Embed presentation
Download as PDF, PPTX
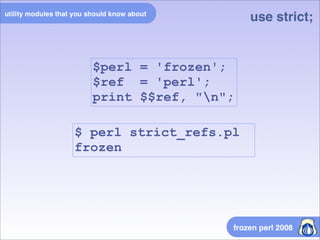
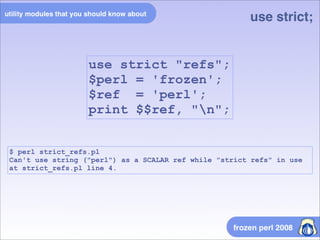
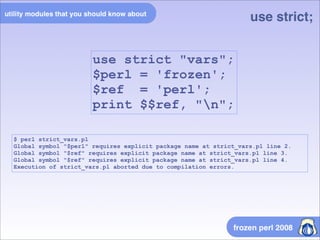
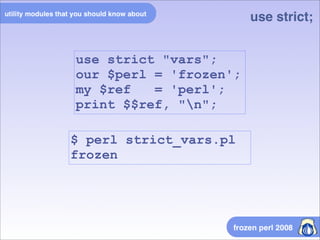
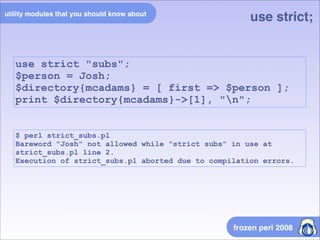
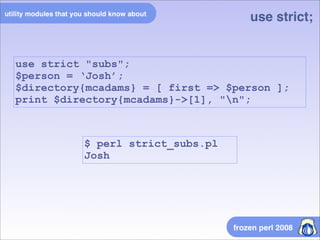
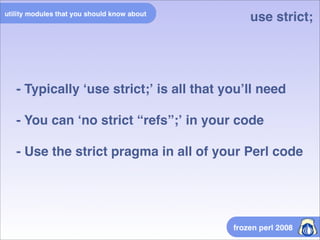



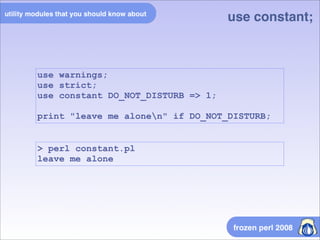


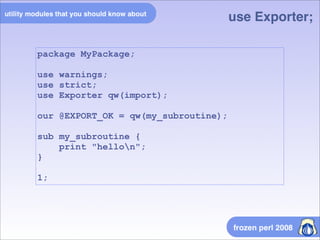
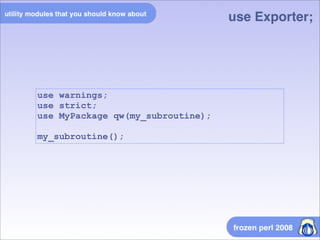
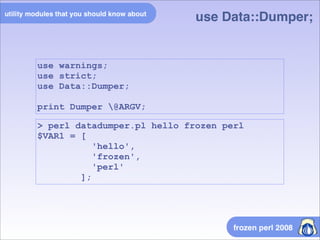
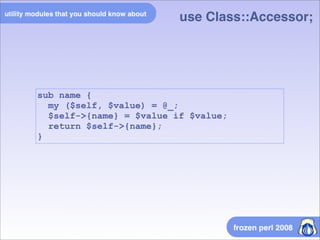
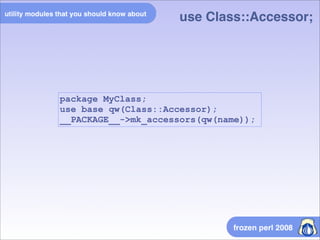
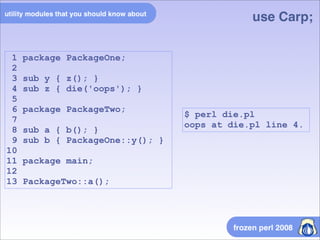
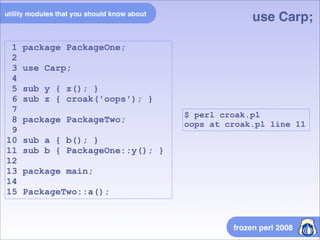
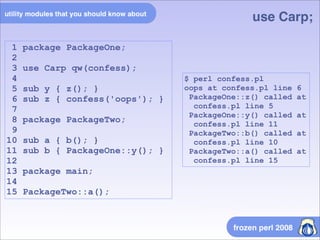
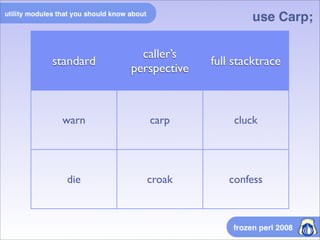
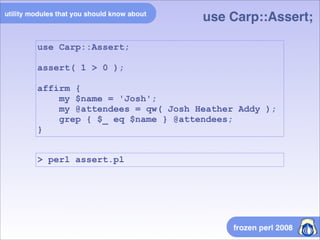
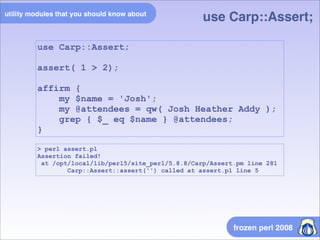
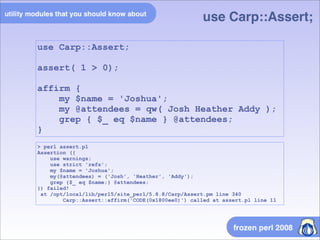
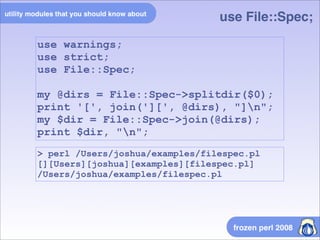
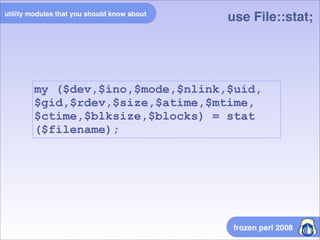
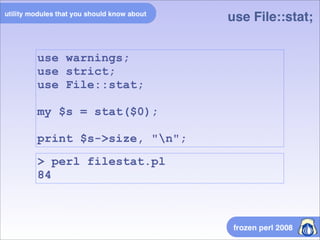
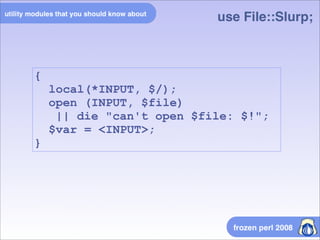
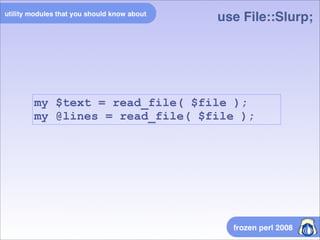
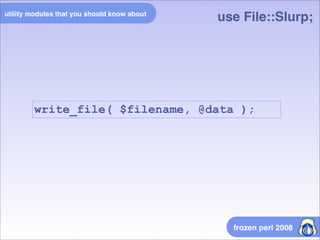
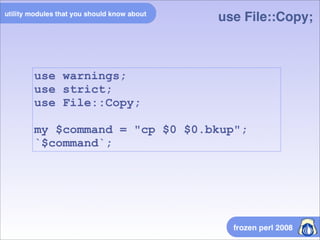
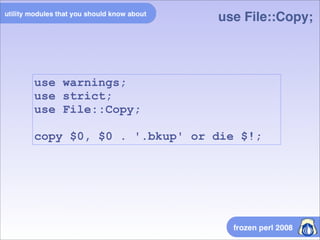
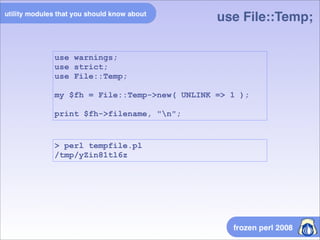
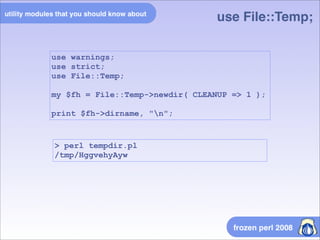
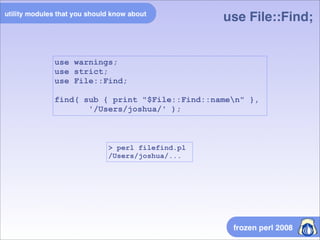
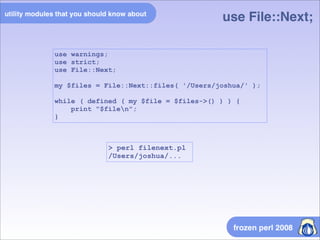

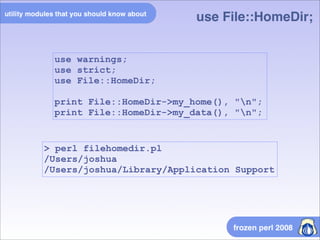
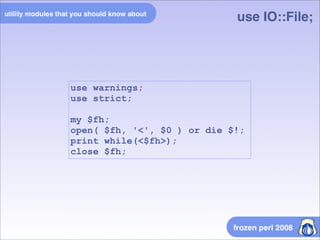
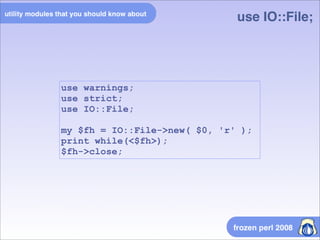
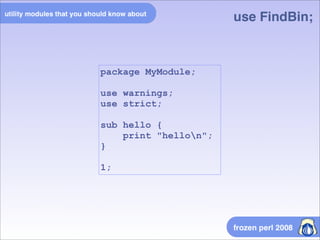
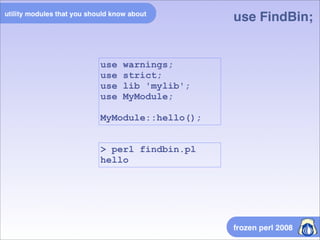

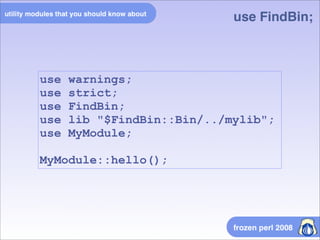
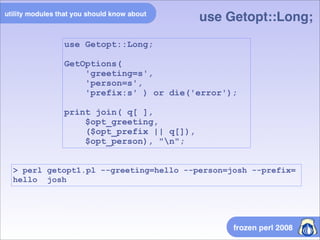
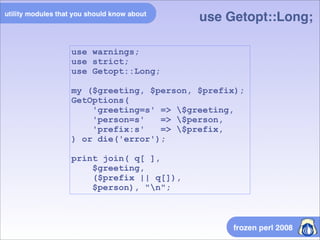
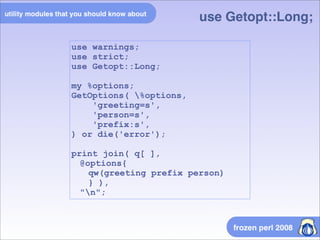
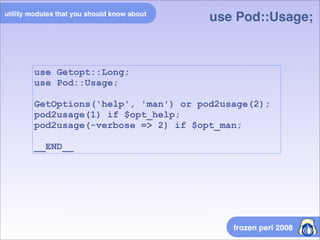


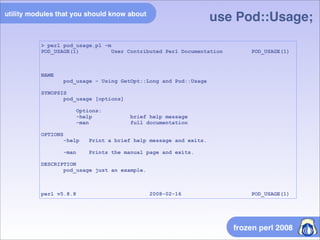
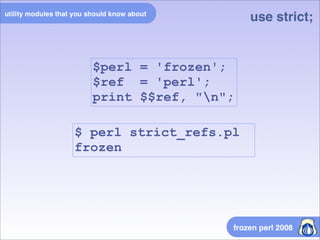
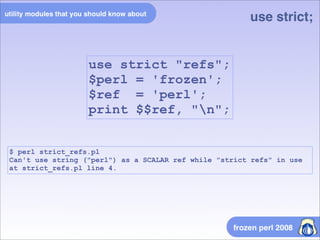
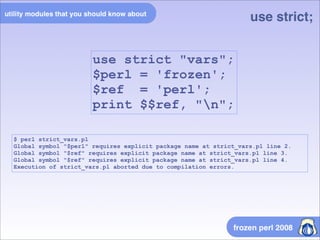
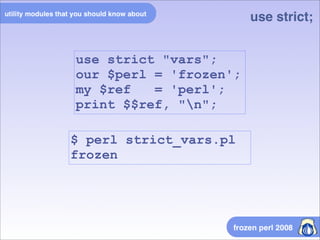
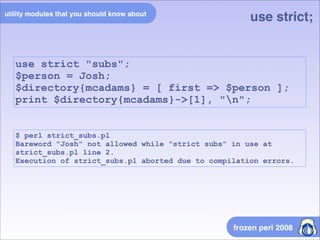
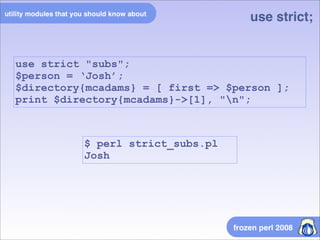
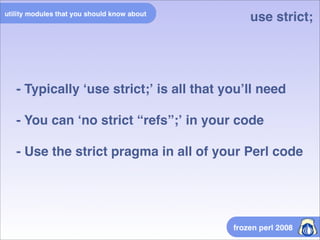
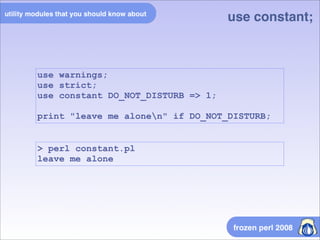
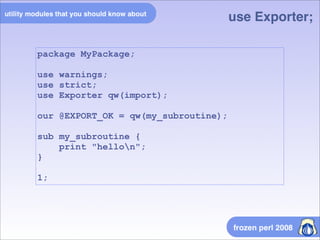
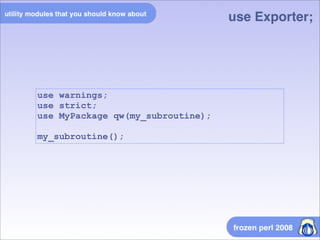
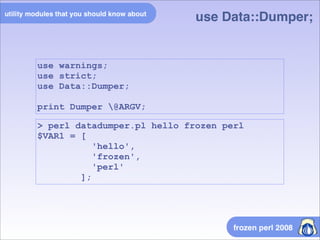
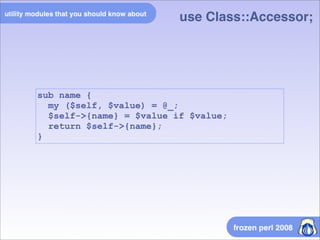
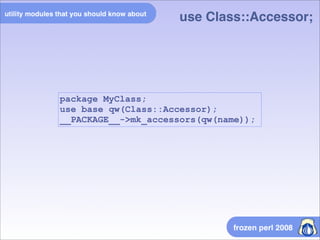
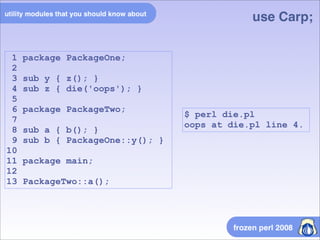
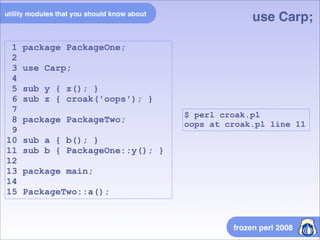
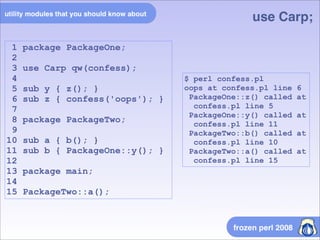
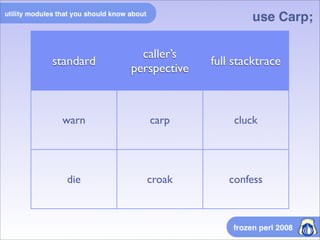
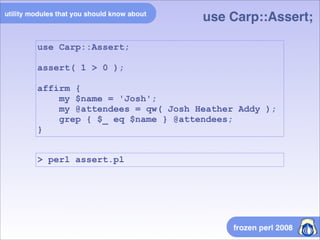
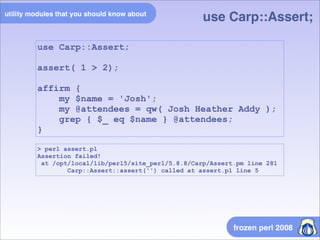
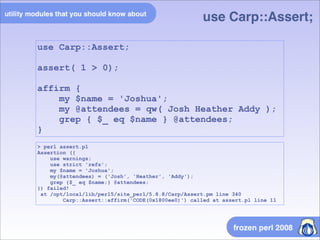
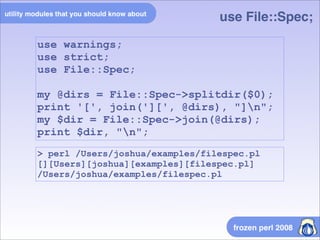
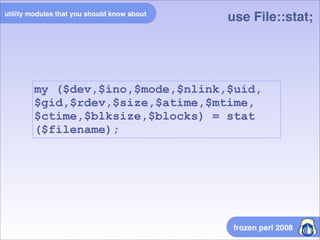
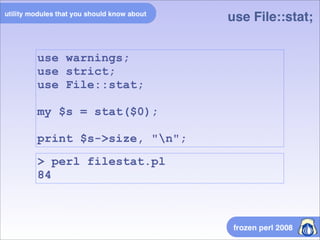
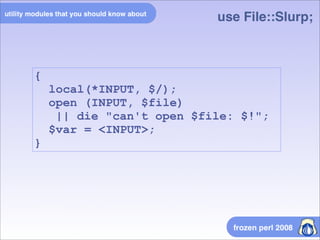
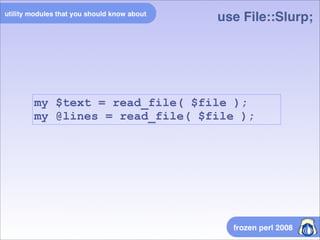
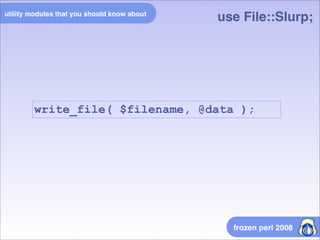
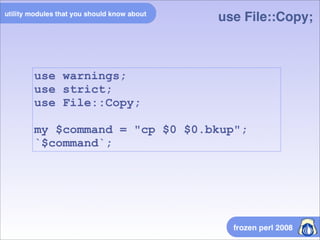
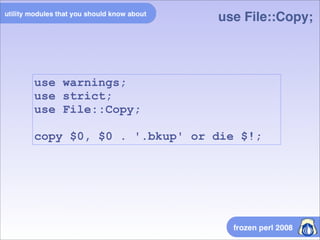
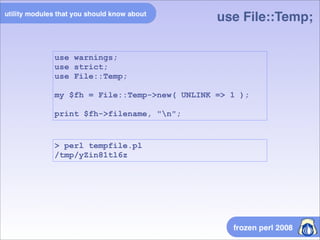
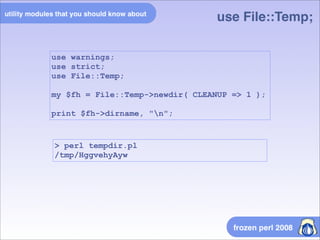
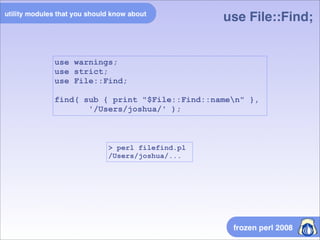
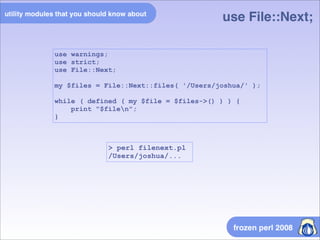
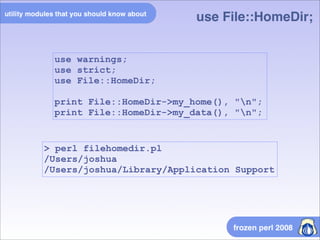
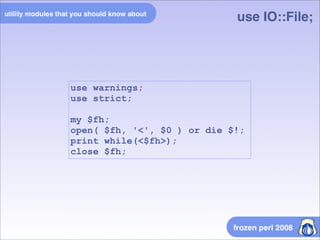
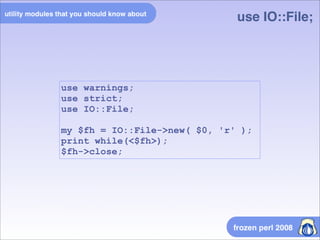
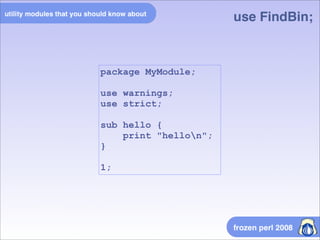
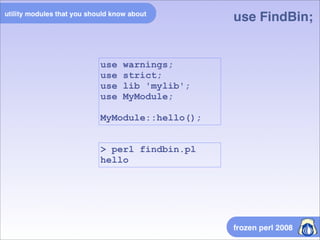
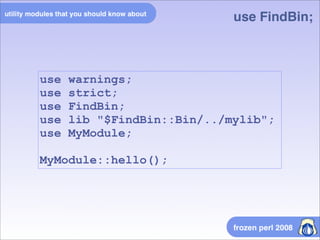
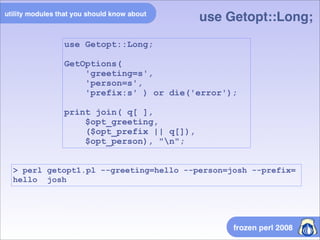
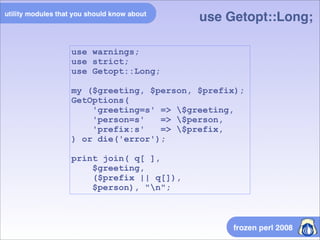
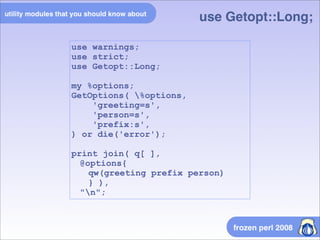
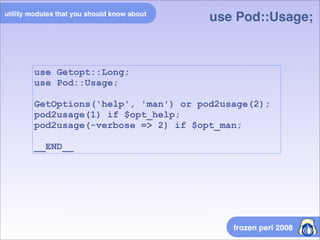
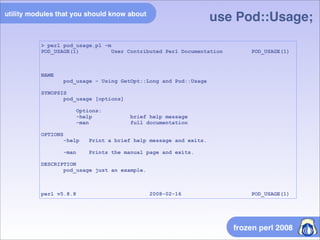
The document is a detailed tutorial on using various features and modules in Perl, including strict pragmas, file handling, error handling, and command-line options. It discusses the importance of using strict programming practices and includes code examples for different modules like Carp, File::Spec, and Getopt::Long. Overall, it serves as a comprehensive reference for Perl programming techniques and best practices.