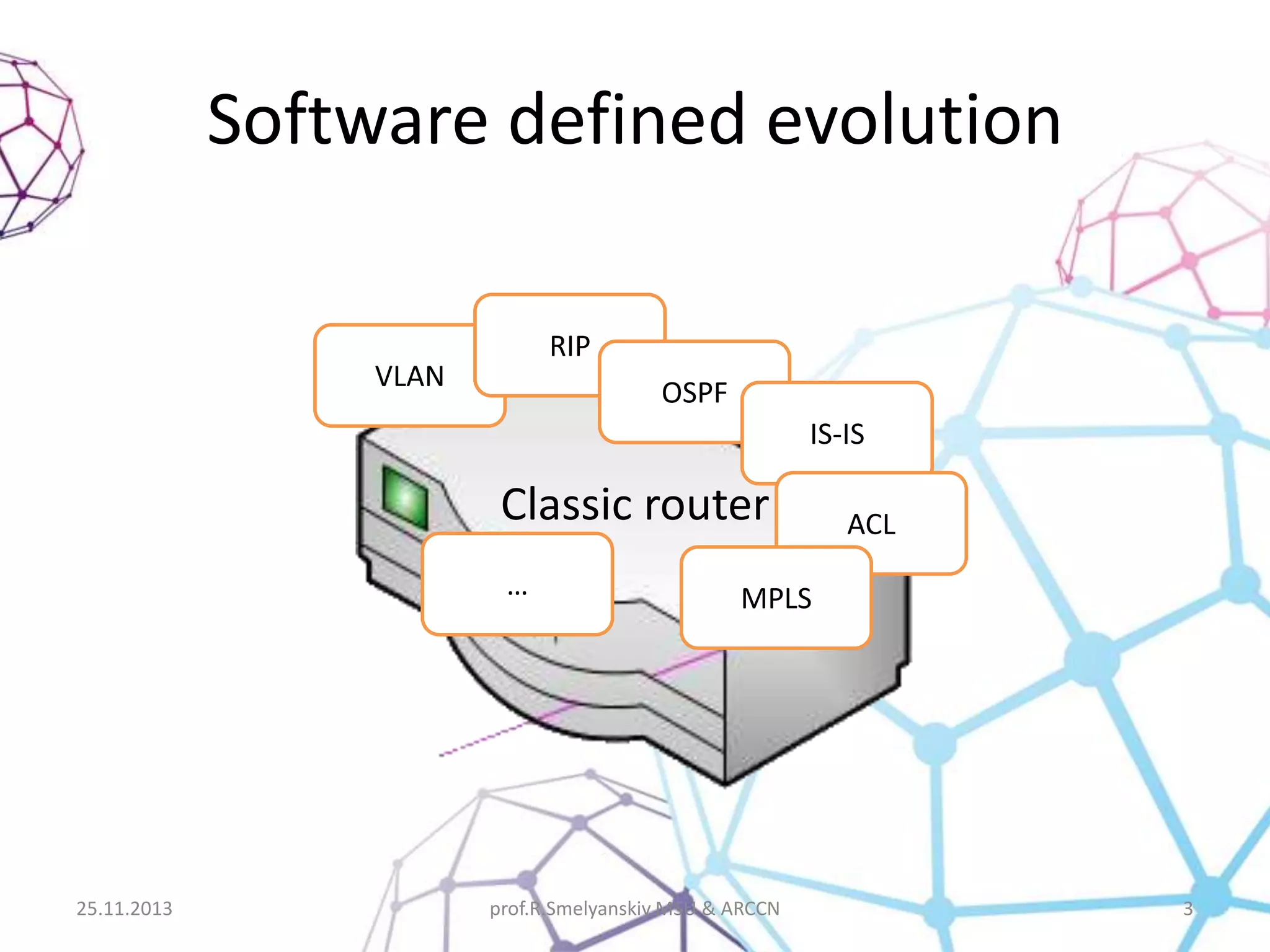
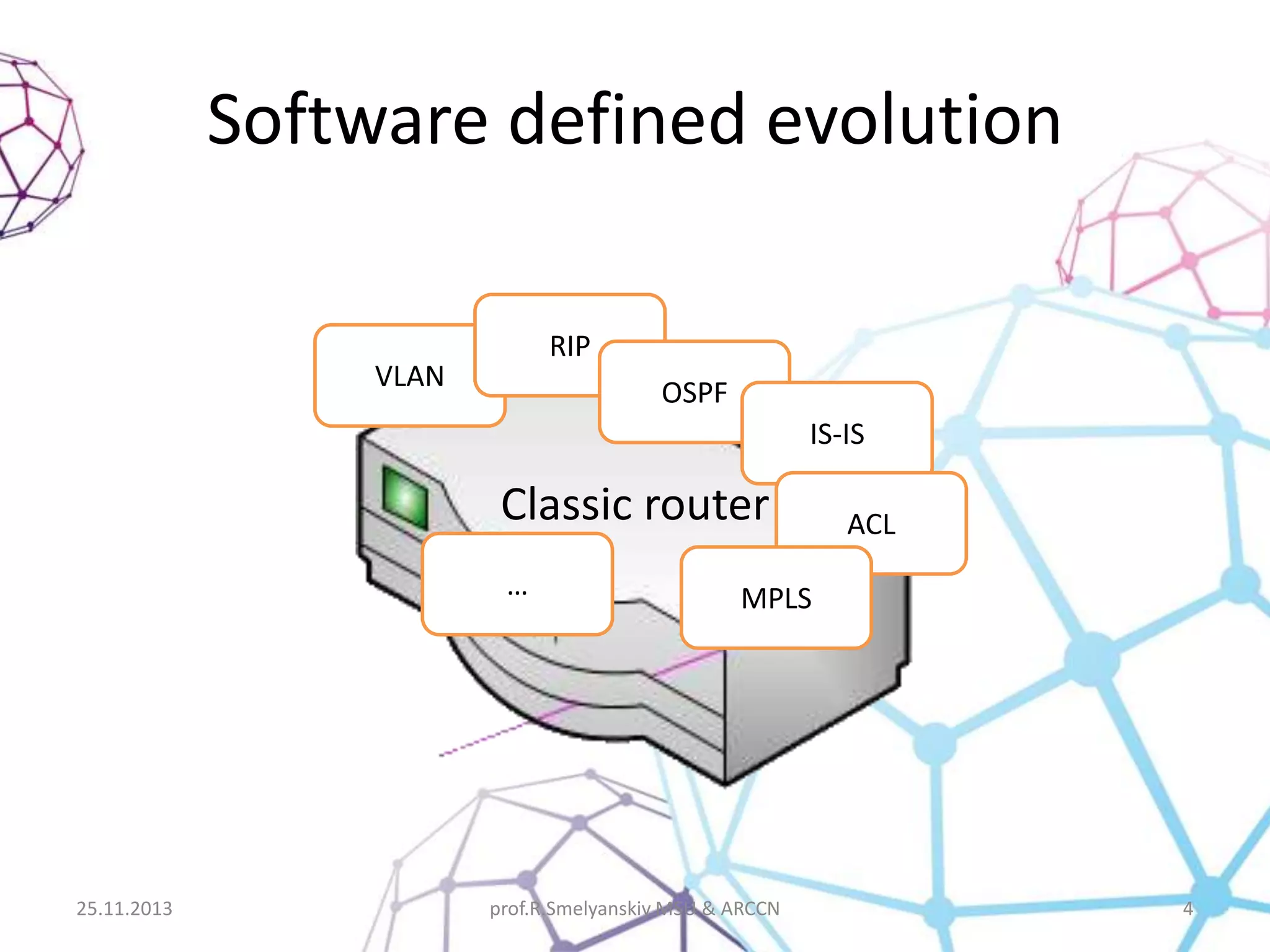
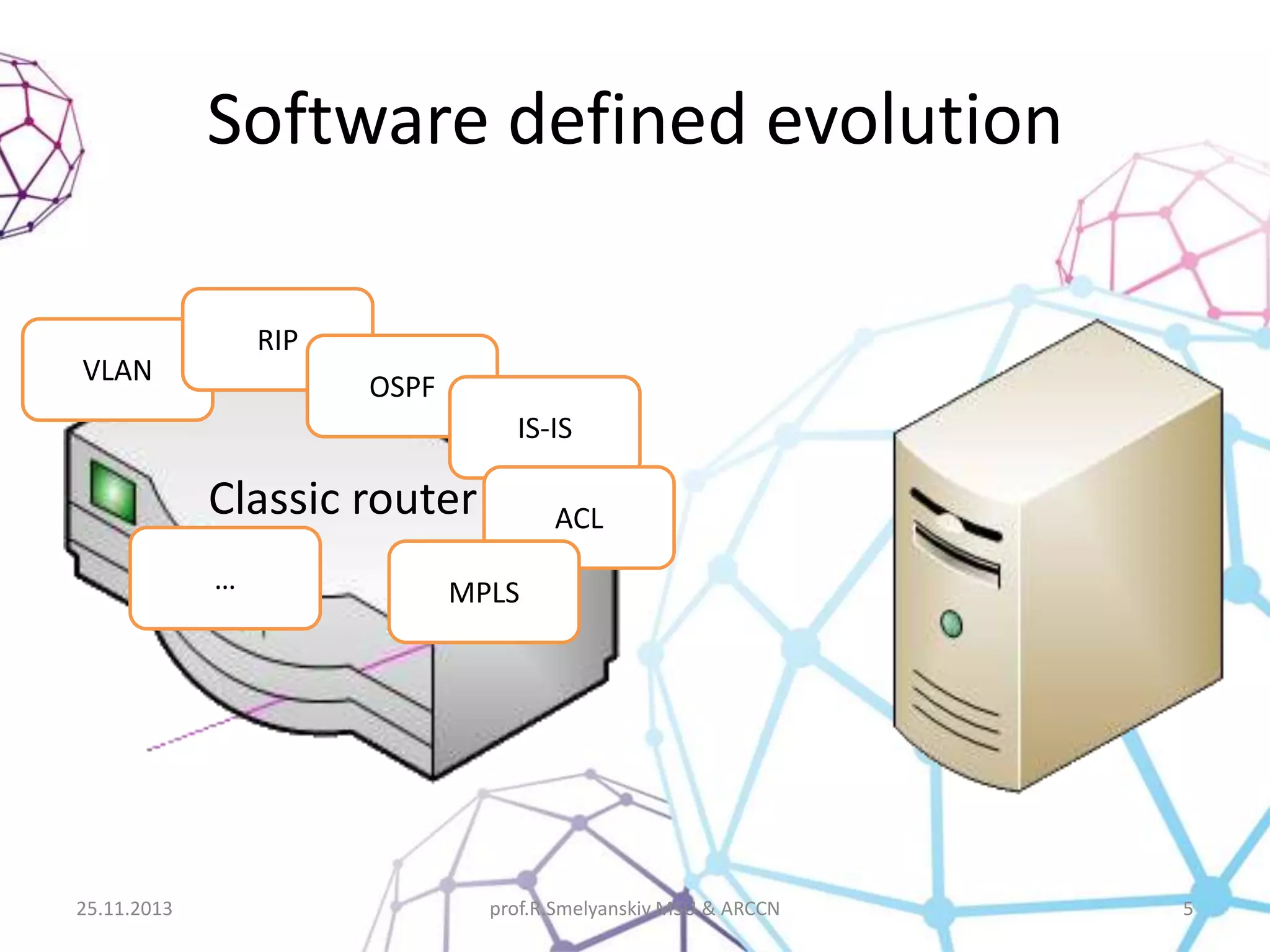
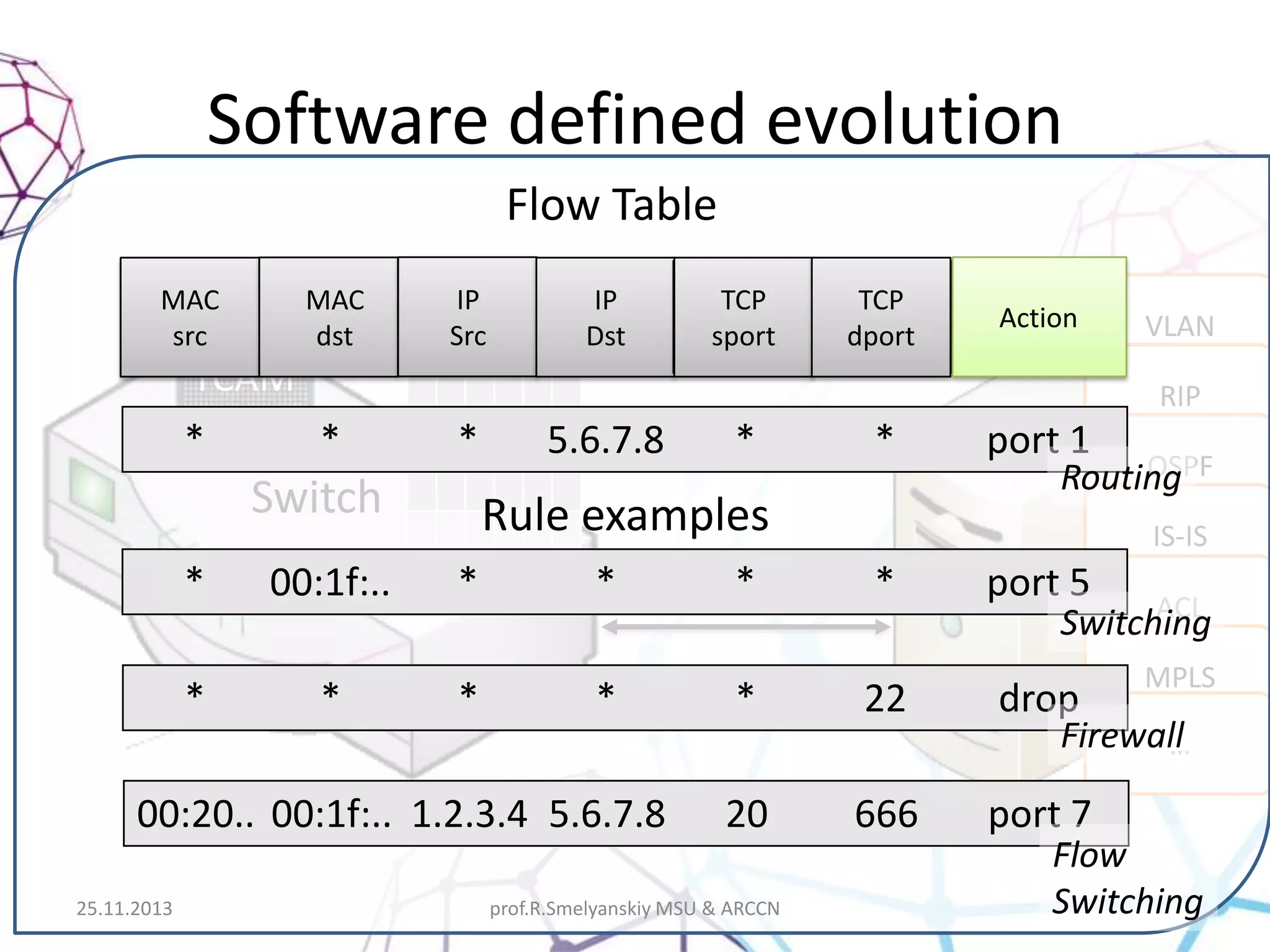
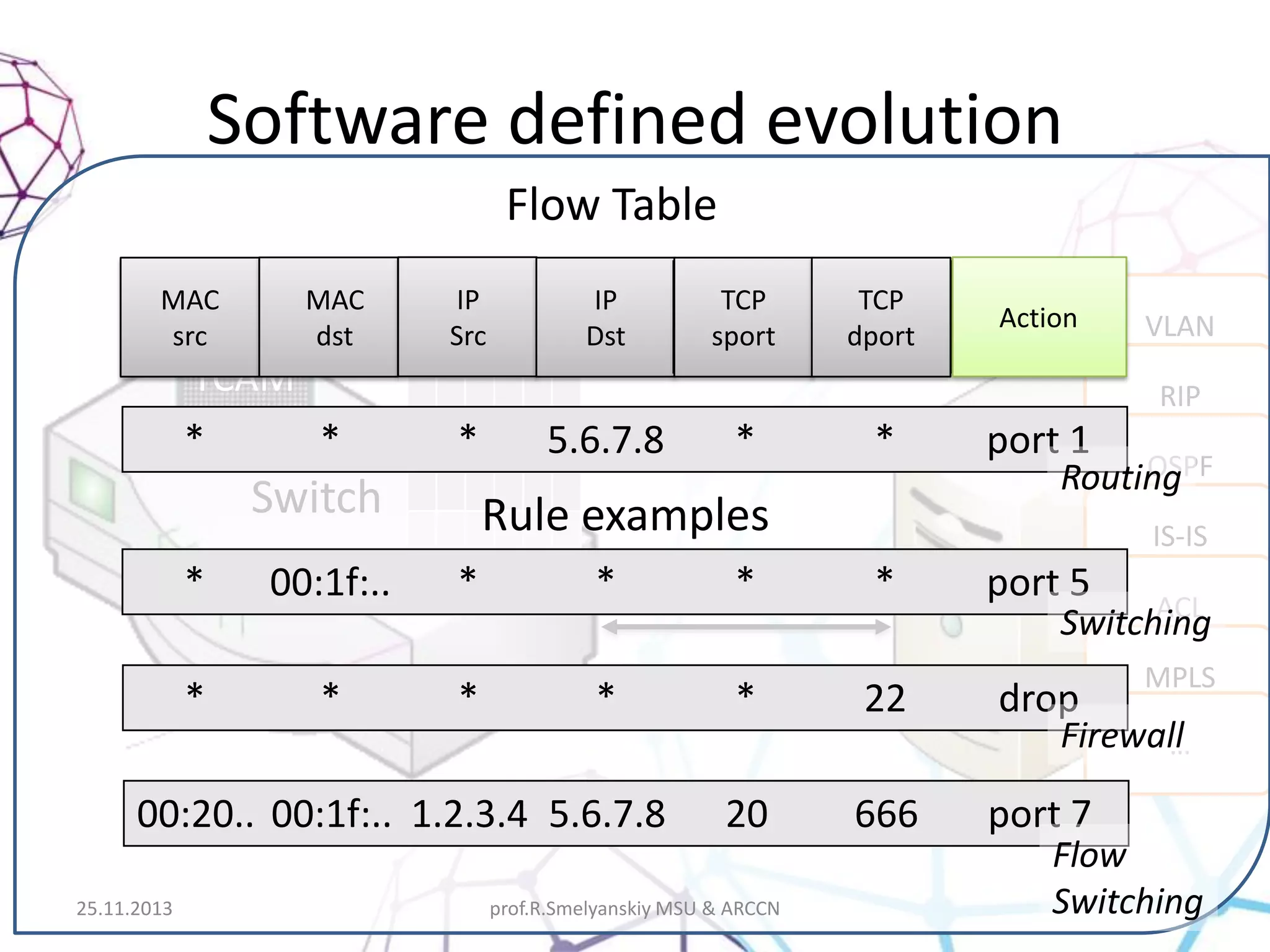
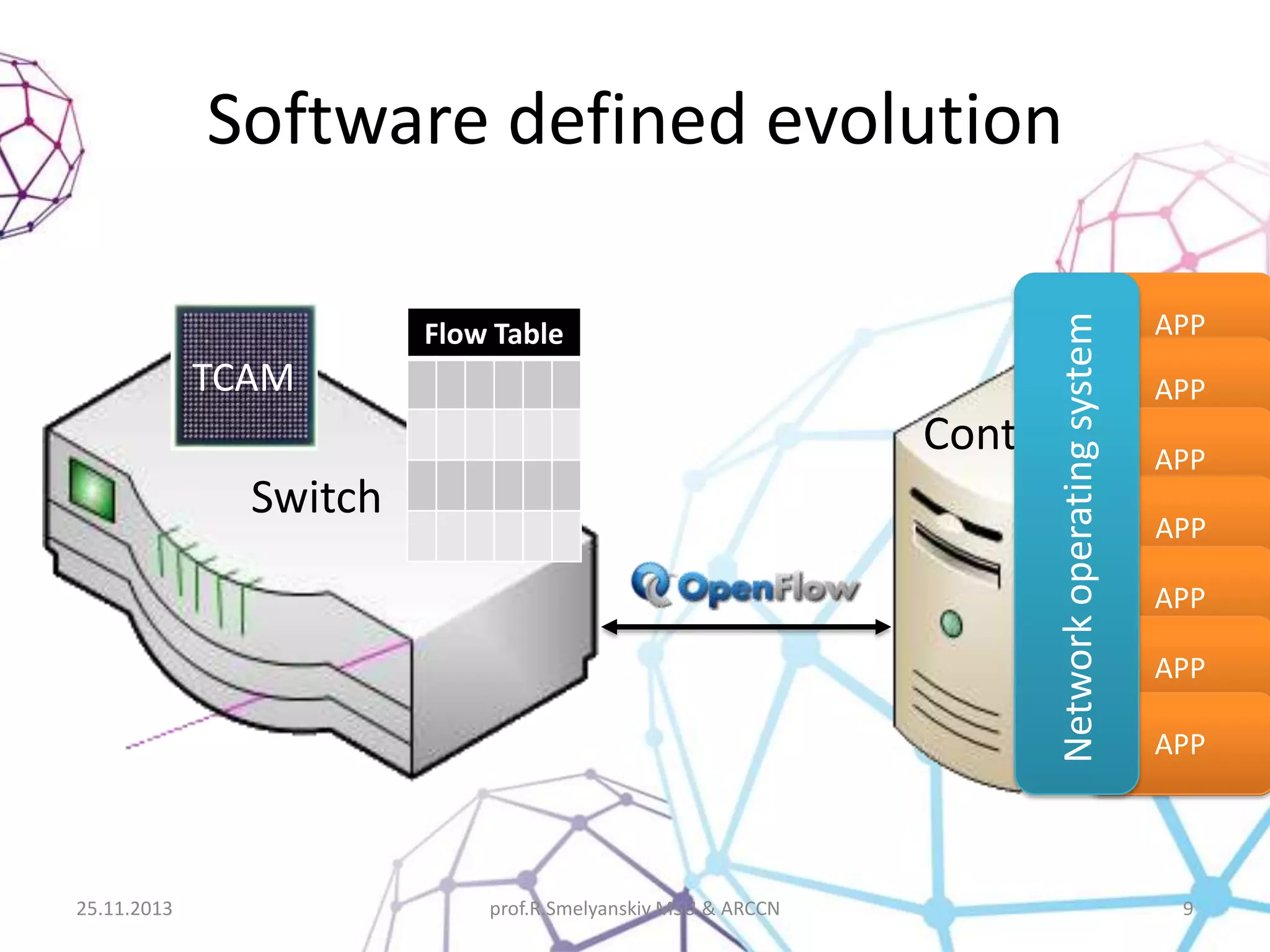
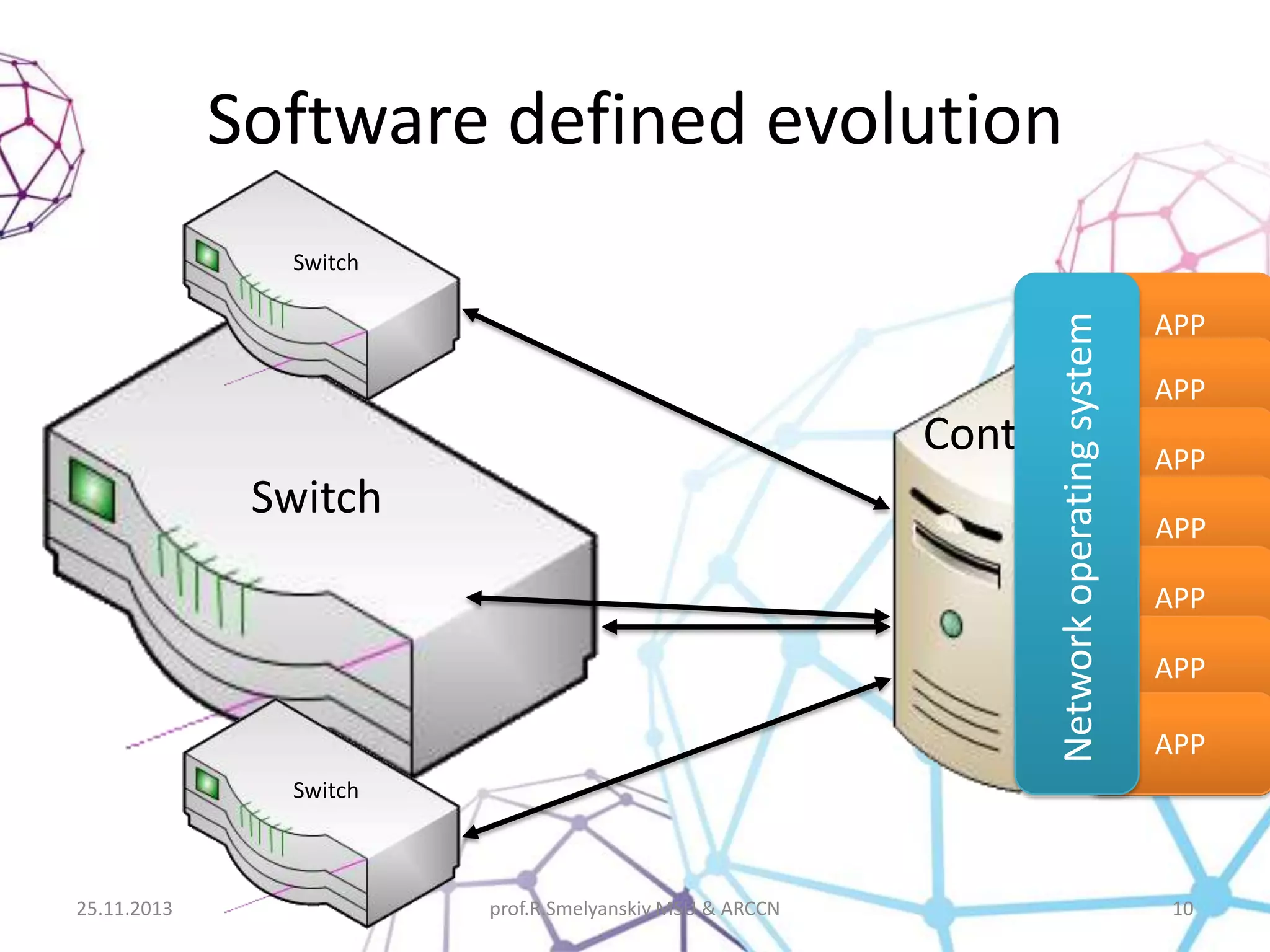
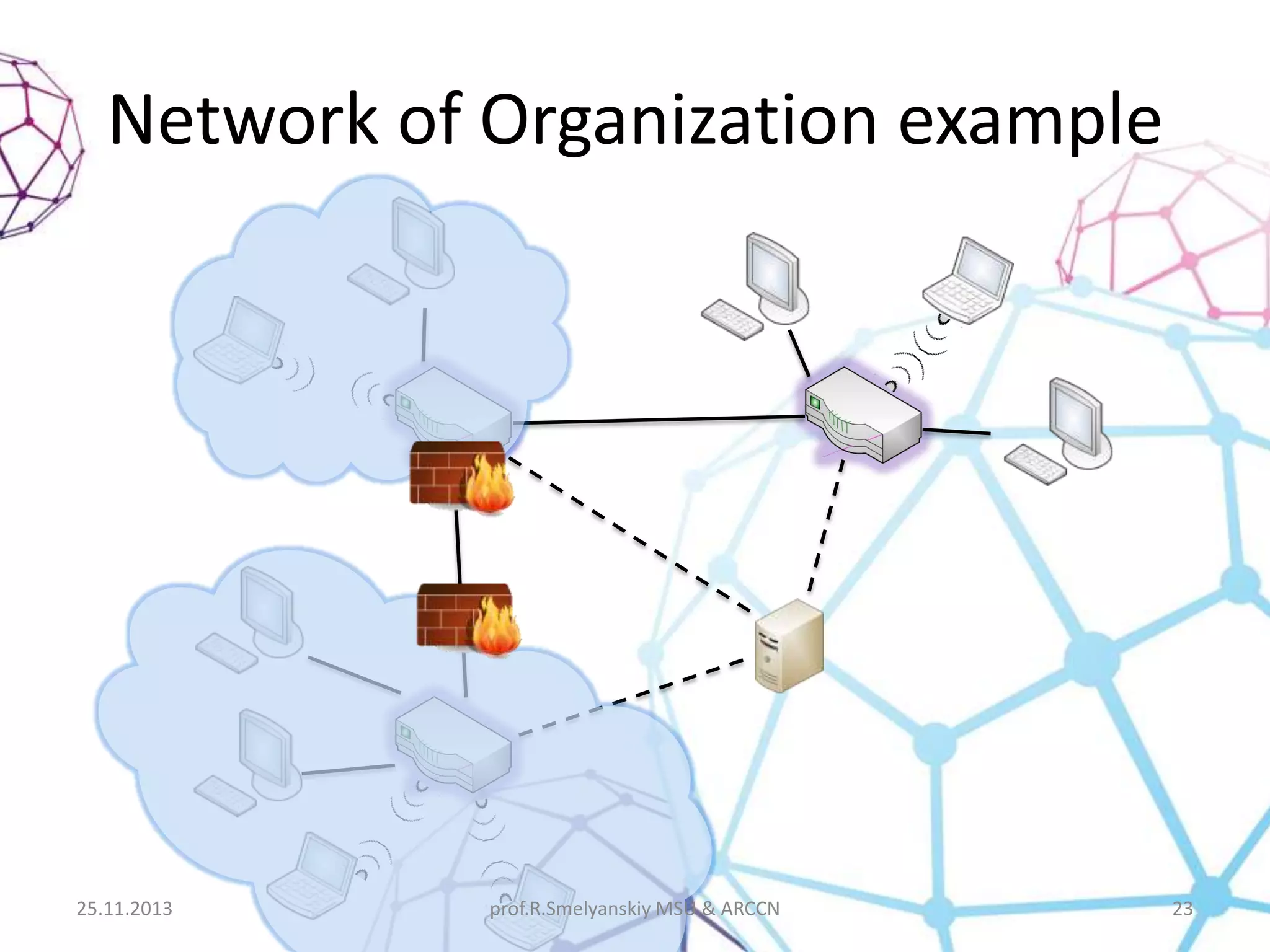
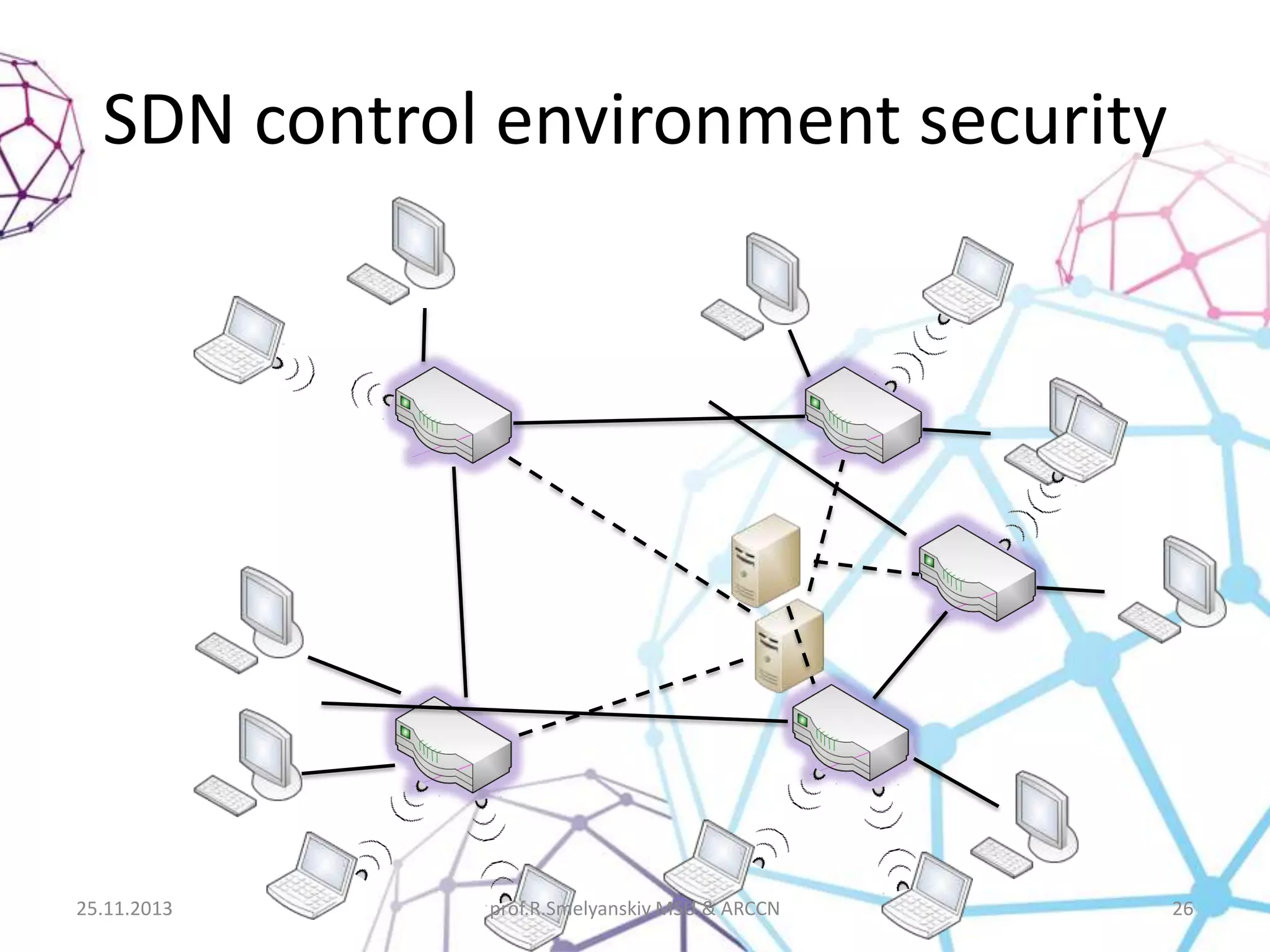
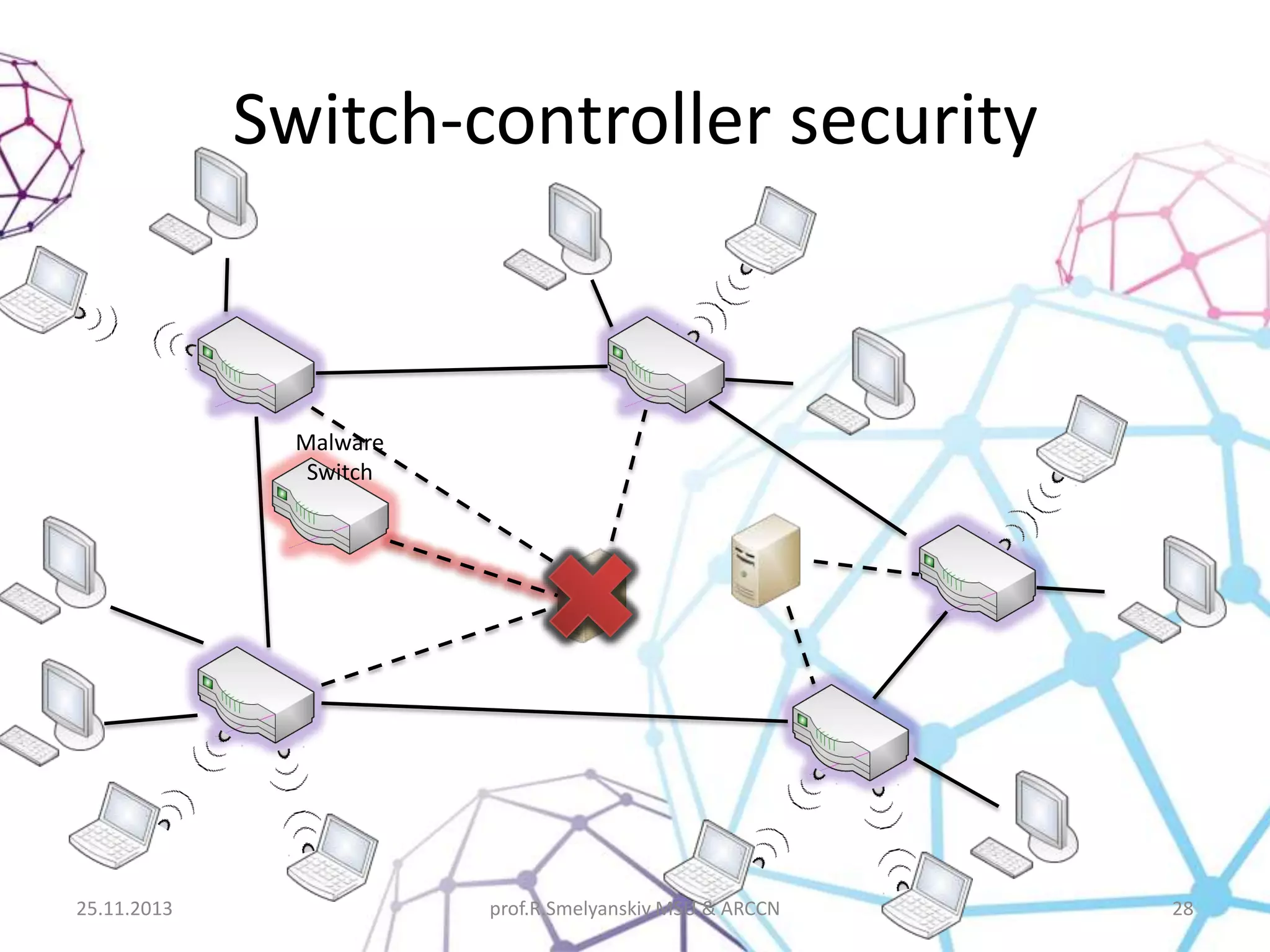
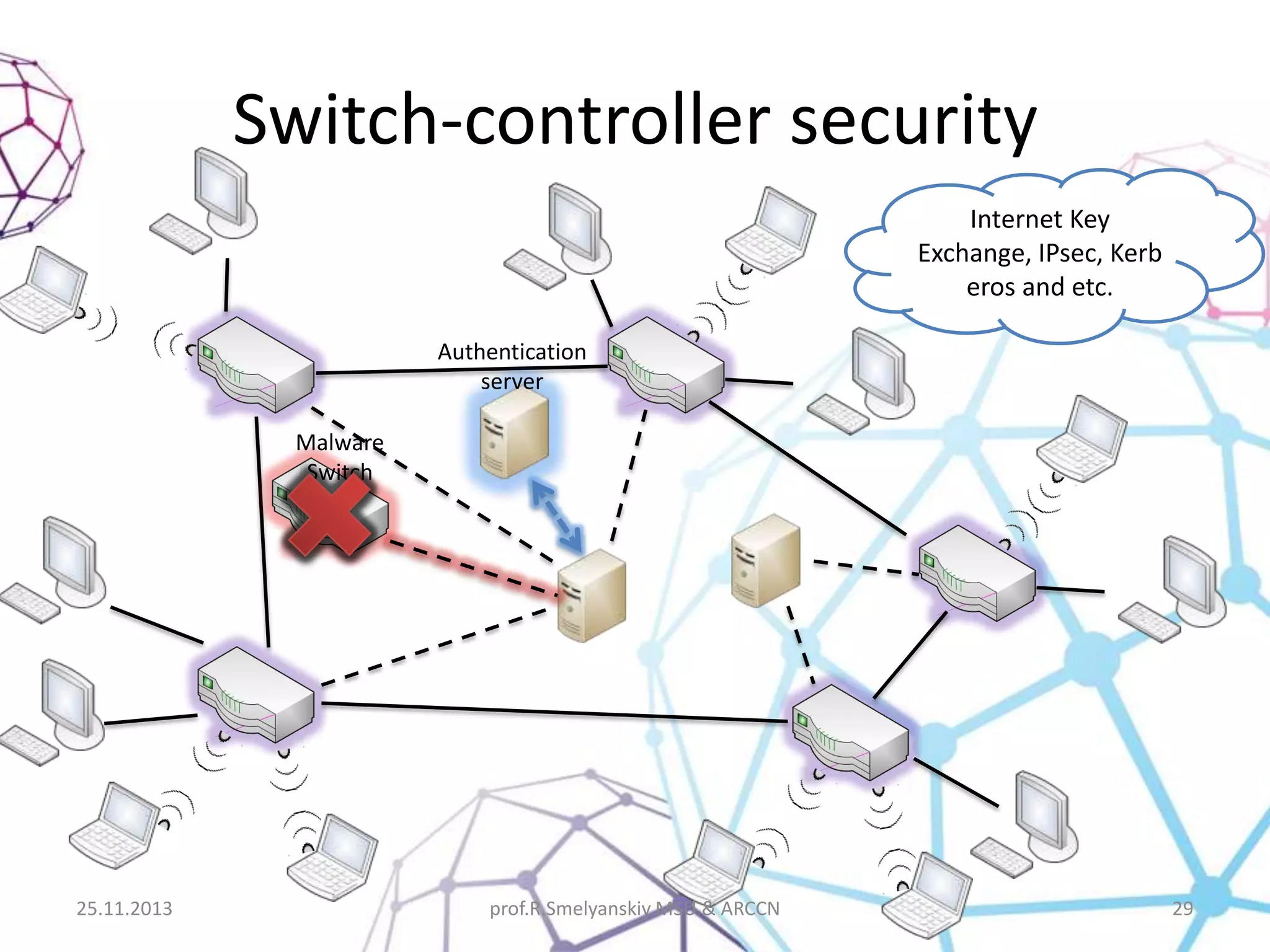
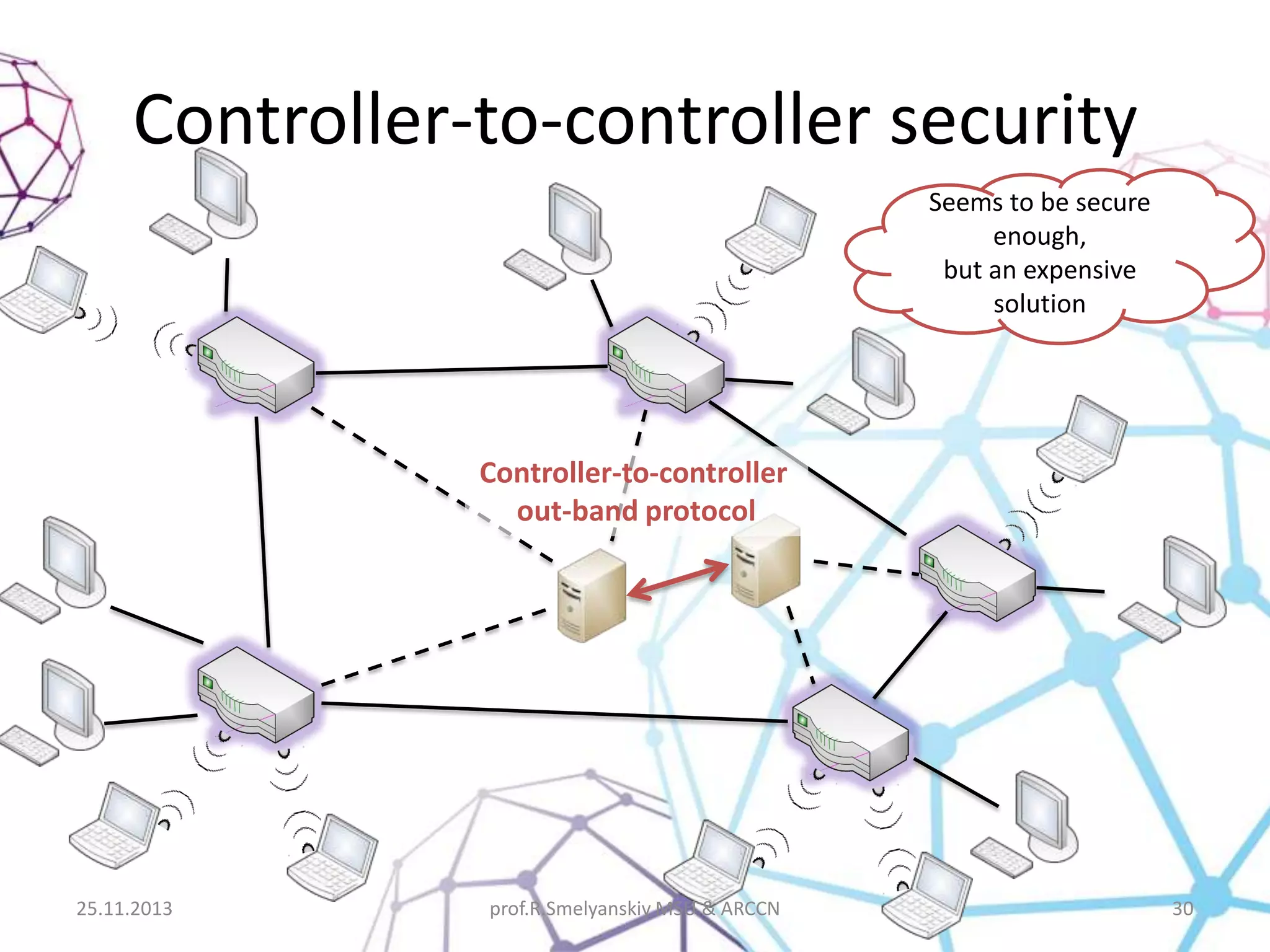
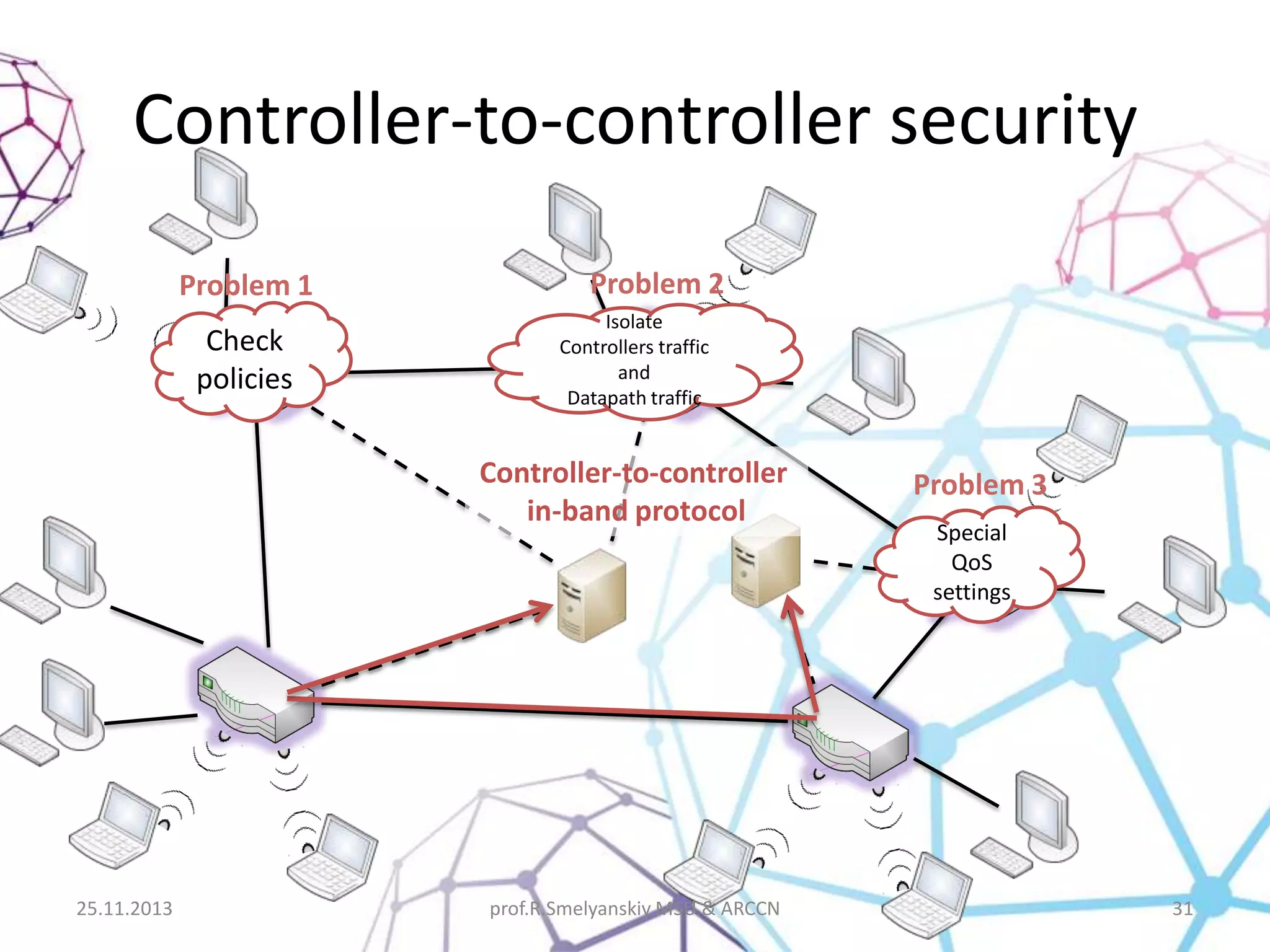
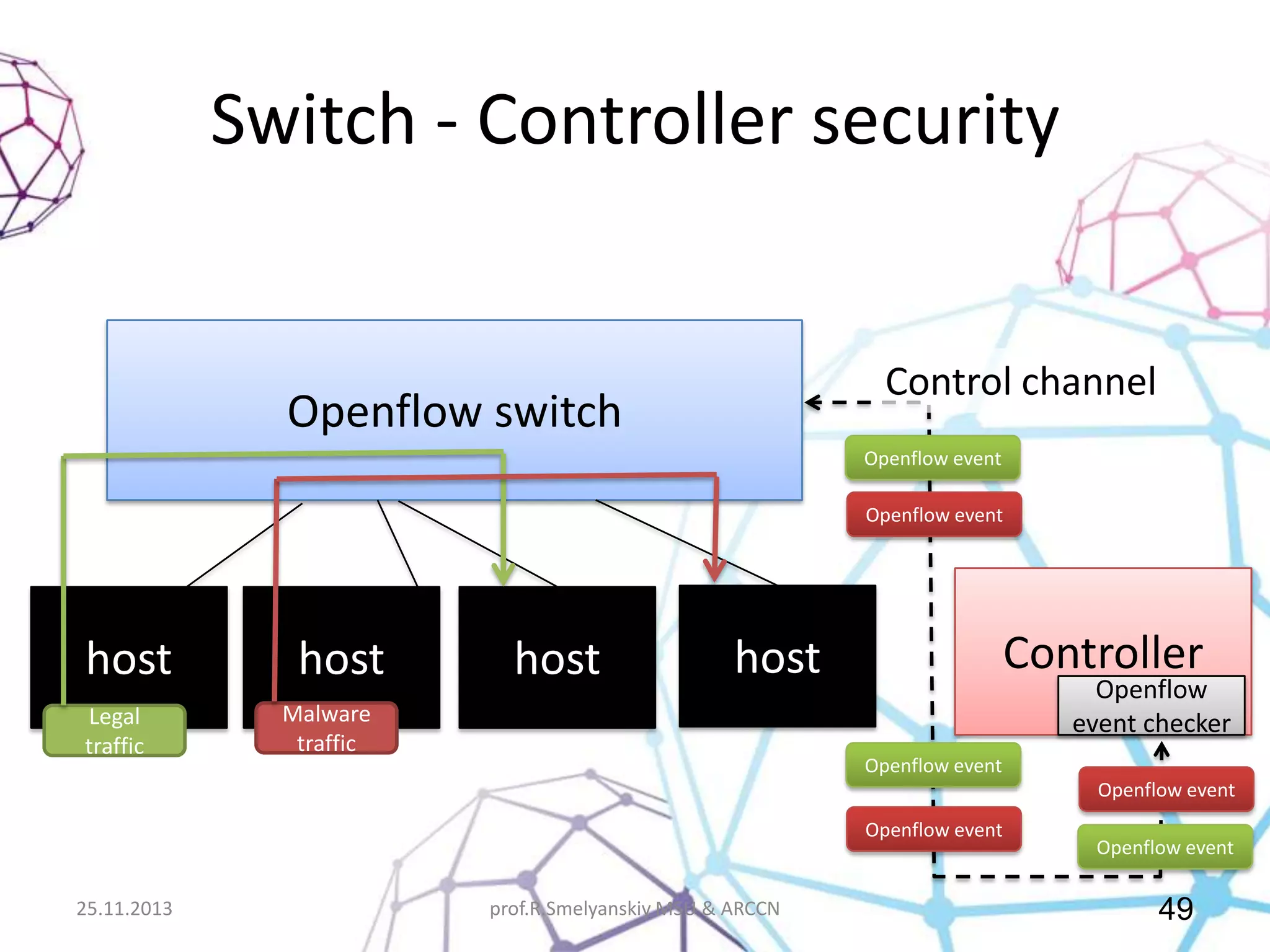
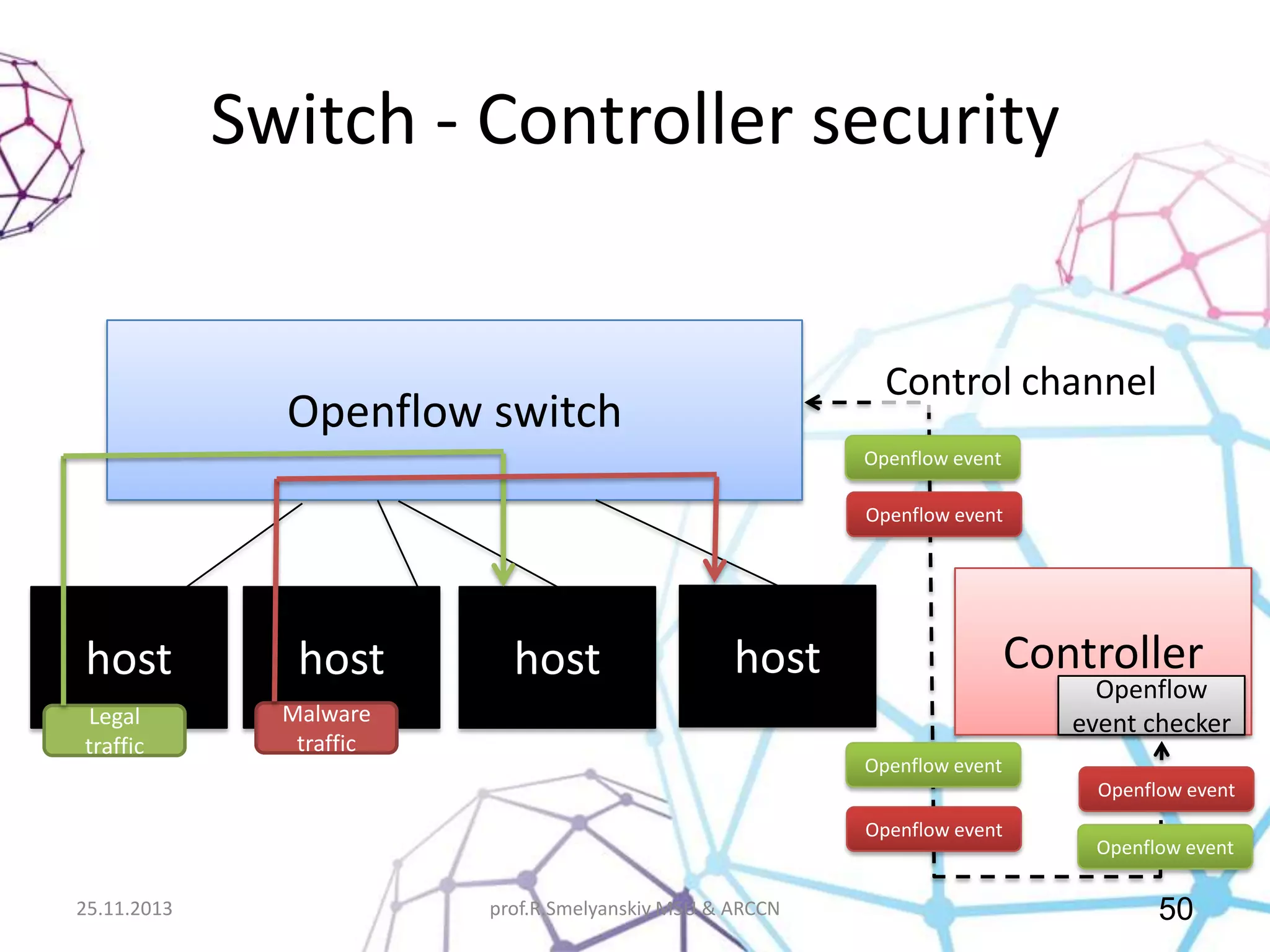
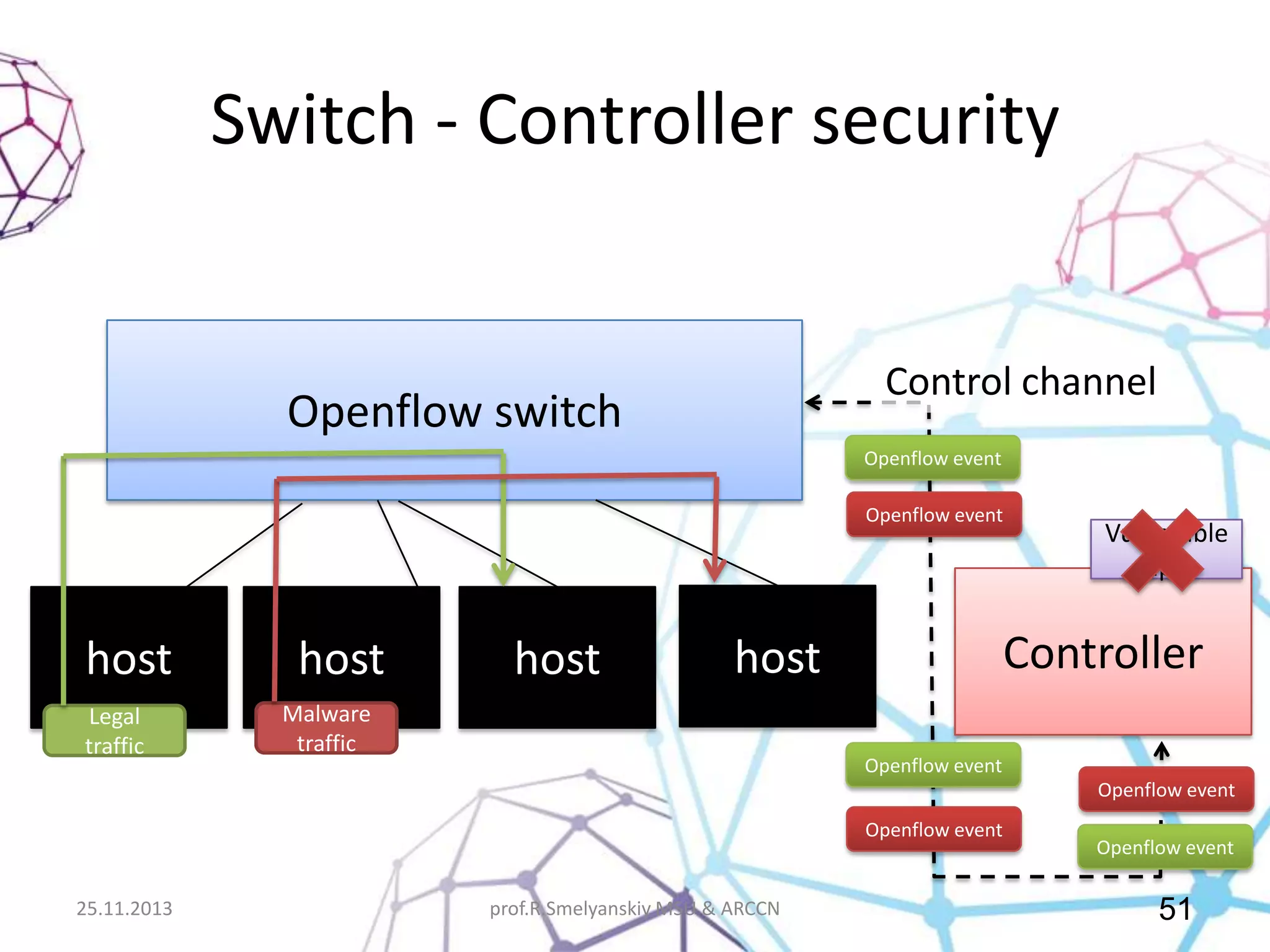
This document discusses Software Defined Networking (SDN) and its implications for network security, emphasizing the need to protect the SDN control environment. It highlights the advantages of SDN, such as programmable configuration and flexible data flow control, while also addressing potential security vulnerabilities that arise from the separation of data and control planes. Various case studies illustrate the application of SDN in real-world scenarios alongside the security challenges faced by traditional architecture networks.