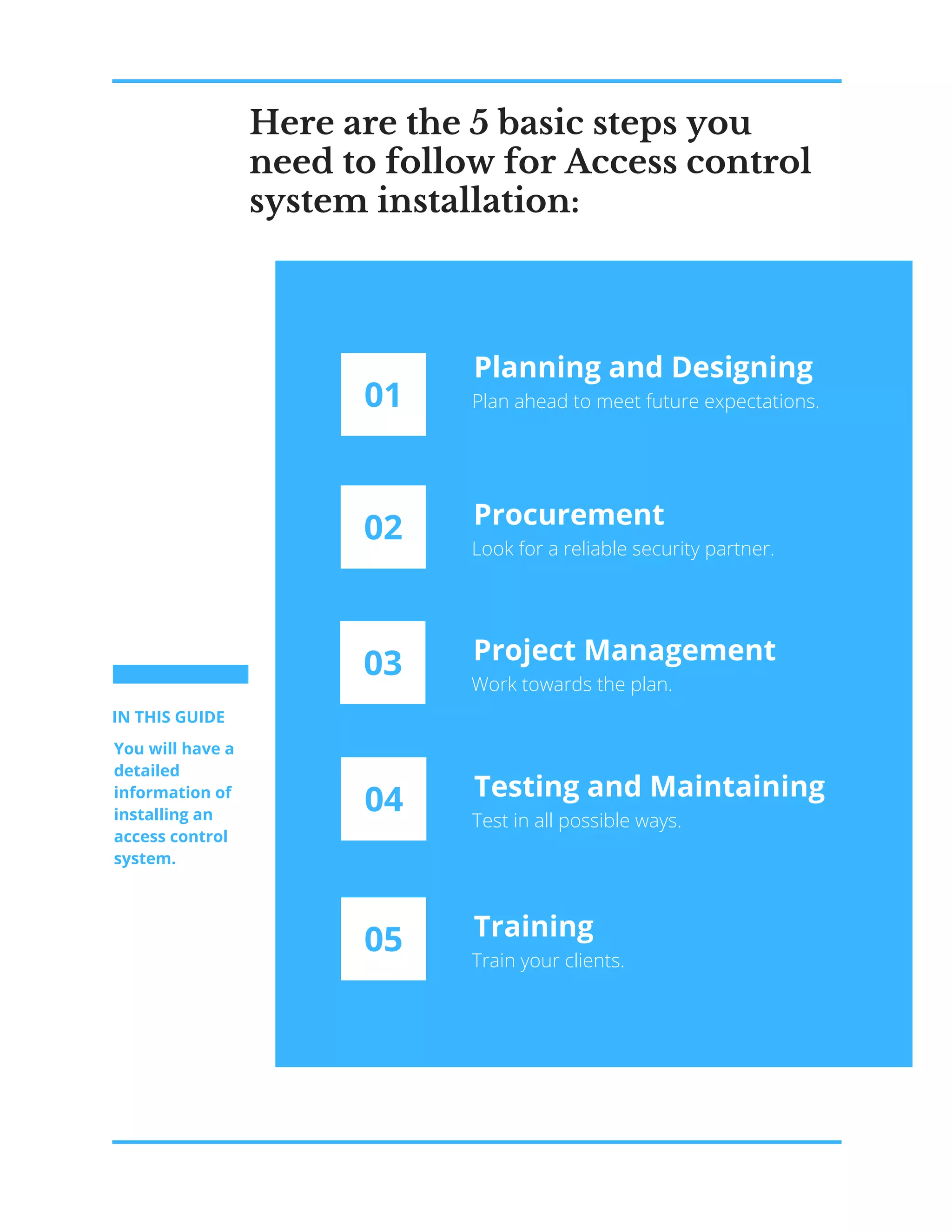
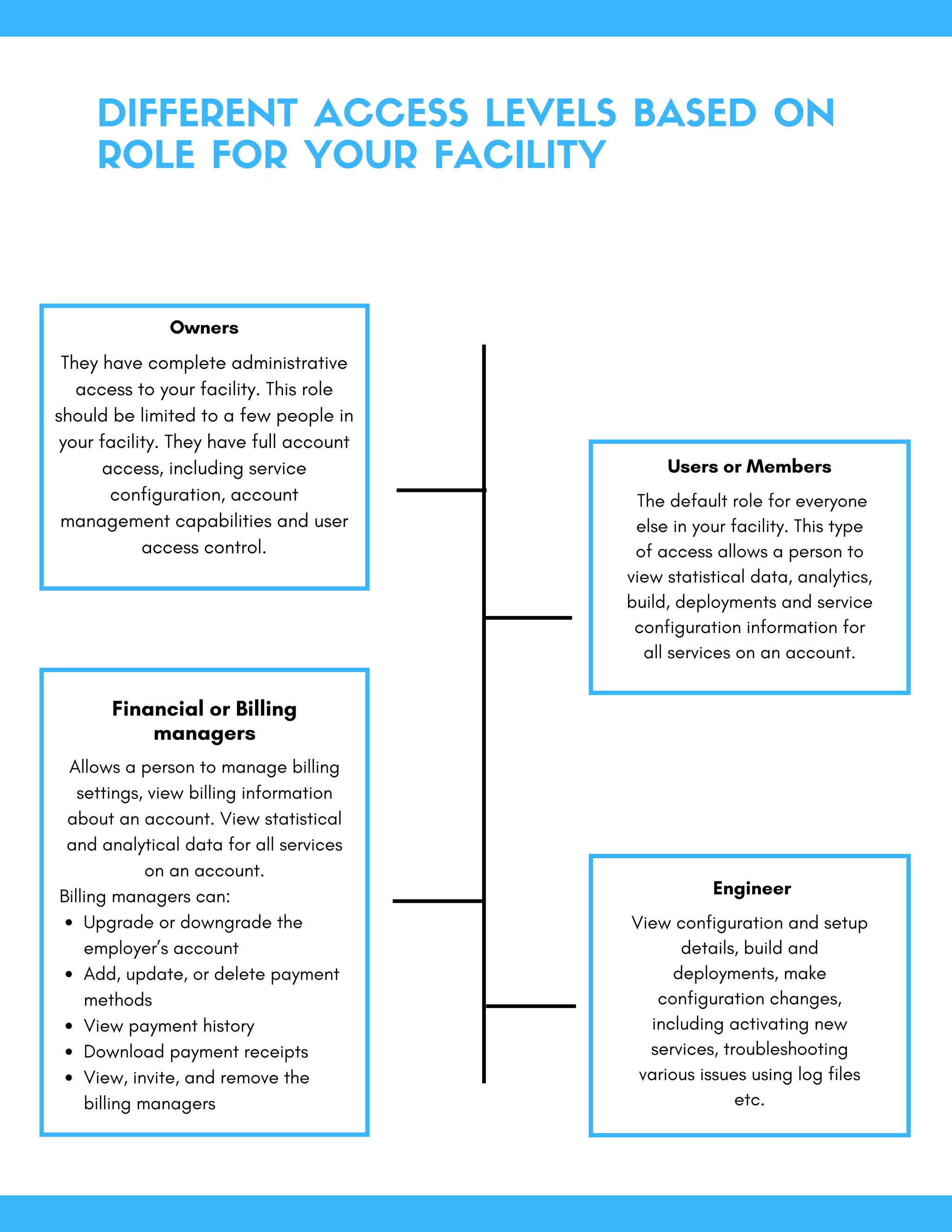
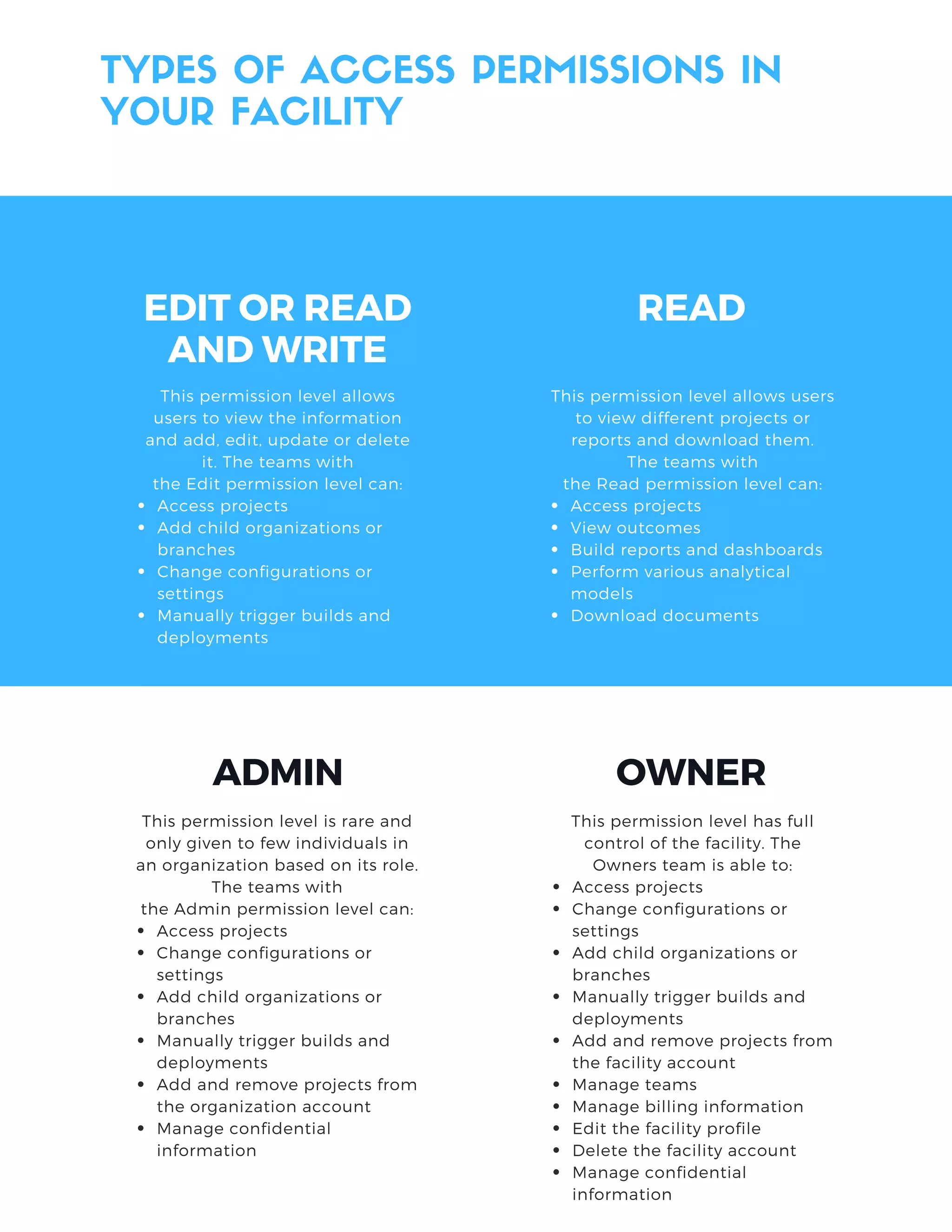
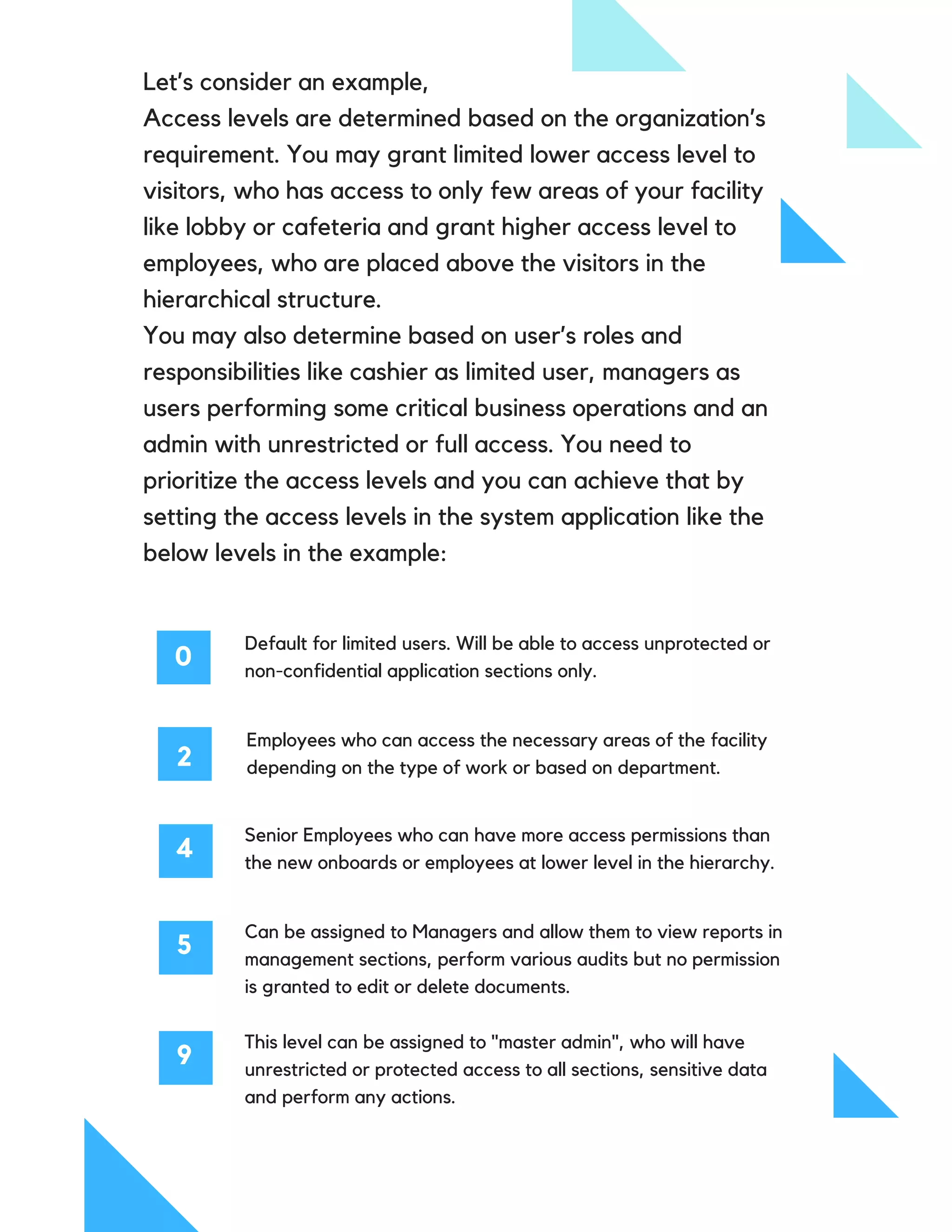
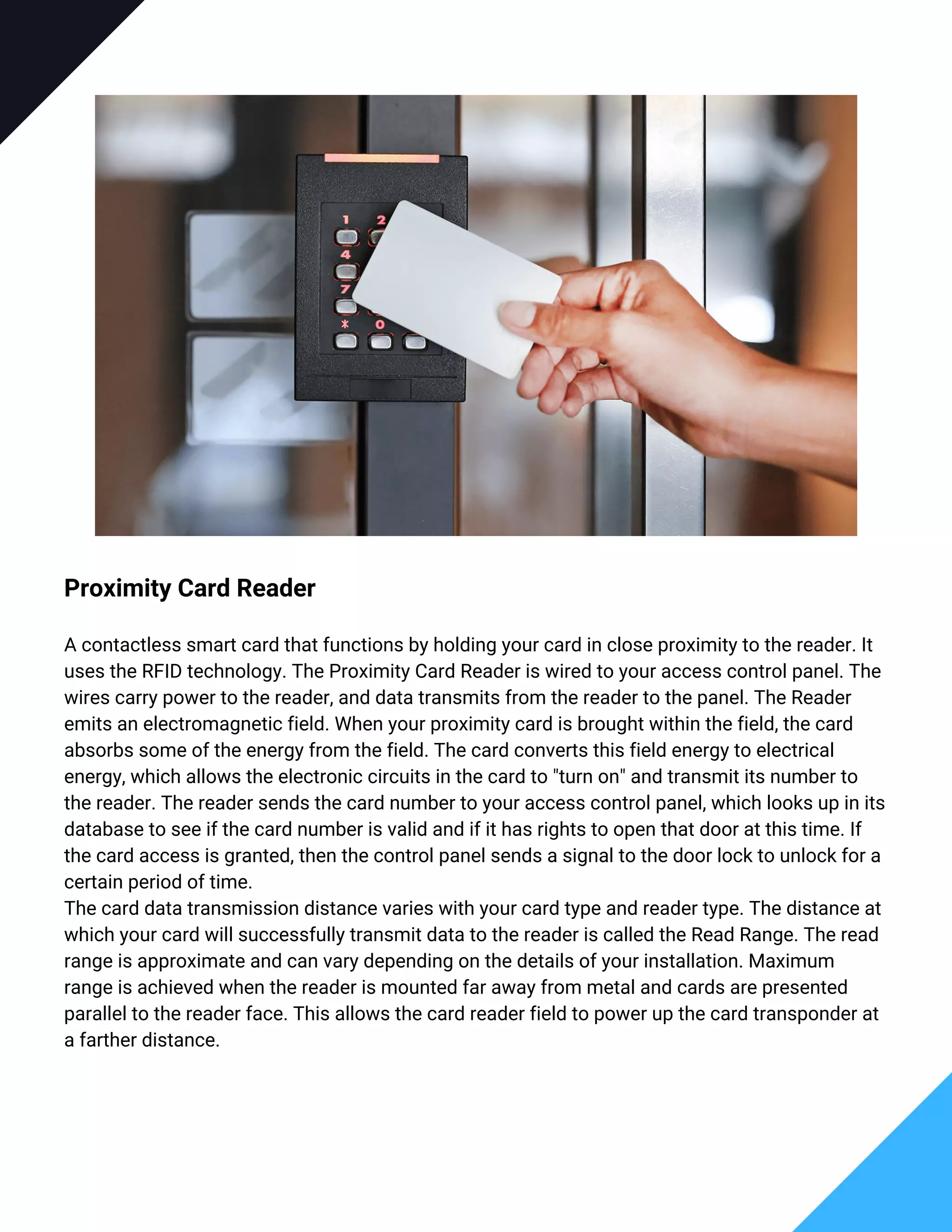
This guide outlines essential steps for planning and installing an electronic access control system, including planning, procurement, project management, testing, and training. It emphasizes the importance of understanding specific facility needs, evaluating access levels, and involves critical roles such as facility managers and HR in the decision-making process. The document also details various authentication technologies and access permissions necessary for ensuring effective security management within an organization.