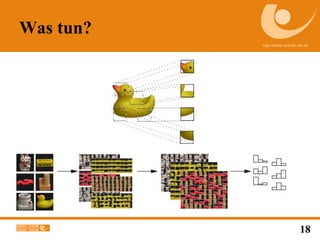
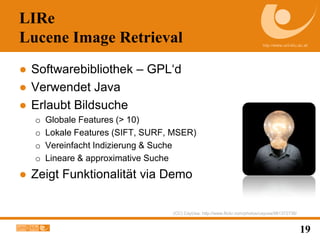
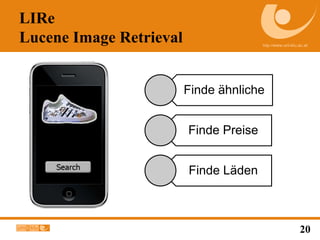
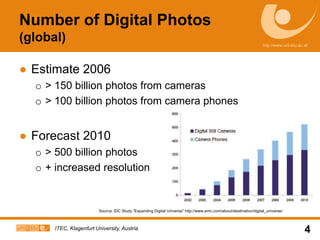
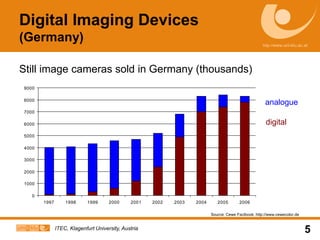
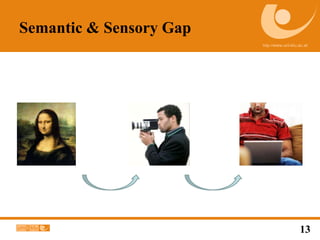
The document discusses advancements in digital imaging and the challenges of image retrieval, particularly in interpreting and comparing images. It highlights the exponential growth in the number of digital photos and the limitations of current technology in bridging the semantic gap in image understanding. Additionally, it mentions the development of image retrieval software that simplifies searching through global and local features.


![ForschungsthemenFrom [Datta et al. 2008]](https://image.slidesharecdn.com/mlux-barcamp-110205041330-phpapp01/85/Ohne-LIRe-keine-Bildsuche-14-320.jpg)