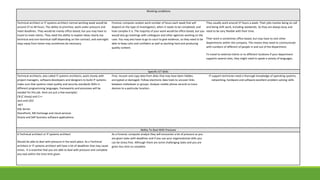
The document discusses the skills and responsibilities required for three IT careers: technical architect, forensic computer analyst, and IT support technician.
A technical architect must understand client needs, break down requirements, present plans, oversee testing, and ensure systems meet standards. Communication skills are essential to explain structures to designers.
A forensic computer analyst recovers hidden data, traces electronic trails, carefully documents investigations, and presents technical findings in court. Attention to detail and the ability to work under pressure are important.
An IT support technician helps clients with faults, sets up new equipment, and provides training. Strong communication is needed to understand issues and explain solutions clearly. Flexibility is also required due to shift work and on