RFID & ITS APPLICATION
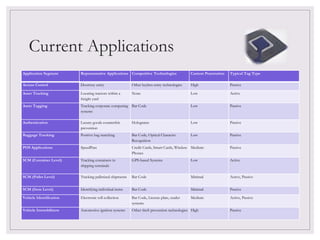
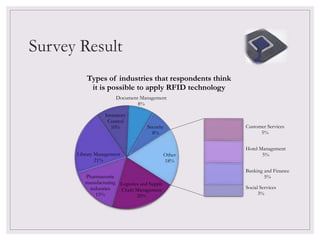
The document discusses Radio Frequency Identification (RFID) including its components, types of tags, applications and a survey on potential industries for RFID application. It covers the basic makeup of an RFID system including tags, readers and antennas. Common applications mentioned are credit cards, transportation tolls and asset tracking. The survey found logistics, libraries and pharmaceuticals as top industries for RFID. Future developments could include more medical and library uses. In conclusion, RFID provides benefits over barcodes but also has higher costs and standardization issues to address.