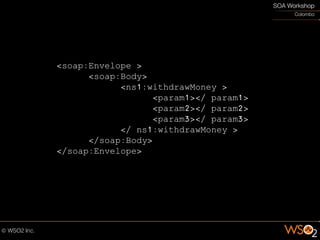
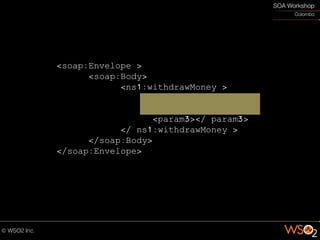
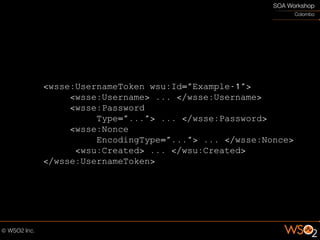
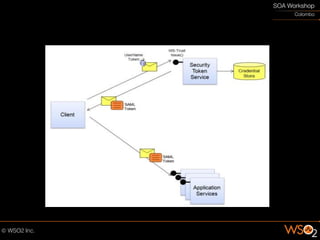
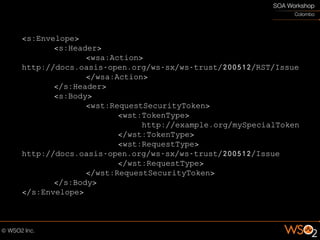
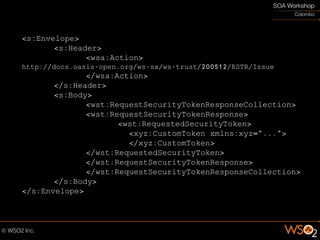
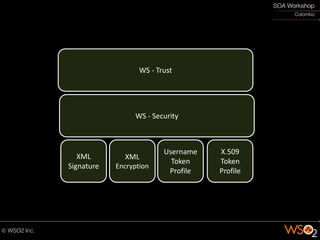
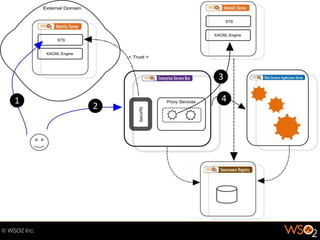
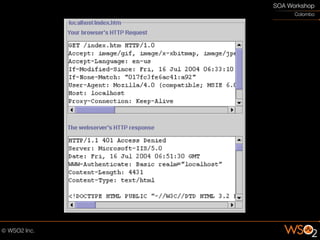
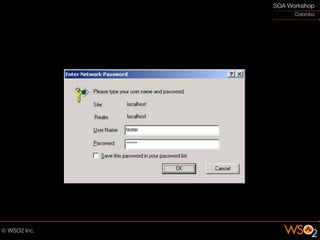
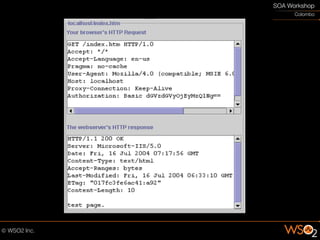
The document discusses the importance of securing web services to protect data from potential exposure and alteration by unauthorized users, emphasizing that HTTPS only provides transport-level security. It outlines methods for enhancing security at the message level using XML encryption, signatures, and WS-Security protocols to ensure confidentiality, integrity, and authentication. Additionally, the document highlights the challenges of managing authentication for external users and communicating security requirements with external domains.




![CLIENT_CERT_REQUEST
[Optional]](https://image.slidesharecdn.com/soasecurity-090923022439-phpapp01/85/Secured-SOA-32-320.jpg)
![CLIENT_CERT
[Optional]](https://image.slidesharecdn.com/soasecurity-090923022439-phpapp01/85/Secured-SOA-33-320.jpg)
![CERTIFICATE_VERIFY
[Optional]](https://image.slidesharecdn.com/soasecurity-090923022439-phpapp01/85/Secured-SOA-35-320.jpg)