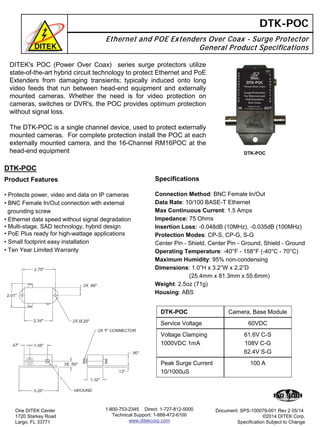
Ditek's POC series surge protectors use advanced hybrid circuit technology to safeguard Ethernet and PoE extenders from transients that could damage long video feeds, particularly for externally mounted cameras. The DTK-POC is a single-channel device that provides optimal protection without signal loss and should be installed at each camera along with a 16-channel RM16POC at the head-end equipment. Key specifications include a service voltage of 60VDC, peak surge current of 100A, and an operating temperature range of -40°F to 158°F.