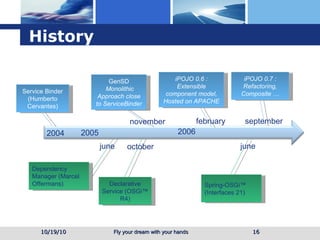
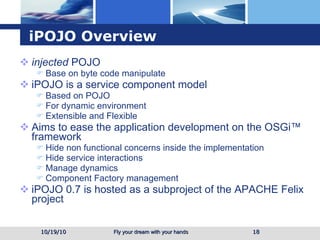
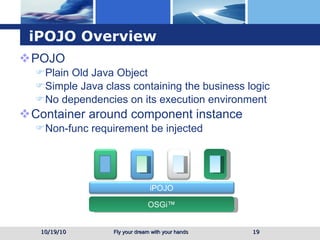
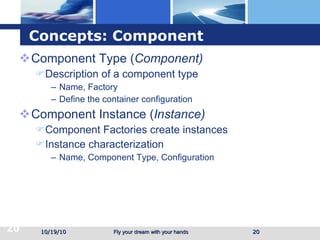
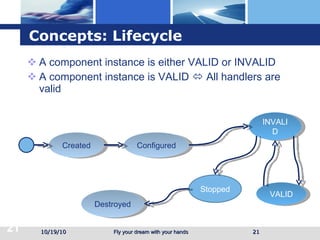
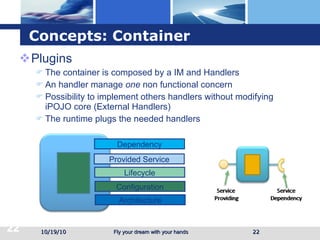
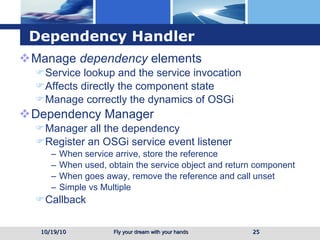
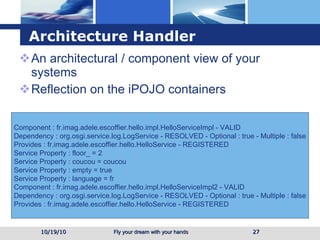
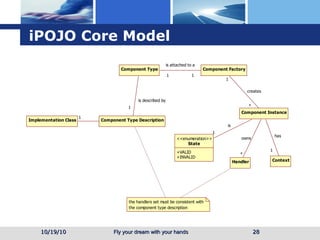
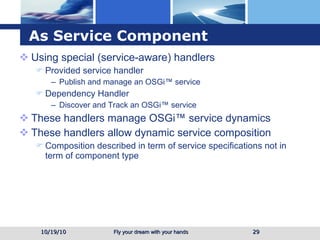
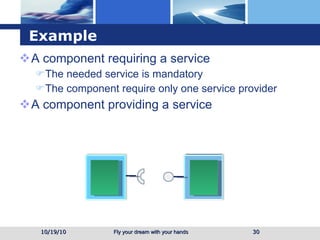
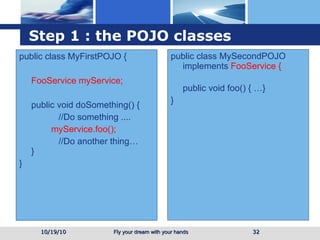
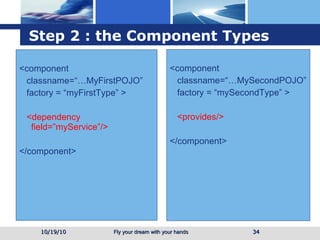
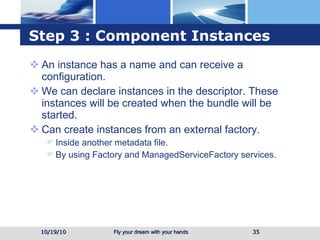
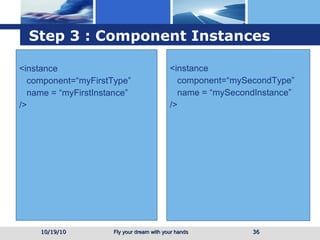
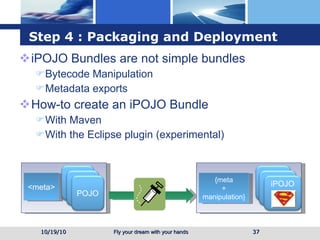
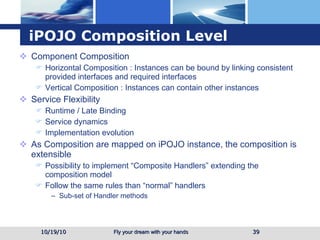
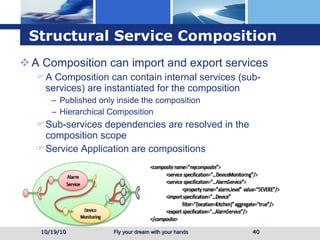
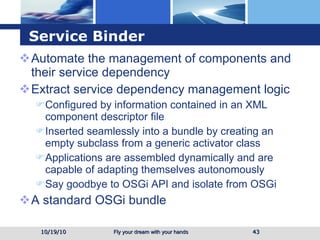
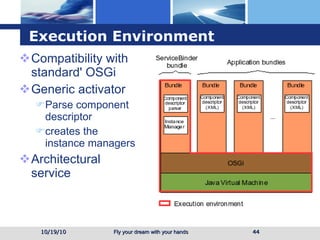
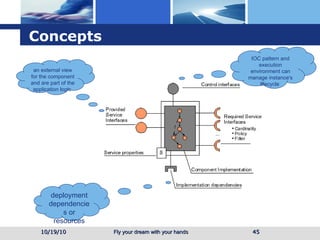
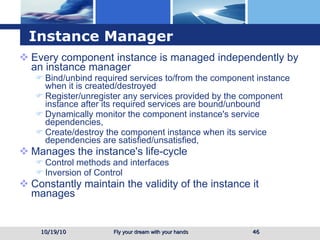
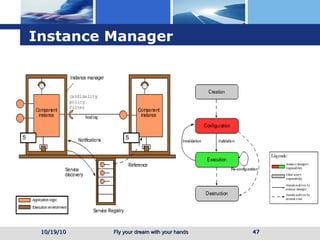
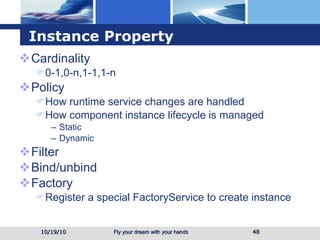
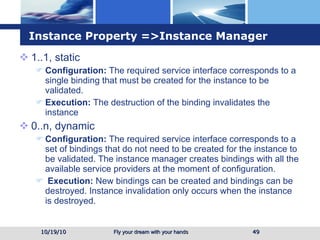
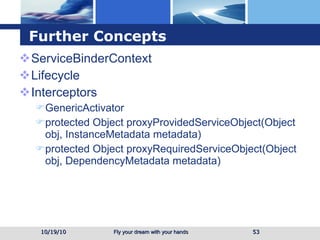
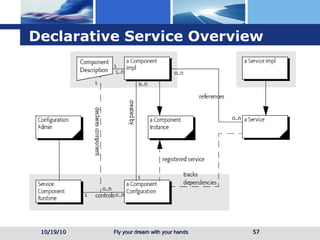
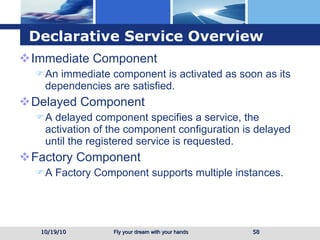
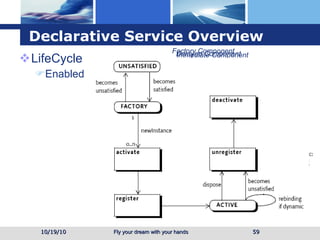
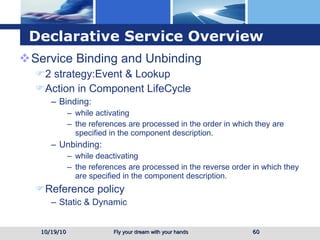
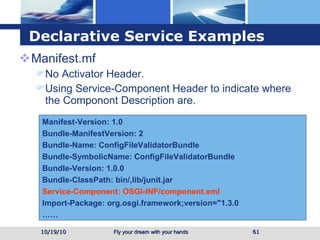
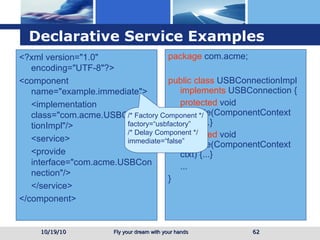
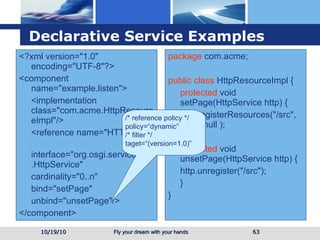
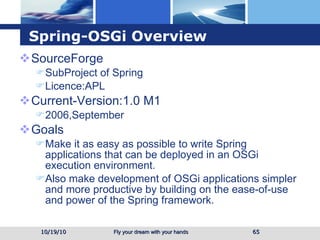
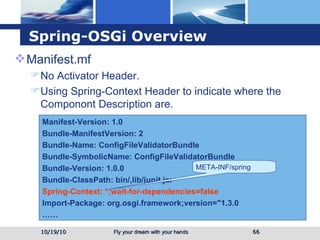
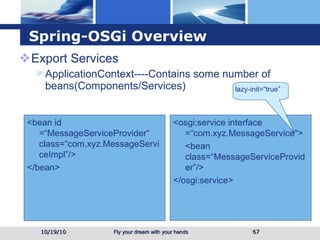
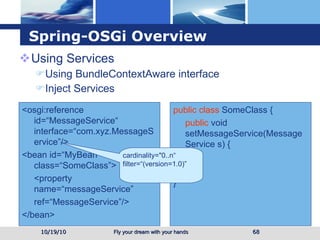
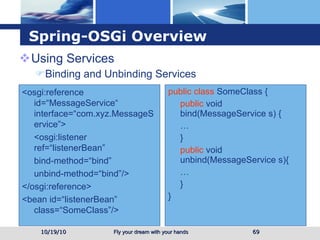
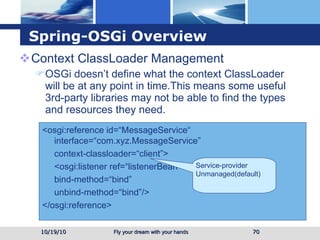
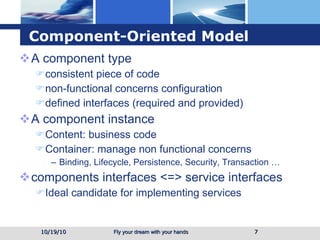
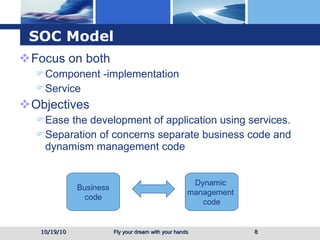
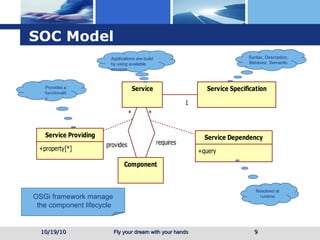
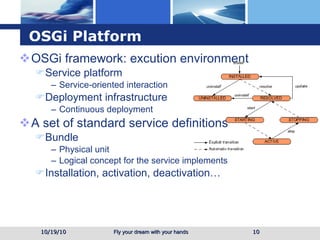
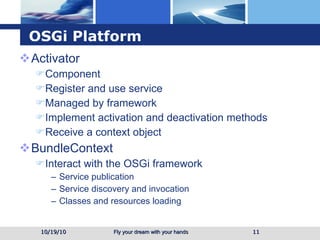
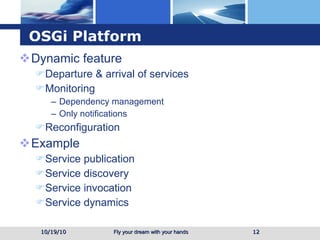
The document discusses several service-oriented component models for OSGi including iPOJO, Service Binder, Declarative Services (DS), and Spring OSGi. It provides an overview of each model, including concepts like components, instances, lifecycles, and how they automate aspects like service registration, lookup, and dependency management. The document also provides examples of how to define and use components with these models.

![Example 10/19/10 ... import tutorial.example2.service.DictionaryService; public class Activator implements BundleActivator, ServiceListener { private BundleContext m_context = null; private ServiceReference m_ref = null; private DictionaryService m_dictionary = null; public void start(BundleContext context) throws Exception { m_context = context; m_context.addServiceListener(this, "(&(objectClass=" + DictionaryService.class.getName() + ")" + "(Language=*))"); ServiceReference[] refs = m_context.getServiceReferences( DictionaryService.class.getName(), "(Language=*)"); ..... } public void stop(BundleContext context) { } public void serviceChanged(ServiceEvent event) { String[] objectClass = (String[]) event.getServiceReference().getProperty("objectClass"); ....... } } import tutorial.example2.service.DictionaryService; public class Activator implements BundleActivator { public void start(BundleContext context) { Properties props = new Properties(); props.put("Language", "English"); context.registerService( DictionaryService.class.getName(), new DictionaryImpl(), props); } public void stop(BundleContext context) { } private static class DictionaryImpl implements DictionaryService { String[] m_dictionary = { "welcome", "to", "the", "osgi", "tutorial" }; public boolean checkWord(String word) { .... } } } package tutorial.example2.service; public interface DictionaryService { public boolean checkWord(String word); } import org.osgi.framework.BundleActivator;import org.osgi.framework.BundleContext;import org.osgi.framework.ServiceReference; import org.osgi.framework.ServiceListener;import org.osgi.framework.ServiceEvent;](https://image.slidesharecdn.com/serviceorientedcomponentmodel-101019064814-phpapp02/85/Service-oriented-component-model-13-320.jpg)