Securing IoT at Scale Requires a Holistic Approach
•
0 likes•1,900 views
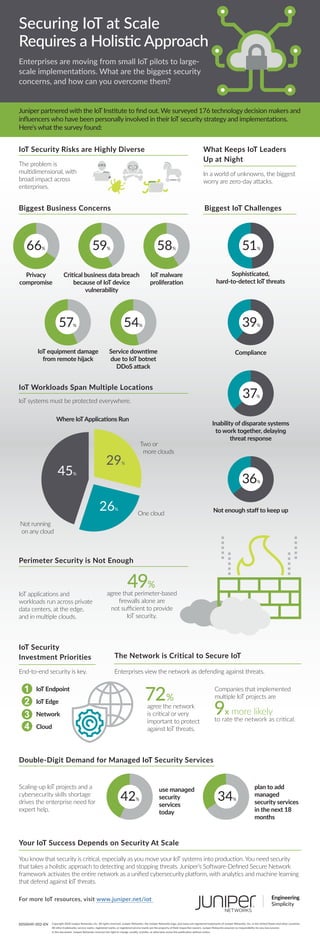
Enterprises are moving from small IoT pilots to large-scale implementations. What are the biggest security concerns, and how can you overcome them? Juniper partnered with the IoT Institute to find out. We surveyed 176 technology decision makers and influencers who have been personally involved in their IoT security strategy and implementations. Here's what the survey found:
Report
Share
Report
Share
Recommended
Experience the AI-Driven Enterprise

Experiences are everything and Juniper knows this. From when a user engages with an app on their smartphone to when a workload is generated in the cloud to pick up the request, we know that every point of contact along the way impacts the user’s experience, from client to cloud. Learn more about what Juniper has recently announced in this SlideShare!
Why Juniper, Driven by Mist AI, Leads the Market

While the rest of the industry has started to copy our AIOps Client to Cloud message recently, we understand that others are nowhere close to delivering on the promise of the AI-Driven Enterprise, both in terms of depth of features and breadth of portfolio. Take a look at this SlideShare to truly understand why Juniper, driven by Mist AI, leads the market.
SD-WAN, Meet MARVIS.

Juniper Networks is introducing the fourth expansion of the AI-driven enterprise to bring artificial intelligence to the LAN, WLAN and now WAN for end-to-end optimization of user experiences and proactive troubleshooting driven by Mist AI.
With the new Juniper Mist WAN Assurance service, customers will receive even better automation and insight in branch locations with AI-driven service level expectations, client-to-cloud event correlation for rapid fault resolution, anomaly detection, and proactive support.
Real AI. Real Results. Mist AI Customer Testimonials.

See what Juniper customers have to say about how Mist AI has statistically improved the way they run their business. For more information on how Mist AI can improve your network, join us for Transformation Thursdays at: https://www.juniper.net/us/en/forms/ai-driven-demo/
MetaFabric Architecture

We are excited to announce the release of MetaFabric, a new end-to-end architecture that encompasses Juniper Network’s switching, routing, software and security portfolios. It provides the freedom and flexibility to use any technology, any protocol, any orchestration platform, any SDN controller, for any data center application with the assurance of interoperability and minimal disruption.
Are you able to deliver reliable experiences for connected devices

Here are 5 things you can do with Mist Wired Assurance. With Wired Assurance, you can leverage Juniper EX switch telemetry to enable simpler operations, shorter mean time to repair, and better visibility into end-user experiences for your connected devices, including access points, servers, and IoT endpoints.
How AI Simplifies Troubleshooting Your WAN

As much the workforce continues to work remotely, The COVID-19 Pandemic has taught us that the WAN is more important than ever, and troubleshooting it couldn’t be more difficult. Learn how MARVIS & Mist AI simplify the burdensome process of troubleshooting the WAN.
Recommended
Experience the AI-Driven Enterprise

Experiences are everything and Juniper knows this. From when a user engages with an app on their smartphone to when a workload is generated in the cloud to pick up the request, we know that every point of contact along the way impacts the user’s experience, from client to cloud. Learn more about what Juniper has recently announced in this SlideShare!
Why Juniper, Driven by Mist AI, Leads the Market

While the rest of the industry has started to copy our AIOps Client to Cloud message recently, we understand that others are nowhere close to delivering on the promise of the AI-Driven Enterprise, both in terms of depth of features and breadth of portfolio. Take a look at this SlideShare to truly understand why Juniper, driven by Mist AI, leads the market.
SD-WAN, Meet MARVIS.

Juniper Networks is introducing the fourth expansion of the AI-driven enterprise to bring artificial intelligence to the LAN, WLAN and now WAN for end-to-end optimization of user experiences and proactive troubleshooting driven by Mist AI.
With the new Juniper Mist WAN Assurance service, customers will receive even better automation and insight in branch locations with AI-driven service level expectations, client-to-cloud event correlation for rapid fault resolution, anomaly detection, and proactive support.
Real AI. Real Results. Mist AI Customer Testimonials.

See what Juniper customers have to say about how Mist AI has statistically improved the way they run their business. For more information on how Mist AI can improve your network, join us for Transformation Thursdays at: https://www.juniper.net/us/en/forms/ai-driven-demo/
MetaFabric Architecture

We are excited to announce the release of MetaFabric, a new end-to-end architecture that encompasses Juniper Network’s switching, routing, software and security portfolios. It provides the freedom and flexibility to use any technology, any protocol, any orchestration platform, any SDN controller, for any data center application with the assurance of interoperability and minimal disruption.
Are you able to deliver reliable experiences for connected devices

Here are 5 things you can do with Mist Wired Assurance. With Wired Assurance, you can leverage Juniper EX switch telemetry to enable simpler operations, shorter mean time to repair, and better visibility into end-user experiences for your connected devices, including access points, servers, and IoT endpoints.
How AI Simplifies Troubleshooting Your WAN

As much the workforce continues to work remotely, The COVID-19 Pandemic has taught us that the WAN is more important than ever, and troubleshooting it couldn’t be more difficult. Learn how MARVIS & Mist AI simplify the burdensome process of troubleshooting the WAN.
SASE Future Proof sdwan 20 Sep2020 v2.1 BA

SASE Gartner’s “The Future of Network Security Is in the Cloud”
Network and Security are Converging
Cisco connect winnipeg 2018 introducing the network intuitive

Cisco connect winnipeg 2018 introducing the network intuitive
Extreme Networks IdentiFi

Award-winning IdentiFi wireless appliances provide an exceptional user experience, regardless of location.
Our Wireless Appliances are simple to deploy and manage, yet provide advanced functionality to allow organizations to define how wireless voice/video/data traffic is processed without architectural constraints and in accordance with the business needs.
The IdentiFi Wireless Appliance portfolio includes:
The C25 supporting up to 100 Access Points (APs)
The V2110 supporting up to 500 APs
The C5210 supporting up to 2,000 APs
Extreme networks - Better Connections. Better Experiences. For Everyone.

Slide งานสัมมนา Westcon Conntect 2015 ประเทศไทย
สนใจสอบถามข้อมูลเพิ่มเติมได้ทันทีที่ บริษัท Westcon Solution Thailand โทร (66) 2 938 9477-9 หรืออีเมลล์ WSTHproducts@westcon.com
Cisco connect winnipeg 2018 simple it leads to simple it management

Cisco connect winnipeg 2018 simple it leads to simple it management
IT Guide for Mobility: Making the case for Security leaders

Learn how to make the case to Security Leaders around mobility. Get Started: www.cisco.com/go/mobility
Cisco dna for mobility introduction

This is an entirely new era of networking. And you should say hello to Cisco Digital Network Architecture (DNA).
Wireless, mobility, wireless and mobility. It's a new world. Bring Wi-Fi into the digital age with Cisco DNA now.
Cisco Connect 2018 Thailand - Cisco Meraki an innovation journey to a smarter...

Cisco Connect 2018 Thailand - Cisco Meraki an innovation journey to a smarter...NetworkCollaborators
Cisco Connect 2018 Thailand i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation ...

i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation ...ProductNation/iSPIRT
i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation initiative. Started in June 2012; they work on the space of BYOD security; Their sweet spot is 100% Agentless device discovery, fingerprinting and health-check and then denying infected/malicious devices from connecting to corporate network.Cisco connect winnipeg 2018 simply powerful networking with meraki

Cisco connect winnipeg 2018 simply powerful networking with meraki
Ot ics cyberattaques dans les organisations industrielles 

Ot ics cyberattaques dans les organisations industrielles
John Merline - How make your cloud SASE 

How make your cloud SASE
John Merline
AWS Community Day | Midwest 2020
Breakfast Briefing- Natilik & Cisco Introducing The Network. Intuitive.

An extract from our latest breakfast briefing with Cisco SVP Scott Harrell. Introducing a new era in Cisco Networking, The Network. Intuitive.
Cisco Connect Halifax 2018 Cisco Meraki -let simple work for you

Cisco Connect Halifax 2018 Cisco Meraki -let simple work for you
Cisco Connect Toronto 2018 the intelligent network with cisco meraki

Cisco connect toronto 2018 the intelligent network with cisco meraki
i7 pregerine7 - Agentless byod security for Enterprises

BYOD Security - 100% agentless (Zero-touch) and Zero-latency; Only tool that works at network layer (as opposed to on the device) discovering fingerprinting health-check for all personal devices and protecting corporate network from infected/malicious/compromised personal devices.
We also the only tool that complements MDM.
TechWiseTV Workshop: Cisco DNA Center Assurance

Watch the replay: http://cs.co/9007Dbh39
In this deep dive you’ll learn how this comprehensive solution provides actionable intelligence to help you get to the right IT decision faster. And speed you on your way to an intent-based network. Learn how to gain end-to-end network visibility in one easy-to-use dashboard, make more sense out of data by eliminating noise and false positives, reduce downtime and troubleshooting time with rapid root-cause analysis and actionable insights and move beyond reactive monitoring with proactive and predictive analytics.
Resources:
Watch the related TechWiseTV episode: http://cs.co/9008DXCQi
TechWiseTV: http://cs.co/9009DzrjN
Schneider electric powers security transformation with one simple app copy

When Schneider Electric decided to undergo a digital transformation initiative, they knew their approach to security would also need to transform. As their apps moved to the cloud and their users left the network, the Schneider team needed a way to deliver consistent security controls across a globally dispersed workforce of 140,000 users.
More Related Content
What's hot
SASE Future Proof sdwan 20 Sep2020 v2.1 BA

SASE Gartner’s “The Future of Network Security Is in the Cloud”
Network and Security are Converging
Cisco connect winnipeg 2018 introducing the network intuitive

Cisco connect winnipeg 2018 introducing the network intuitive
Extreme Networks IdentiFi

Award-winning IdentiFi wireless appliances provide an exceptional user experience, regardless of location.
Our Wireless Appliances are simple to deploy and manage, yet provide advanced functionality to allow organizations to define how wireless voice/video/data traffic is processed without architectural constraints and in accordance with the business needs.
The IdentiFi Wireless Appliance portfolio includes:
The C25 supporting up to 100 Access Points (APs)
The V2110 supporting up to 500 APs
The C5210 supporting up to 2,000 APs
Extreme networks - Better Connections. Better Experiences. For Everyone.

Slide งานสัมมนา Westcon Conntect 2015 ประเทศไทย
สนใจสอบถามข้อมูลเพิ่มเติมได้ทันทีที่ บริษัท Westcon Solution Thailand โทร (66) 2 938 9477-9 หรืออีเมลล์ WSTHproducts@westcon.com
Cisco connect winnipeg 2018 simple it leads to simple it management

Cisco connect winnipeg 2018 simple it leads to simple it management
IT Guide for Mobility: Making the case for Security leaders

Learn how to make the case to Security Leaders around mobility. Get Started: www.cisco.com/go/mobility
Cisco dna for mobility introduction

This is an entirely new era of networking. And you should say hello to Cisco Digital Network Architecture (DNA).
Wireless, mobility, wireless and mobility. It's a new world. Bring Wi-Fi into the digital age with Cisco DNA now.
Cisco Connect 2018 Thailand - Cisco Meraki an innovation journey to a smarter...

Cisco Connect 2018 Thailand - Cisco Meraki an innovation journey to a smarter...NetworkCollaborators
Cisco Connect 2018 Thailand i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation ...

i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation ...ProductNation/iSPIRT
i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation initiative. Started in June 2012; they work on the space of BYOD security; Their sweet spot is 100% Agentless device discovery, fingerprinting and health-check and then denying infected/malicious devices from connecting to corporate network.Cisco connect winnipeg 2018 simply powerful networking with meraki

Cisco connect winnipeg 2018 simply powerful networking with meraki
Ot ics cyberattaques dans les organisations industrielles 

Ot ics cyberattaques dans les organisations industrielles
John Merline - How make your cloud SASE 

How make your cloud SASE
John Merline
AWS Community Day | Midwest 2020
Breakfast Briefing- Natilik & Cisco Introducing The Network. Intuitive.

An extract from our latest breakfast briefing with Cisco SVP Scott Harrell. Introducing a new era in Cisco Networking, The Network. Intuitive.
Cisco Connect Halifax 2018 Cisco Meraki -let simple work for you

Cisco Connect Halifax 2018 Cisco Meraki -let simple work for you
Cisco Connect Toronto 2018 the intelligent network with cisco meraki

Cisco connect toronto 2018 the intelligent network with cisco meraki
i7 pregerine7 - Agentless byod security for Enterprises

BYOD Security - 100% agentless (Zero-touch) and Zero-latency; Only tool that works at network layer (as opposed to on the device) discovering fingerprinting health-check for all personal devices and protecting corporate network from infected/malicious/compromised personal devices.
We also the only tool that complements MDM.
TechWiseTV Workshop: Cisco DNA Center Assurance

Watch the replay: http://cs.co/9007Dbh39
In this deep dive you’ll learn how this comprehensive solution provides actionable intelligence to help you get to the right IT decision faster. And speed you on your way to an intent-based network. Learn how to gain end-to-end network visibility in one easy-to-use dashboard, make more sense out of data by eliminating noise and false positives, reduce downtime and troubleshooting time with rapid root-cause analysis and actionable insights and move beyond reactive monitoring with proactive and predictive analytics.
Resources:
Watch the related TechWiseTV episode: http://cs.co/9008DXCQi
TechWiseTV: http://cs.co/9009DzrjN
Schneider electric powers security transformation with one simple app copy

When Schneider Electric decided to undergo a digital transformation initiative, they knew their approach to security would also need to transform. As their apps moved to the cloud and their users left the network, the Schneider team needed a way to deliver consistent security controls across a globally dispersed workforce of 140,000 users.
What's hot (20)
Cisco Connect 2018 Philippines - introducing cisco dna assurance

Cisco Connect 2018 Philippines - introducing cisco dna assurance
Cisco connect winnipeg 2018 introducing the network intuitive

Cisco connect winnipeg 2018 introducing the network intuitive
[Cisco Connect 2018 - Vietnam] Yedu s. introducing cisco dna assurance![[Cisco Connect 2018 - Vietnam] Yedu s. introducing cisco dna assurance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Cisco Connect 2018 - Vietnam] Yedu s. introducing cisco dna assurance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Cisco Connect 2018 - Vietnam] Yedu s. introducing cisco dna assurance
Extreme networks - Better Connections. Better Experiences. For Everyone.

Extreme networks - Better Connections. Better Experiences. For Everyone.
Cisco connect winnipeg 2018 simple it leads to simple it management

Cisco connect winnipeg 2018 simple it leads to simple it management
IT Guide for Mobility: Making the case for Security leaders

IT Guide for Mobility: Making the case for Security leaders
Cisco Connect 2018 Thailand - Cisco Meraki an innovation journey to a smarter...

Cisco Connect 2018 Thailand - Cisco Meraki an innovation journey to a smarter...
i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation ...

i7 Networks - Presentation at Zensar #TechShowcase - An iSPIRT ProductNation ...
Cisco connect winnipeg 2018 simply powerful networking with meraki

Cisco connect winnipeg 2018 simply powerful networking with meraki
Ot ics cyberattaques dans les organisations industrielles 

Ot ics cyberattaques dans les organisations industrielles
Breakfast Briefing- Natilik & Cisco Introducing The Network. Intuitive.

Breakfast Briefing- Natilik & Cisco Introducing The Network. Intuitive.
Cisco Connect Halifax 2018 Cisco Meraki -let simple work for you

Cisco Connect Halifax 2018 Cisco Meraki -let simple work for you
Cisco Connect Toronto 2018 the intelligent network with cisco meraki

Cisco Connect Toronto 2018 the intelligent network with cisco meraki
i7 pregerine7 - Agentless byod security for Enterprises

i7 pregerine7 - Agentless byod security for Enterprises
Schneider electric powers security transformation with one simple app copy

Schneider electric powers security transformation with one simple app copy
Similar to Securing IoT at Scale Requires a Holistic Approach
Cybersecurity In IoT Challenges And Effective Strategies.pdf

Explore the world of IoT cybersecurity. Expose challenges and discover effective strategies to secure your digital security. Stay secure in the dynamical landscape of cybersecurity in IoT.
Cybersecurity in the Age of IoT - Skillmine

Cybersecurity stands as the bedrock of our digital world, safeguarding systems, networks, and data from a rising tide of cyber threats. In the era of the Internet of Things (IoT), wherean ever-expanding array of devices and objects are seamlessly interconnected, the importance of cybersecurity has escalated to unprecedented levels.
Strengthening IoT Security Against Cyber Threats.pdf

The future of IoT is not just about connectivity; it's about securing the connections that make our lives easier, safer, and more efficient.
Just-How-Secure-is-your-Remote-Workforce-Infinity-Group-Ebook.pdf

In this comprehensive ebook from Infinity Group, we highlight cyber security threats and the practical steps you can embark on to promote an effective remote and hybrid workforce for your business.
Security Challenges in IoT Software Development and Possible Solutions.pdf

However, this type of accessibility has security threats and issues. IoT devices are known to be vulnerable to security risks when they first connect to corporate networks, which may result in security breaches and expose a company's assets to cyberattacks. IoT security is essential for companies that want to reap the benefits of IoT software development and minimize security risks.
Cybersecurity

Cyber crimes are on the rise and especially prevalent during the global pandemic where hackers leverage the vulnerabilities of organisations for new opportunities through technology.
Hospitals, for instance, are more likely to pay ransoms to restore access to their servers. Similarly, criminals may believe that corporations grappling with economic turmoil or logistical crises will be similarly easy to manipulate.
Final Research Project - Securing IoT Devices What are the Challe.docx

Final Research Project - Securing IoT Devices: What are the Challenges?
Internet security, in general, is a challenge that we have been dealing with for decades. It is a regular topic of discussion and concern, but a relatively new segment of internet security is getting most attention—internet of things (IoT). So why is internet of things security so important?
The high growth rate of IoT should get the attention of cybersecurity professionals. The rate at which new technology goes to market is inversely proportional to the amount of security that gets designed into the product. According to IHS Markit, “The number of connected IoT devices worldwide will jump 12 percent on average annually, from nearly 27 billion in 2017 to 125 billion in 2030.”
IoT devices are quite a bit different from other internet-connected devices such as laptops and servers. They are designed with a single purpose in mind, usually running minimal software with minimal resources to serve that purpose. Adding the capability to run and update security software is often not taken into consideration.
Due to the lack of security integrated into IoT devices, they present significant risks that must be addressed. IoT security is the practice of understanding and mitigating these risks. Let’s consider the challenges of IoT security and how we can address them.
Some security practitioners suggest that key IoT security steps include:
1. Make people aware that there is a threat to security;
2. Design a technical solution to reduce security vulnerabilities;
3. Align the legal and regulatory frameworks; and
4. Develop a workforce with the skills to handle IoT security.
Final Assignment - Project Plan (Deliverables):
1) Address each of the FOURIoT security steps listed above in terms of IoT devices.
2) Explain in detail, in a step-by-step guide, how to make people more aware of the problems associated with the use of IoT devices.
Bottom of Form
Top of Form
Bottom of Form
IoT References:
https://www.techrepublic.com/article/how-to-secure-your-iot-devices-from-botnets-and-other-threats/
https://www.peerbits.com/blog/biggest-iot-security-challenges.html
https://www.bankinfosecurity.asia/securing-iot-devices-challenges-a-11138
https://www.sumologic.com/blog/iot-security/
https://news.ihsmarkit.com/press-release/number-connected-iot-devices-will-surge-125-billion-2030-ihs-markit-says
https://cdn.ihs.com/www/pdf/IoT_ebook.pdf
https://go.armis.com/hubfs/Buyers%E2%80%99%20Guide%20to%20IoT%20Security%20-Final.pdf
https://www.techrepublic.com/article/smart-farming-how-iot-robotics-and-ai-are-tackling-one-of-the-biggest-problems-of-the-century/
Video Resources:What is the Internet of Things (IoT) and how can we secure it?
https://www.youtube.com/watch?v=H_X6IP1-NDc
What is the problem with IoT security? - Gary explains
https://www.youtube.com/watch?v=D3yrk4TaIQQ
What are the Challenges of IoT Security?
IoT has many of the same security challenges that other systems have. There are, howe.
Final Research Project - Securing IoT Devices What are the Challe.docx

Final Research Project - Securing IoT Devices: What are the Challenges?
Internet security, in general, is a challenge that we have been dealing with for decades. It is a regular topic of discussion and concern, but a relatively new segment of internet security is getting most attention—internet of things (IoT). So why is internet of things security so important?
The high growth rate of IoT should get the attention of cybersecurity professionals. The rate at which new technology goes to market is inversely proportional to the amount of security that gets designed into the product. According to IHS Markit, “The number of connected IoT devices worldwide will jump 12 percent on average annually, from nearly 27 billion in 2017 to 125 billion in 2030.”
IoT devices are quite a bit different from other internet-connected devices such as laptops and servers. They are designed with a single purpose in mind, usually running minimal software with minimal resources to serve that purpose. Adding the capability to run and update security software is often not taken into consideration.
Due to the lack of security integrated into IoT devices, they present significant risks that must be addressed. IoT security is the practice of understanding and mitigating these risks. Let’s consider the challenges of IoT security and how we can address them.
Some security practitioners suggest that key IoT security steps include:
1. Make people aware that there is a threat to security;
2. Design a technical solution to reduce security vulnerabilities;
3. Align the legal and regulatory frameworks; and
4. Develop a workforce with the skills to handle IoT security.
Final Assignment - Project Plan (Deliverables):
1) Address each of the FOURIoT security steps listed above in terms of IoT devices.
2) Explain in detail, in a step-by-step guide, how to make people more aware of the problems associated with the use of IoT devices.
Bottom of Form
Top of Form
Bottom of Form
IoT References:
https://www.techrepublic.com/article/how-to-secure-your-iot-devices-from-botnets-and-other-threats/
https://www.peerbits.com/blog/biggest-iot-security-challenges.html
https://www.bankinfosecurity.asia/securing-iot-devices-challenges-a-11138
https://www.sumologic.com/blog/iot-security/
https://news.ihsmarkit.com/press-release/number-connected-iot-devices-will-surge-125-billion-2030-ihs-markit-says
https://cdn.ihs.com/www/pdf/IoT_ebook.pdf
https://go.armis.com/hubfs/Buyers%E2%80%99%20Guide%20to%20IoT%20Security%20-Final.pdf
https://www.techrepublic.com/article/smart-farming-how-iot-robotics-and-ai-are-tackling-one-of-the-biggest-problems-of-the-century/
Video Resources:What is the Internet of Things (IoT) and how can we secure it?
https://www.youtube.com/watch?v=H_X6IP1-NDc
What is the problem with IoT security? - Gary explains
https://www.youtube.com/watch?v=D3yrk4TaIQQ
What are the Challenges of IoT Security?
IoT has many of the same security challenges that other systems have. There are, howe ...
IoT Security Why Hiring Skilled Developers is Crucial for Protecting Your Dev...

The Internet of Things (IoT) has revolutionized the way we interact with technology. From smart homes to industrial automation, IoT devices have become an integral part of our daily lives. However, with this increasing dependency on interconnected devices comes the pressing concern of security vulnerabilities. As the number of IoT devices grows, so does the risk of cyberattacks and data breaches. This article explores the importance of hiring skilled developers to build secure IoT applications and the benefits they bring in protecting your devices.
Software security, secure software development in the age of IoT, smart thing...

How to design secure software products for IoT, embedded application, smart metering, smart lighting, medical application with the help of Common Criteria
Cybersecurity and continuous intelligence

Welcome to the cybersecurity & continuous intelligence knowledge slidedeck of NISI (Nederlands Instituut voor de Software Industrie).
Cybersecurity & Continuous Intelligence is a broad topic, covering rules & regulation, internet, cyberwar, software, machine learning and society & trust.
This slidedeck offers you a more in-depth view of this exciting area.
Please contact us directly for more information via email info@nisi.nl or the contact on form on nisi.nl.
Nederlands Instituut voor de Software Industrie
Best Practices for Cloud-Based IoT Security

Cloud-based IoT solutions are the future for digital products and services. However, the security risks associated with virtual infrastructures can’t be ignored either. Cybercriminals are constantly finding new ways to carry out malicious attacks and call for tighter security practices. Thankfully, building IoT solutions on the cloud is a solution and can significantly bolster the network’s security.
IoT security and privacy: main challenges and how ISOC-OTA address them

Internet Society (ISOC) aims are:
make security an integrated function of connected objects and encourages IoT device and service providers for consumers to adopt the Online Trust Alliance (OTA) security and privacy principles ;
increase the consumer demand for security and privacy in the IoT devices they purchase;
create government policies and regulations that promote better security and privacy features in IoT devices.
Networking Expertise

Because IP video cameras are networked, partnering with a technology vendor who knows networking technologies is critical. This is a skill that many traditional video surveillance firms lack thus increasing the reliability of the network security service provider.
Similar to Securing IoT at Scale Requires a Holistic Approach (20)
kaspersky presentation for palette business solution June 2016 v1.0.

kaspersky presentation for palette business solution June 2016 v1.0.
Cybersecurity In IoT Challenges And Effective Strategies.pdf

Cybersecurity In IoT Challenges And Effective Strategies.pdf
Strengthening IoT Security Against Cyber Threats.pdf

Strengthening IoT Security Against Cyber Threats.pdf
Just-How-Secure-is-your-Remote-Workforce-Infinity-Group-Ebook.pdf

Just-How-Secure-is-your-Remote-Workforce-Infinity-Group-Ebook.pdf
Security Challenges in IoT Software Development and Possible Solutions.pdf

Security Challenges in IoT Software Development and Possible Solutions.pdf
Final Research Project - Securing IoT Devices What are the Challe.docx

Final Research Project - Securing IoT Devices What are the Challe.docx
Final Research Project - Securing IoT Devices What are the Challe.docx

Final Research Project - Securing IoT Devices What are the Challe.docx
IoT Security Why Hiring Skilled Developers is Crucial for Protecting Your Dev...

IoT Security Why Hiring Skilled Developers is Crucial for Protecting Your Dev...
Software security, secure software development in the age of IoT, smart thing...

Software security, secure software development in the age of IoT, smart thing...
IoT security and privacy: main challenges and how ISOC-OTA address them

IoT security and privacy: main challenges and how ISOC-OTA address them
More from Juniper Networks
Stop Doing These 5 Things with Your SD-WAN

It's time to scale way back on those support tickets from your branch users. Security shouldn’t come at the cost of performance. Register now to attend a live demo. You may be eligible to receive a free SRX!
https://www.juniper.net/sdwan-thursdays
Smart Solutions for Smart Communities: What's Next & Who's Responsible?

Juniper Networks EMEA - Smart Solutions for Smart Communities: What's Next and Who's Responsible?
Are You Ready for Digital Cohesion?

We recently conducted a 16-country survey to gauge the appetite for Digital Cohesion. The results suggest business and consumer users see Digital Cohesion as an inevitable, positive societal development.
Juniper vSRX - Fast Performance, Low TCO

A quick look at how the industry's fastest virtual firewall also sports the lowest Total Cost of Ownership (TCO) to better support today's businesses.
SDN and NFV: Transforming the Service Provider Organization

As competition increases, service providers must be able to respond quickly to competitive pressures and rapidly evolving customer demands. Learn how NFV and SDN allows service providers to embrace a holistic approach to their business transformation and maximize existing capabilities: http://juni.pr/1JQZYOl
Navigating the Uncertain World Facing Service Providers - Juniper's Perspective

Service providers are facing more and more pressure as customers demand immediacy. Learn how adopting a carrier-grade, open network platform closes the innovation gap to create value for your network. http://juni.pr/1JQZYOl
NFV Solutions for the Telco Cloud 

Network service providers—those with access networks like DSL, cable, or mobile—continue
to face a dual threat: rising operating expenses associated with explosive bandwidth growth
and declining revenues driven by commoditization. A true Telco cloud, featuring automation
and dynamic scalability, becomes a comprehensive delivery platform enabling network service
providers to offer differentiated services that solve their customer’s business demands.
Juniper SRX5800 Infographic

With mobile subscriptions expected to reach 8.5 billion users by the end of 2016, mobile attack surfaces are growing at an alarming rate. Juniper’s SRX5800 is primed for this increase - with speeds up to 2 Tbps the SRX5800 enables customers to inspect more traffic faster. Mobile has met its match. http://juni.pr/1MKBQDu
Infographic: 90% MetaFabric Customer Satisfaction

Over 90% of MetaFabric customers report being satisfied with their network. Read the blog to learn more: http://juni.pr/1JMlWa6
High performance data center computing using manageable distributed computing

Terrapin Trading Show Chicago, Thursday, June 4
Andy Bach, FSI Architect, Juniper Networks
Distributed computing concepts (QFX5100-AA)
Scale and performance enhancements (QFX10000 Series)
Automation capabilities (tie in QFX-PFA)
Larry Van Deusen, Director of the Network Integration Business Unit, Dimension Data
Automation
Value Added Partner Services
What Are Virtual Chassis and Virtual Chassis Fabric?

This Day One book poster explains the differences between Virtual Chassis and Virtual Chassis Fabric.
For additional technical resources, please visit: www.juniper.net/documentation/
MetaFabric Architectures 1.0 - Virtualized IT Data Center

Design and implement an IT data center that supports a virtualized environment to run business-critical applications.
WAN Solution Meets The Challenges Of The Large Enterprise Solution Brief

This solution brief walks you through how WAN solutions enable cloud adoption and service expansion for large enterprises.
Juniper switching infographic_final_0415[2]![Juniper switching infographic_final_0415[2]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Juniper switching infographic_final_0415[2]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
As clouds become increasingly important to businesses and individuals, really there is no predicting how fast or how much your data center or cloud network will need to scale. Enter the QFX10000 line of switches.
The Case for Disaggregation of Compute in the Data Center

Maximizing Data Center Performance in Financial Services.
Andrew Bach, Chief Architect for Financial Services, Juniper Networks.
More from Juniper Networks (20)
Smart Solutions for Smart Communities: What's Next & Who's Responsible?

Smart Solutions for Smart Communities: What's Next & Who's Responsible?
SDN and NFV: Transforming the Service Provider Organization

SDN and NFV: Transforming the Service Provider Organization
Navigating the Uncertain World Facing Service Providers - Juniper's Perspective

Navigating the Uncertain World Facing Service Providers - Juniper's Perspective
High performance data center computing using manageable distributed computing

High performance data center computing using manageable distributed computing
What Are Virtual Chassis and Virtual Chassis Fabric?

What Are Virtual Chassis and Virtual Chassis Fabric?
MetaFabric Architectures 1.0 - Virtualized IT Data Center

MetaFabric Architectures 1.0 - Virtualized IT Data Center
WAN Solution Meets The Challenges Of The Large Enterprise Solution Brief

WAN Solution Meets The Challenges Of The Large Enterprise Solution Brief
The Case for Disaggregation of Compute in the Data Center

The Case for Disaggregation of Compute in the Data Center
Recently uploaded
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Recently uploaded (20)
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Securing IoT at Scale Requires a Holistic Approach
- 1. IoT Security Risks are Highly Diverse Biggest Business Concerns Biggest IoT Challenges What Keeps IoT Leaders Up at Night For more IoT resources, visit www.juniper.net/iot 3050049-002-EN Juniper partnered with the IoT Institute to find out. We surveyed 176 technology decision makers and influencers who have been personally involved in their IoT security strategy and implementations. Here's what the survey found: Sophisticated, hard-to-detect IoT threats Compliance Inability of disparate systems to work together, delaying threat response Not enough staff to keep up Privacy compromise Critical business data breach because of IoT device vulnerability IoT malware proliferation IoT equipment damage from remote hijack Service downtime due to IoT botnet DDoS attack The problem is multidimensional, with broad impact across enterprises. 72% agree the network is critical or very important to protect against IoT threats. Securing IoT at Scale Requires a Holistic Approach Enterprises are moving from small IoT pilots to large- scale implementations. What are the biggest security concerns, and how can you overcome them? In a world of unknowns, the biggest worry are zero-day attacks. End-to-end security is key. Scaling-up IoT projects and a cybersecurity skills shortage drives the enterprise need for expert help. Enterprises view the network as defending against threats. 66% IoT Security Investment Priorities The Network is Critical to Secure IoT IoT Endpoint IoT Edge Network Cloud Companies that implemented multiple IoT projects are to rate the network as critical. 9x more likely Copyright 2018 Juniper Networks, Inc. All rights reserved. Juniper Networks, the Juniper Networks logo, and Junos are registered trademarks of Juniper Networks, Inc. in the United States and other countries. All other trademarks, service marks, registered marks, or registered service marks are the property of their respective owners. Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify, transfer, or otherwise revise this publication without notice. IoT Workloads Span Multiple Locations Not running on any cloud Two or more clouds One cloud IoT systems must be protected everywhere. 59% 58% 57% 54% 39% 51% 37% 36% Where IoTApplications Run 45% 26% 29% Perimeter Security is Not Enough Double-Digit Demand for Managed IoT Security Services 49% agree that perimeter-based firewalls alone are not sufficient to provide IoT security. IoT applications and workloads run across private data centers, at the edge, and in multiple clouds. 1 2 3 4 use managed security services today plan to add managed security services in the next 18 months 42% 34% You know that security is critical, especially as you move your IoT systems into production. You need security that takes a holistic approach to detecting and stopping threats. Juniper’s Software-Defined Secure Network framework activates the entire network as a unified cybersecurity platform, with analytics and machine learning that defend against IoT threats. Your IoT Success Depends on Security At Scale
