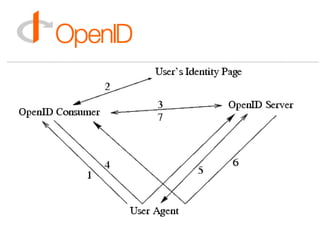
OpenID
•
4 likes•366 views
Presentation of Tamas Neltz (Index.hu) at Budapest New Tech MeetUp 2nd of may, 2007. http://newtech.meetup.com/42/calendar/5637411/
Report
Share
Report
Share
Recommended
PSR7 - interoperabilità HTTP

Talk dell'incontro di aprile 2018 del PUG Roma. Video disponibile su https://www.youtube.com/watch?v=U0TQ0iehXYU
Creativity-in-Cosmetics

This document summarizes research conducted by a team on creativity in the cosmetics industry. Through surveys and interviews at Sephora stores, the team found that many cosmetics users struggle to find products that match their skin tone. They observed Sephora's Color IQ machine, which identifies matching products but has limitations. The team's research showed opportunities to help users select the right makeup through an improved technology solution. Their goal is to develop a concept that provides an easy, efficient way for women to find matching products and feel confident in their purchases.
Certificate on Cybersecurity

This certificate certifies that the individual successfully completed a 12-hour online cybersecurity course from September 15 to October 27, 2015. The course was developed by faculty from MIT's Computer Science and Artificial Intelligence Laboratory in collaboration with MIT Professional Education. The certificate is signed by the Executive Director of MIT Professional Education and the Director and a Principal Research Scientist of the Computer Science and Artificial Intelligence Laboratory to validate the individual's completion of the course.
Alternating Current Machines 11&12

The document discusses synchronous motors and single-phase synchronous motors. It provides details on 2-pole and 3-phase synchronous motors, including their construction, operation at different loads, and stability. It also describes two main types of single-phase synchronous motors - reluctance motors and hysteresis motors. Reluctance motors start as induction motors and lock into synchronism once the salient poles become permanently magnetized by the stator field.
Mina essam CV

Mina Essam Anton is seeking a career in electrical power engineering. She has a B.S. degree in electric power and machines from El shourouk Academy. She has experience working as a maintenance engineer and has completed training at ABB factories. Her technical skills include knowledge of circuit boards, processors, electronic equipment, and computer hardware and software as well as transmission, broadcasting, switching, control systems and quality control.
Recommended
PSR7 - interoperabilità HTTP

Talk dell'incontro di aprile 2018 del PUG Roma. Video disponibile su https://www.youtube.com/watch?v=U0TQ0iehXYU
Creativity-in-Cosmetics

This document summarizes research conducted by a team on creativity in the cosmetics industry. Through surveys and interviews at Sephora stores, the team found that many cosmetics users struggle to find products that match their skin tone. They observed Sephora's Color IQ machine, which identifies matching products but has limitations. The team's research showed opportunities to help users select the right makeup through an improved technology solution. Their goal is to develop a concept that provides an easy, efficient way for women to find matching products and feel confident in their purchases.
Certificate on Cybersecurity

This certificate certifies that the individual successfully completed a 12-hour online cybersecurity course from September 15 to October 27, 2015. The course was developed by faculty from MIT's Computer Science and Artificial Intelligence Laboratory in collaboration with MIT Professional Education. The certificate is signed by the Executive Director of MIT Professional Education and the Director and a Principal Research Scientist of the Computer Science and Artificial Intelligence Laboratory to validate the individual's completion of the course.
Alternating Current Machines 11&12

The document discusses synchronous motors and single-phase synchronous motors. It provides details on 2-pole and 3-phase synchronous motors, including their construction, operation at different loads, and stability. It also describes two main types of single-phase synchronous motors - reluctance motors and hysteresis motors. Reluctance motors start as induction motors and lock into synchronism once the salient poles become permanently magnetized by the stator field.
Mina essam CV

Mina Essam Anton is seeking a career in electrical power engineering. She has a B.S. degree in electric power and machines from El shourouk Academy. She has experience working as a maintenance engineer and has completed training at ABB factories. Her technical skills include knowledge of circuit boards, processors, electronic equipment, and computer hardware and software as well as transmission, broadcasting, switching, control systems and quality control.
ios-app-02

The document discusses privacy settings for social media posts. It explains that posts can be set as public, where anyone can see and comment, or private, where only invited friends have access. When a post is set to private, the user is prompted to invite friends to view the post before it becomes private and uneditable. The document provides examples of notifications shown when changing a post's privacy settings between public and private viewability and commenting options.
The saying3

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive function. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
SmartWatch Prototype

This document describes the design and implementation of a smartwatch prototype using inexpensive, commonly available components. Key features included are a touchscreen LCD for display and input, Bluetooth module for communication with a smartphone, and a wireless charging system for the battery. The prototype demonstrates the integration of these technologies and serves as a proof of concept for a basic smartwatch. Challenges encountered included inefficient screen updates, modifying Bluetooth code for notifications, and addressing differences in the charging module and Arduino voltages. The completed prototype functions as a basic smartwatch, displaying time and notifications from a paired phone.
Mina CV

Mina Tabib Souliman is seeking a position as an accountant. He has over 5 years of experience working as an accountant for various companies in Kuwait and Egypt. Currently, he works as an accountant for Unirisk Insurance Services Company in Kuwait where his responsibilities include handling accounts receivable and payable, preparing journal vouchers, processing premium payments and commissions, and generating various reports. He is fluent in Arabic and English and has a bachelor's degree in commerce from Assuit University in Egypt.
noha cv

Noha Mohammed Ibrahim is a Pharmaceutical Chemistry student at Cairo University currently pursuing her M.S. degree. She graduated from Cairo University in 2012 with a B.S. in Pharmaceutical Chemistry, ranking 15th in her class of 1,700 students. She has received Dean's Honors and has experience as a teaching assistant, lab assistant, and community pharmacist. Her skills include research, teamwork, communication, problem solving, and computers. She is currently working on her Master's thesis and volunteers with a charity committee.
Noha Hefny CV

Noha Anbar Hefny is a content management specialist currently working at Hindawi Publishing Corporation in Cairo, Egypt. She has over 3 years of experience handling academic papers and publications. Prior to her current role, she worked as a project coordinator at EMP media. Noha is seeking new challenges at a well-established organization where she can further develop her skills through diligent effort. She holds a BSc in Commerce and Business Administration from Helwan University.
Human body center of mass and stability

This document discusses how to analyze the center of mass and static stability of the human body. It provides instructions on how to calculate the center of gravity (CG) of different body segments and the whole body by:
1) Drawing a scaled diagram and labeling joint positions
2) Calculating the CG of each segment using coordinates and mass ratios from tables
3) Summing the products of each segment's mass and CG coordinates to find the whole body's CG position using provided equations.
An example calculation is shown to find the female player's CG in the diagram and check her static stability.
Contact center services

Bluewish Solutions provides virtual reception services for small businesses through call handling, appointment setting, and feedback collection according to a client's protocols without the overhead of full-time employees. Clients can reach their business 24/7 without changing their phone number. The service includes appointment scheduling, confirmation calls, and generating reports to analyze performance and service feedback for both franchise locations and corporate offices.
Twitter.com ry4

@RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4
ios-app-01

The document is a screenshot of a social media post writing interface. It shows that the post is currently private, with only invited friends able to comment but everyone able to read. It also includes text from a New York Times article about whether travel has become narcissistic.
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
More Related Content
Viewers also liked
ios-app-02

The document discusses privacy settings for social media posts. It explains that posts can be set as public, where anyone can see and comment, or private, where only invited friends have access. When a post is set to private, the user is prompted to invite friends to view the post before it becomes private and uneditable. The document provides examples of notifications shown when changing a post's privacy settings between public and private viewability and commenting options.
The saying3

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive function. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
SmartWatch Prototype

This document describes the design and implementation of a smartwatch prototype using inexpensive, commonly available components. Key features included are a touchscreen LCD for display and input, Bluetooth module for communication with a smartphone, and a wireless charging system for the battery. The prototype demonstrates the integration of these technologies and serves as a proof of concept for a basic smartwatch. Challenges encountered included inefficient screen updates, modifying Bluetooth code for notifications, and addressing differences in the charging module and Arduino voltages. The completed prototype functions as a basic smartwatch, displaying time and notifications from a paired phone.
Mina CV

Mina Tabib Souliman is seeking a position as an accountant. He has over 5 years of experience working as an accountant for various companies in Kuwait and Egypt. Currently, he works as an accountant for Unirisk Insurance Services Company in Kuwait where his responsibilities include handling accounts receivable and payable, preparing journal vouchers, processing premium payments and commissions, and generating various reports. He is fluent in Arabic and English and has a bachelor's degree in commerce from Assuit University in Egypt.
noha cv

Noha Mohammed Ibrahim is a Pharmaceutical Chemistry student at Cairo University currently pursuing her M.S. degree. She graduated from Cairo University in 2012 with a B.S. in Pharmaceutical Chemistry, ranking 15th in her class of 1,700 students. She has received Dean's Honors and has experience as a teaching assistant, lab assistant, and community pharmacist. Her skills include research, teamwork, communication, problem solving, and computers. She is currently working on her Master's thesis and volunteers with a charity committee.
Noha Hefny CV

Noha Anbar Hefny is a content management specialist currently working at Hindawi Publishing Corporation in Cairo, Egypt. She has over 3 years of experience handling academic papers and publications. Prior to her current role, she worked as a project coordinator at EMP media. Noha is seeking new challenges at a well-established organization where she can further develop her skills through diligent effort. She holds a BSc in Commerce and Business Administration from Helwan University.
Human body center of mass and stability

This document discusses how to analyze the center of mass and static stability of the human body. It provides instructions on how to calculate the center of gravity (CG) of different body segments and the whole body by:
1) Drawing a scaled diagram and labeling joint positions
2) Calculating the CG of each segment using coordinates and mass ratios from tables
3) Summing the products of each segment's mass and CG coordinates to find the whole body's CG position using provided equations.
An example calculation is shown to find the female player's CG in the diagram and check her static stability.
Contact center services

Bluewish Solutions provides virtual reception services for small businesses through call handling, appointment setting, and feedback collection according to a client's protocols without the overhead of full-time employees. Clients can reach their business 24/7 without changing their phone number. The service includes appointment scheduling, confirmation calls, and generating reports to analyze performance and service feedback for both franchise locations and corporate offices.
Viewers also liked (9)
More from hirbehozo
Twitter.com ry4

@RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4 @RY4
ios-app-01

The document is a screenshot of a social media post writing interface. It shows that the post is currently private, with only invited friends able to comment but everyone able to read. It also includes text from a New York Times article about whether travel has become narcissistic.
More from hirbehozo (6)
Recently uploaded
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/building-and-scaling-ai-applications-with-the-nx-ai-manager-a-presentation-from-network-optix/
Robin van Emden, Senior Director of Data Science at Network Optix, presents the “Building and Scaling AI Applications with the Nx AI Manager,” tutorial at the May 2024 Embedded Vision Summit.
In this presentation, van Emden covers the basics of scaling edge AI solutions using the Nx tool kit. He emphasizes the process of developing AI models and deploying them globally. He also showcases the conversion of AI models and the creation of effective edge AI pipelines, with a focus on pre-processing, model conversion, selecting the appropriate inference engine for the target hardware and post-processing.
van Emden shows how Nx can simplify the developer’s life and facilitate a rapid transition from concept to production-ready applications.He provides valuable insights into developing scalable and efficient edge AI solutions, with a strong focus on practical implementation.GraphRAG for Life Science to increase LLM accuracy

GraphRAG for life science domain, where you retriever information from biomedical knowledge graphs using LLMs to increase the accuracy and performance of generated answers
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

Imagine a world where machines not only perform tasks but also learn, adapt, and make decisions. This is the promise of Artificial Intelligence (AI), a technology that's not just enhancing our lives but revolutionizing entire industries.
CAKE: Sharing Slices of Confidential Data on Blockchain

Presented at the CAiSE 2024 Forum, Intelligent Information Systems, June 6th, Limassol, Cyprus.
Synopsis: Cooperative information systems typically involve various entities in a collaborative process within a distributed environment. Blockchain technology offers a mechanism for automating such processes, even when only partial trust exists among participants. The data stored on the blockchain is replicated across all nodes in the network, ensuring accessibility to all participants. While this aspect facilitates traceability, integrity, and persistence, it poses challenges for adopting public blockchains in enterprise settings due to confidentiality issues. In this paper, we present a software tool named Control Access via Key Encryption (CAKE), designed to ensure data confidentiality in scenarios involving public blockchains. After outlining its core components and functionalities, we showcase the application of CAKE in the context of a real-world cyber-security project within the logistics domain.
Paper: https://doi.org/10.1007/978-3-031-61000-4_16
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Recently uploaded (20)
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
Best 20 SEO Techniques To Improve Website Visibility In SERP

Best 20 SEO Techniques To Improve Website Visibility In SERP
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for Life Science to increase LLM accuracy
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

AI 101: An Introduction to the Basics and Impact of Artificial Intelligence
CAKE: Sharing Slices of Confidential Data on Blockchain

CAKE: Sharing Slices of Confidential Data on Blockchain