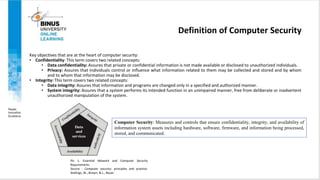
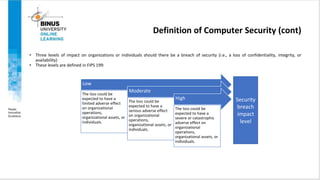
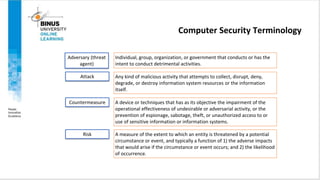
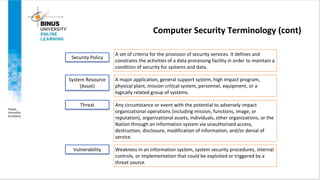
The document summarizes key concepts from the book "Computer Security: Principles and Practice" by Stallings, Brown, and Bauer. It defines computer security as measures that ensure confidentiality, integrity, and availability of information systems. It outlines threats to computer security like unauthorized disclosure, deception, disruption, and usurpation. It also defines security terminology like attacks, vulnerabilities, risks, and countermeasures. The document presents models for understanding computer security and the relationships between threats, vulnerabilities, attacks, and assets.





















![Fundamental Security Design Principles (cont)
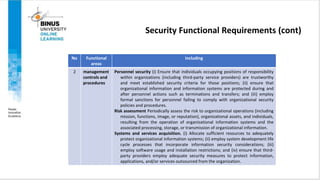
• Separation of privilege, is defined in [SALT75] as a practice in which multiple privilege attributes are required to achieve access to a
restricted resource. A good example of this is multifactor user authentication, which requires the use of multiple techniques, such as
a password and a smart card, to authorize a user.
• Least privilege, means every process and every user of the system should operate using the least set of privileges necessary to
perform the task. A good example of the use of this principle is role-based access control.
• Least common mechanism, means the design should minimize the functions shared by different users, providing mutual security.
• Psychological acceptability, implies the security mechanisms should not interfere unduly with the work of users, and at the same
time meet the needs of those who authorize access. If security mechanisms hinder the usability or accessibility of resources, users
may opt to turn off those mechanisms.
• Isolation, is a principle that applies in three contexts.
• Public access systems should be isolated from critical resources (data, processes, etc.) to prevent disclosure or tampering.
• The processes and files of individual users should be isolated from one another except where it is explicitly desired.
• Security mechanisms should be isolated in the sense of preventing access to those mechanisms.](https://image.slidesharecdn.com/ppt0-computersecurityconcepts-231026202004-243d019d/85/PPT0-Computer-Security-Concepts-pptx-27-320.jpg)














