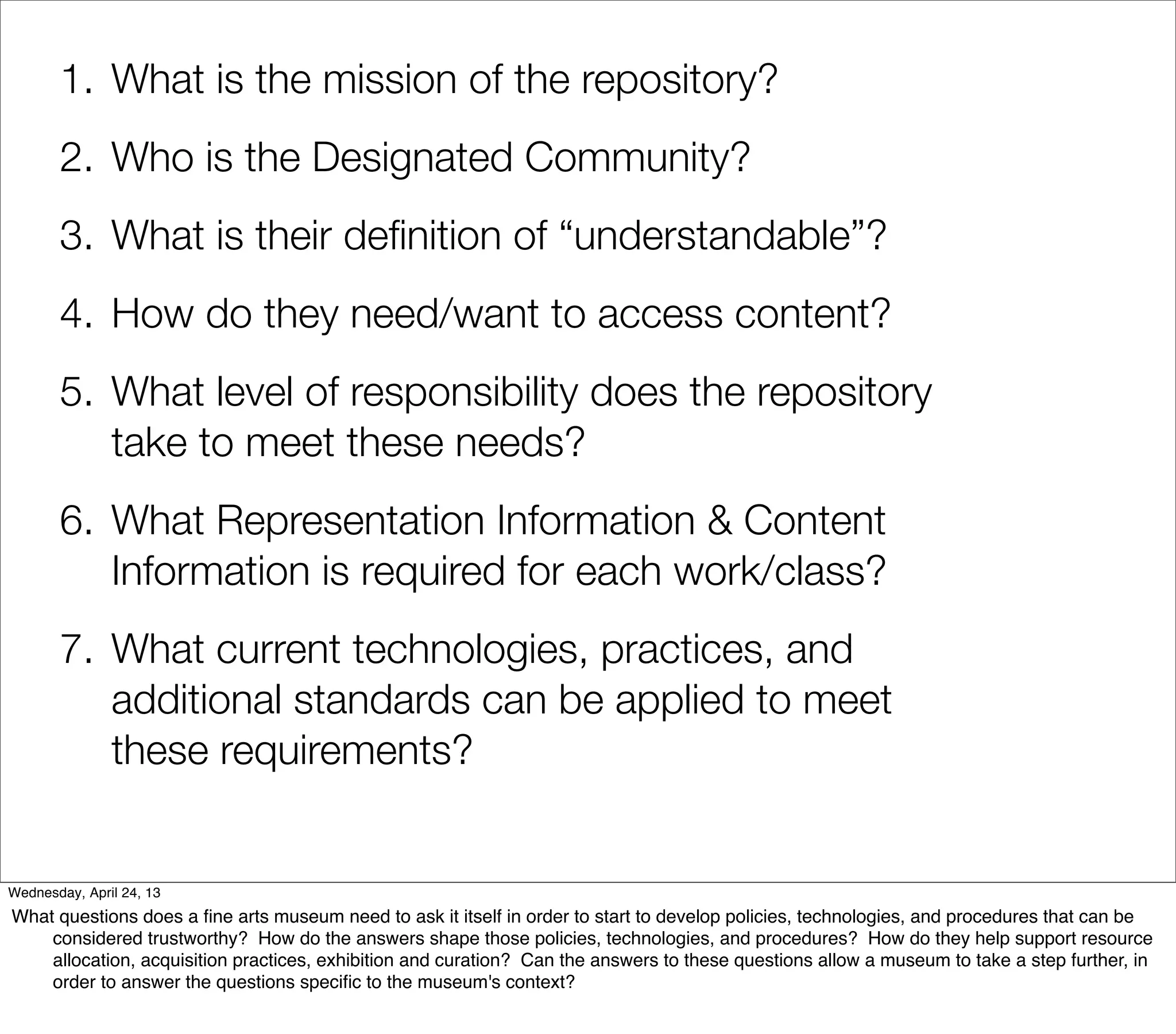
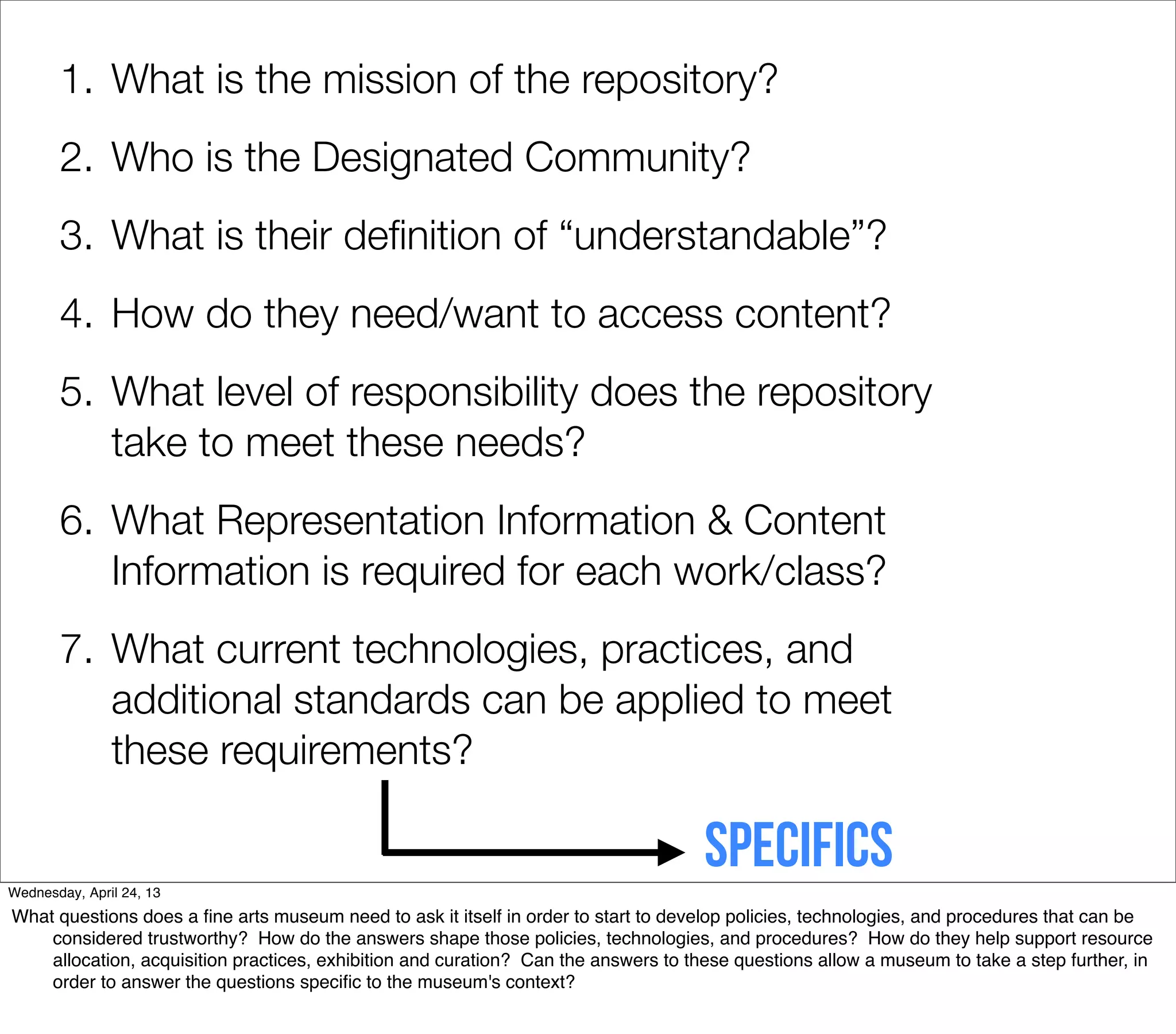
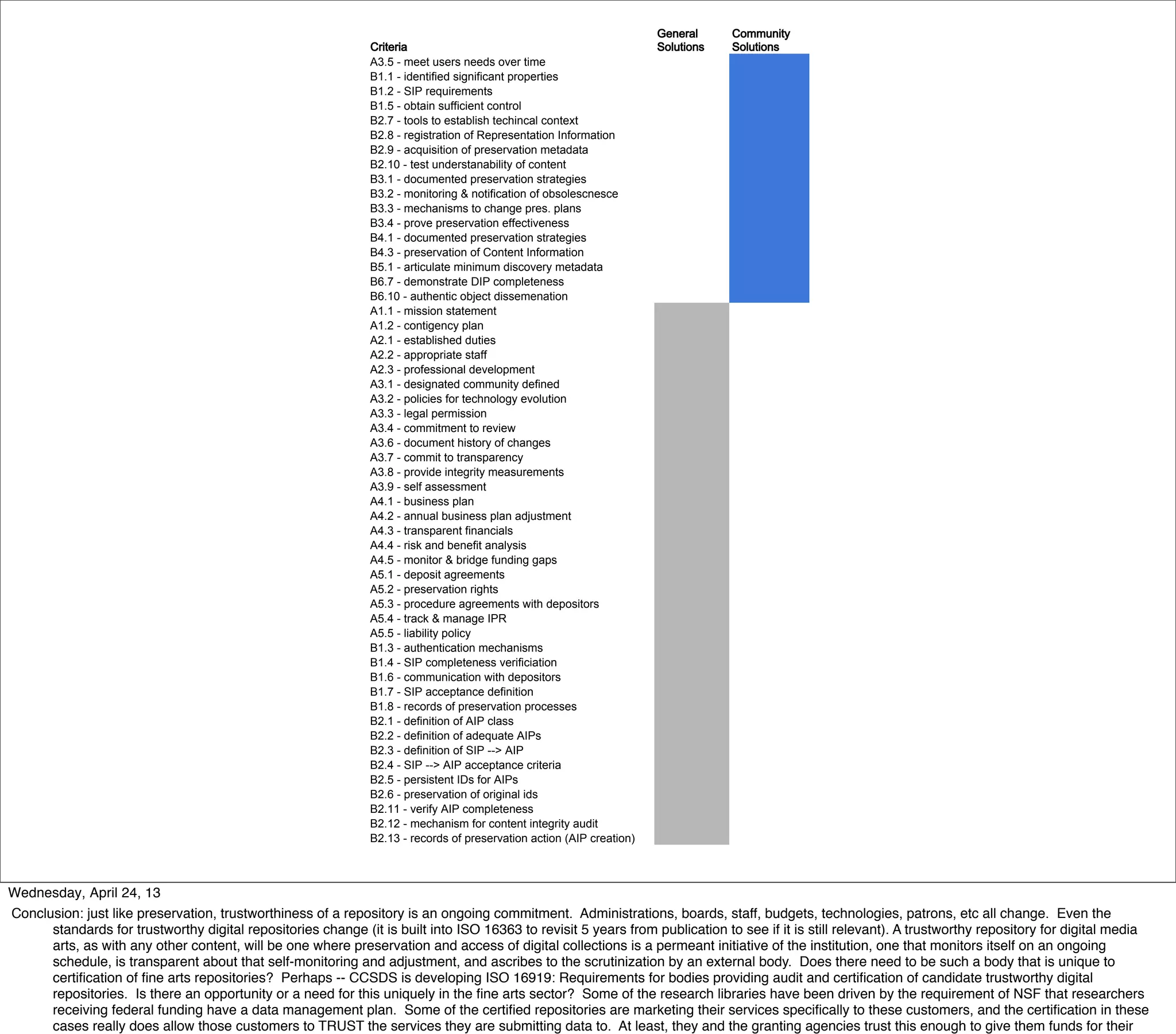
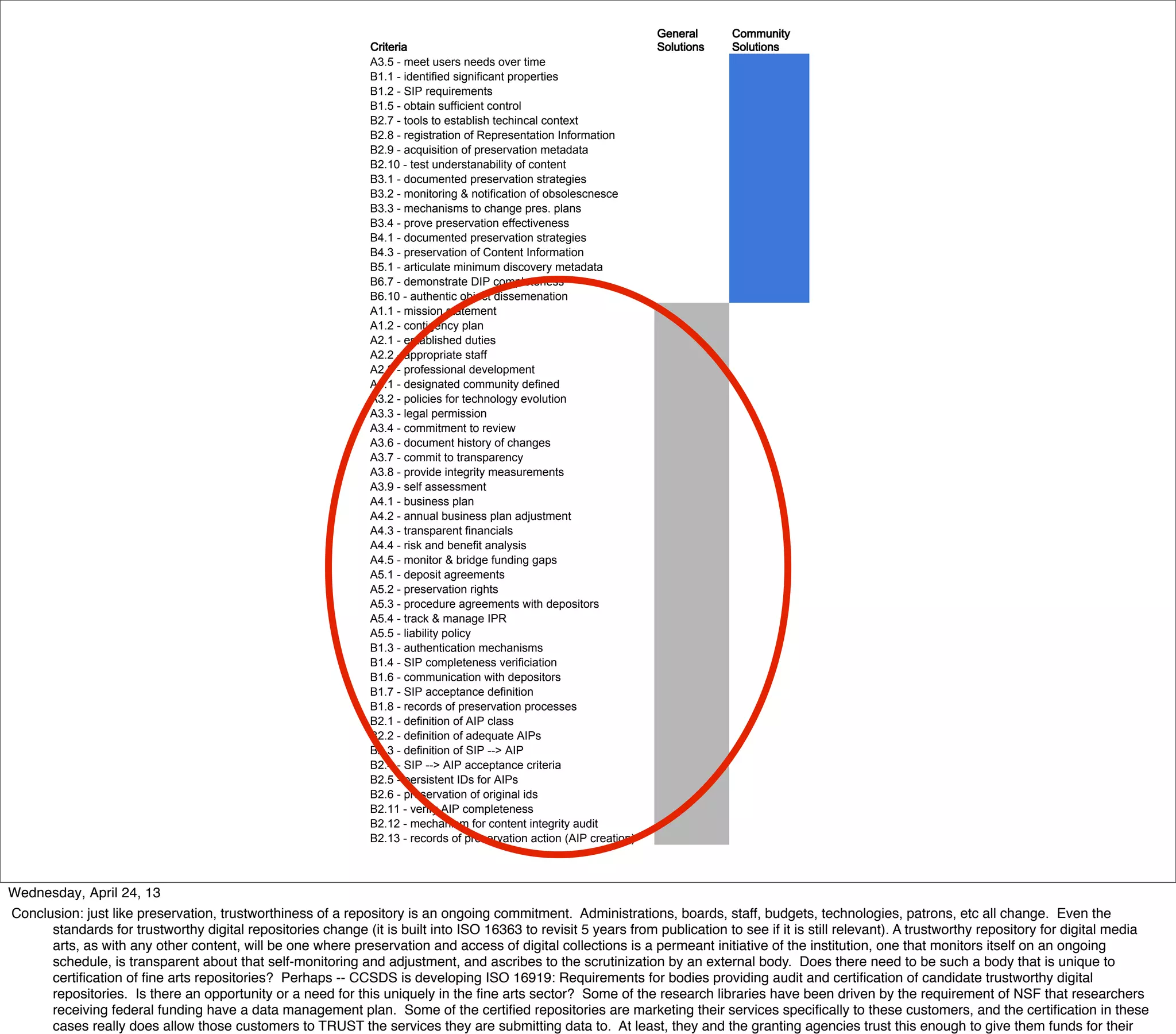
The document discusses the concept of trustworthy digital repositories, focusing on their role in preserving time-based media art and digital fine art. It emphasizes the need for a certification process to establish trust, outlining standards and guidelines for managing and preserving digital information effectively. Key topics include the responsibilities of repositories, community understanding, and the long-term accessibility and authenticity of archived content.