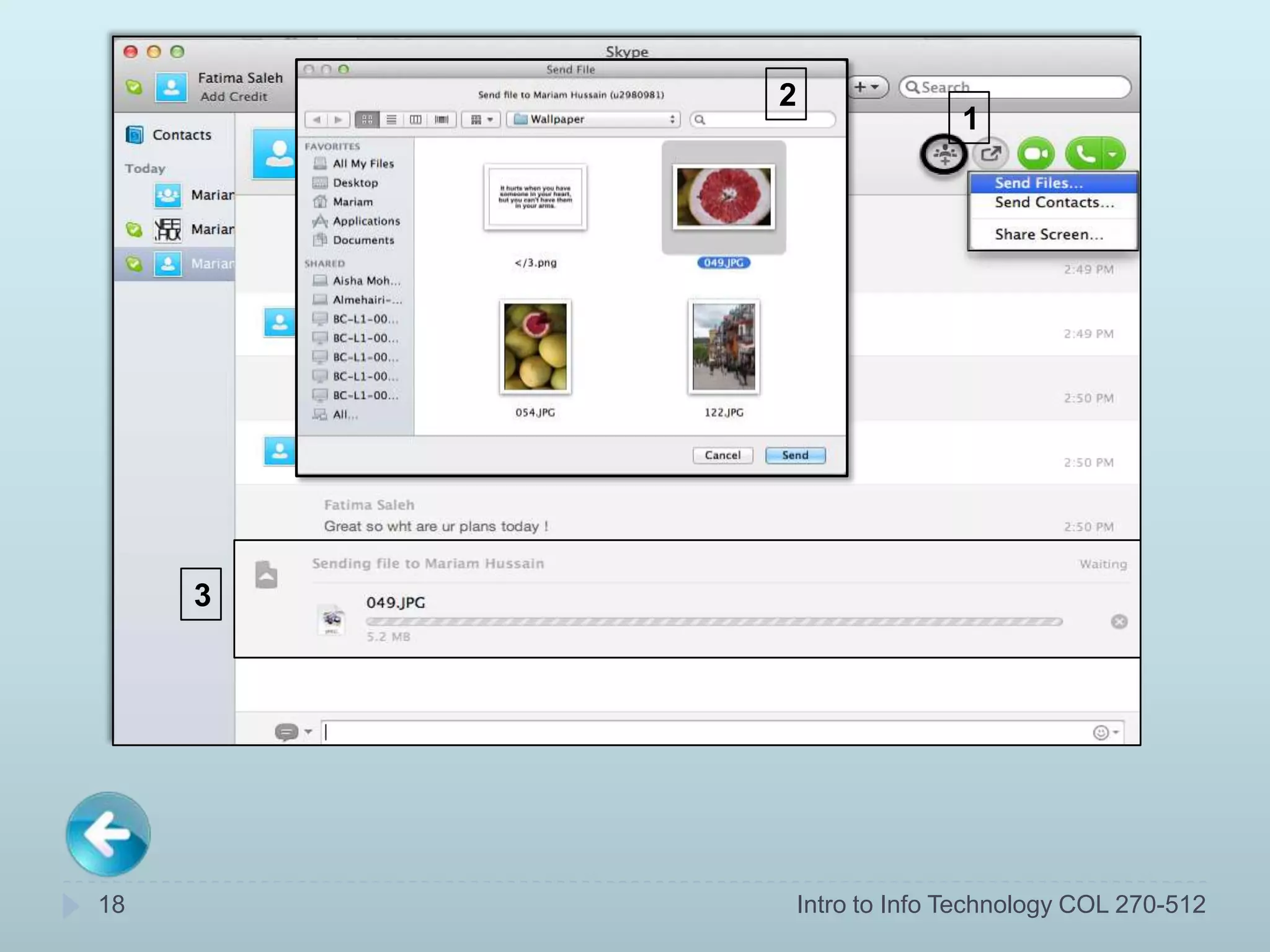
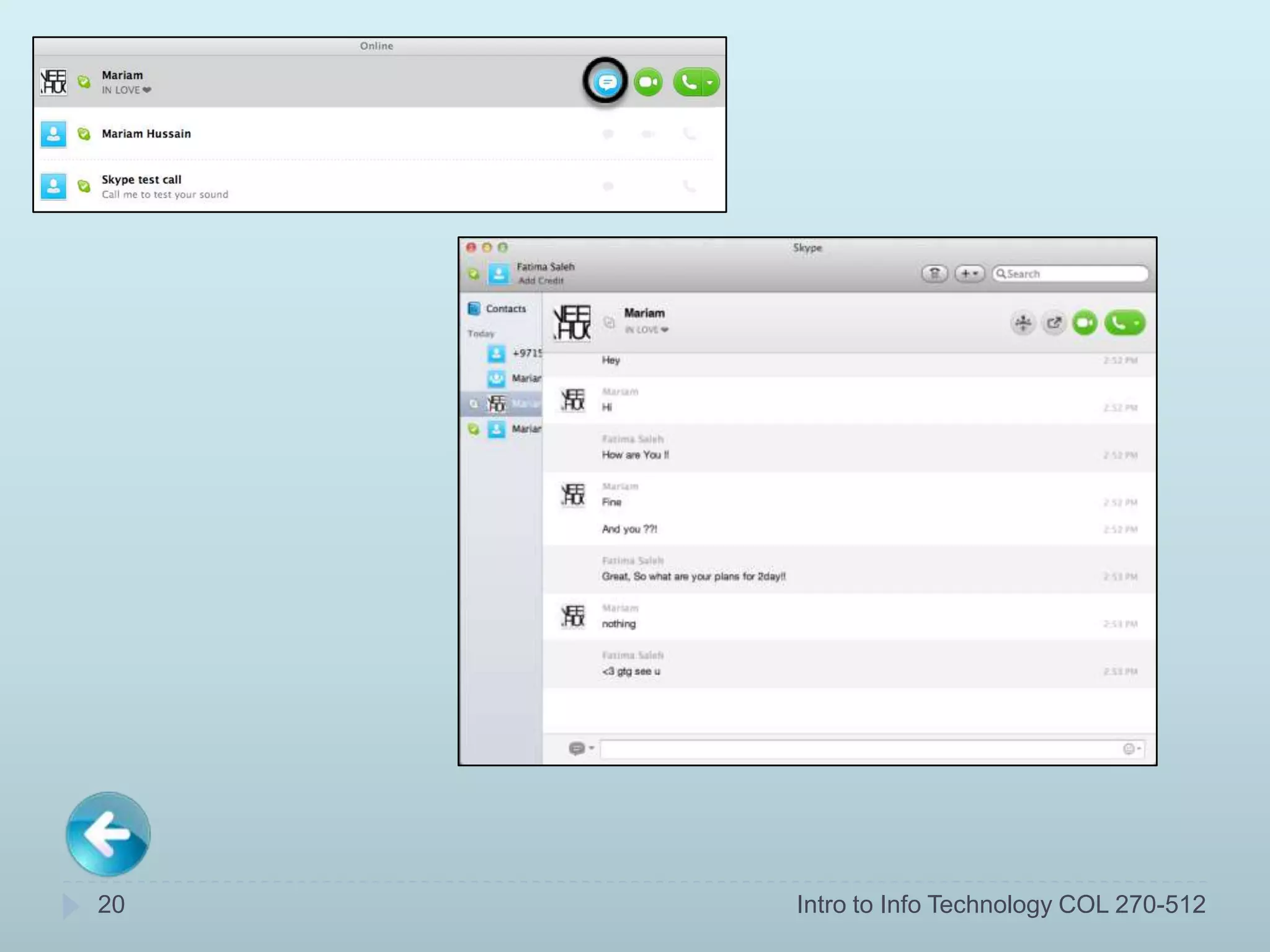
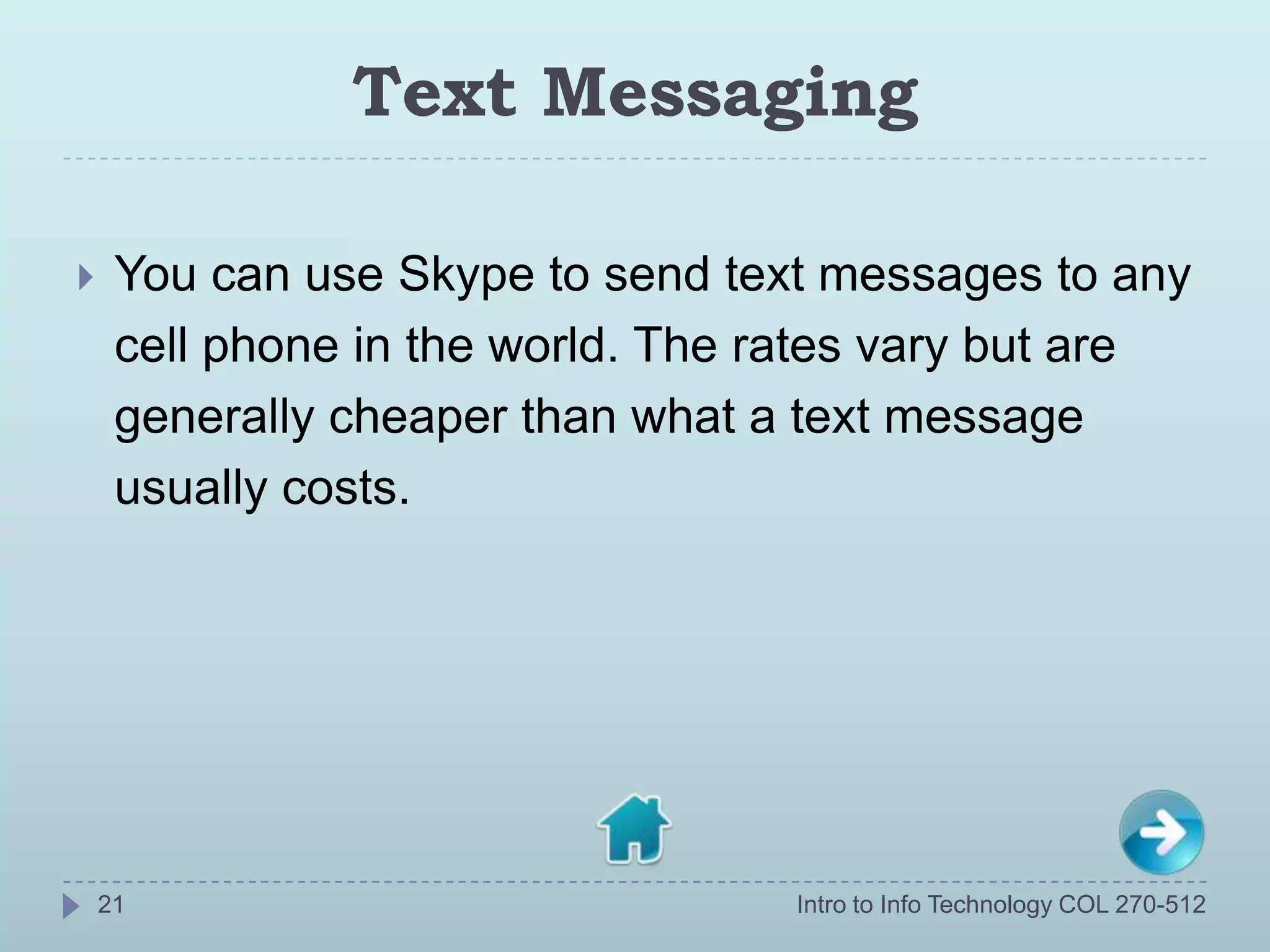
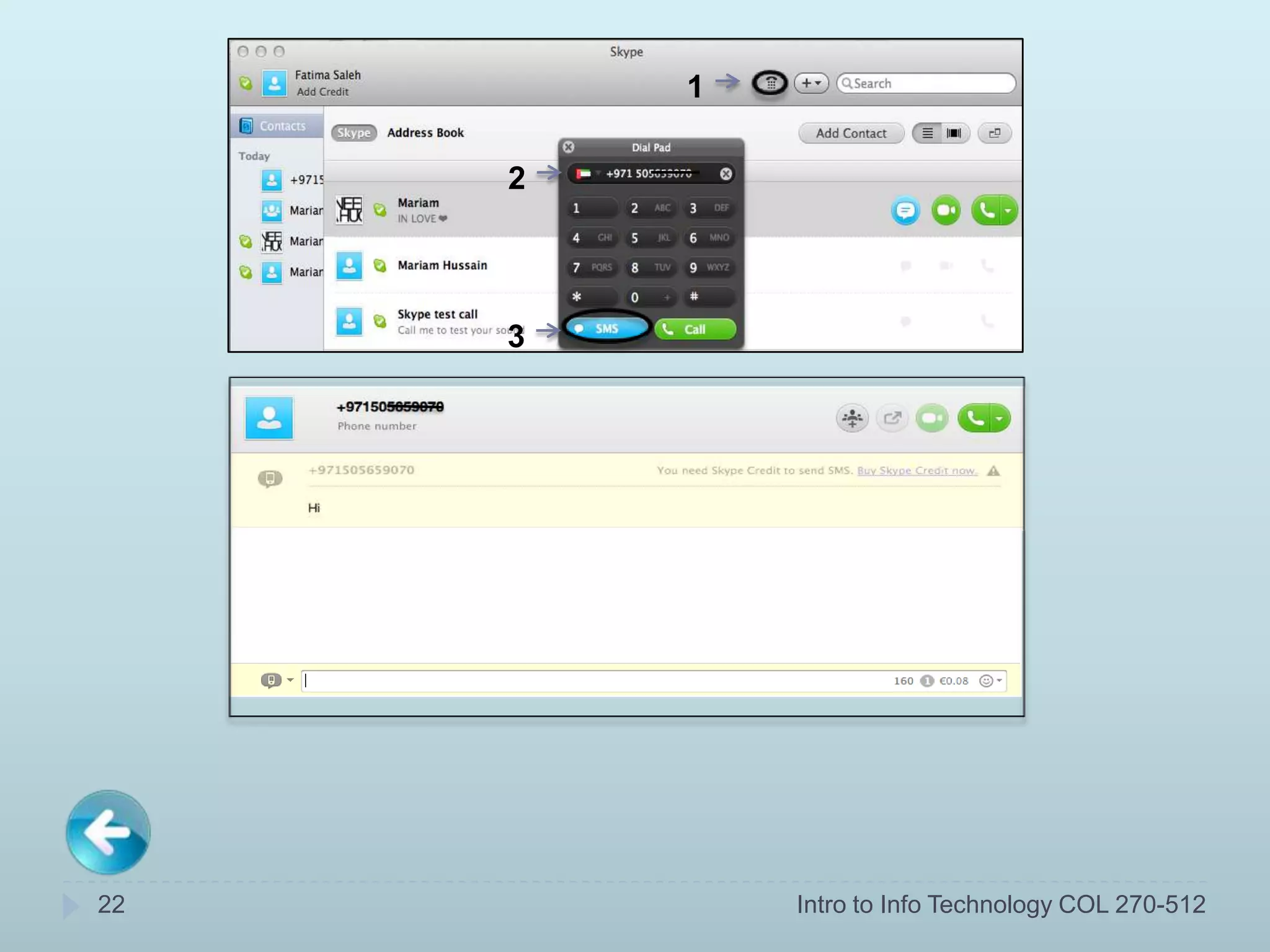
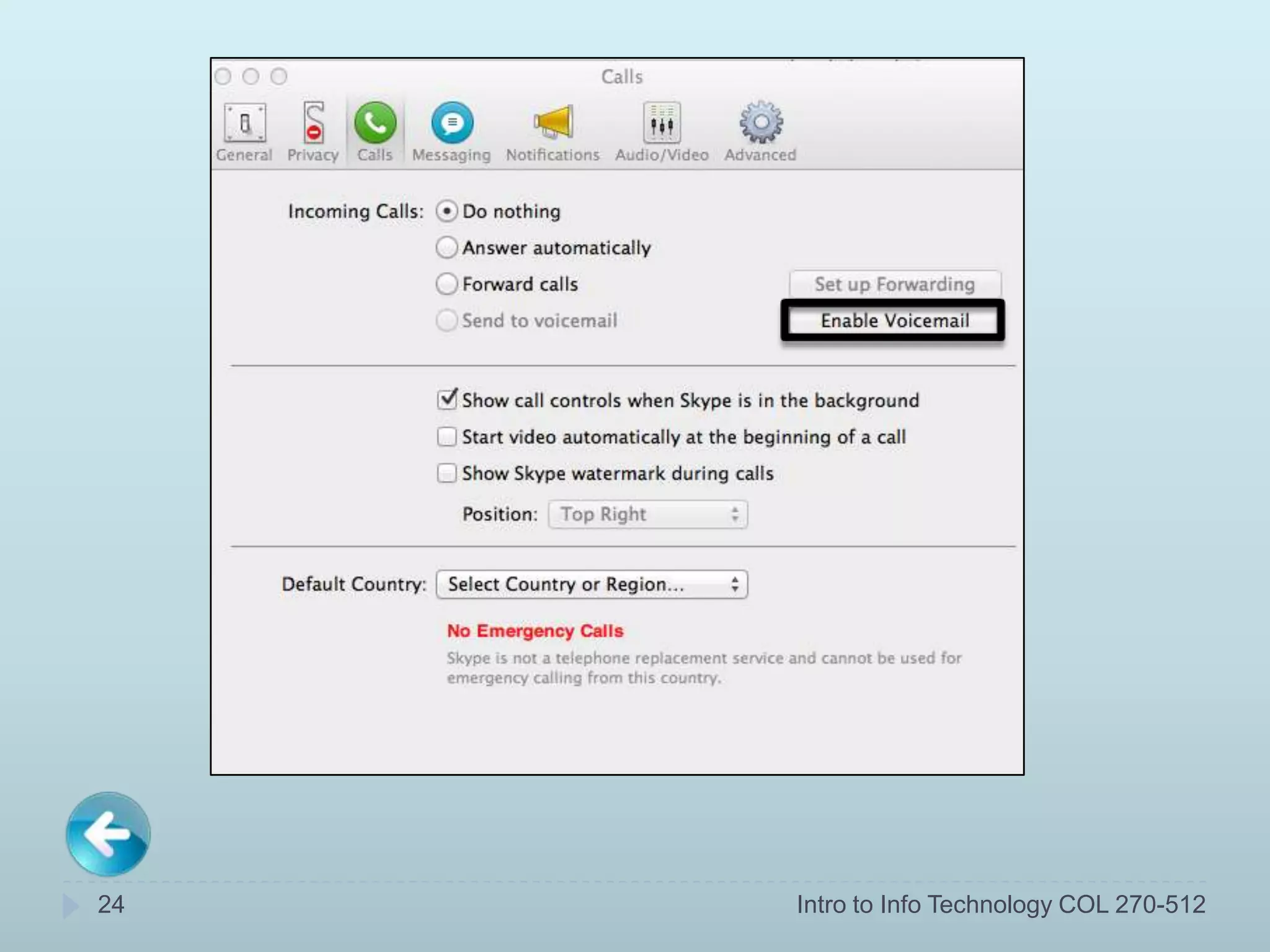
Skype is a free software program that allows users to make voice and video calls over the internet. It can be used to keep in touch with friends and family or for educational purposes from any location with an internet connection, such as homes, schools, or workplaces. Skype has features like video calling, file sharing, instant messaging, and voice mail. To use Skype, users download the software, create an account, add contacts, and can then make calls, share files, and message others on Skype for free or at low rates.

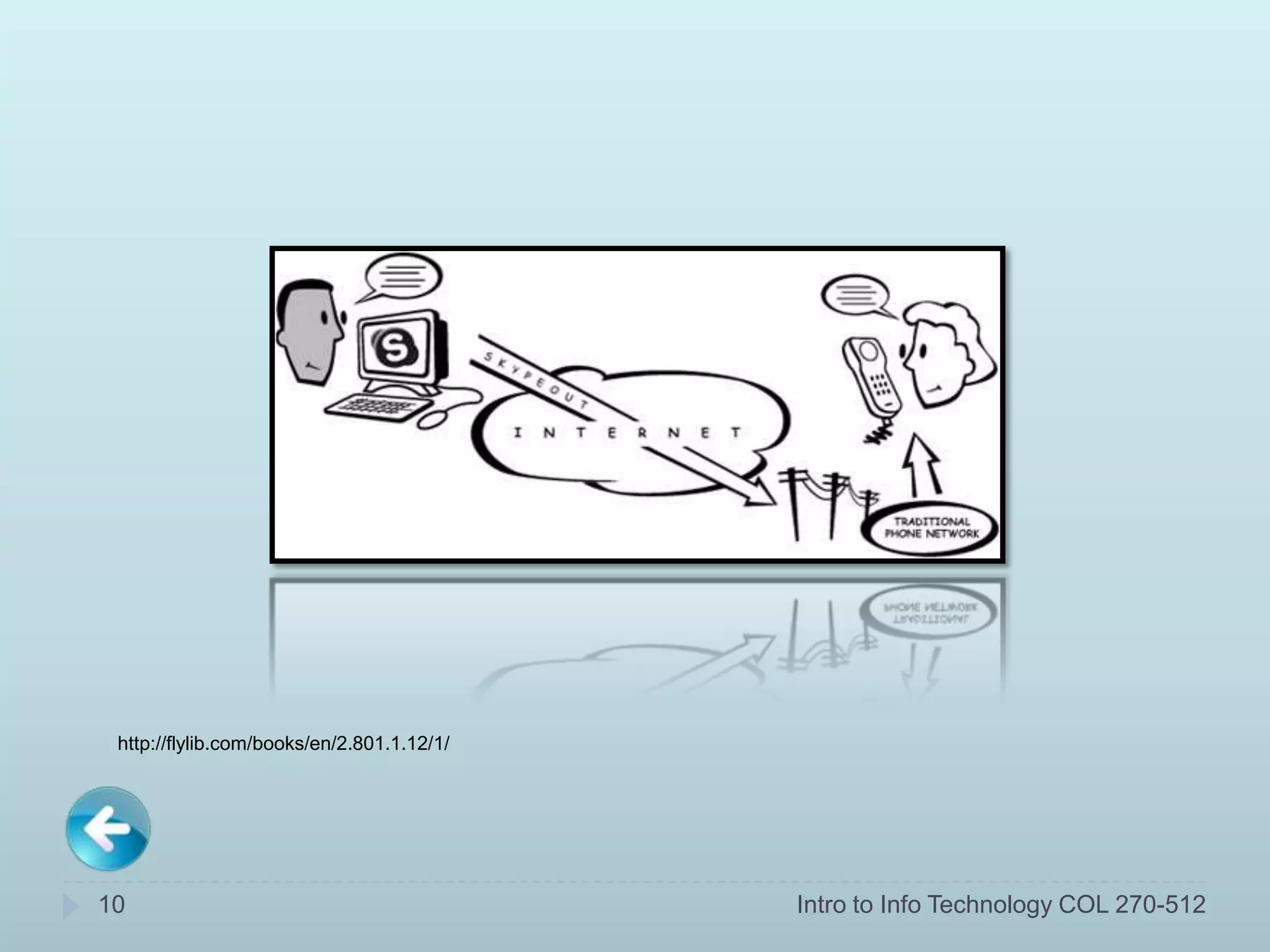
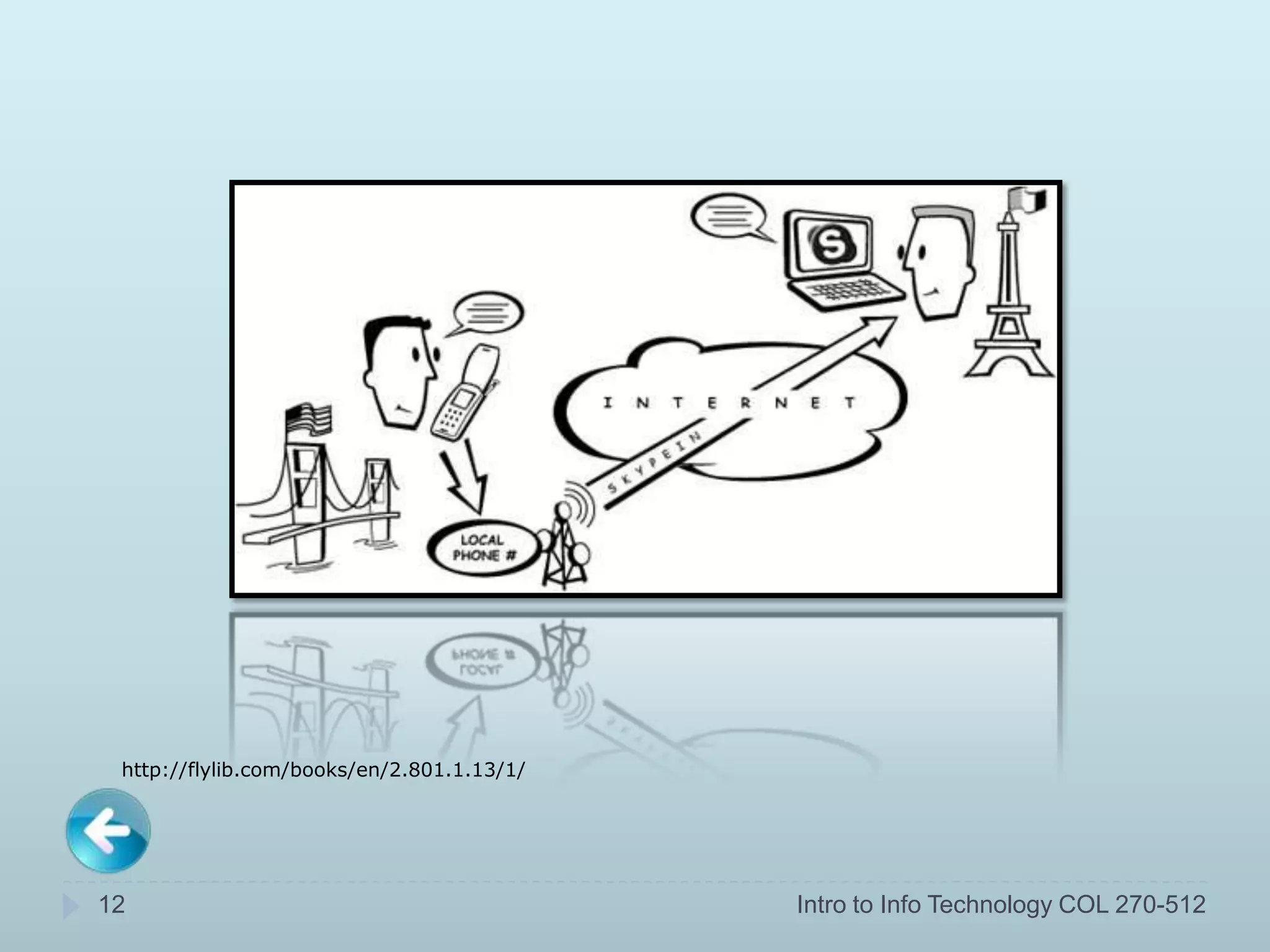
![SkypeIn [Your personal online number]
For people to be able to call your Skype account
from a phone, you need a SkypeIn number to
give it to them.
Receiving calls from phones doesn’t cost you
anything but will charge the caller the same rate
as if they were calling a real phone.
11 Intro to Info Technology COL 270-512](https://image.slidesharecdn.com/finaldraft-120108095637-phpapp01/75/Skype-Powerpoint-11-2048.jpg)