A key technical underpinning of the Cloud are Application Programming Interfaces (API) - consistent methods for applications to interface with services in the cloud. More and more it will be through APIs that cloud data moves. The security of consumer APIs was threatened by the so-called 'password anti-pattern' – a model in which a client would collect and replay the password for a user at an API in order to access information on behalf of that user. OAuth not only defeats the password anti-pattern, but does much more. OAuth 2.0 defines a consistent, flexible identity and policy architecture for web applications, web services, devices, and desktop clients attempting to communicate with Cloud APIs. We'll discuss what OAuth provides, where it came from, and where its going.
About Paul Madsen
Paul Madsen is a Senior Technical Architect within the Office of the CTO at Ping Identity. He has served in various design, chairing, editing, and education roles for a number of federation standards, including OASIS Security Assertion Markup Language (SAML), OASIS Service Provisioning Markup Language (SPML), and Liberty Identity Web Services Framework (ID-WSF). He participates in a number of the Kantara Initiative's activities, as well as various other cloud identity initiatives. He holds an M.Sc. in Applied Mathematics and a Ph.D. in Theoretical Physics from Carleton University and the University of Western
About Brian Campbell
As Principal Architect for Ping Identity, Brian Campbell aspires to one day know what a Principal Architect actually does for a living. In the meantime, he tries to make himself useful by ideating, designing and building software systems such as Ping’s flagship product PingFederate. When not making himself useful, he contributes to various identity and security standards including a two-year stint as co-chair of the OASIS Security Services Technical Committee and a current focus on OAuth 2.0 within the IETF. He holds a B.A., magna cum laude, in Computer Science from Amherst College in Massachusetts. Despite spending four years in the state, he has to look up how to spell "Massachusetts" every time he writes it.
![" 8)*0-/&9),%*0,(A&"/,%0$),$&40$%0*&$%)&![,)&-2&
$%)&>9!&($&:0*D&;C)*+$E&
" ?3(C<)*?0*D0C)*+$EI,-3&
" %]?^__444IA0*5)C0*I,-3_0*_?(#A3(C<)*&
" 8)/H)C&0*&H(/0-#<&C)<0D*K&,%(0/0*DK&)C0+*DK&(*C&
)C#,(+-*&/-A)<&2-/&(&*#3@)/&-2&2)C)/(+-*&
<$(*C(/C<K&0*,A#C0*D&8:BFK&;JON8V&.&
;*2-/3(+-*&>(/C<&
" N-/5)C&40$%&<#,,)<<2#A&<$(*C(/C<&$--K&A05)&
8"BF&.&`%-?)2#AAEa&!"#$%&.&8>;B&
" b-AC<&(*&BI8,I&0*&"??A0)C&B($%)3(+,<&(*C&(&:%IJI&0*&9%)-/)+,(A&:%E<0,<&2/-3&>(/A)$-*&
c*0H)/<0$E&(*C&$%)&c*0H)/<0$E&-2&N)<$)/*&!*$(/0-&/)<?),+H)AEI&
" ;&5*-4K&3E&@-EG<&40,5)C&<3(%$I&
" d)$K&?/-2)<<0-*(AAEK&%)&0<&)e),+H)AE&3E&?))/I&
" 8-&4%-f<&<-&<3(/$&*-4K&)%g&
" 8)A2&(<<)/$)C&B-<$&;*$)/)<+*D&B(*&0*&;C)*+$E&&
" J-)<*f$&(A4(E<&C/0*5&@)2-/)&*--*K&@#$&4%)*&%)&C-)<&`E-#&5*-4K&02&$%)/)&4(<&(&A-*D&
3))+*D&-/&<-3)$%0*DaK&%)&?/)2)/<&(&S.9&
" !/&<0P&
" :/-A0h,&$4))$)/&40$%&4)AA&-H)/&%(A2&(&$%-#<(*C&2-AA-4)/<&O&?(#A3(C<)*&
" 8+AA&@A-D<&`%-4&L#(0*$a&($&,-**),+CI@A-D<?-$I,-3&.&?(#A3(C<)*I?-<$)/-#<I,-3&
" 8+AA&4(0+*D&2-/&(&S--DA)T&0*H0$)&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-3-2048.jpg)


&$-5)*&
`8"BF&(<<)/+-*a&$-&(&8!":&/)L#)<$&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-8-2048.jpg)
![Ua&:(<<4-/C&(*+O?(])/*&&
80$)<&(<5<&d!c&2-/&E-#/&S!!SF7&?(<<4-/C&<-&0$&
,(*&(,,)<<&E-#/&S--DA)&<$#eI&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-11-2048.jpg)


![J/0H)/<&
:(<<4-/C&
F(,5&-2& (*+O
<$(*C(/C<& ?(])/*&
!"#$%&
&
W(+H)&
&
3-@0A)&
>A-#C&":;<&
"??A0,(+-*<&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-18-2048.jpg)
![7*$)/&!"#$%l&
• "*&-?)*&?/-$-,-A&$-&(AA-4&<),#/)&":;&(#$%-/01(+-*&0*&(&
<03?A)&(*C&<$(*C(/C&3)$%-C&2/-3&C)<5$-?K&3-@0A)&(*C&
4)@&(??A0,(+-*<I&
• J)h*)<&(#$%-/01(+-*&.&(#$%)*+,(+-*&2/(3)4-/5&2-/&
67892#A&":;<&
• "??A0)C&$-&C)A)D($)C&(#$%-/01(+-*&'&30+D($)<&?(<<4-/C&
(*+O?(])/*&O&(/,%)$E?0,(A&#<)&,(<)&
• :/-H0C)<&(&<$(*C(/C&4(E&$-&D0H)&(&r5)Ef&$-&(&$%0/CO?(/$E&
4%0,%&(AA-4<&-*AE&A030$)C&(,,)<<&$-&?)/2-/3&<?),0h,&
2#*,+-*<&
– N0$%-#$&C0H#AD0*D&E-#/&,/)C)*+(A<&&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-19-2048.jpg)
![A [confusing] Little History&
• First was the Emergence of Proprietary Solutions
– Google AuthSub, AOL OpenAuth, Yahoo BBAuth,
Upcoming API, Flickr API, AWS API, and more
• OAuth Core 1.0 [Oct 2007]
– Open protocol to standardize what was already being
done
• OAuth Core 1.0 Revision A [June 2009]
– Addresses a session fixation attack
• The OAuth 1.0 Protocol / RFC 5849 [April 2010]
– Move to the IETF as informational documentation of
1.0a with editorial clarifications and errata](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-31-2048.jpg)
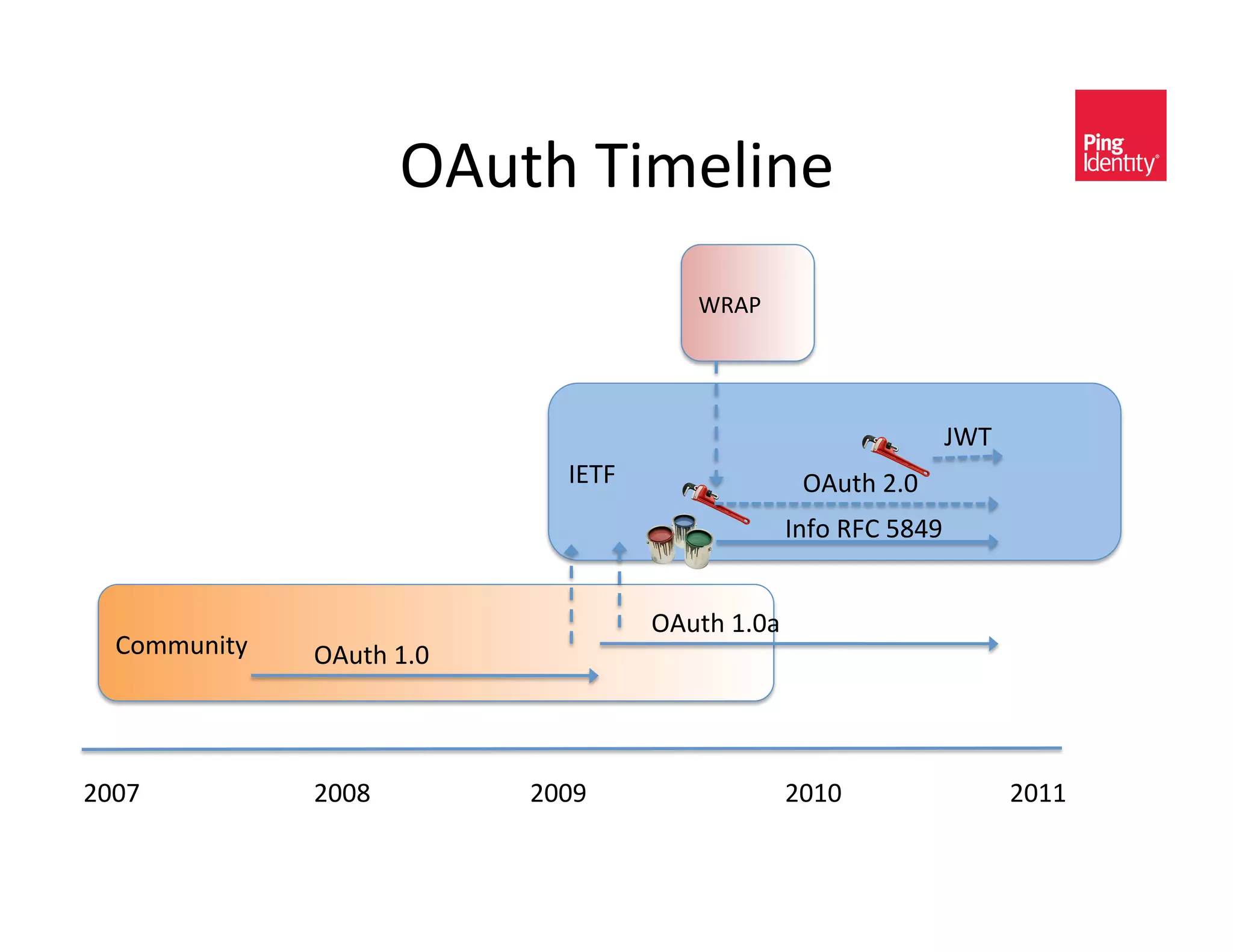
![B-/)&b0<$-/EK&8+AA&>-*2#<0*D&
• !"#$%&N6":&`N)@&6)<-#/,)&"#$%-/01(+-*&
:/-hA)<a [v(*&UZkZ]
– Better Support for non-web applications
– Simplify the Client
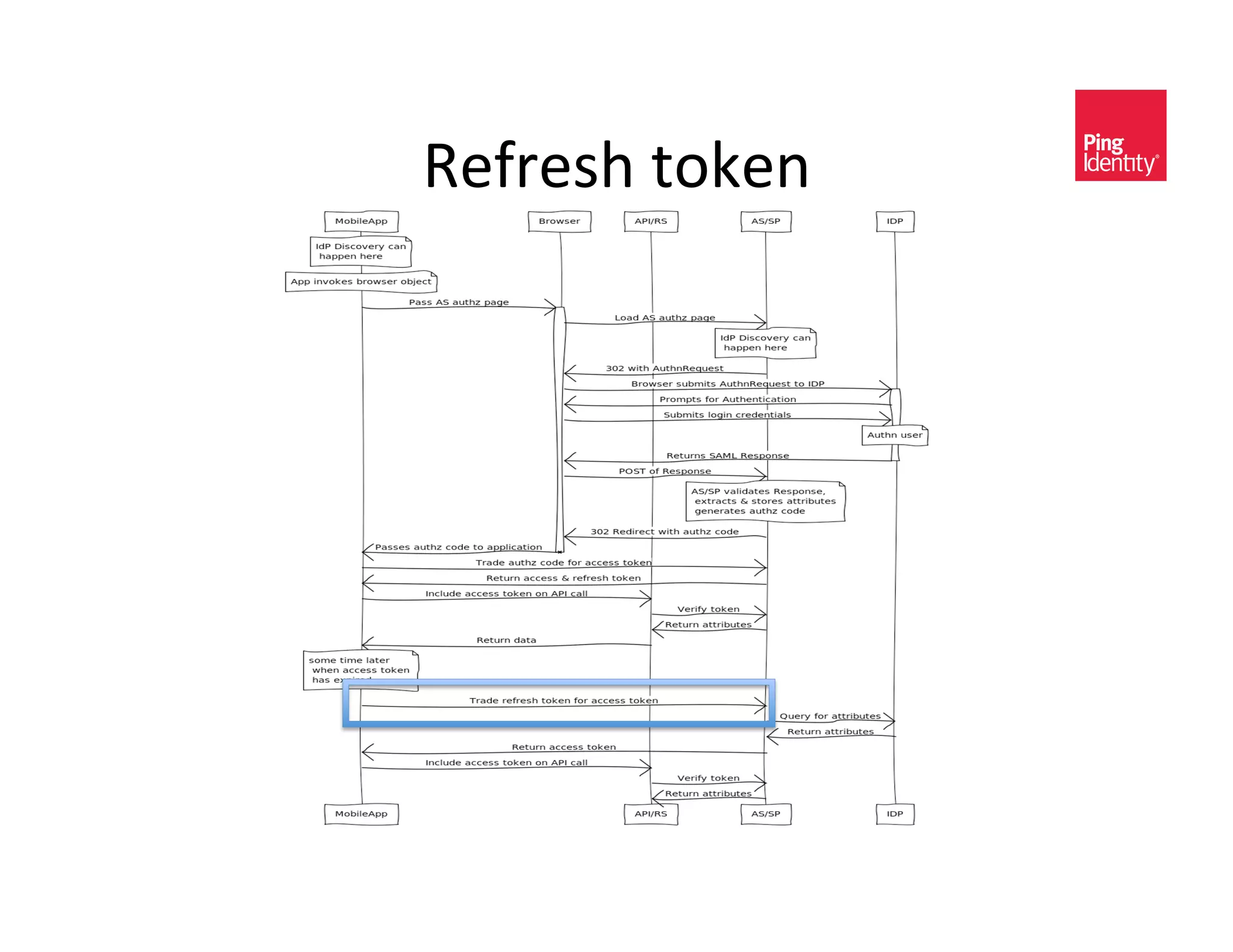
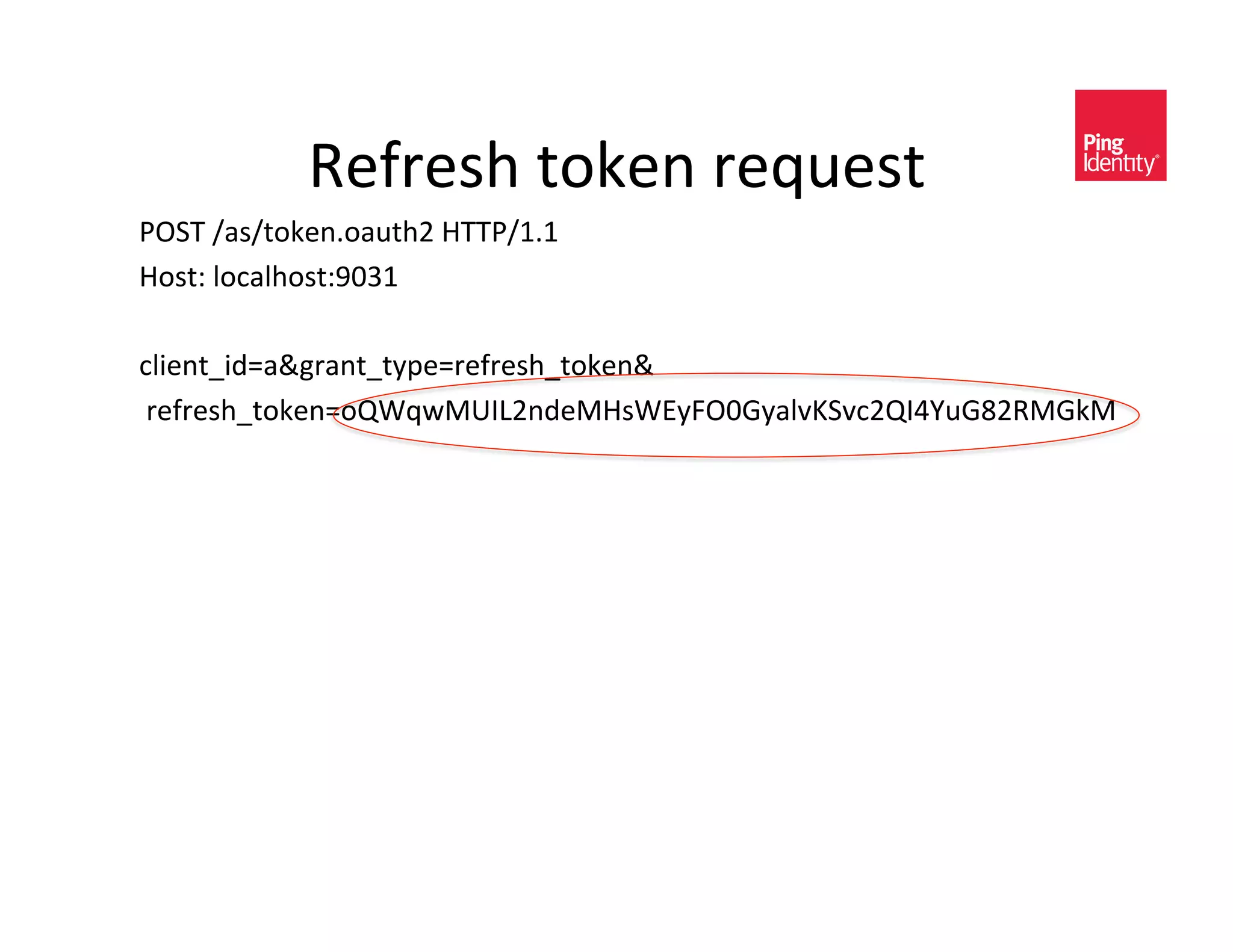
– Short lived, opaque, bearer access tokens with
long lived refresh tokens
– Cleaner separation of roles
• Server handling authorization requests
• Server handling protected resource access
• Client
– Simple Web Token (SWT)
• Attempt to standardize an access token format
• Oauth 2.0 [in progress]](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-33-2048.jpg)
![b-*)<$AE&8(AAEll&;&,(*G$&@)A0)H)&E-#&2)AA&2-/&
$%)&G;&C-*f$&%(H)&3E&$-5)*x<),/)$&40$%&3)G&
A0*)ll&>A0)*$<&%(H)&@))*&$)AA0*D&#<&68<&$%($&
-*)&2-/&E)(/<ll&
=#$&%)&)P?A(0*)C&$%($&%)&%(C&2-/D-])*&0$&($&%-3)I&
"*C&(*E4(E<K&dH-**)&($&$%)&<(A-*&$-AC&3)&$%($&
!"#$%&N6":&C-)<*f$&)H)*&/)L#0/)&,A0)*$&
<0D*($#/)<&<-&;&C-*G$&5*-4&4%E&E-#&(/)&@)0*D&<-&
w#CD)3)*$(A&p&&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-34-2048.jpg)
![9)/30*-A-DE^&8,-?)&
• 9%)&C)h*0+-*&-2&<,-?)&0<&`3-<$AEa&-#$&-2&<,-?)&
– 8))&4%($&;&C0C&$%)/)g&
– 9%)&<,-?)&-2&$%)&(,,)<<&/)L#)<$&0<&)P?/)<<)C&(<&(&A0<$&-2&
<?(,)OC)A030$)CK&,(<)&<)*<0+H)&<$/0*D<I&
– !/C)/&C-)<*f$&3(])/I&
– 9%)&H(A#)&(*C&3)(*0*D&-2&<,-?)&<$/0*D<&(/)&C)h*)C&@E&$%)&
(#$%-/01(+-*&<)/H)/I&
• 6)L#)<+*D_D/(*+*D&<?),0h,&<,-?)`<a&(AA-4<&$%)&(,,)<<&
/0D%$<&(<<-,0($)C&40$%&(&$-5)*&$-&@)&A030$)C&
– 7*(@A)<&$%)&?/0*,0?A)&-2&A)(<$&?/0H0A)D)&`-/&A)<<&?/0H0A)D)&
(*E4(Ea&
– !*AE&(<5&2-/&4%($&0<&*))C)C&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-44-2048.jpg)
![S)y*D&(*&"#$%-/01(+-*&>-C)&
4%,1$!+203$)'.";%"#,'
S79&_(<_(#$%-/01(+-*I-(#$%Ug,A0)*$x0C}(,A0)*$.&
&/)C0/),$x#/0}%]?<mY"__,A0)*$I)P(3?A)I,-3_,@.&
/%6"!<%$%#'=0)050'>0#1+)?@'A+!#,''
&&&&&&&&&/)<?-*<)x$E?)},-C).<,-?)}@))/T%-,5)ETC-*#$<&b99:_kIk&&
$B'C0)D'
b-<$^&<)/H)/I)P(3?A)I,-3&&
4%,1$!+203$)'."#6$)#"'
b99:_kIk&YZU&V-#*C&
F-,(+-*^&%]?<^__,A0)*$I)P(3?A)I,-3_,@g,-C)}S),B7C0P8o6v!tP2?>qbDsVDUb1)&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-48-2048.jpg)
![7P,%(*D)&"#$%-/01(+-*&>-C)&2-/&",,)<<&9-5)*&
4&&"##'7$8")'.";%"#,'
:!89&_(<_$-5)*I-(#$%U&b99:_kIk&
b-<$^&(<I)P(3?A)I,-3&
>-*$)*$O9E?)^&(??A0,(+-*_PO444O2-/3O#/A)*,-C)C~,%(/<)$}c9VOt&
&
,A0)*$x0C}(,A0)*$.,A0)*$x<),/)$}%-<)/./)C0/),$x#/0}%]?<mY"__,A0)*$I)P(3?A)I,-3_
,@.D/(*$x$E?)}(#$%-/01(+-*x,-C).,-C)}S),B7C0P8o6v!tP2?>qbDsVDUb1)&
4&&"##'7$8")'."#6$)#"'
b99:_kIk&UZZ&!o&
>(,%)O>-*$/-A^&*-O<$-/)&
:/(D3(^&*-O,(,%)&
>-*$)*$O9E?)^&(??A0,(+-*_w<-*~&,%(/<)$}c9VOt&
&&
&
&z$-5)*x$E?)z^z=)(/)/zK&
&z(,,)<<x$-5)*z^z(ZÄ#1JYW2J<w><9cÅ=XF3q<uN:|kPZuJ>b6{K&&
&z)P?0/)<x0*z^YÇZZK
&z/)2/)<%x$-5)*z^z389=?L|,8567>W2J,A26Jw67*3L)NÄ(?ZJ<)BÇ(q50P;q{&
É&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-49-2048.jpg)
![S)y*D&(&9-5)*&40$%&;3?A0,0$&
4%,1$!+203$)'.";%"#,'
S79&_(<_(#$%-/01(+-*I-(#$%Ug,A0)*$x0C}(,A0)*$.&
&/)C0/),$x#/0}%]?<mY"__,A0)*$I)P(3?A)I,-3_,@./)<?-*<)x$E?)}$-5)*&b99:_kIk&&
b-<$^&<)/H)/I)P(3?A)I,-3&&
4%,1$!+203$)'."#6$)#"'
b99:_kIk&YZU&V-#*C&
F-,(+-*^&%]?<^__,A0)*$I)P(3?A)I,-3_,@M)P?0/)<x0*}YÇZZ &
&.$-5)*x$E?)}=)(/)/.(,,)<<x$-5)*}D=w""2u;-ZV;24Å(qJ96|DZCuS94"!FuSÇ)&
E!$,"&,"5'."#$%!&"'.";%"#,'
S79&_C-#@A)_<),/)$_?/-@(+-*_/)<-#/,)&b99:_kIk&&
b-<$^&/<I)P(3?A)I,-3&&
"#$%-/01(+-*^&=)(/)/&D=w""2u;-ZV;24Å(qJ96|DZCuS94"!FuSÇ)&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-52-2048.jpg)
![:(/+(A&8?),0h,(+-*&F(*C<,(?)&
H"I)?'0'7$8")' 9#+)?'0'7$8")'
9%)&!"#$%&UIZ&"#$%-/01(+-*&:/-$-,-A& 9%)&!"#$%&UIZ&:/-$-,-A^&=)(/)/&9-5)*<&
C/(iO0)ÖO-(#$%OHU& C/(iO0)ÖO-(#$%OHUO@)(/)/&
b99:&"#$%)*+,(+-*^&B">&",,)<<&"#$%)*+,(+-*&
C/(iO0)ÖO-(#$%OHUO%]?O3(,&
7P$)*<0-*&S/(*$<&&
.& !"#$%&UIZ&"<<)/+-*&:/-hA)&&&&&&&&&&&&&&&&&&&&&&
&>A0)*$&"#$%)*+,(+-*& C/(iO0)ÖO-(#$%O(<<)/+-*<&
7$8")#' "<<)/+-*<&(*C&:/-$-,-A<&2-/&8"BF&ÄUIZ&
<(3AO,-/)OUIZO-<&
8"BF&UIZ&=)(/)/&"<<)/+-*&S/(*$&&
9E?)&:/-hA)&2-/&!"#$%&UIZ&
C/(iO0)ÖO-(#$%O<(3AUO@)(/)/& JKLMN'
v8!W&N)@&9-5)*&`vN9a&&
v8!W&N)@&9-5)*&`vN9a&=)(/)/& C/(iOw-*)<Ow<-*O4)@O$-5)*&
:/-hA)&2-/&!"#$%&UIZ&
&C/(iOw-*)<O-(#$%Ow4$O@)(/)/&
v8!W&N)@&80D*($#/)&`vN8a&
C/(iOw-*)<Ow<-*O4)@O<0D*($#/)&
O,1"!'E!$,$&$*#'
c<)/OB(*(D)C&",,)<<&`cB"a& v8!W&N)@&80D*($#/)&`vN7a&
>-/)&:/-$-,-A& C/(iOw-*)<Ow<-*O4)@O)*,/E?+-*&
!?)*;J&>-**),$&>-/)&kIZ& C/(iO%(/Cw-*-O-(#$%O#3(,-/)&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-59-2048.jpg)

![d";Ä&`d)$&"*-$%)/&;C)*+$E&Ä)**a&
!"#$%&
8"BF&
• 88!&?/-hA)&
• ;>"B&
• "#$%*&2-/&8!":&":;<& • "#$%*&2-/&6789&":;<&
• 9-5)*&2-/3($& • "]/0@#$)&<%(/0*D&
&
• >A-#C&"#$%1&
• "#$%1&C),0<0-*<&
• "#$%1&|#)/En&
• :-A0,E&<E*$(P&
q">BF&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-62-2048.jpg)
,(#<)&-2&(<<)/+-*&C0<,A-<#/)&($&
@/-4<)/&
• ;3?A)3)*$(+-*&,-3?A)P0$E&
– J0[)Ob)A3(*&5)E&)P,%(*D)K&>(*-*0,(A01(+-*&(*C&
80D*($#/)&%(/C&$-&03?A)3)*$&
• J($(&8%(/0*D&F030$(+-*<&
– !*AE&?(0/O40<)&C($(&<%(/0*D&@)$4))*&$%)&!:&(*C&6:&0<&
?-<<0@A)I&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-64-2048.jpg)
![9/(C0*D&
Use SAML assertion( or JWT) for
OAuth client authentication and/or OAuth grant type
:!89&_$-5)*&b99:_kIk&
b-<$^&<)/H)/I)P(3?A)I,-3&
>-*$)*$O9E?)^&(??A0,(+-*_PO444O2-/3O#/A)*,-C)C&
&
D/(*$x$E?)}(#$%-/01(+-*x,-C).&,-C)}0kN<6*k#=k.&,A0)*$x0C}<Ç=%C65L$Y.&
,A0)*$x(<<)/+-*x$E?)}#/*mY"-(<0<mY"*(3)<m<"$,mY"8"BF
mY"UIZmY"(<<)/+-*.&,A0)*$x(<<)/+-*}:bW%@NP4!AIIIÜ-30])C&2-/&
@/)H0$EáIIIÅ9&
&
&
&
&
&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-71-2048.jpg)
![9/(C0*D&
&
8"BF& vN9& :/-hA)<&(<<)/+-*&?/-hA)&
V-/&<?),0h,&(<<)/+-*&
V-/3($<&ÜUá&.&ÜYá&
"<<)/+-*&?/-hA)& b-4&$-&#<)&(<<)/+-*<&&
2-/&,A0)*$&(#$%)*+,(+-*&&
(*C&(<&(&D/(*$&$E?)&Üká&&
!"#$%& >-/)&?/-$-,-A&
Üká&O&%]?^__$--A<I0)ÖI-/D_%$3A_C/(iO0)ÖO-(#$%O(<<)/+-*<&
ÜUá&O&C/(iO0)ÖO-(#$%O<(3AUO@)(/)/&
ÜYáO&C/(iO0)ÖO-(#$%Ow4$O@)(/)/&
&
&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-72-2048.jpg)
![!"#$%&c<)&>(<)^&B-@0A)&>-*<#3)/&
• "&>-*<#3)/&>A-#C&=#<0*)<<&`)IDI&B(//0-]a&@#0AC0*D&
B-@0A)&"??<&
• :/-H0C)&88!&(,,)<<&H0(&0:(CK&0:%-*)K&"*C/-0CK&)$,&
• 9/#<$&/)A(+-*<%0?&0<&@)$4))*&)*$)/?/0<)&.&
,-*<#3)/&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-81-2048.jpg)
![B-@0A)&>-*<#3)/^&&8?),0h,<&
ka&B-@0A)&(??A0,(+-*&A(#*,%)<&
S' "#$%Å& @/-4<)/K&0*&4%0,%&#<)/&
V'
7*C?-0*$& (#$%)*+,($)<&$-&:0*DV)C)/($)&
`(*C&D/(*$<&,-*<)*$a&&&
9-5)*&
7*C?-0*$& Ua&:0*DV)C)/($)&/)$#/*<&,-C)&$-&
3-@0A)&(??A0,(+-*&$%/-#D%&
Ä(A0C(+-*&
@/-4<)/&
W' 7*C?-0*$&
Ya&B-@0A)&(??A0,(+-*&)P,%(*D)<&,-C)&
2-/&(,,)<<&$-5)*&
Ra&B-@0A)&(??A0,(+-*&(CC<&(,,)<<&
['
$-5)*&$-&0$<&6789&/)L#)<$&-2&
6)<-#/,)&8)/H)/&`":;a&
' Xa&68&0*$)/(,$<&40$%&:0*DV)C)/($)&$-&
H)/02E&$-5)*K&(*C&/)$/0)H)&C)<0/)C&
68& (]/0@#$)<&
Ça&"<<#30*D&!oK&68&/)$#/*<&
/)L#)<$)C&C($(&$-&3-@0A)&
(??A0,(+-*&
Z'](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-82-2048.jpg)
![B-@0A)&>-*<#3)/<^&;*A0*)&-?+-*&
ka&B-@0A)&(??A0,(+-*&,-AA),$<&#<)/&
?(<<4-/C&(*C&<)*C<&$-&
"#$%Å& :0*DV)C)/($)&0*&/)L#)<$&2-/&
7*C?-0*$&
(,,)<<&$-5)*a&&&
S' 9-5)*& Ua&:0*DV)C)/($)&/)$#/*<&(,,)<<&$-5)*&
7*C?-0*$& $-&3-@0A)&(??A0,(+-*&
V'
Ya&B-@0A)&(??A0,(+-*&(CC<&(,,)<<&
Ä(A0C(+-*&
7*C?-0*$& $-5)*&$-&0$<&6789&/)L#)<$&-2&
6)<-#/,)&8)/H)/&`":;a&
Ra&68&0*$)/(,$<&40$%&:0*DV)C)/($)&$-&
W'
Z' H)/02E&$-5)*K&(*C&/)$/0)H)&
C)<0/)C&(]/0@#$)<&
Xa&"<<#30*D&!oK&68&/)$#/*<&
/)L#)<$)C&C($(&$-&3-@0A)&
(??A0,(+-*&
['
68&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-83-2048.jpg)
![B-@0A)&>A-#C&
ka&B-@0A)&(??A0,(+-*&A(#*,%)<&
;C:& @/-4<)/&$-&:0*DV)C)/($)&(#$%*&
V'
?(D)&
"#$%Å&
V'
7*C?-0*$& &Ua&:0*DV)C)/($)&<)*C<&)3?A-E))&
S'
@/-4<)/&$-&)*$)/?/0<)&;C:&2-/&88!K&
9-5)*& /),)0H)<&8"BF&(<<)/+-*&
7*C?-0*$&
W' Ya&:0*DV)C)/($)&/)$#/*<&,-C)&$-&
Ä(A0C(+-*& 3-@0A)&(??A0,(+-*&$%/-#D%&
W' Z' 7*C?-0*$& @/-4<)/&
Ra&B-@0A)&(??A0,(+-*&)P,%(*D)<&,-C)&
2-/&(,,)<<&$-5)*&
'
Xa&B-@0A)&(??A0,(+-*&(CC<&(,,)<<&
$-5)*&$-&0$<&6789&/)L#)<$&-2&
]' 6)<-#/,)&8)/H)/&`":;a&
Ça&68&0*$)/(,$<&40$%&:0*DV)C)/($)&$-&
68& H)/02E&$-5)*K&(*C&/)$/0)H)&C)<0/)C&
(]/0@#$)<&
ua&"<<#30*D&!oK&68&/)$#/*<&
/)L#)<$)C&C($(&$-&3-@0A)&
[' (??A0,(+-*&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-86-2048.jpg)
![;*$)/*(A&":;<^&O&"#$-*-3-#<&
kI ;*$)/*(A&,A0)*$&(#$%)*+,($)<&$-&
:0*DV)C)/($)&-*&/)L#)<$&2-/&
"#$%Å& (,,)<<&$-5)*&
7*C?-0*$&
UI :0*DV)C)/($)&/)$#/*<&(,,)<<&
S' 9-5)*& $-5)*&$-&,A0)*$&
7*C?-0*$&
YI B-@0A)&(??A0,(+-*&(CC<&(,,)<<&
V'
$-5)*&$-&0$<&6789&/)L#)<$&-2&
Ä(A0C(+-*&
7*C?-0*$& 6)<-#/,)&8)/H)/&`":;a&
RI 68&0*$)/(,$<&40$%&:0*DV)C)/($)&
$-&H)/02E&$-5)*K&(*C&/)$/0)H)&
W'
Z' (??/-?/0($)&,A0)*$&(]/0@#$)<&
XI "<<#30*D&!oK&68&/)$#/*<&
/)L#)<$)C&C($(&$-&,A0)*$&
(??A0,(+-*&
['
68&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-88-2048.jpg)
![;*$)/*(A&":;<^&&O&J)A)D($)C&
kI >A0)*$&(??A0,(+-*&A(#*,%)<&
S' @/-4<)/&$-&:0*DV)C)/($)&(#$%*&
"#$%Å& ?(D)&
7*C?-0*$&
UI &"i)/&A-D0*K&:0*DV)C)/($)&
V' 9-5)*& /)$#/*<&,-C)&$-&,A0)*$&
7*C?-0*$& (??A0,(+-*&$%/-#D%&@/-4<)/&
V'
YI >A0)*$&(??A0,(+-*&)P,%(*D)<&
Ä(A0C(+-*&
7*C?-0*$& ,-C)&2-/&(,,)<<&$-5)*&
RI >A0)*$&(??A0,(+-*&(CC<&(,,)<<&
$-5)*&$-&0$<&6789&/)L#)<$&-2&
[' 6)<-#/,)&8)/H)/&`":;a&
W'
XI 68&0*$)/(,$<&40$%&:0*DV)C)/($)&
$-&H)/02E&$-5)*K&(*C&/)$/0)H)&
C)<0/)C&(]/0@#$)<&
Z'
68& ÇI "<<#30*D&!oK&68&/)$#/*<&
/)L#)<$)C&C($(&$-&,A0)*$&
(??A0,(+-*&
'](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-89-2048.jpg)
![VA-4&
kI >A0)*$&(??A0,(+-*&/)$/0)H)<&8"BF&
(<<)/+-*&2/-3&A-,(A&;C:&
UI >A0)*$&<)*C<&8"BF&(<<)/+-*&$-&
:0*DV)C)/($)&($&8((8&:/-H0C)/_
?(/$*)/&)$,&
YI :0*DV)C)/($)&/)$#/*<&(,,)<<&
$-5)*&$-&,A0)*$&
RI >A0)*$&(??A0,(+-*&(CC<&(,,)<<&
$-5)*&$-&0$<&6789&/)L#)<$&-2&
6)<-#/,)&8)/H)/&`":;a&
XI 8((8&68&0*$)/(,$<&40$%&
:0*DV)C)/($)&$-&H)/02E&$-5)*K&
(*C&/)$/0)H)&C)<0/)C&(]/0@#$)<&
ÇI "<<#30*D&!oK&8((8&68&/)$#/*<&
/)L#)<$)C&C($(&$-&,A0)*$&
(??A0,(+-*&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-91-2048.jpg)
![88!&6)L#)<$&
à2-/3&3)$%-C}z?-<$z&(,+-*}z%]?<^__0C?I)P(3?A)I-/D_8"BFU_88!_:!89z&â&
à0*?#$&$E?)}z%0CC)*z&*(3)}z8"BF6)L#)<$z&H(A#)}z!"#$"%&z&_â&
à0*?#$&$E?)}z<#@30$z&H(A#)}z8#@30$z&_â&
à_2-/3â&&
à<(3A?^"#$%*6)L#)<$&
&P3A*<^<(3A?}z#/*^-(<0<^*(3)<^$,^8"BF^UIZ^?/-$-,-Az&
P3A*<^<(3A}z#/*^-(<0<^*(3)<^$,^8"BF^UIZ^(<<)/+-*z&;J}z((2UYksÇOkuuYOUkkYORuR(O
2)kkRRkU(@uUz&Ä)/<0-*}zUIZz&;<<#);*<$(*$}zUZZROkUOZX9Zs^Uk^XsÅ{â&
& &à<(3A^;<<#)/â%]?<^__<?I)P(3?A)I,-3_8"BFUà_<(3A^;<<#)/â&&à<(3A?^W(3);J:-A0,E&
"AA-4>/)($)}z$/#)z& &V-/3($}z#/*^-(<0<^*(3)<^$,^8"BF^
UIZ^*(3)0C^2-/3($^?)/<0<$)*$z_â&
à_<(3A?^"#$%*6)L#)<$â&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-110-2048.jpg)
![88!&6)<?-*<)&
à<(3A^"<<)/+-*â&
à<(3A^;<<#)/â%]?<^__0C?I)P(3?A)I-/D_8"BFUà_<(3A^;<<#)/â&
àC<^80D*($#/)&P3A*<^C<}z%]?^__444I4YI-/D_UZZZ_Zs_P3AC<0DMzâIIIà_C<^80D*($#/)â&
à<(3A^8#@w),$â&à<(3A^W(3);J&V-/3($}z#/*^-(<0<^*(3)<^$,^8"BF^UIZ^*(3)0CO2-/3($^?)/<0<$)*$zâ&
Y2u@YC,2OkÇuROR),COsU,tOkXRR2YRÇ@(2t&à_<(3A^W(3);Jâà_<(3A^8#@w),$â&
à<(3A^"]/0@#$)8$($)3)*$â&
à<(3A^"]/0@#$)&W(3)}Ñ)3(0A{&â&
à<(3A^"]/0@#$)Ä(A#)&P<0^$E?)}zP<^<$/0*Dzâ?3(C<)*?0*D0C)*+$EI,-3à_<(3A^"]/0@#$)Ä(A#)â&&
à_<(3A^"]/0@#$)â&&
à_<(3A^"]/0@#$)8$($)3)*$â&&
à_<(3A^"<<)/+-*â&&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-116-2048.jpg)

![>A0)*$&,(AA<&":;&
%]?<^__D/(?%I2(,)@--5I,-3_?(#AI)I3(C<)*_
2/0)*C<_g
(,,)<<x$-5)*}A8=@,0RvDtB<w08LÅF=/17qDCR3o
cW%!5EV&
&
&
&
&
&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-125-2048.jpg)
![S)$&2/)<%&(]/0@#$)<&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-136-2048.jpg)
![S)$&2/)<%&(]/0@#$)<&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-137-2048.jpg)
![S)$&2/)<%&(]/0@#$)<&
8>;B&-/&8"BFgg&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-138-2048.jpg)
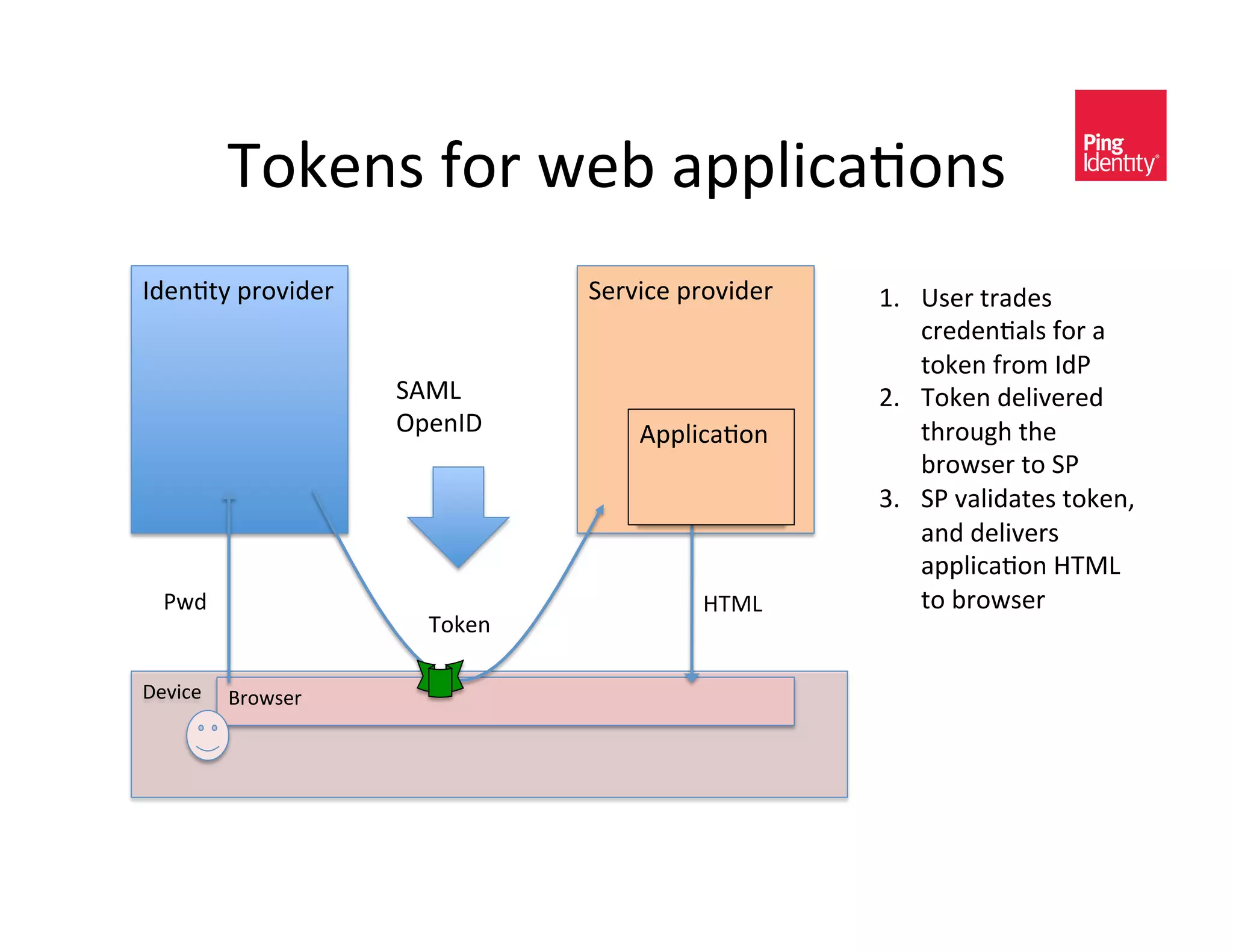
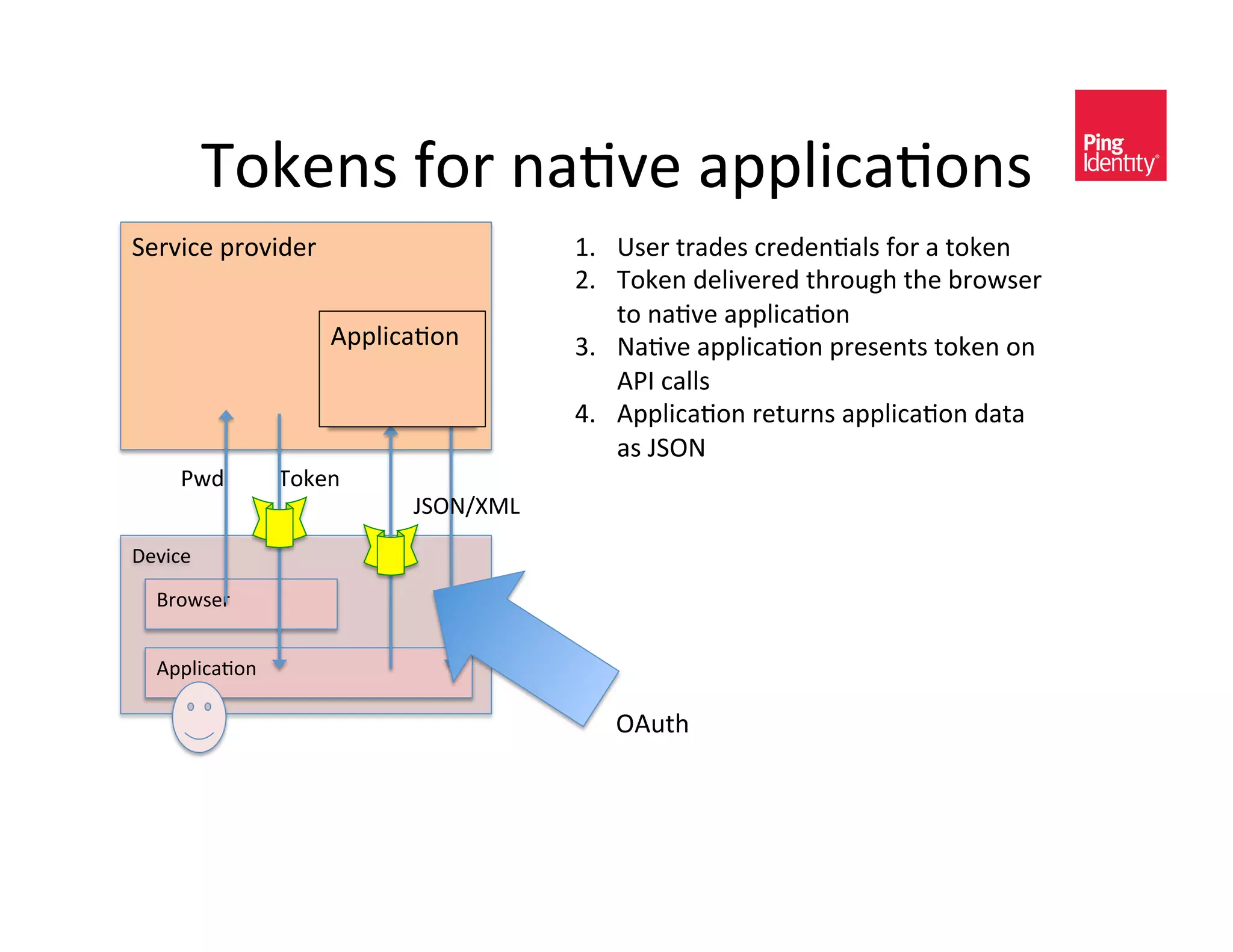
![9-5)*<&
• V)C)/($)C&(#$%)*+,(+-*&2-/&@-$%&4)@&(*C&
*(+H)&3-@0A)&(??A0,(+-*<&0<&@(<)C&-*&)P,%(*D)&
(*C&C)A0H)/E&-2&&'(")%*$-&$%)&(??A0,(+-*&
• 9-5)*<&,(//E&`-/&?-0*$&$-a&<),#/0$E&0*2-/3(+-*&
`A05)&(]/0@#$)<&-/&(#$%-/01(+-*<a&2-/&#<)/&$/E0*D&
$-&(,,)<<&$%)&(??A0,(+-*I&&
• >A0)*$<&$E?0,(AAE&)P,%(*D)&,/)C)*+(A<&2-/&$-5)*<&
O&)(<0)/_<(2)/&$-&<%(/)&$%)&$-5)*&(,/-<<&$%)&
*)$4-/5&/($%)/&$%(*&$%)&-/0D0*(A&,/)C)*+(A<&
• N%)*&$-5)*&0<&<#@<)L#)*$AE&?/)<)*$)C&$-&(*&
(??A0,(+-*&?/-H0C)/K&$%)E&<)/H)&$-&(#$%)*+,($)&
(*C_-/&(#$%-/01)&$%)&/)L#)<$&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-147-2048.jpg)
![V)C)/(+-*&$(5)<&C0e)/)*$&2-/3<&
V-/&4)@&(??<K&$-5)*<&,(//E&
=/-4<)/& (??&
"]/0@#$)<&2-/&(#$%)*+,(+-*&
V-/&*(+H)&(??<K&$-5)*<&,(//E&
(??& C($(&
"#$%-/01(+-*&2-/&(]/0@#$)<&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-148-2048.jpg)
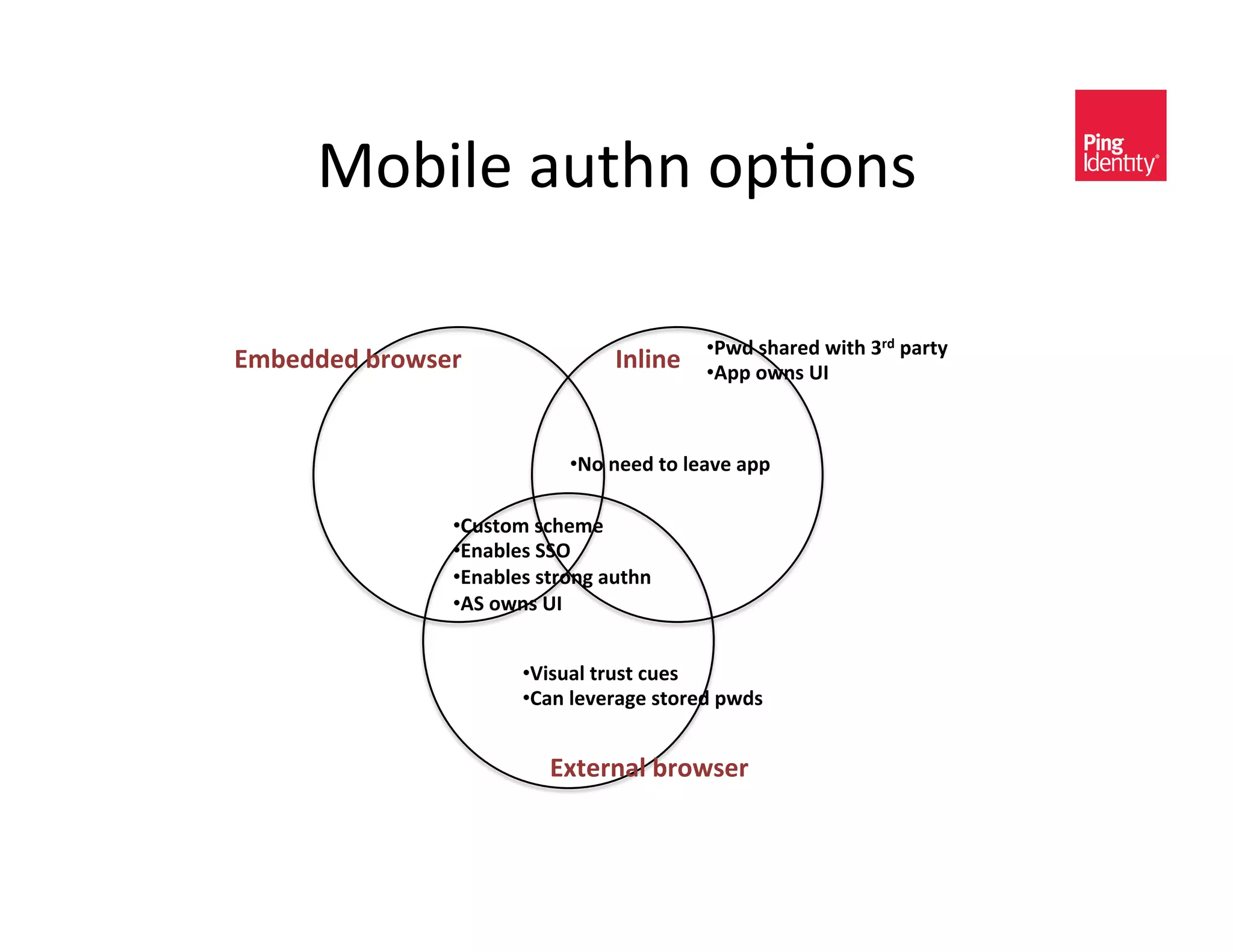
![9-5)*<&2-/&3-@0A)&4)@&(??A0,(+-*<&
• V)C)/(+-*&2-/&4)@&(??A0,(+-*<&3(*02)<$<&(<&
88!&2/-3&<-3)&;C:&$-&$%)&(??A0,(+-*&?/-H0C)/&
• 88!&)<?),0(AAE&/)A)H(*$&2-/&3-@0A)&
• 9-5)*<&(])<+*D&$-&$%)&#<)/f<&0C)*+$E&(*C_-/&
(#$%)*+,(+-*&<$($#<&C)A0H)/)C&&+!'$,+*`(<&
/)C0/),$<a&$%)&@/-4<)/&2/-3&;C:&$-&$%)&
(??A0,(+-*&?/-H0C)/&
• "??A0,(+-*&?/-H0C)/&H(A0C($)<&$-5)*&(*C&
)P$/(,$<&0C)*+$E&(]/0@#$)<&2/-3&40$%0*&0*&-/C)/&
$-&,/)($)&A-,(A&<)<<0-*&&](https://image.slidesharecdn.com/cis-oauth-workshop-110722072613-phpapp02/75/OAuth-101-Secure-API-s-Paul-Madsen-and-Brian-Campbell-Ping-Identity-149-2048.jpg)