Simple Social Media
•Download as PPT, PDF•
0 likes•586 views
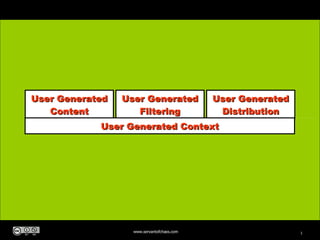
The four basic elements of social media. Note: it requires "users" -- that is folks like you and me ;)
Report
Share
Report
Share
Recommended
Greenys Esol

Greeny the Teletubby enjoys visiting several locations, including a book, a tree where he plays, a tunnel inside of which he is seen, leaves in a garden where he lies, outside of a library, and sliding down a slide.
Copy Of partlyshankly

The document appears to be a story told from the perspective of Ruyita about her relationship with Melissa. It describes their interactions at school, expressing love for each other, and an implied break up between the two. The story jumps between different locations and times in their relationship in a nonlinear fashion.
Improved PHP Development

Felix De Vliegher gave a presentation on improved PHP development at Arteveldehogeschool campus Mariakerke in Gent, Belgium on August 20, 2008. He introduced himself as a PHP developer of 7 years and Zend Certified PHP5 engineer. The presentation covered topics like coding standards, frameworks and libraries, version control, testing, documentation, design patterns, PHP 5.3, and resources. Coding standards were emphasized as important for consistency, reducing bugs, enhancing readability, easing collaboration, and should not be invented but enforced for new employees.
Johnnie Walker

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive function. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
Datafolha/Sensus

Uma pesquisa eleitoral para governador de estado listou os candidatos e suas intenções de voto. O candidato do PMDB, Leonardo Quintão, liderava com 16,7% das intenções, seguido pelo candidato do PC do B, Jô Moraes, com 17%. A pesquisa foi realizada entre 17 e 24 de julho de 2008 pela empresa Datafolha a pedido do jornal Folha de São Paulo.
Inscribe Te CampañA De CedulacióN

El documento habla sobre un joven llamado Héctor Johnny Ballesteros Cedeño que realizó el trámite para obtener su cédula de identidad para poder votar en las elecciones de 2009 en Panamá. También menciona que el Tribunal Electoral está realizando una campaña para alentar a los jóvenes que cumplen 18 años antes del 2 de mayo de 2009 a que obtengan su cédula a tiempo. Finalmente, provee instrucciones sobre el proceso para obtener una cédula, incluyendo los documentos requeridos y los pasos a seguir como
Municipal Iquique perdio 1-0 ante Coquimbo Unido

Municipal Iquique perdió 1-0 ante Coquimbo Unido en un partido jugado en el estadio La Pampilla el miércoles 20 de agosto de 2008.
Recommended
Greenys Esol

Greeny the Teletubby enjoys visiting several locations, including a book, a tree where he plays, a tunnel inside of which he is seen, leaves in a garden where he lies, outside of a library, and sliding down a slide.
Copy Of partlyshankly

The document appears to be a story told from the perspective of Ruyita about her relationship with Melissa. It describes their interactions at school, expressing love for each other, and an implied break up between the two. The story jumps between different locations and times in their relationship in a nonlinear fashion.
Improved PHP Development

Felix De Vliegher gave a presentation on improved PHP development at Arteveldehogeschool campus Mariakerke in Gent, Belgium on August 20, 2008. He introduced himself as a PHP developer of 7 years and Zend Certified PHP5 engineer. The presentation covered topics like coding standards, frameworks and libraries, version control, testing, documentation, design patterns, PHP 5.3, and resources. Coding standards were emphasized as important for consistency, reducing bugs, enhancing readability, easing collaboration, and should not be invented but enforced for new employees.
Johnnie Walker

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive function. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
Datafolha/Sensus

Uma pesquisa eleitoral para governador de estado listou os candidatos e suas intenções de voto. O candidato do PMDB, Leonardo Quintão, liderava com 16,7% das intenções, seguido pelo candidato do PC do B, Jô Moraes, com 17%. A pesquisa foi realizada entre 17 e 24 de julho de 2008 pela empresa Datafolha a pedido do jornal Folha de São Paulo.
Inscribe Te CampañA De CedulacióN

El documento habla sobre un joven llamado Héctor Johnny Ballesteros Cedeño que realizó el trámite para obtener su cédula de identidad para poder votar en las elecciones de 2009 en Panamá. También menciona que el Tribunal Electoral está realizando una campaña para alentar a los jóvenes que cumplen 18 años antes del 2 de mayo de 2009 a que obtengan su cédula a tiempo. Finalmente, provee instrucciones sobre el proceso para obtener una cédula, incluyendo los documentos requeridos y los pasos a seguir como
Municipal Iquique perdio 1-0 ante Coquimbo Unido

Municipal Iquique perdió 1-0 ante Coquimbo Unido en un partido jugado en el estadio La Pampilla el miércoles 20 de agosto de 2008.
Stop Talking at Me. Nobody is Listening: The New Physics of the Consumerverse

Presented at the DiG Festival, NSW, 2013.
Digital is hot right now. But as brands and businesses of all shapes and sizes rush into the digital domain, they bring with them the baggage of old marketing and PR practices. This brave new digital world is a fundamentally different space. Welcome to the "Consumerverse" - an upside-down, inside-out universe where analytics are revealing, on the one hand, the hit and miss randomness of broadcast messaging, and on the other, the growing importance of guided engagement-laden conversation designed to reach the consumer’s “sphere of attraction.”
To succeed in this new Consumerverse, brands need to understand the new physics of attraction and design their business, communications and customer experience accordingly.
How to Listen to Social Media for the Pharma Industry

Listening and monitoring social media for regulated industries like Pharmaceuticals is not simple. This infographic points you in the right direction.
Business of Being Social

The recent Outlook for Australian Social Business 2012 showed there was a perception gap between brands and customers. This goes far beyond "social media" - and becoming a "Social Business" means reaching beyond just Facebook or Twitter. It's about transforming your business, industry and relationships.
How to Write for Social Media

To understand the difference between business communications/writing, it's important to look at authority, authenticity and the mirror of intent.
How to Build Trust in Social Networks - The 4 As

What do you need to do to create trust in your social networks? The 4 As provide you some simple guidelines.
Social Media: How to listen 

The document discusses how to effectively listen in social media to gain business insights. It recommends breaking listening into 5 key segments: brand, product, industry, key personnel, and intent. Within each segment, create keyword lists to track mentions. The document also categorizes what will be heard into 7 categories from questions to loyalty. It concludes by recommending setting up keyword searches across platforms and aggregating them for easy monitoring.
Storytelling for social media

How do you consistently engage your audience? How do you tell a compelling story? This presentation shows, through the P-L-A-Y framework, just how you can make your stories move through social networks
Connect Now Lead Gen+Community

This document discusses the importance of continuous digital strategy and engagement in a changing media landscape. It emphasizes understanding audiences through listening, researching their behaviors and interests, and creating relevant content to start meaningful conversations. Measurement of engagement, influence and the spread of content is important for evolving the strategy over time based on what resonates. The goal is turning user-generated stories into amplification of the brand message through conversation rather than one-way shouting.
Videos That Explain Social Media

A collection of my favourite videos that eloquently explain social media. Perfect for a client or executive briefing.
Lead Generation, Community and Social Media

Gavin Heaton's presentation on generating leads and connecting communities via social media from the MarketingNow conference (#mktgnow)
Creative Sydney: Creative Networking: Coffee Mornings Sydney

This document describes a weekly coffee meetup called "Coffee Mornings" that takes place every Friday at 8am at the Single Origin coffee shop in Surry Hills, Sydney. The meetup was started by bloggers Emily Reed and Gavin Heaton as a way to get to know other people in their community over coffee. It has grown popular on social media under the Twitter handle @coffeemornings, though the organizers emphasize it is a low-key, relaxed event focused on conversation and community building more than work or promotion. Photos included were taken at past Coffee Mornings events.
The Business Of Web 2.0 V6

This document discusses the opportunities and lessons of Web 2.0 for businesses. It notes that markets have become conversations as people share knowledge quickly online. It argues that companies must listen to these online conversations and communities to understand their markets. The rise of user-generated content and new online tools are transforming how value is created and how people interact, representing a fundamental shift for businesses.
SocialMediaJobs.com.au Salary Survey 2009

This is the first annual survey of employers and job seekers working in social media.
It was carried out in early February 2009.
The Business Of Web 2.0 V3

Revised edition talking about the shift from B2C + B2B models to a Brand-to-Community model of marketing. Case study on the Age of Conversation.
InterestingSouth: Cluetrain - Through the Eyes of a Child

Presentation for InterestingSouth. To reimagine the world we live in, we often try to "see through the eyes of a child". But what happens when the world of a four year old collides with the new media world of the Cluetrain Manifesto? This THREE minute presentation puts a digital camera in the hands of my daughters.
The Business Of Web 2.0

The document discusses the rise of Web 2.0 and how it has changed business models. It notes that Web 2.0 allows for more conversation and user participation through sites like Flickr, YouTube, and Wikipedia. It also discusses how this has led to a convergence of markets, with knowledge workers expecting rich web experiences at work similarly to how they engage online outside of work. This new "Brand-to-Community" model extends consumer-focused engagement strategies into the enterprise space.
Digital Storytelling

The document discusses using digital storytelling to brand yourself or a product. It emphasizes that an effective story does not need to be big, but should have a beginning, middle, and end. Small stories can be just as impactful as big ones. The key is to define what you want to happen with your brand and make that promise tangible to customers through a story they control.
Key Themes and Messges

The document provides guidance on developing key messaging for communications, including:
1. Defining a concise mission/proposition and vision in less than 10 words.
2. Crafting a clear, jargon-free core message that directly addresses the needs fulfilled by the product or service.
3. Identifying from the client/consumer's perspective what they are looking for in a partner and how the product/service addresses their needs in 1-3 points.
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Harnessing the Power of NLP and Knowledge Graphs for Opioid Research

Gursev Pirge, PhD
Senior Data Scientist - JohnSnowLabs
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
More Related Content
More from Gavin Heaton
Stop Talking at Me. Nobody is Listening: The New Physics of the Consumerverse

Presented at the DiG Festival, NSW, 2013.
Digital is hot right now. But as brands and businesses of all shapes and sizes rush into the digital domain, they bring with them the baggage of old marketing and PR practices. This brave new digital world is a fundamentally different space. Welcome to the "Consumerverse" - an upside-down, inside-out universe where analytics are revealing, on the one hand, the hit and miss randomness of broadcast messaging, and on the other, the growing importance of guided engagement-laden conversation designed to reach the consumer’s “sphere of attraction.”
To succeed in this new Consumerverse, brands need to understand the new physics of attraction and design their business, communications and customer experience accordingly.
How to Listen to Social Media for the Pharma Industry

Listening and monitoring social media for regulated industries like Pharmaceuticals is not simple. This infographic points you in the right direction.
Business of Being Social

The recent Outlook for Australian Social Business 2012 showed there was a perception gap between brands and customers. This goes far beyond "social media" - and becoming a "Social Business" means reaching beyond just Facebook or Twitter. It's about transforming your business, industry and relationships.
How to Write for Social Media

To understand the difference between business communications/writing, it's important to look at authority, authenticity and the mirror of intent.
How to Build Trust in Social Networks - The 4 As

What do you need to do to create trust in your social networks? The 4 As provide you some simple guidelines.
Social Media: How to listen 

The document discusses how to effectively listen in social media to gain business insights. It recommends breaking listening into 5 key segments: brand, product, industry, key personnel, and intent. Within each segment, create keyword lists to track mentions. The document also categorizes what will be heard into 7 categories from questions to loyalty. It concludes by recommending setting up keyword searches across platforms and aggregating them for easy monitoring.
Storytelling for social media

How do you consistently engage your audience? How do you tell a compelling story? This presentation shows, through the P-L-A-Y framework, just how you can make your stories move through social networks
Connect Now Lead Gen+Community

This document discusses the importance of continuous digital strategy and engagement in a changing media landscape. It emphasizes understanding audiences through listening, researching their behaviors and interests, and creating relevant content to start meaningful conversations. Measurement of engagement, influence and the spread of content is important for evolving the strategy over time based on what resonates. The goal is turning user-generated stories into amplification of the brand message through conversation rather than one-way shouting.
Videos That Explain Social Media

A collection of my favourite videos that eloquently explain social media. Perfect for a client or executive briefing.
Lead Generation, Community and Social Media

Gavin Heaton's presentation on generating leads and connecting communities via social media from the MarketingNow conference (#mktgnow)
Creative Sydney: Creative Networking: Coffee Mornings Sydney

This document describes a weekly coffee meetup called "Coffee Mornings" that takes place every Friday at 8am at the Single Origin coffee shop in Surry Hills, Sydney. The meetup was started by bloggers Emily Reed and Gavin Heaton as a way to get to know other people in their community over coffee. It has grown popular on social media under the Twitter handle @coffeemornings, though the organizers emphasize it is a low-key, relaxed event focused on conversation and community building more than work or promotion. Photos included were taken at past Coffee Mornings events.
The Business Of Web 2.0 V6

This document discusses the opportunities and lessons of Web 2.0 for businesses. It notes that markets have become conversations as people share knowledge quickly online. It argues that companies must listen to these online conversations and communities to understand their markets. The rise of user-generated content and new online tools are transforming how value is created and how people interact, representing a fundamental shift for businesses.
SocialMediaJobs.com.au Salary Survey 2009

This is the first annual survey of employers and job seekers working in social media.
It was carried out in early February 2009.
The Business Of Web 2.0 V3

Revised edition talking about the shift from B2C + B2B models to a Brand-to-Community model of marketing. Case study on the Age of Conversation.
InterestingSouth: Cluetrain - Through the Eyes of a Child

Presentation for InterestingSouth. To reimagine the world we live in, we often try to "see through the eyes of a child". But what happens when the world of a four year old collides with the new media world of the Cluetrain Manifesto? This THREE minute presentation puts a digital camera in the hands of my daughters.
The Business Of Web 2.0

The document discusses the rise of Web 2.0 and how it has changed business models. It notes that Web 2.0 allows for more conversation and user participation through sites like Flickr, YouTube, and Wikipedia. It also discusses how this has led to a convergence of markets, with knowledge workers expecting rich web experiences at work similarly to how they engage online outside of work. This new "Brand-to-Community" model extends consumer-focused engagement strategies into the enterprise space.
Digital Storytelling

The document discusses using digital storytelling to brand yourself or a product. It emphasizes that an effective story does not need to be big, but should have a beginning, middle, and end. Small stories can be just as impactful as big ones. The key is to define what you want to happen with your brand and make that promise tangible to customers through a story they control.
Key Themes and Messges

The document provides guidance on developing key messaging for communications, including:
1. Defining a concise mission/proposition and vision in less than 10 words.
2. Crafting a clear, jargon-free core message that directly addresses the needs fulfilled by the product or service.
3. Identifying from the client/consumer's perspective what they are looking for in a partner and how the product/service addresses their needs in 1-3 points.
More from Gavin Heaton (18)
Stop Talking at Me. Nobody is Listening: The New Physics of the Consumerverse

Stop Talking at Me. Nobody is Listening: The New Physics of the Consumerverse
How to Listen to Social Media for the Pharma Industry

How to Listen to Social Media for the Pharma Industry
Creative Sydney: Creative Networking: Coffee Mornings Sydney

Creative Sydney: Creative Networking: Coffee Mornings Sydney
InterestingSouth: Cluetrain - Through the Eyes of a Child

InterestingSouth: Cluetrain - Through the Eyes of a Child
Recently uploaded
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Harnessing the Power of NLP and Knowledge Graphs for Opioid Research

Gursev Pirge, PhD
Senior Data Scientist - JohnSnowLabs
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
Principle of conventional tomography-Bibash Shahi ppt..pptx

before the computed tomography, it had been widely used.
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The typical problem in product engineering is not bad strategy, so much as “no strategy”. This leads to confusion, lack of motivation, and incoherent action. The next time you look for a strategy and find an empty space, instead of waiting for it to be filled, I will show you how to fill it in yourself. If you’re wrong, it forces a correction. If you’re right, it helps create focus. I’ll share how I’ve approached this in the past, both what works and lessons for what didn’t work so well.
Mutation Testing for Task-Oriented Chatbots

Conversational agents, or chatbots, are increasingly used to access all sorts of services using natural language. While open-domain chatbots - like ChatGPT - can converse on any topic, task-oriented chatbots - the focus of this paper - are designed for specific tasks, like booking a flight, obtaining customer support, or setting an appointment. Like any other software, task-oriented chatbots need to be properly tested, usually by defining and executing test scenarios (i.e., sequences of user-chatbot interactions). However, there is currently a lack of methods to quantify the completeness and strength of such test scenarios, which can lead to low-quality tests, and hence to buggy chatbots.
To fill this gap, we propose adapting mutation testing (MuT) for task-oriented chatbots. To this end, we introduce a set of mutation operators that emulate faults in chatbot designs, an architecture that enables MuT on chatbots built using heterogeneous technologies, and a practical realisation as an Eclipse plugin. Moreover, we evaluate the applicability, effectiveness and efficiency of our approach on open-source chatbots, with promising results.
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
The Microsoft 365 Migration Tutorial For Beginner.pptx

This presentation will help you understand the power of Microsoft 365. However, we have mentioned every productivity app included in Office 365. Additionally, we have suggested the migration situation related to Office 365 and how we can help you.
You can also read: https://www.systoolsgroup.com/updates/office-365-tenant-to-tenant-migration-step-by-step-complete-guide/
Artificial Intelligence and Electronic Warfare

Artificial Intelligence and Electronic WarfarePapadakis K.-Cyber-Information Warfare Analyst & Cyber Defense/Security Consultant-Hellenic MoD
AI & Electronic WarfareCrafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...Pitangent Analytics & Technology Solutions Pvt. Ltd
Discover top-tier mobile app development services, offering innovative solutions for iOS and Android. Enhance your business with custom, user-friendly mobile applications.GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
Biomedical Knowledge Graphs for Data Scientists and Bioinformaticians

Dmitrii Kamaev, PhD
Senior Product Owner - QIAGEN
Recently uploaded (20)
Harnessing the Power of NLP and Knowledge Graphs for Opioid Research

Harnessing the Power of NLP and Knowledge Graphs for Opioid Research
Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...

Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...
Principle of conventional tomography-Bibash Shahi ppt..pptx

Principle of conventional tomography-Bibash Shahi ppt..pptx
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...

9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
The Microsoft 365 Migration Tutorial For Beginner.pptx

The Microsoft 365 Migration Tutorial For Beginner.pptx
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph
Biomedical Knowledge Graphs for Data Scientists and Bioinformaticians

Biomedical Knowledge Graphs for Data Scientists and Bioinformaticians
Simple Social Media
- 1. User Generated Content User Generated Filtering User Generated Distribution User Generated Context