Score Report CCNA
•
2 likes•4,780 views
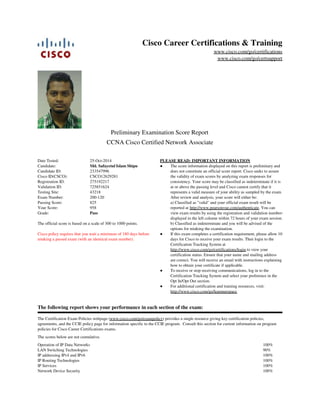
The document reports the results of a certification exam taken by Md. Safayetul Islam Shipu on October 25, 2014 for the CCNA Cisco Certified Network Associate certification. It provides the preliminary scores on each section of the exam, the overall score of 825, and the passing score of 200. It notes that the official exam results will be available on the Pearson VUE website within 72 hours and that Cisco will review scores classified as indeterminate before providing official certification status within 10 days.
Report
Share
Report
Share
Download to read offline
Recommended
Learn intrusion detection: Using Zeek and Elastic for incident response

Intrusion detection is a foundational skill for many cybersecurity careers. Learn how intrusion detection works in action in this live webcast. Then take these free intrusion detection system (IDS) tools and start building your skills.
Join Infosec Skills author Mark Viglione on March 8 at 11 a.m. CST to learn all about:
What is intrusion detection?
How intrusion detection fits into different career paths
Live demo of Zeek for log analysis
Live demo of Elastic SIEM for incident response
Plus your live intrusion detection and career questions
Cybersecurity Interview Questions and Answers | CyberSecurity Interview Tips ...

** CyberSecurity Certification Training: https://www.edureka.co/cybersecurity-certification-training **
This Edureka tutorial on "Cybersecurity Interview Questions and Answers" consists of 50 questions from multiple cybersecurity domains which will help you in preparation of your interviews.
Ch07 Access Control Fundamentals

Security+ Guide to Network Security Fundamentals, 3rd Edition, by Mark Ciampa
Knowledge and skills required for Network Administrators and Information Technology professionals to be aware of security vulnerabilities, to implement security measures, to analyze an existing network environment in consideration of known security threats or risks, to defend against attacks or viruses, and to ensure data privacy and integrity. Terminology and procedures for implementation and configuration of security, including access control, authorization, encryption, packet filters, firewalls, and Virtual Private Networks (VPNs).
CNIT 120: Network Security
http://samsclass.info/120/120_S09.shtml#lecture
Policy: http://samsclass.info/policy_use.htm
Many thanks to Sam Bowne for allowing to publish these presentations.
Cybersecurity Basics - Aravindr.com

The Presentation is about the Basic Introduction to Cybersecurity that talks about introduction and what is security means. Also the presentation talks about CIA Triad i.e confidentiality, integrity and availability
Recommended
Learn intrusion detection: Using Zeek and Elastic for incident response

Intrusion detection is a foundational skill for many cybersecurity careers. Learn how intrusion detection works in action in this live webcast. Then take these free intrusion detection system (IDS) tools and start building your skills.
Join Infosec Skills author Mark Viglione on March 8 at 11 a.m. CST to learn all about:
What is intrusion detection?
How intrusion detection fits into different career paths
Live demo of Zeek for log analysis
Live demo of Elastic SIEM for incident response
Plus your live intrusion detection and career questions
Cybersecurity Interview Questions and Answers | CyberSecurity Interview Tips ...

** CyberSecurity Certification Training: https://www.edureka.co/cybersecurity-certification-training **
This Edureka tutorial on "Cybersecurity Interview Questions and Answers" consists of 50 questions from multiple cybersecurity domains which will help you in preparation of your interviews.
Ch07 Access Control Fundamentals

Security+ Guide to Network Security Fundamentals, 3rd Edition, by Mark Ciampa
Knowledge and skills required for Network Administrators and Information Technology professionals to be aware of security vulnerabilities, to implement security measures, to analyze an existing network environment in consideration of known security threats or risks, to defend against attacks or viruses, and to ensure data privacy and integrity. Terminology and procedures for implementation and configuration of security, including access control, authorization, encryption, packet filters, firewalls, and Virtual Private Networks (VPNs).
CNIT 120: Network Security
http://samsclass.info/120/120_S09.shtml#lecture
Policy: http://samsclass.info/policy_use.htm
Many thanks to Sam Bowne for allowing to publish these presentations.
Cybersecurity Basics - Aravindr.com

The Presentation is about the Basic Introduction to Cybersecurity that talks about introduction and what is security means. Also the presentation talks about CIA Triad i.e confidentiality, integrity and availability
Open Source Security Testing Methodology Manual - OSSTMM by Falgun Rathod

The OSSTMM is about operational security. It is about knowing and measuring how well security works. This methodology will tell you if what you have does what you want it to do and not just what you were told it does.
Pasta Threat Modeling

PASTA allows organizations to understand an attacker’s perspective on applications and infrastructure, thus developing threat management processes and policies. Let’s learn more about PASTA threat modeling in this slideshare. To know more about threat modeling, click here: https://www.eccouncil.org/threat-modeling/
Access Control: Principles and Practice

Slides prepared based on the paper Access Control: Principles and Practice by Ravi S. Sandhu and Pierangela Samarati, IEEE Communications Magazine, 1994
SOC presentation- Building a Security Operations Center

Presentation I used to give on the topic of using a SIM/SIEM to unify the information stream flowing into the SOC. This piece of collateral was used to help close the largest SIEM deal (Product and services) that my employer achieved with this product line.
Critical Capabilities for MDR Services - What to Know Before You Buy

24/7 coverage and skills shortages for post breach detection and response are driving the need for Managed Detection and Response (MDR) Services. Analysts are predicting 15X growth for MDR services over the next few years as security leaders shift their focus from prevention to detection knowing attacks are evading existing defenses, often without malware by using macros and scripts.
Managed services often use MDR marketing messages and this sometimes results in their security monitoring services not meeting expectations. Buyers must learn what to look for in an MDR solution to avoid falling into this trap.
Cyber Security Career Advice

This the first edition of the Trainers Underground will cover topics of career advice, cyber security certifications, and other topics like marketing yourself. Using LinkedIn and cyber security certifications.
Guide to MFA

Multi-factor authentication (or MFA) Learn all you need to know about what multi-factor authentication is, and why you need MFA to protect customer data.
https://bit.ly/3jowx1a
CyberOps Associate Modul 23 Endpoint Vulnerability Assessment

CyberOps Associate Modul 23 Endpoint Vulnerability Assessment
Penetration Testing Report

A penetration testing report submitted during internship at ICT Academy, IIT Kanpur. This report contains a basic flow how to perform penetration testing, from reconnaissance to finding vulnerability. This should be helpful for security researchers who are looking to write a penetration testing for their project.
Threat hunting foundations: People, process and technology.pptx

Ever wonder what threat hunting is all about? Join Infosec Principal Security Researcher Keatron Evans as he breaks down the basics of what it’s like to have a career hunting down potential cyber threats.
Join us on for an inside look at a day in the life of a threat hunter, including:
Why threat hunters are more critical today than ever before
Knowledge and skills needed to drive threat hunting success
Live demos of essential threat hunting skills and tools used to detect and mitigate adversarial behavior
One lucky attendee will win a free year of Infosec Skills. Complete the form to save your seat!
P.S. Want to go even deeper into threat hunting? Don’t miss our advanced threat hunting session on June 28, Join the hunt: Threat hunting for proactive cyber defense.
How to Prepare for the CISSP Exam

How to prepare for the CISSP Exam. A presentation created by the (ISC)2 Hellenic Chapter to assist and instruct those in Greece interested in pursuing the CISSP Certification.
The (ISC)2 Hellenic Chapter Team
Aujas incident management webinar deck 08162016

In this presentation we will look at the cause and effect of the problem, analyze preparedness and learn how you can better prepare, detect, respond and recover from cyber-attacks.
Domain 6 - Security Assessment and Testing

Design and validate assessment and test strategies, Conduct security control testing, Collect security process data (e.g., management and operational controls),
CyberSecurity Certifications | CyberSecurity Career | CyberSecurity Certifica...

** CyberSecurity Certification Training: https://www.edureka.co/cybersecurity-certification-training **
This Edureka tutorial on "Cybersecurity Certifications" talks about some of the major cybersecurity certifications required to get into the security industry. If you're interested in a developing an exciting career in cybersecurity, check out 2018's top ten cybersecurity certifications.
More Related Content
What's hot
Open Source Security Testing Methodology Manual - OSSTMM by Falgun Rathod

The OSSTMM is about operational security. It is about knowing and measuring how well security works. This methodology will tell you if what you have does what you want it to do and not just what you were told it does.
Pasta Threat Modeling

PASTA allows organizations to understand an attacker’s perspective on applications and infrastructure, thus developing threat management processes and policies. Let’s learn more about PASTA threat modeling in this slideshare. To know more about threat modeling, click here: https://www.eccouncil.org/threat-modeling/
Access Control: Principles and Practice

Slides prepared based on the paper Access Control: Principles and Practice by Ravi S. Sandhu and Pierangela Samarati, IEEE Communications Magazine, 1994
SOC presentation- Building a Security Operations Center

Presentation I used to give on the topic of using a SIM/SIEM to unify the information stream flowing into the SOC. This piece of collateral was used to help close the largest SIEM deal (Product and services) that my employer achieved with this product line.
Critical Capabilities for MDR Services - What to Know Before You Buy

24/7 coverage and skills shortages for post breach detection and response are driving the need for Managed Detection and Response (MDR) Services. Analysts are predicting 15X growth for MDR services over the next few years as security leaders shift their focus from prevention to detection knowing attacks are evading existing defenses, often without malware by using macros and scripts.
Managed services often use MDR marketing messages and this sometimes results in their security monitoring services not meeting expectations. Buyers must learn what to look for in an MDR solution to avoid falling into this trap.
Cyber Security Career Advice

This the first edition of the Trainers Underground will cover topics of career advice, cyber security certifications, and other topics like marketing yourself. Using LinkedIn and cyber security certifications.
Guide to MFA

Multi-factor authentication (or MFA) Learn all you need to know about what multi-factor authentication is, and why you need MFA to protect customer data.
https://bit.ly/3jowx1a
CyberOps Associate Modul 23 Endpoint Vulnerability Assessment

CyberOps Associate Modul 23 Endpoint Vulnerability Assessment
Penetration Testing Report

A penetration testing report submitted during internship at ICT Academy, IIT Kanpur. This report contains a basic flow how to perform penetration testing, from reconnaissance to finding vulnerability. This should be helpful for security researchers who are looking to write a penetration testing for their project.
Threat hunting foundations: People, process and technology.pptx

Ever wonder what threat hunting is all about? Join Infosec Principal Security Researcher Keatron Evans as he breaks down the basics of what it’s like to have a career hunting down potential cyber threats.
Join us on for an inside look at a day in the life of a threat hunter, including:
Why threat hunters are more critical today than ever before
Knowledge and skills needed to drive threat hunting success
Live demos of essential threat hunting skills and tools used to detect and mitigate adversarial behavior
One lucky attendee will win a free year of Infosec Skills. Complete the form to save your seat!
P.S. Want to go even deeper into threat hunting? Don’t miss our advanced threat hunting session on June 28, Join the hunt: Threat hunting for proactive cyber defense.
How to Prepare for the CISSP Exam

How to prepare for the CISSP Exam. A presentation created by the (ISC)2 Hellenic Chapter to assist and instruct those in Greece interested in pursuing the CISSP Certification.
The (ISC)2 Hellenic Chapter Team
Aujas incident management webinar deck 08162016

In this presentation we will look at the cause and effect of the problem, analyze preparedness and learn how you can better prepare, detect, respond and recover from cyber-attacks.
Domain 6 - Security Assessment and Testing

Design and validate assessment and test strategies, Conduct security control testing, Collect security process data (e.g., management and operational controls),
CyberSecurity Certifications | CyberSecurity Career | CyberSecurity Certifica...

** CyberSecurity Certification Training: https://www.edureka.co/cybersecurity-certification-training **
This Edureka tutorial on "Cybersecurity Certifications" talks about some of the major cybersecurity certifications required to get into the security industry. If you're interested in a developing an exciting career in cybersecurity, check out 2018's top ten cybersecurity certifications.
What's hot (20)
Open Source Security Testing Methodology Manual - OSSTMM by Falgun Rathod

Open Source Security Testing Methodology Manual - OSSTMM by Falgun Rathod
SOC presentation- Building a Security Operations Center

SOC presentation- Building a Security Operations Center
Critical Capabilities for MDR Services - What to Know Before You Buy

Critical Capabilities for MDR Services - What to Know Before You Buy
CyberOps Associate Modul 23 Endpoint Vulnerability Assessment

CyberOps Associate Modul 23 Endpoint Vulnerability Assessment
Threat hunting foundations: People, process and technology.pptx

Threat hunting foundations: People, process and technology.pptx
CyberSecurity Certifications | CyberSecurity Career | CyberSecurity Certifica...

CyberSecurity Certifications | CyberSecurity Career | CyberSecurity Certifica...
Viewers also liked
Cisco CCENT Cram Notes

Provides last minute review of important topics on Cisco CCENT. Usefull for candidates preparing to take CCENT/CCNA certification exam.
Viewers also liked (6)
Similar to Score Report CCNA
Top Cybersecurity Certs

This blog explains the list of the top cybersecurity certifications which is must for any enthusiasts, students or professional who is in the field of cybersecurity.
Certified Information System Auditor- CISA

Certifi ed Information Systems Auditor (CISA®) is a globally recognised professional
certi cation for Information Technology Audit professionals, and serves to validate
their competence in the fields of audit, control and security of information systems.
The certi ficate is awarded by the Information Systems Audit and Control Association
(ISACA).
The CISA® certi fication is considered the globally accepted standard of profi ciency
in IS audit. CISA®-certi ed individuals have demonstrated their capabilities in managing
vulnerabilities and instituting controls within the enterprise, and undertake to
comply with the rigorous auditing standards set by ISACA. They are highly sought
after in hiring circles - having this achievement under your belt would lead to more
extensive employment opportunities with higher pay grades.
How to prepare for CCIE Routing and Switching Certification 

What you can expect from this Slide:-
Details about CCIE R&S Certification
Importance and Scope of CCIE Certification
Popular CCIE Job profiles in Industry
CCIE Examination format
Prerequisite for CCIE R&S Certification
Study Plan for CCIE R&S Certification
Tips to prepare for CCIE R&S Lab Examination
Amazing offer on our upcoming boot camp
CCIE R&S related FAQs
Q&A Session
Fit4 Business

FIT$BUSINESS: Cisco Channel Partners helpen een Cisco partner te worden, te blijven of zelfs te helpen een hogere status te bemachtigen – van Select tot Gold Partner Status
Understanding the Risk Management Framework & (ISC)2 CAP Module 1: Exam 

Part 1 of 15 covering NIST Risk Management Framework (RMF) and (ISC)2 Certified Authorization Professional (CAP).
CompTIA 220-802 Dumps

Prepare your CompTIA certification exams with real CompTIA Questions & Answers verified by experienced CompTIA professionals!https://www.pass4sureexam.com/220-802.html
Similar to Score Report CCNA (20)
Netacad certification exam_discount_-_step_by_step_guide

Netacad certification exam_discount_-_step_by_step_guide
How to prepare for CCIE Routing and Switching Certification 

How to prepare for CCIE Routing and Switching Certification
Understanding the Risk Management Framework & (ISC)2 CAP Module 1: Exam 

Understanding the Risk Management Framework & (ISC)2 CAP Module 1: Exam
538522937-Cisa-easdasdsadsadasdBook-New-1-188.pptx

538522937-Cisa-easdasdsadsadasdBook-New-1-188.pptx
Score Report CCNA
- 1. 100% 90% 100% 100% 100% 100% Operation of IP Data Networks LAN Switching Technologies IP addressing IPv4 and IPv6 IP Routing Technologies IP Services Network Device Security The scores below are not cumulative. The Certification Exam Policies webpage (www.cisco.com/go/exampolicy) provides a single resource giving key certification policies, agreements, and the CCIE policy page for information specific to the CCIE program. Consult this section for current information on program policies for Cisco Career Certifications exams. The following report shows your performance in each section of the exam: For additional certification and training resources, visit: http://www.cisco.com/go/learnnetspace ● To receive or stop receiving communications, log in to the Certification Tracking System and select your preference in the Opt In/Opt Out section. ● If this exam completes a certification requirement, please allow 10 days for Cisco to receive your exam results. Then login to the Certification Tracking System at http://www.cisco.com/go/certifications/login to view your certification status. Ensure that your name and mailing address are correct. You will receive an email with instructions explaining how to obtain your certificate if applicable. ● b) Classified as indeterminate and you will be advised of the options for retaking the examination. a) Classified as "valid" and your official exam result will be reported at http://www.pearsonvue.com/authenticate. You can view exam results by using the registration and validation numbers displayed in the left column within 72 hours of your exam session. The score information displayed on this report is preliminary and does not constitute an official score report. Cisco seeks to assure the validity of exam scores by analyzing exam responses for consistency. Your score may be classified as indeterminate if it is at or above the passing level and Cisco cannot certify that it represents a valid measure of your ability as sampled by the exam. After review and analysis, your score will either be: ● PLEASE READ: IMPORTANT INFORMATION Cisco policy requires that you wait a minimum of 180 days before retaking a passed exam (with an identical exam number). The official score is based on a scale of 300 to 1000 points. PassGrade: 958Your Score: 825Passing Score: 200-120Exam Number: 43218Testing Site: 725851624Validation ID: 275192217Registration ID: CSCO12629281Cisco ID(CSCO): 233547996Candidate ID: Md. Safayetul Islam ShipuCandidate: 25-Oct-2014Date Tested: CCNA Cisco Certified Network Associate Preliminary Examination Score Report www.cisco.com/go/certsupport www.cisco.com/go/certifications Cisco Career Certifications & Training
- 2. As a Cisco certification candidate, you deserve a fair and secure testing experience. Please report any suspicious behavior you observe to security-tipline@external.cisco.com. Examples of such behavior include receiving help or copying from another test taker, taking a test for someone else, accessing stolen test questions, or using notes or unauthorized aids. Thank you for your assistance in helping to detect and prevent these unfair testing practices. This examination was delivered at a Pearson VUE Authorized Testing Center. To register for another Cisco exam in the United States call 1-877-404-EXAM. Elsewhere, contact your local Pearson VUE Authorized Center or go to: www.pearsonvue.com/cisco. Join the Cisco Learning Network (www.ciscolearningnetwork.com) and connect with other Cisco certified community members in many ways such as discussion forums. Browse exclusive items at the Cisco Learning Network store (www.cisco.com/go/learningnetworkstore) designed to inform you of current CCNA topics and help advance you to the next level of your certification goals. 100% 60% Troubleshooting WAN Technologies