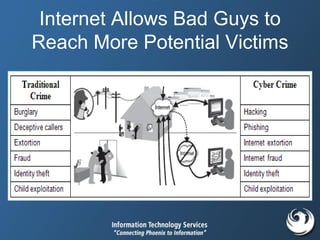
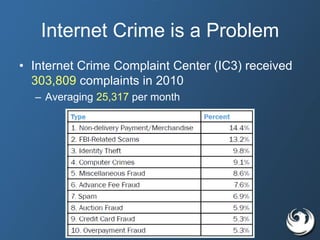
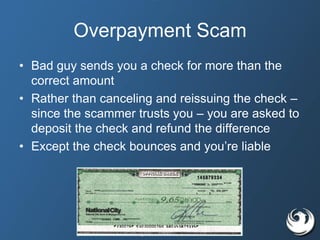
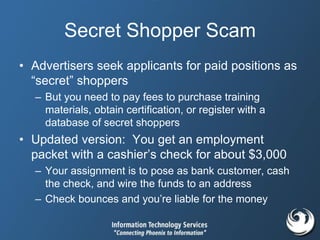
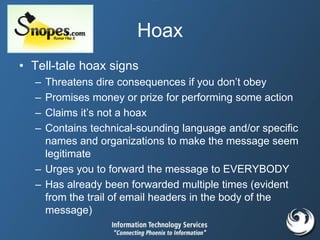
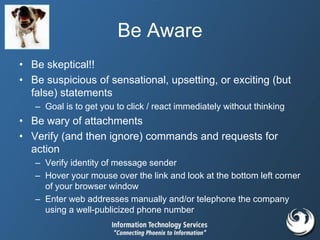
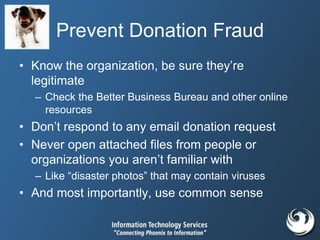
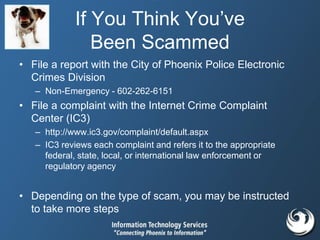
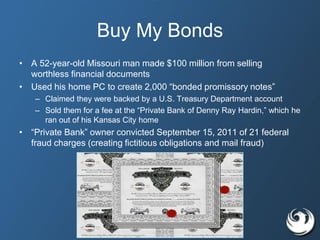
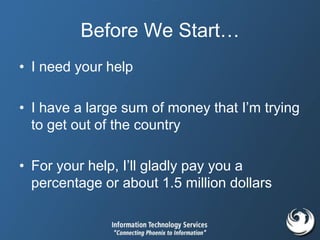
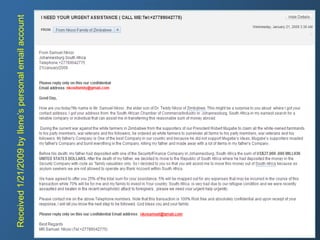
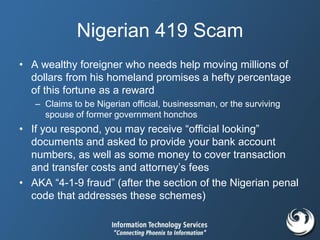
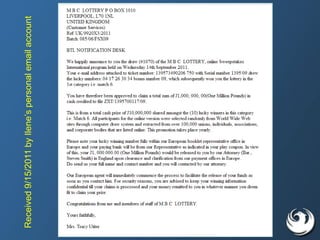
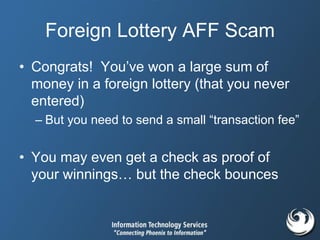
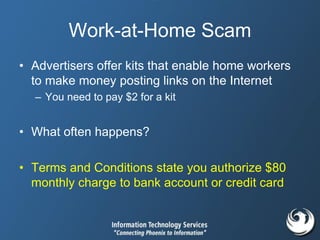
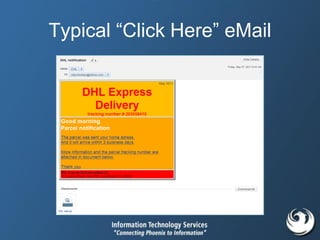
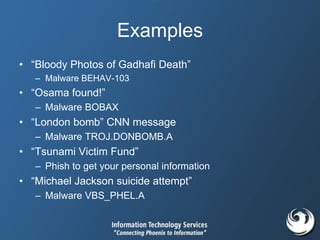
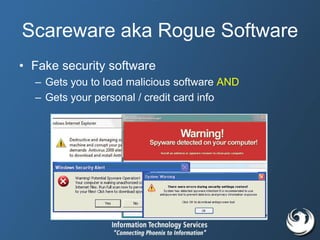
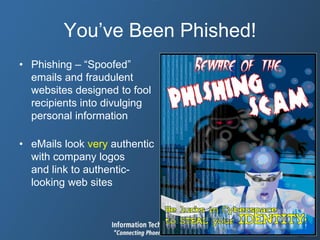
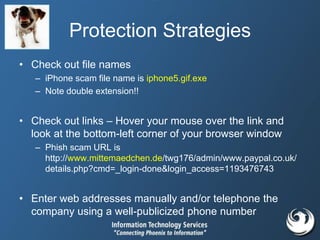
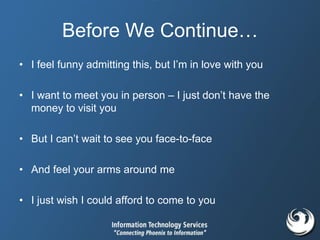
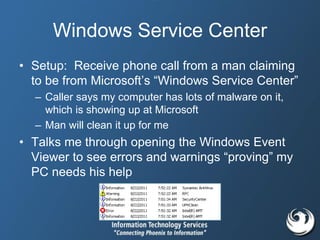
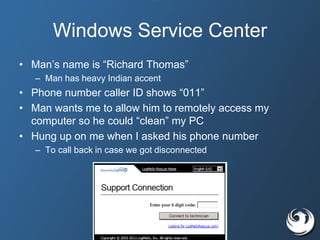
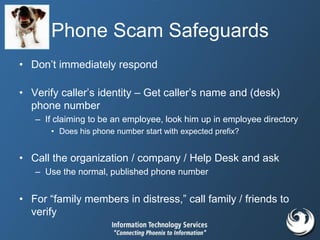
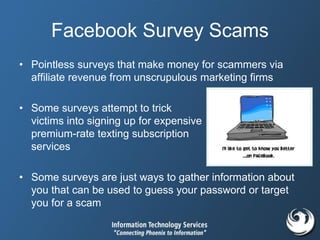
This document discusses various types of internet scams and fraud. It describes common scams like Nigerian 419 scams, work from home scams, romance scams, and malware scams disguised as important notifications. It provides tips on how to recognize these scams and advises readers not to provide personal information or money to potential scammers. The document also discusses psychological tricks scammers use and strategies to protect yourself from various internet and phone-based scams.




![Get More Twitter Followers
• “GET MORE FOLLOWERS MY BEST
FRIENDS? I WILL FOLLOW YOU BACK IF YOU
FOLLOW ME - [LINK]”
– Just enter your Twitter username and password
• You’ve just given control of your account to
someone else
– They may then post spam or malicious updates and
links, send unwanted messages, or violate other
Twitter rules with your account](https://image.slidesharecdn.com/scams-and-fraud-presentation-180809160247/85/Scams-and-fraud-presentation-46-320.jpg)