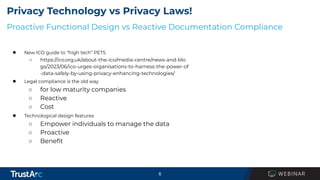
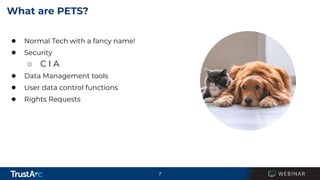
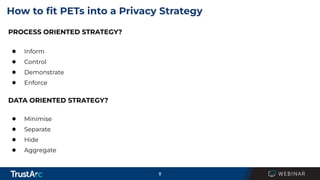
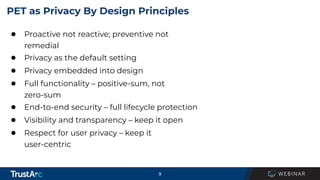
The webinar titled 'Privacy Enhancing Technologies: Exploring the Benefits and Recommendations' aims to provide an overview of privacy enhancing technologies (PETs) and their benefits for privacy protection. Key topics include the distinction between proactive technology design and reactive compliance, as well as how organizations can integrate PETs into their privacy strategies. The session features speakers from TrustArc and will conclude with a Q&A segment.