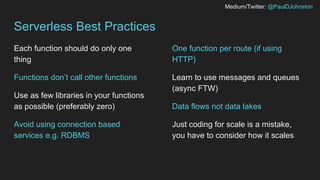
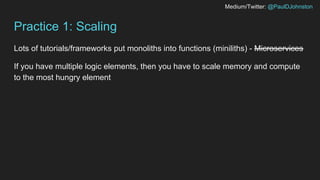
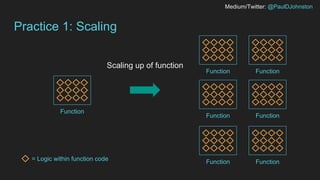
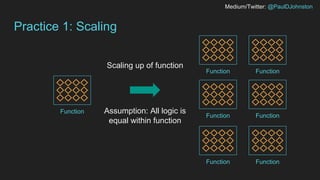
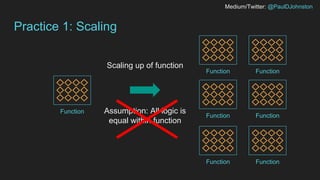
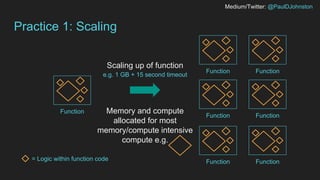
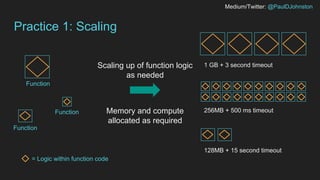
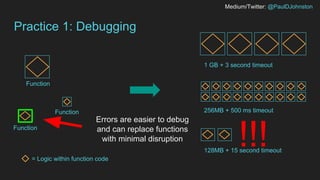
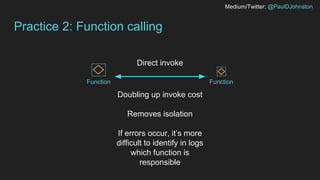
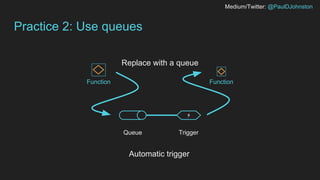
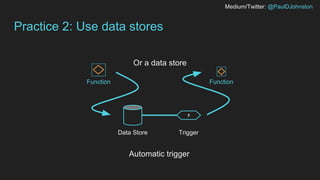
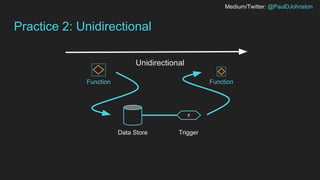
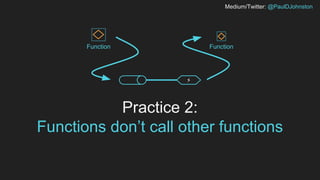
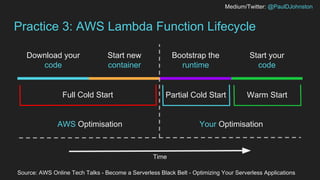
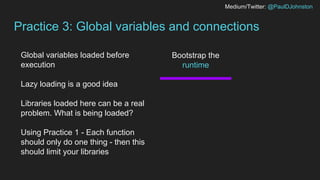
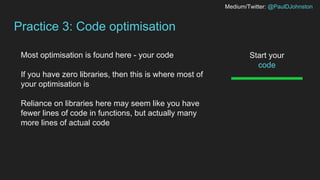
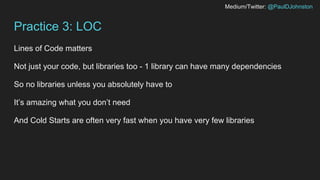
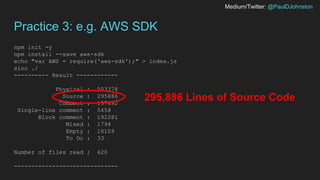
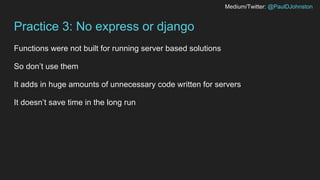
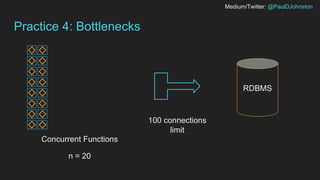
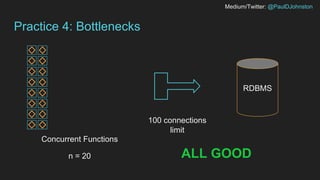
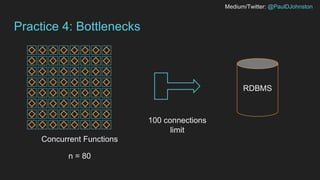
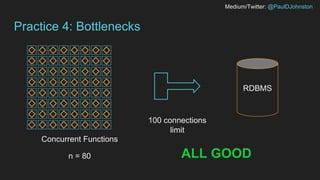
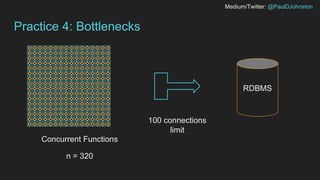
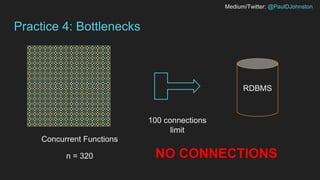
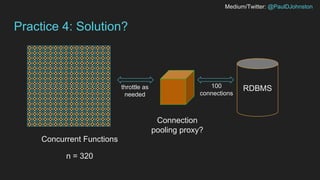
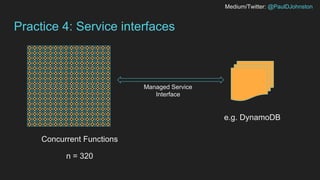
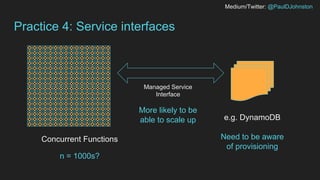
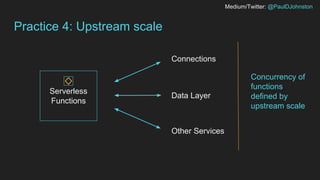
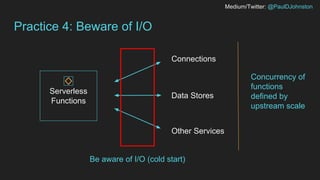
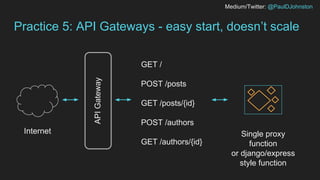
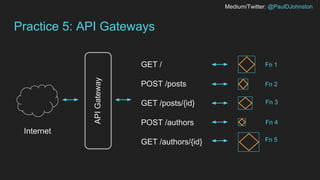
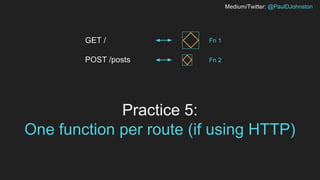
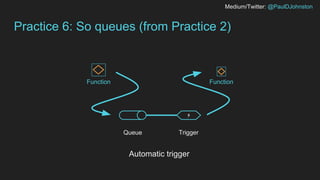
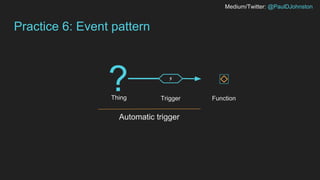
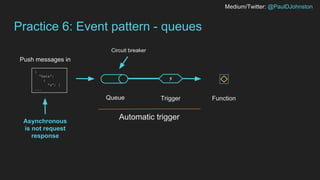
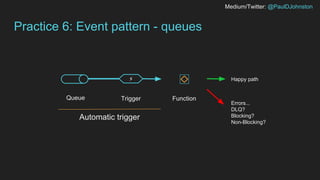
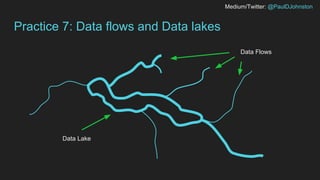
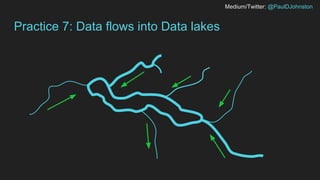
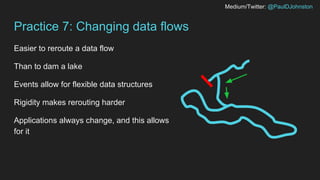
The document outlines best practices for serverless computing, emphasizing the importance of designing functions that are event-driven and isolated, with each function performing a single task. It suggests avoiding the use of connection-based services like RDBMS, minimizing library usage, and adopting asynchronous messaging patterns. Additionally, it encourages developers to think critically about scaling, data flows, and the overall architecture of serverless applications.