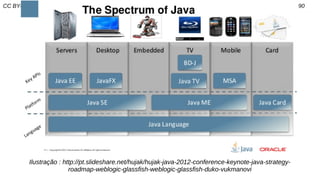
This document provides a comprehensive overview of the Java programming language and its frameworks, including its history, features such as object-oriented programming, security, and multi-platform capabilities. It encompasses practical coding examples, advice for effective programming practices, and references to various educational resources. Additionally, it emphasizes the importance of agile software development principles and includes insights from notable figures in the field.







![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 43/90
public class MyFirstJavaProgram{
/* This is my first java program.
* This will print 'Hello World' as the output
*/
public static void main(String[]args){
System.out.println("Hello World");// prints Hello World
}
}
Hello World!
C :> javac MyFirstJavaProgram.java
C :> java MyFirstJavaProgram
HelloWorld
Tutorialspoint, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-43-320.jpg)

![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 47/90
public class Puppy{
public Puppy(String name){
System.out.println("Passed Name is :"+ name );
}
public static void main(String[] args){
Puppy myPuppy =new Puppy("tommy");
}
}
PassedNameis:tommy](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-47-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 48/90
public class Puppy{
int puppyAge;
public Puppy(String name){
System.out.println("Passed Name is
:"+ name );
}
public void setAge(int age ){
puppyAge = age;
}
public int getAge(){
System.out.println("Puppy's age
is :"+ puppyAge );
return puppyAge;
PassedName is:tommy
Puppy's age is :2
Variable Value :2
public static void main(String[]args){
Puppy myPuppy =new
Puppy("tommy");
myPuppy.setAge(2);
myPuppy.getAge();
System.out.println("Variable
Value :"+ myPuppy.puppyAge );
}
}](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-48-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 49/90
import java.util.Scanner;
public class Entrada {
public static void main(String[] args) {
Scanner entrada = new Scanner(System.in);
String printar;
System.out.print("Printa o escrito pelo usuario ");
printar = entrada.nextLine(); //nextFloat, nextInt
System.out.println("Digitado: " +printar+ " !");
}
}](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-49-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 50/90public class Employee{
String name;
int age;
String designation;
double salary;
public Employee(String name){
this.name = name;
}
public void empAge(int empAge){
age = empAge;
}
public void empDesignation(String empDesig){
designation = empDesig;
}
public void empSalary(double empSalary){
salary = empSalary;
}
public void printEmployee(){
System.out.println("Name:"+ name );
System.out.println("Age:"+ age );
System.out.println("Designation:"+ designation );
System.out.println("Salary:"+ salary);
}
}
Age: 26
Designation:SeniorSoftwareEngineer
Salary: 1000.0
Name:MaryAnne
Age: 21
Designation:SoftwareEngineer
Salary: 500.0
public static void main(String args[]){
Employee empOne =new Employee("James Smith");
Employee empTwo =new Employee("Mary Anne");
empOne.empAge( 26 );
empOne.empDesignation("Senior Software
Engineer");
empOne.empSalary( 1000 );
empOne.printEmployee();
empTwo.empAge( 21 );
empTwo.empDesignation("Software Engineer");
empTwo.empSalary( 500 );
empTwo.printEmployee();
}
}](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-50-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 51/90public class Employee{
String name;
int age;
String designation;
double salary;
public Employee(String name){
this.name = name;
}
public void empAge(int empAge){
age = empAge;
}
public void empDesignation(String empDesig){
designation = empDesig;
}
public void empSalary(double empSalary){
salary = empSalary;
}
public void printEmployee(){
System.out.println("Name:"+ name );
System.out.println("Age:"+ age );
System.out.println("Designation:"+ designation );
System.out.println("Salary:"+ salary);
}
}
Age: 26
Designation:SeniorSoftwareEngineer
Salary: 1000.0
Name:MaryAnne
Age: 21
Designation:SoftwareEngineer
Salary: 500.0
public class EmployeeTest{
}
public staticvoid main(String args[]){
Employee empOne =new Employee("James Smith");
Employee empTwo =new Employee("Mary Anne");
empOne.empAge( 26 );
empOne.empDesignation("Senior Software
Engineer");
empOne.empSalary( 1000 );
empOne.printEmployee();
empTwo.empAge( 21 );
empTwo.empDesignation("Software Engineer");
empTwo.empSalary( 500 );
empTwo.printEmployee();
}
}](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-51-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 52/90public class Employee{
String name;
int age;
String designation;
double salary;
public Employee(String name){
this.name = name;
}
public void empAge(int empAge){
age = empAge;
}
public void empDesignation(String empDesig){
designation = empDesig;
}
public void empSalary(double empSalary){
salary = empSalary;
}
public void printEmployee(){
System.out.println("Name:"+ name );
System.out.println("Age:"+ age );
System.out.println("Designation:"+ designation );
System.out.println("Salary:"+ salary);
}
}
Age: 26
Designation:SeniorSoftwareEngineer
Salary: 1000.0
Name:MaryAnne
Age: 21
Designation:SoftwareEngineer
Salary: 500.0
public class EmployeeTest{
public staticvoid main(String args[]){
Employee empOne =new Employee("James Smith");
Employee empTwo =new Employee("Mary Anne");
empOne.empAge( 26 );
empOne.empDesignation("Senior Software
Engineer");
empOne.empSalary( 1000 );
empOne.printEmployee();
empTwo.empAge( 21 );
empTwo.empDesignation("Software Engineer");
empTwo.empSalary( 500 );
empTwo.printEmployee();
}
}](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-52-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 59/90
public class Test{
public static void main(String args[]){
int x =10;
if( x <20){
System.out.print("This is if statement");
}
}
}
This is if statement
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-59-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 60/90
public class Test{
public static void main(String args[]){
int x =30;
int y =10;
if( x ==30){
if( y ==10){
System.out.print("X = 30 and Y = 10");
}
}
}
}
X = 30 and Y = 10
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-60-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 61/90
public class Test{
public static void main(String args[]){
int x =30;
if(x <20){
System.out.print("This is if statement");
}else{
System.out.print("This is else statement");
}
}
}
Thisiselse statement
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-61-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 62/90
public class Test{
public static void main(String args[]){
int x =30;
if( x ==10){
System.out.print("Value of X is 10");
}elseif( x ==20){
System.out.print("Value of X is 20");
}elseif( x ==30){
System.out.print("Value of X is 30");
}else{
System.out.print("This is else statement");
}
}
} Value of X is30
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-62-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 63/90
public class Test{
public static void main(String args[]){
char grade = args[0].charAt(0);
switch(grade) {
case'A': System.out.println("Excellent!"); break;
case'B':
case'C': System.out.println("Well done"); break;
case'D': System.out.println("You passed"); break;
Case'F': System.out.println("Better try again"); break;
default: System.out.println("Invalid grade"); break
}
System.out.println("Your grade is "+ grade);
}
}
Your grade is A
Excellent!
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-63-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 64/90
public class Test{
public static void main(String args[]){
int x =10;
while( x <20){
System.out.print("value of x : "+ x );
x++;
System.out.print("n");
}
}
}
value of x :10
…
value of x :19
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-64-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 65/90
public class Test{
public static void main(String args[]){
int x =10;
do{
System.out.print("value of x : "+ x );
x++;
System.out.print("n");
}while( x <20);
}
} value of x :10
…
value of x :19
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-65-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 66/90
public class Test{
public static void main(String args[]){
for(int x =10; x <20; x = x+1){
System.out.print("value of x : "+ x );
System.out.print("n");
}
}
}
value of x :10
…
value of x :19
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-66-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 67/90
public class Test{
public static void main(String args[]){
int[] numbers ={10,20,30,40,50};
for(int x : numbers){
System.out.print( x );
}
}
}
1020304050
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-67-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 70/90
public class Test{
public static void main(String args[]){
int[] numbers ={10,20,30,40,50};
for(int x : numbers){
if(x ==30){
break;
}
System.out.print( x );
System.out.print("n");
}
}
}
10
20
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-70-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 71/90
public class Test{
public static void main(String args[]){
int[] numbers ={10,20,30,40,50};
for(int x : numbers){
if( x ==30){
continue;
}
System.out.print( x );
System.out.print("n");
}
}
}
10
20
40
50Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-71-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 72/90
public class TestArray{
public static void main(String[] args){
double[] myList ={1.9,2.9,3.4,3.5};
for(double element: myList){
System.out.println(element);
}
}
}
1.9
2.9
3.4
3.5Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-72-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 73/90
public class Test{
public static void main(String args[]){
int[] numbers ={10,20,30,40,50};
for(int x : numbers ){
System.out.print(x);
System.out.print(",");
}
System.out.print("n");
String[] names ={"James","Larry","Tom","Lacy"};
for(String name : names ){
System.out.print( name );
System.out.print(",");
}
}
}
10,20,30,40,50,
James,Larry,Tom,Lacy,
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-73-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 74/90
public class TestArray{
public static void main(String[] args){
double[] myList ={1.9,2.9,3.4,3.5};
for(int i =0; i < myList.length; i++){
System.out.println(myList[i]+" ");
}
double total =0;
for(int i =0; i < myList.length; i++){
total += myList[i];
}
System.out.println("Total is "+ total);
double max = myList[0];
for(int i =1; i < myList.length; i++){
if(myList[i]> max) max = myList[i];
}
System.out.println("Max is "+ max);
}
}
1.9
2.9
3.4
3.5
Totalis11.7
Maxis3.5
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-74-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 75/90
public static void printArray(int[] array){
for(int i =0; i < array.length; i++){
System.out.print(array[i]+" ");
}
}
objeto.printArray(newint[]{3,1,2,6,4,2});
public static int[] reverse(int[] list){
int[] result =new int[list.length];
for(int i =0, j = result.length -1; i < list.length; i++, j--){
result[j]= list[i];
}
return result;
}
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-75-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 76/90
public class Test{
public static void main(String args[]){
Integer x =5;
System.out.println( x.byteValue());
System.out.println(x.doubleValue());
System.out.println( x.longValue());
}
}
5
5.0
5Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-76-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 78/90
public class StringDemo{
public static void main(String args[]){
String string1 ="saw I was ";
System.out.println("Dot "+ string1 +"Tod");
}
}
Dot saw I was Tod
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-78-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 79/90
public class StringDemo{
public static void main(String args[]){
char[] helloArray ={'h','e','l','l','o','.'};
String helloString =new String(helloArray);
System.out.println(helloString);
}
}
hello.
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-79-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 80/90
int compareTo(Object o)
int compareTo(String anotherString)
String concat(String str)
static String copyValueOf(char[] data)
int length()
String toUpperCase()
…
Pag 105-156
.
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-80-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 81/90
Class FreshJuice{
enum FreshJuiceSize{ SMALL, MEDUIM, LARGE }
FreshJuiceSize size;
public static void main(String args[]){
FreshJuice juice =new FreshJuice();
juice.size =FreshJuice.FreshJuiceSize.MEDUIM;
System.out.println("Tamanho do Suco:" +juice.size);
}
}
Tamanho do Suco: MEDIUM
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-81-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 82/90
public class Employee{
private static double salary;
public static final String DEPARTMENT = "Development ";
public static void main(String args[]){
salary = 1000;
System.out.println(DEPARTMENT+"average salary:"+salary);
}
}
Development average salary:1000
Tutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-82-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 84/90
public class Dog extends Mammal{
public static void main(String args[]){
Animal a =new Animal();
Mammal m =new Mammal();
Dog d =new Dog();
System.out.println(m instanceof Animal);
System.out.println(d instanceof Mammal);
System.out.println(d instanceof Animal);
}
} true
true
trueTutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-84-320.jpg)
![CC BY-SA luizrauber@gmail.com || fb.com/luizrauber 86/90
Interface Animal{}
class Mammal implements Animal{}
public class Dog extends Mammal{
public static void main(String args[]){
Mammal m =new Mammal();
Dog d =new Dog();
System.out.println(m instanceof Animal);
System.out.println(d instanceof Mammal);
System.out.println(d instanceof Animal);
}
}
true
true
trueTutorialspoint Java, 2015](https://image.slidesharecdn.com/java-160805171753/85/Plataforma-e-Lingaguem-Java-Swing-86-320.jpg)