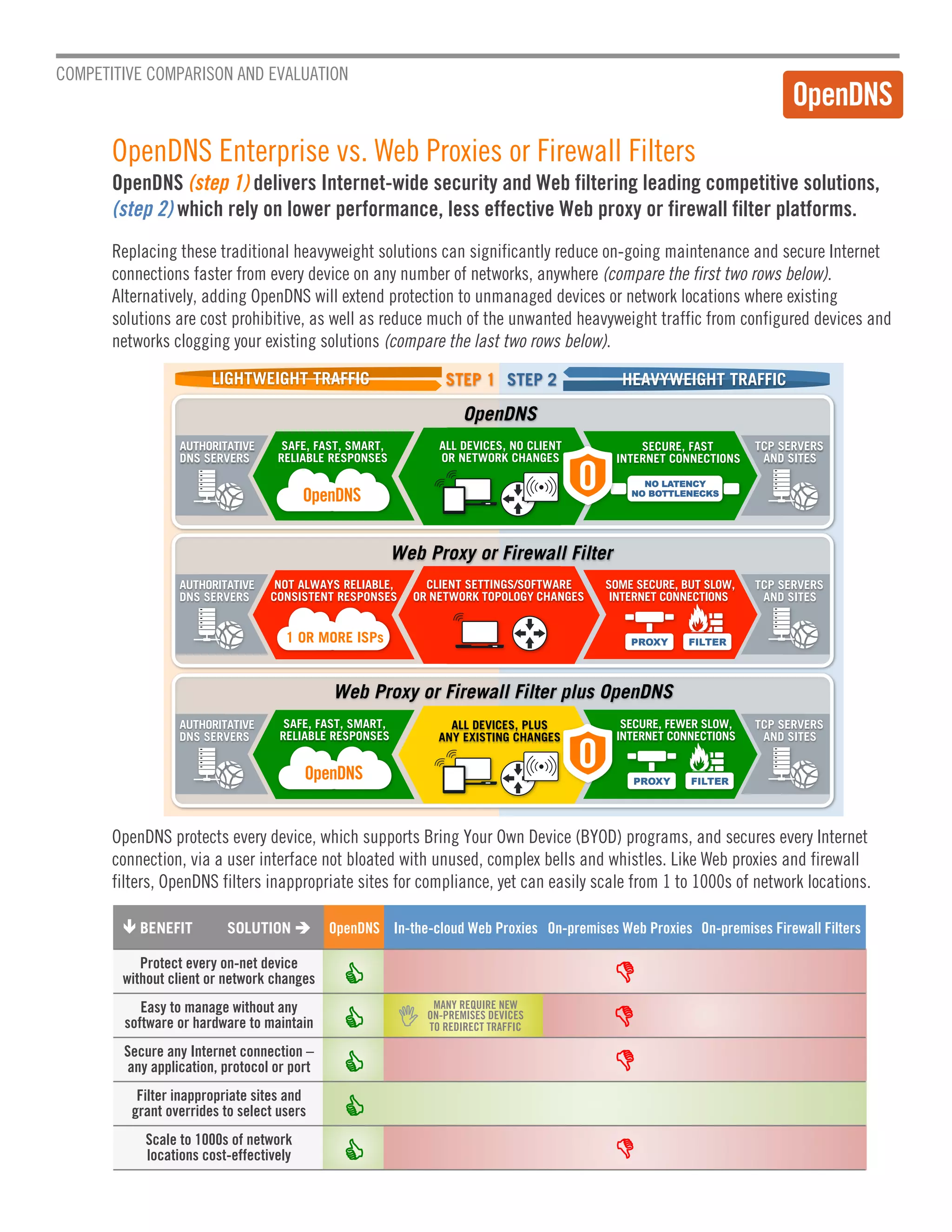
Many security vendors focus on efficacy but overlook usability and performance. OpenDNS delivers internet-wide security and filtering through lightweight DNS redirection without network changes, making it easy to provision, enforce policies, and manage across many locations. Alternatively, web proxies and firewalls rely on heavier traffic redirection and often require new appliances, client settings, and network topology changes per site, increasing maintenance costs and potentially reducing performance.