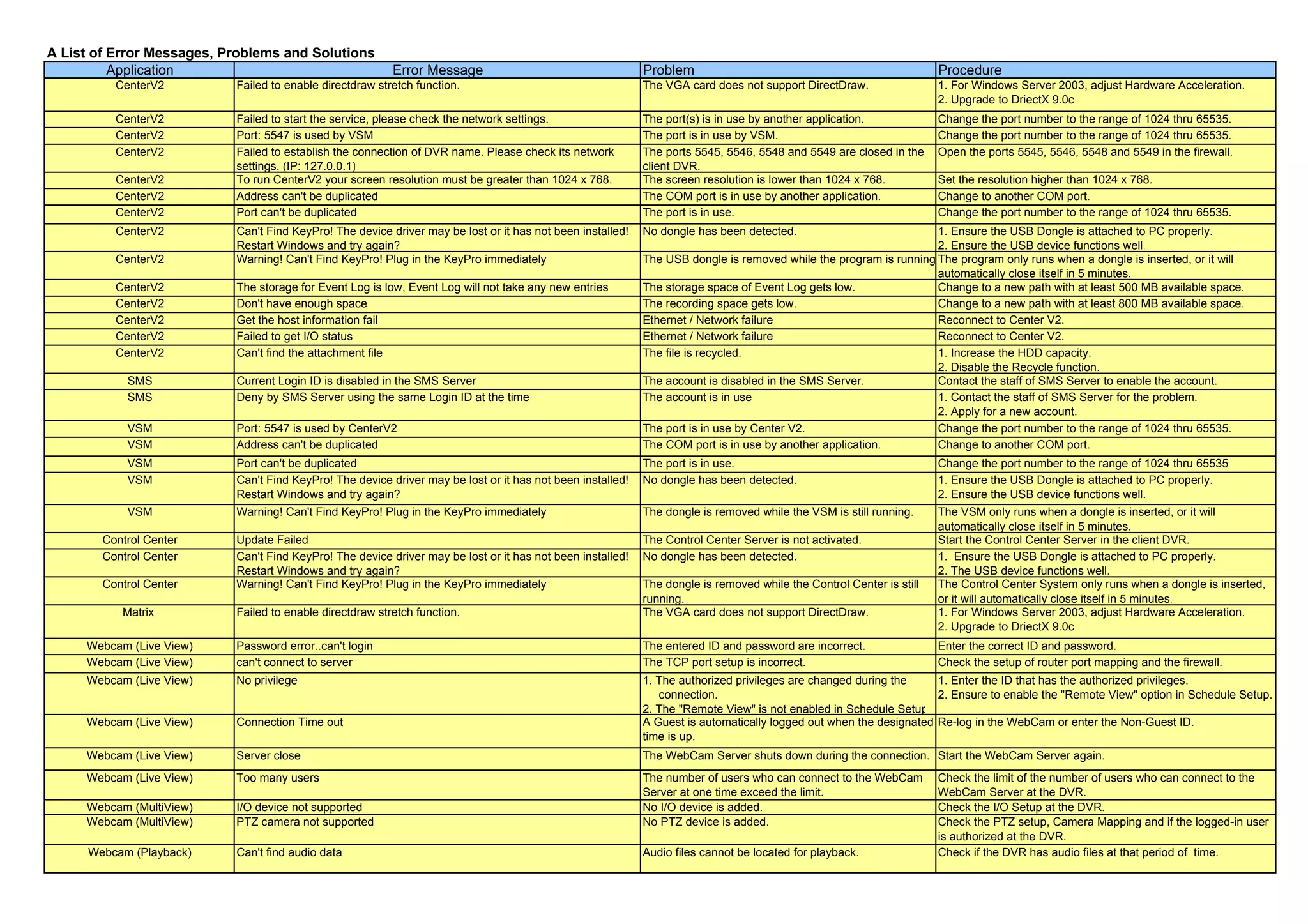
This document contains a list of error messages for various applications along with descriptions of common problems and suggested procedures. It includes error messages for CenterV2, SMS, VSM, Control Center, Matrix, Webcam applications for live viewing, playback, server, and EMap functions. The errors range from issues with graphics cards, network ports being in use, missing or disconnected dongles, incorrect passwords, low storage space, and more. Suggested procedures include changing settings, upgrading software, ensuring proper hardware connections, and contacting server administrators.