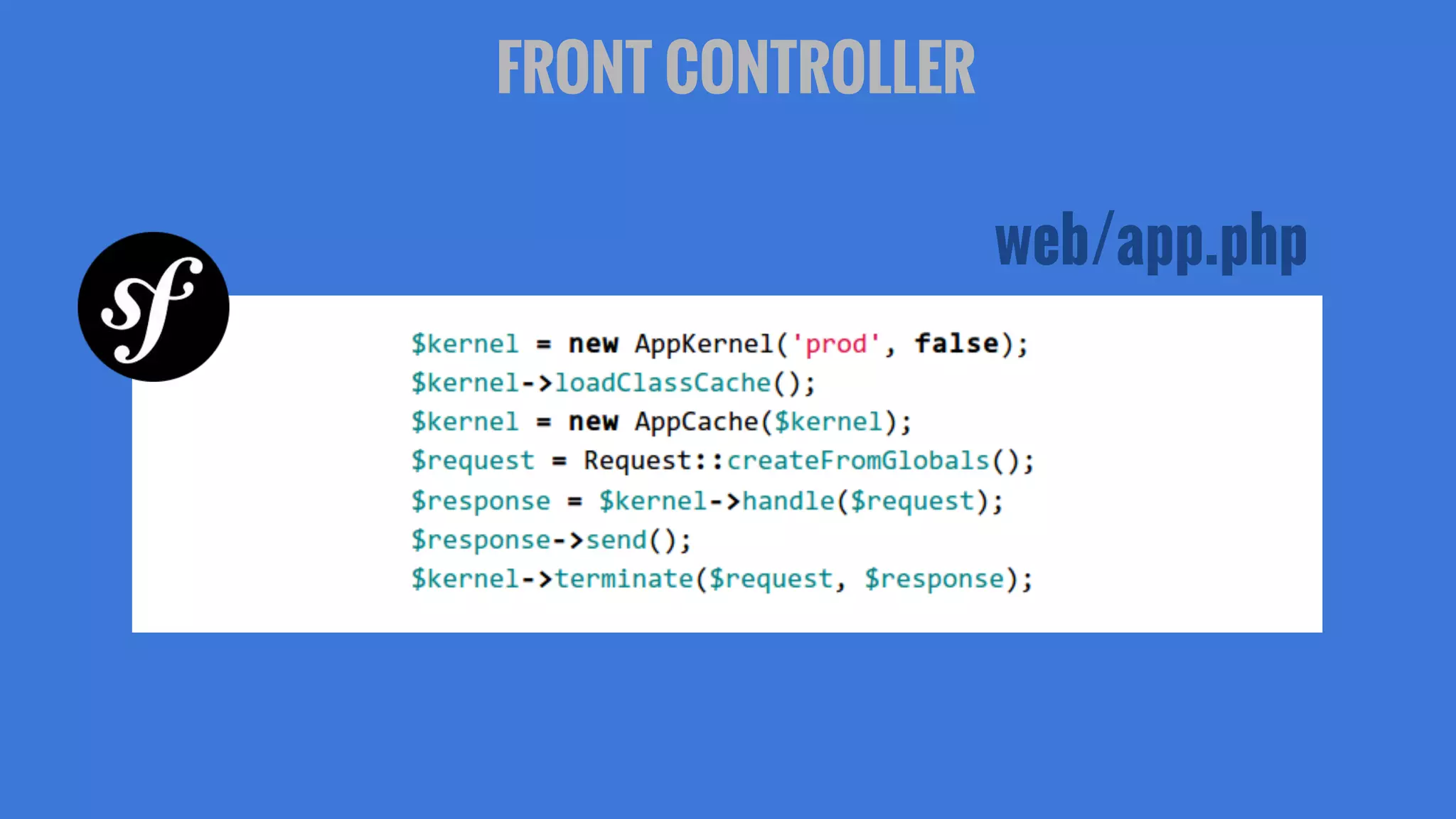
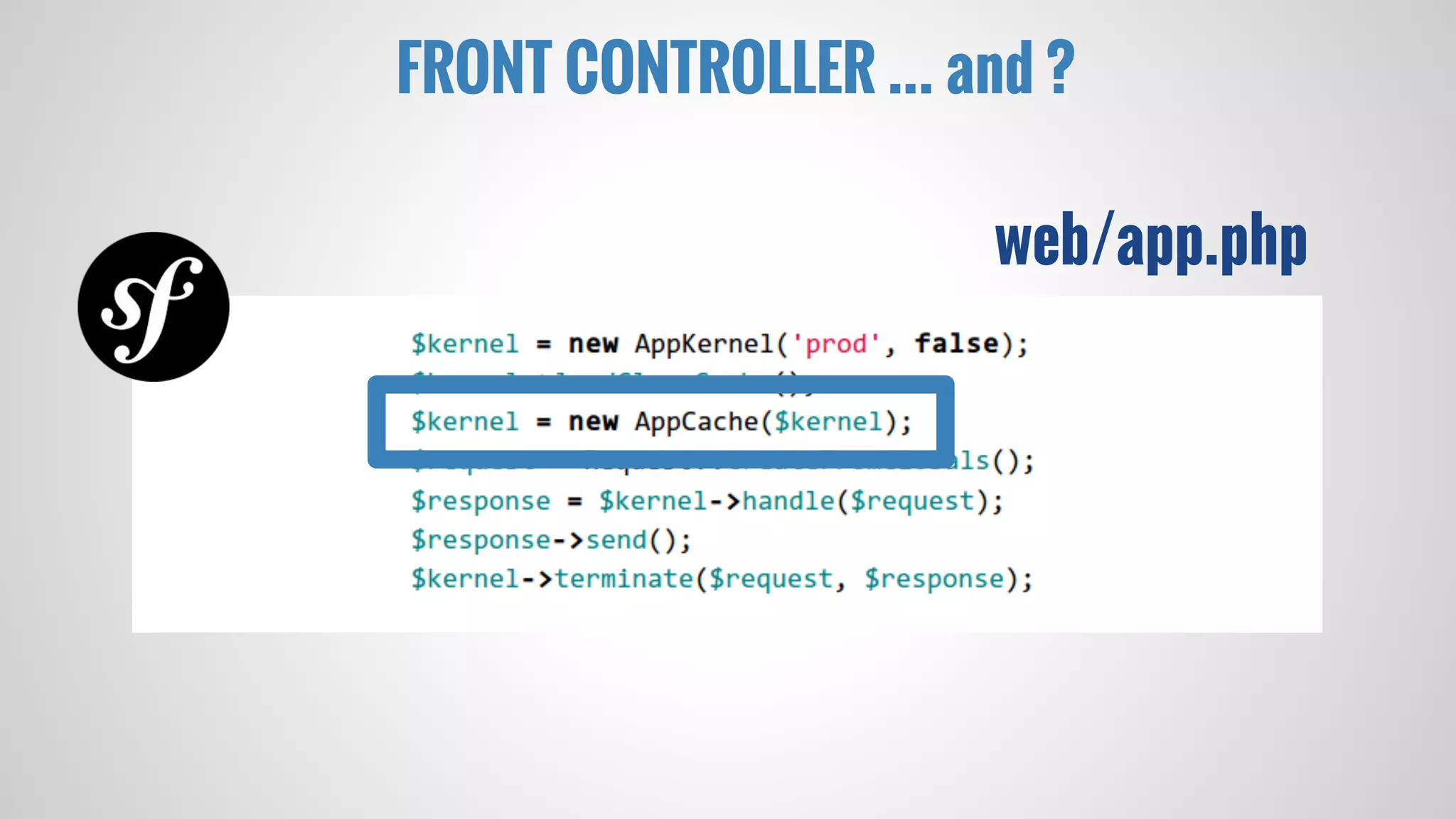
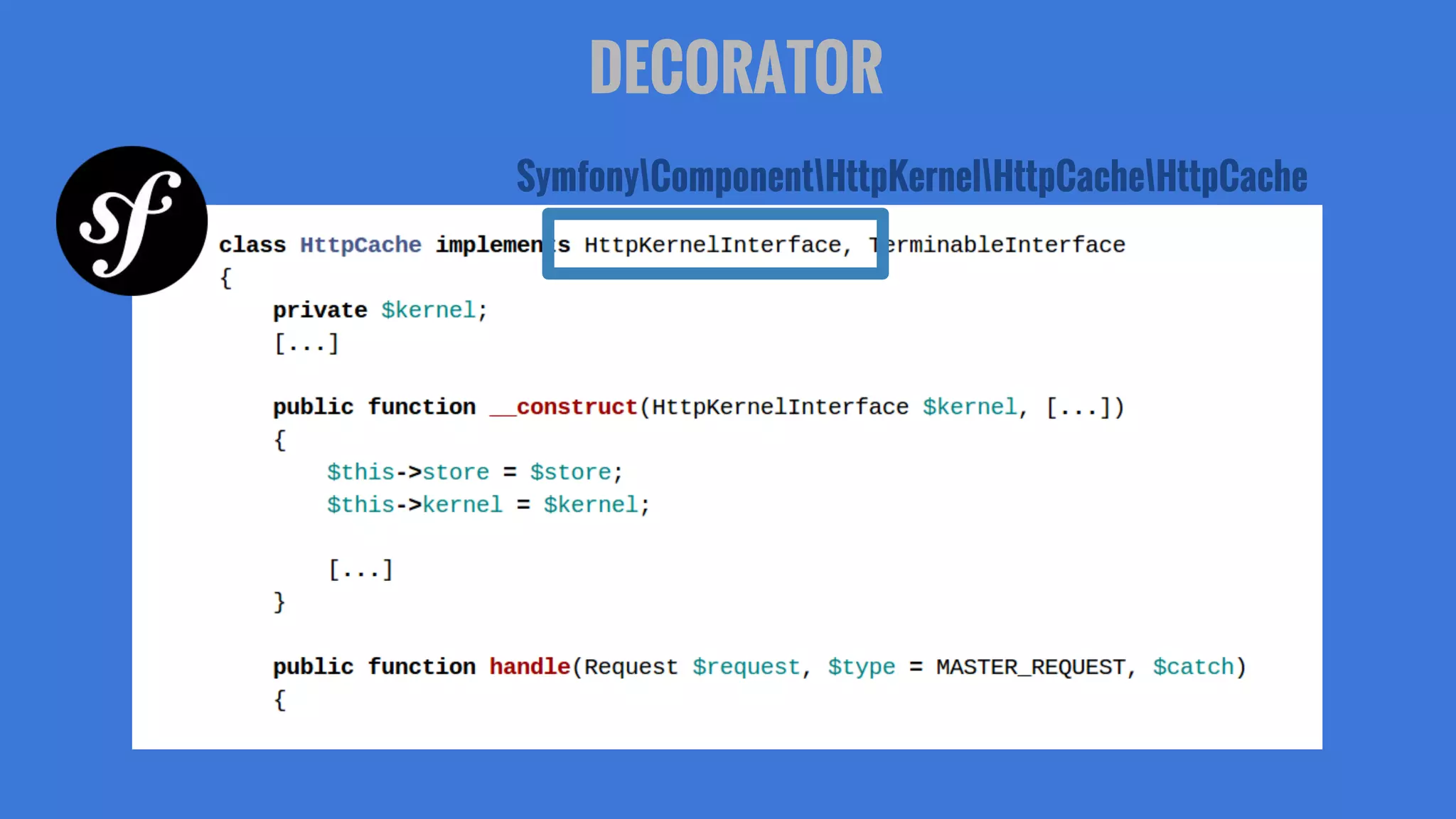
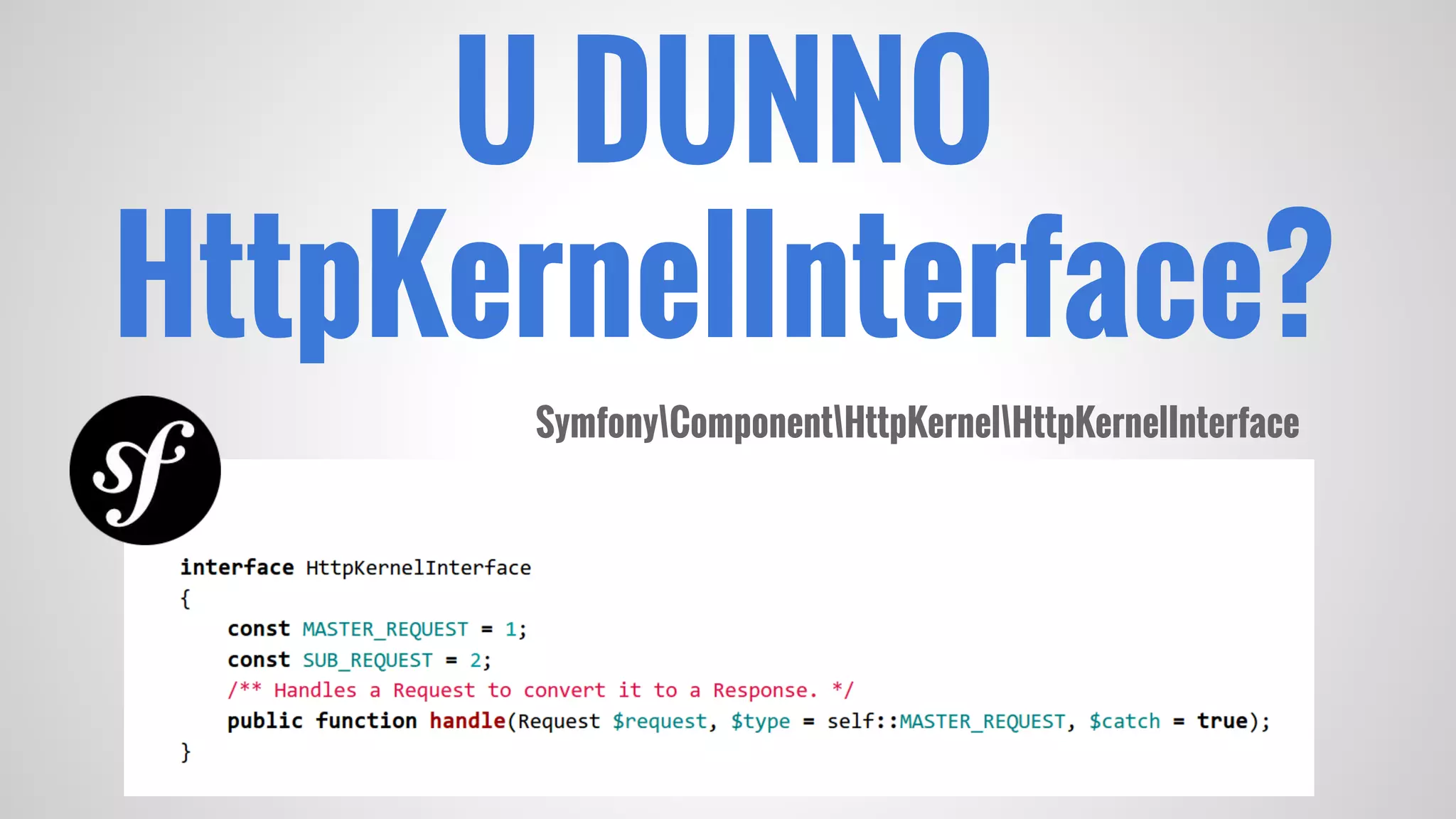
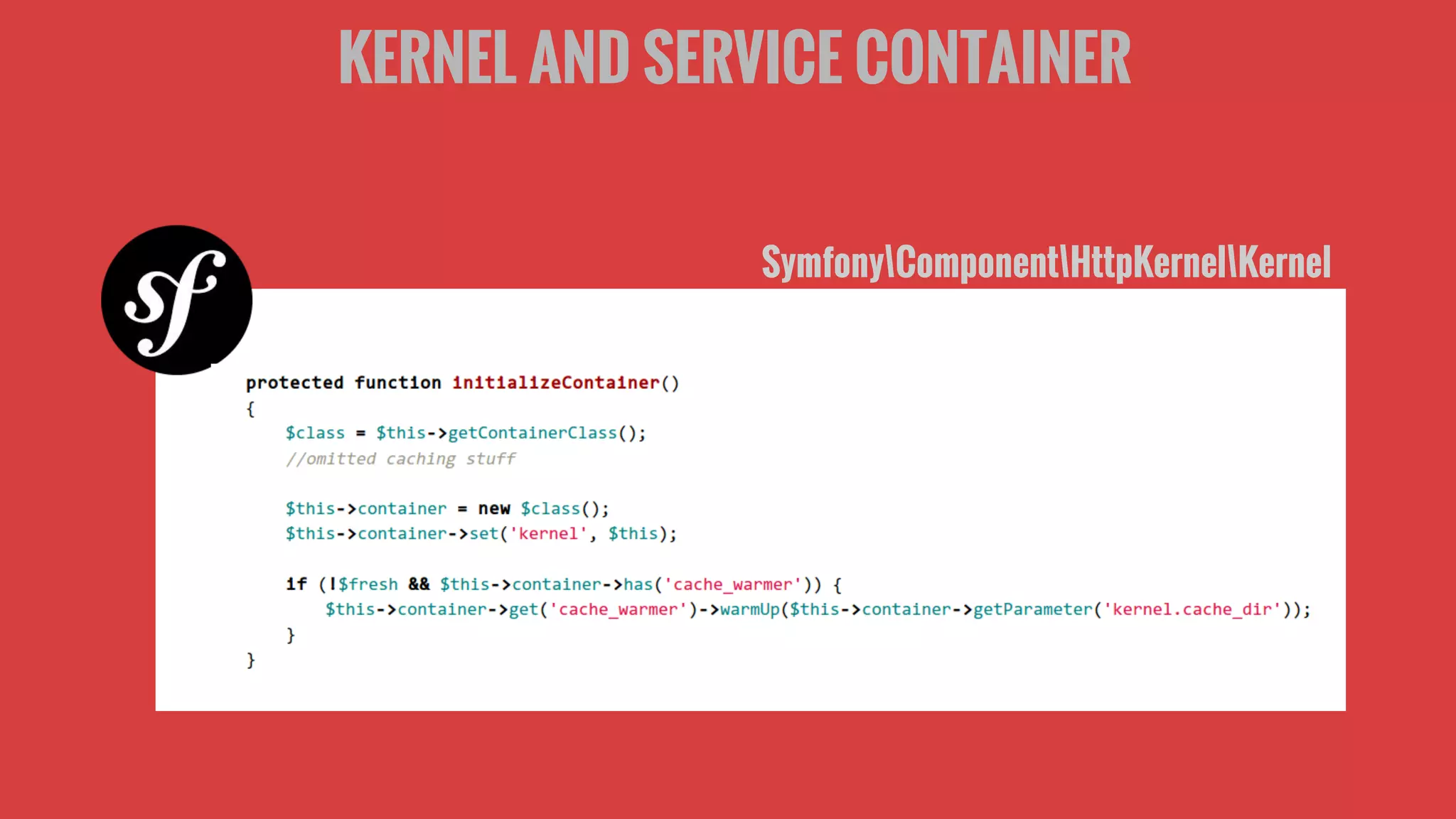
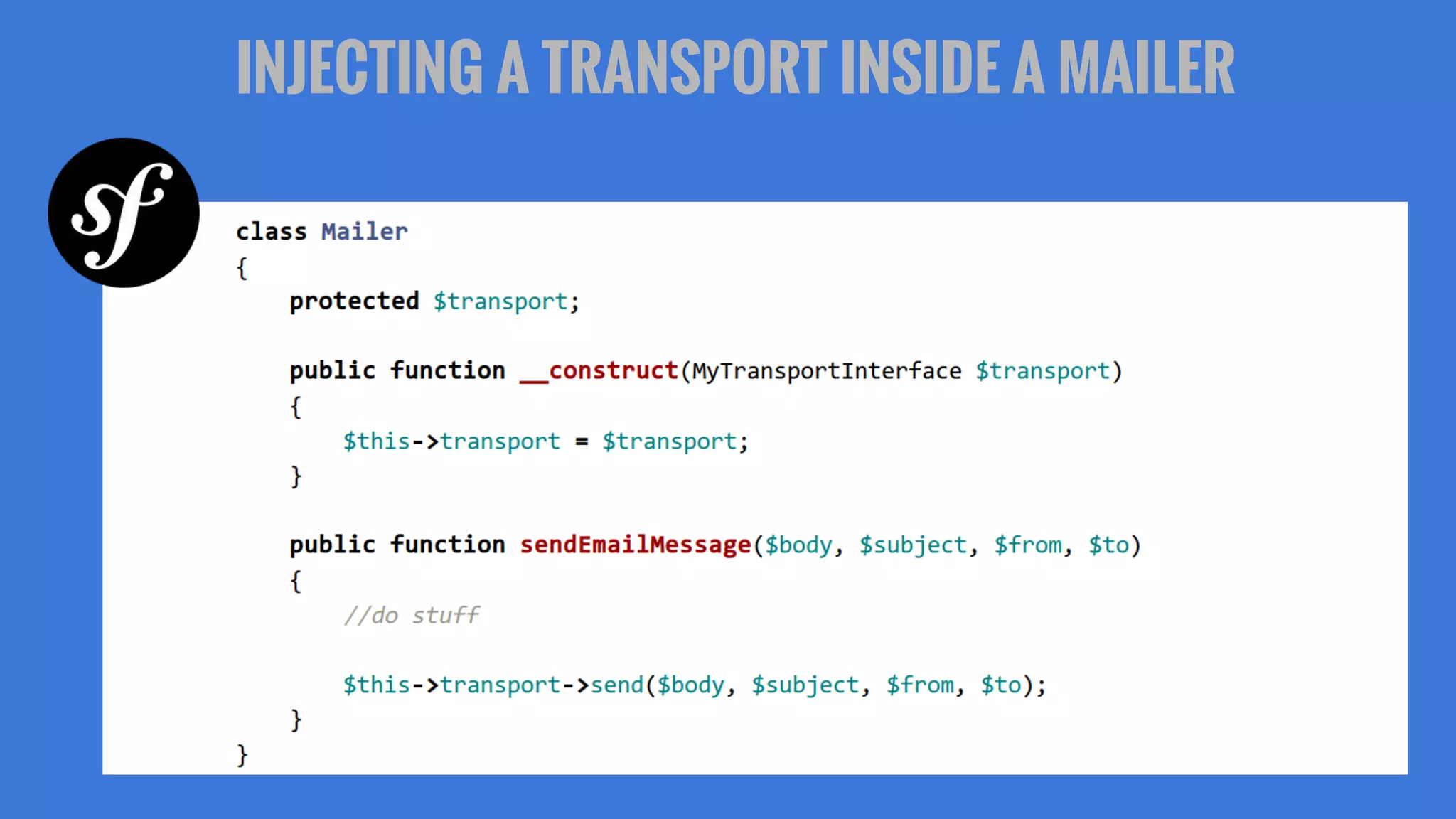
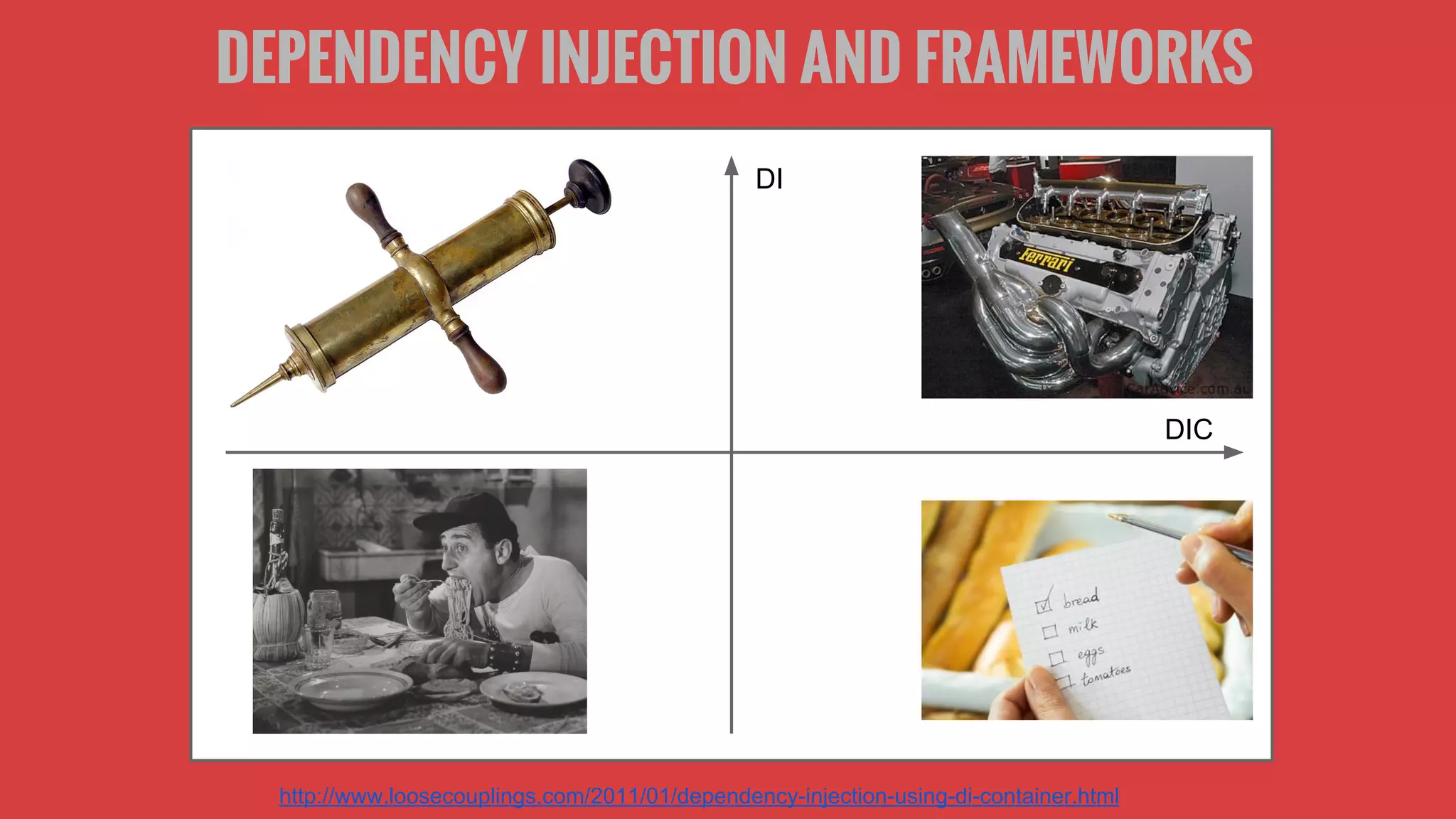
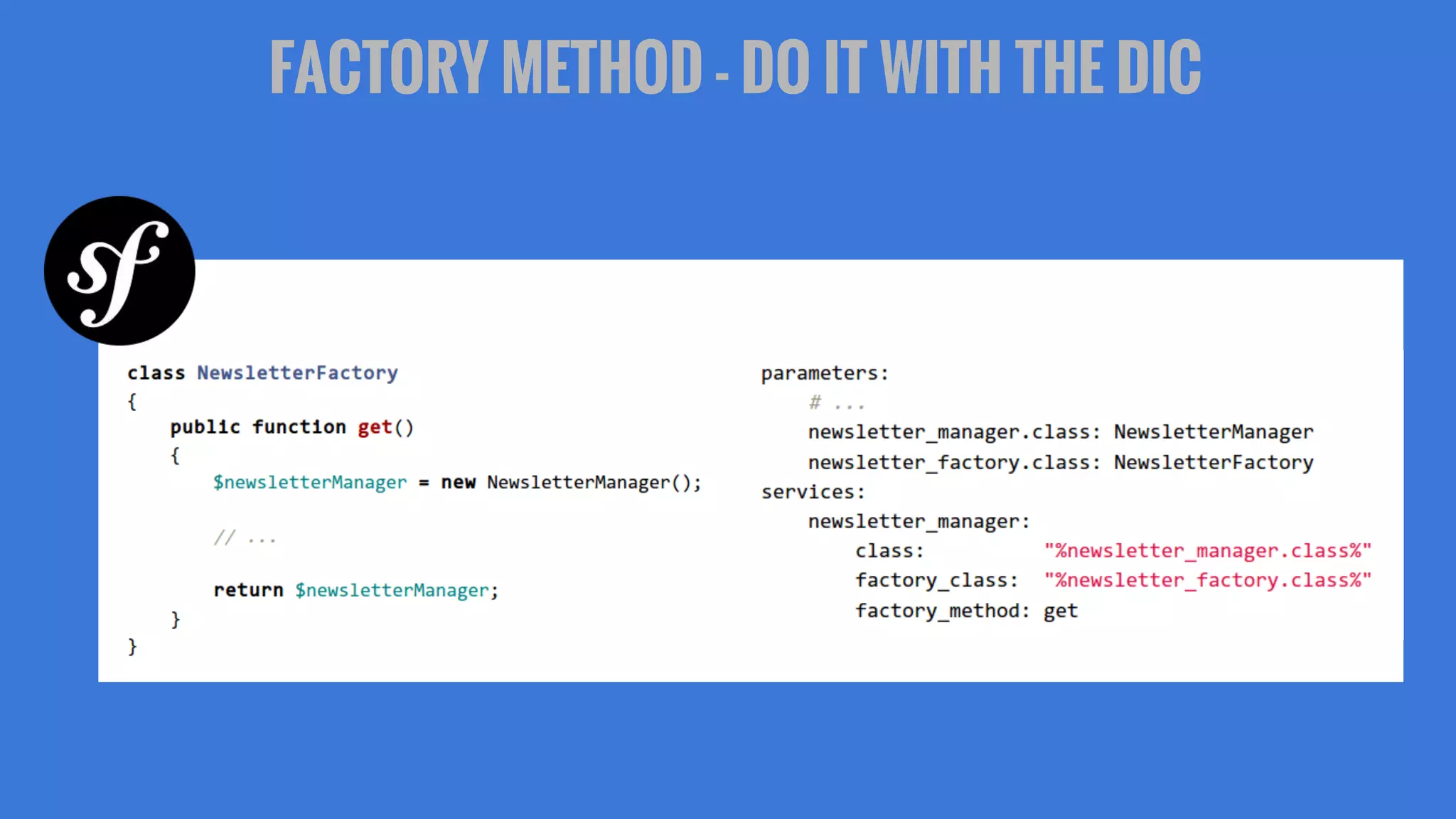
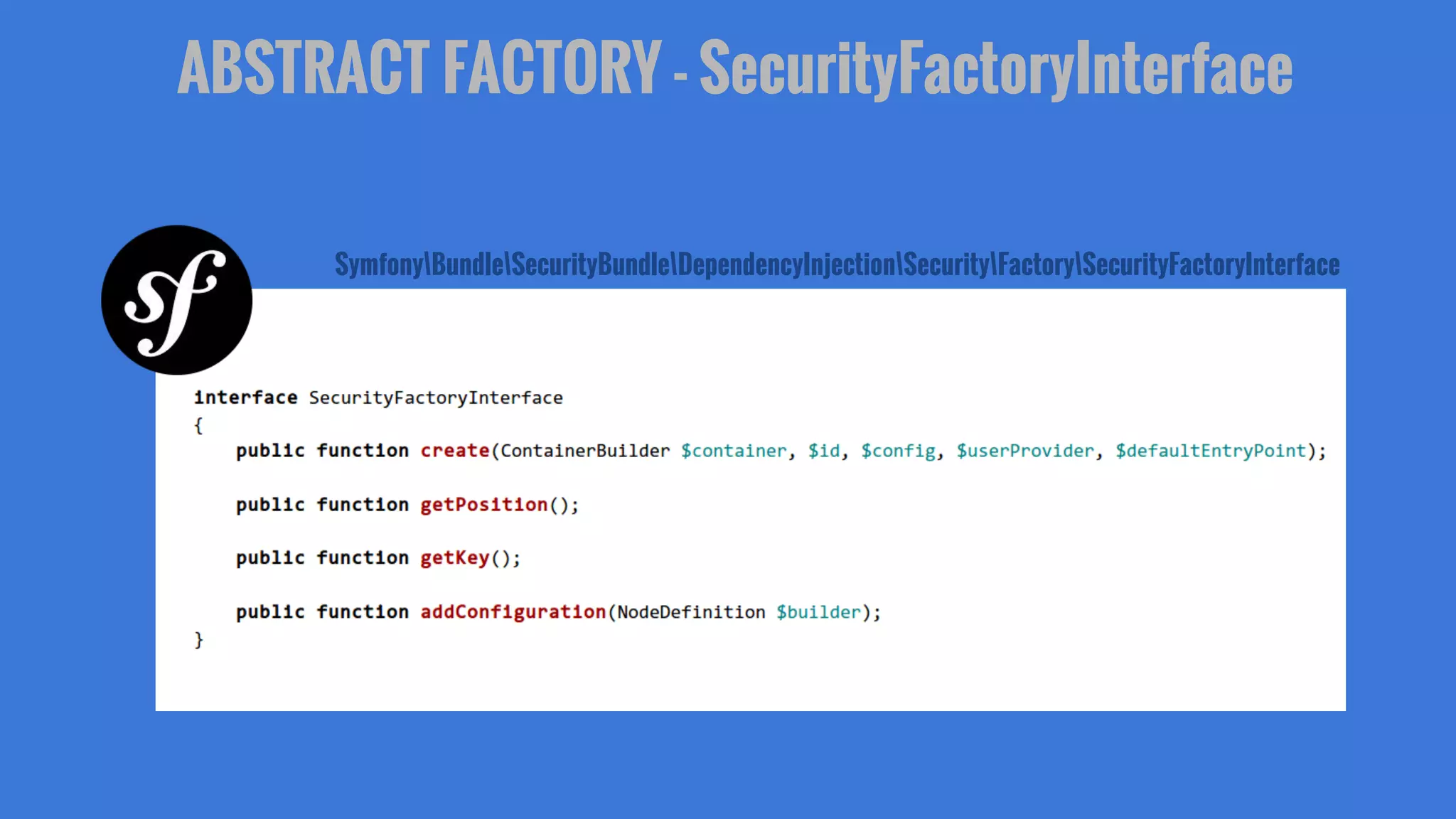
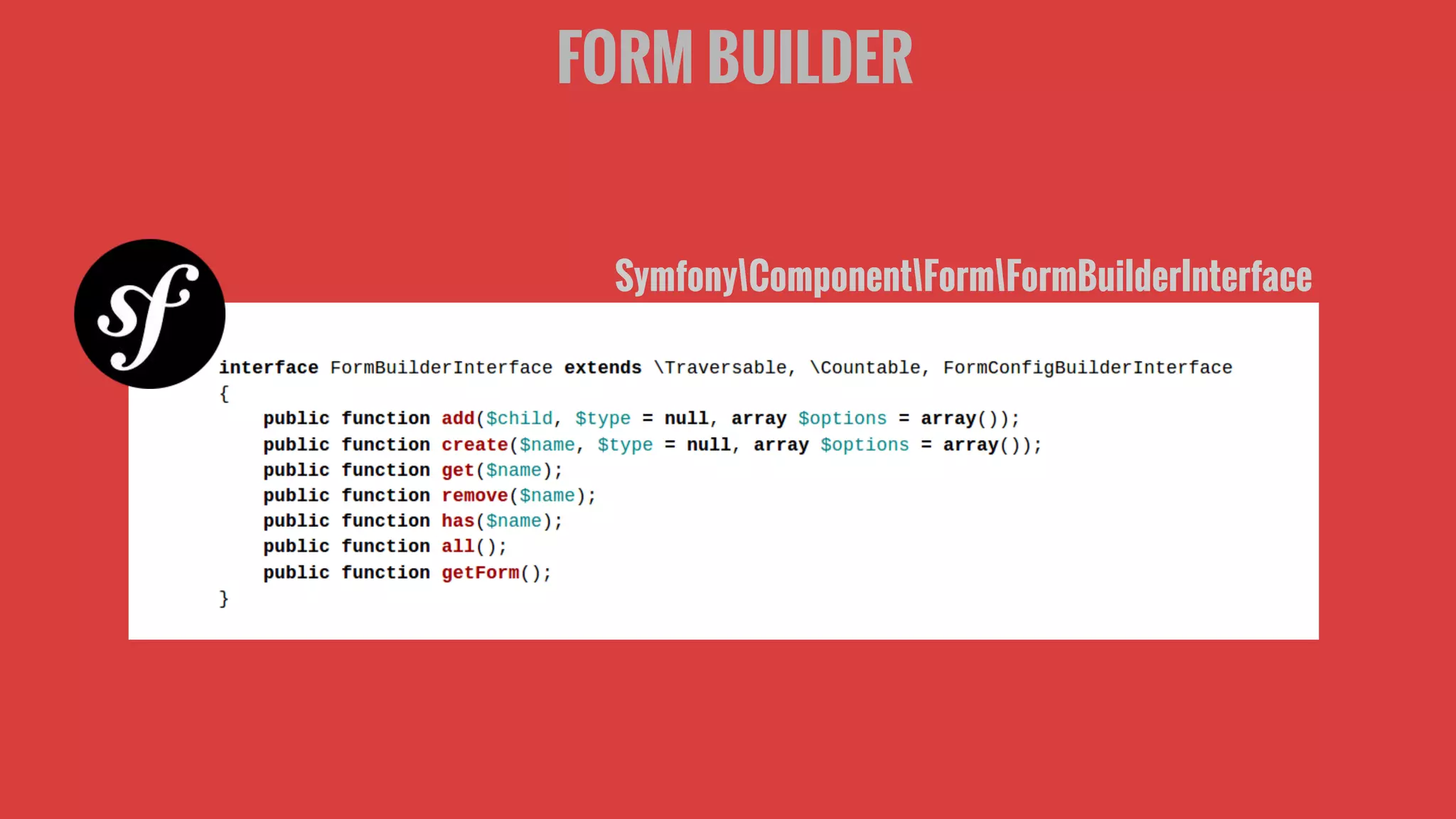
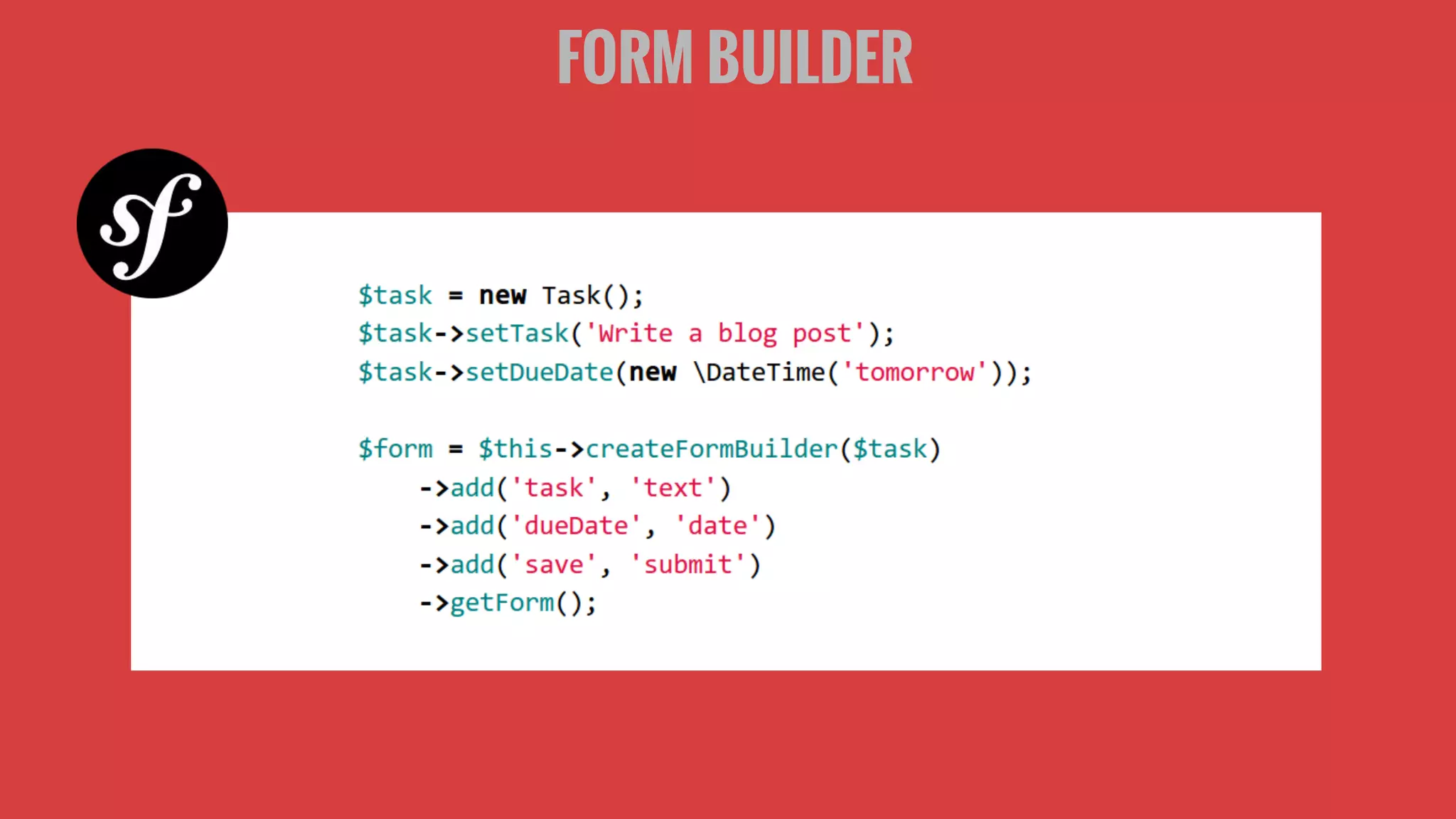
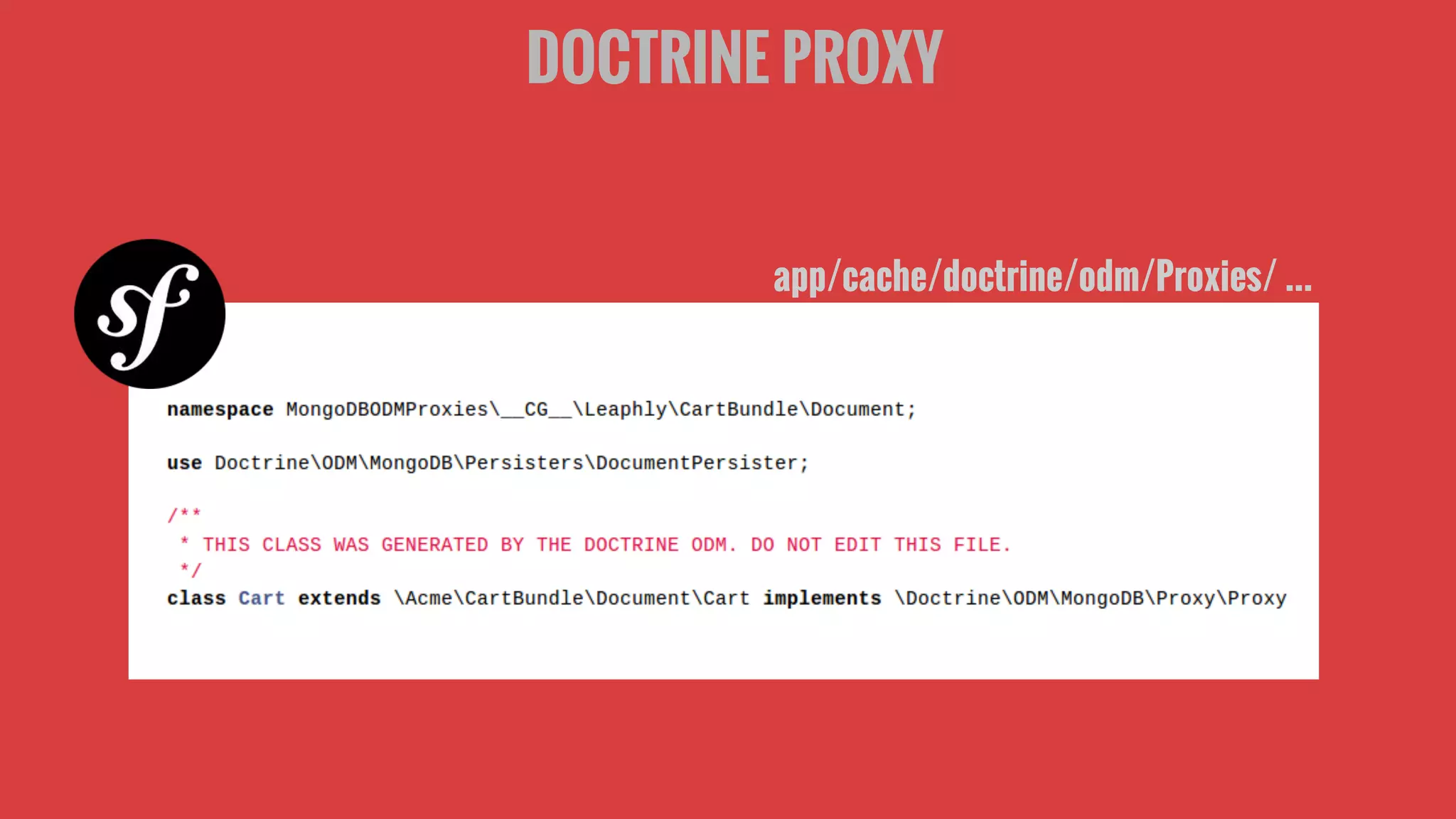
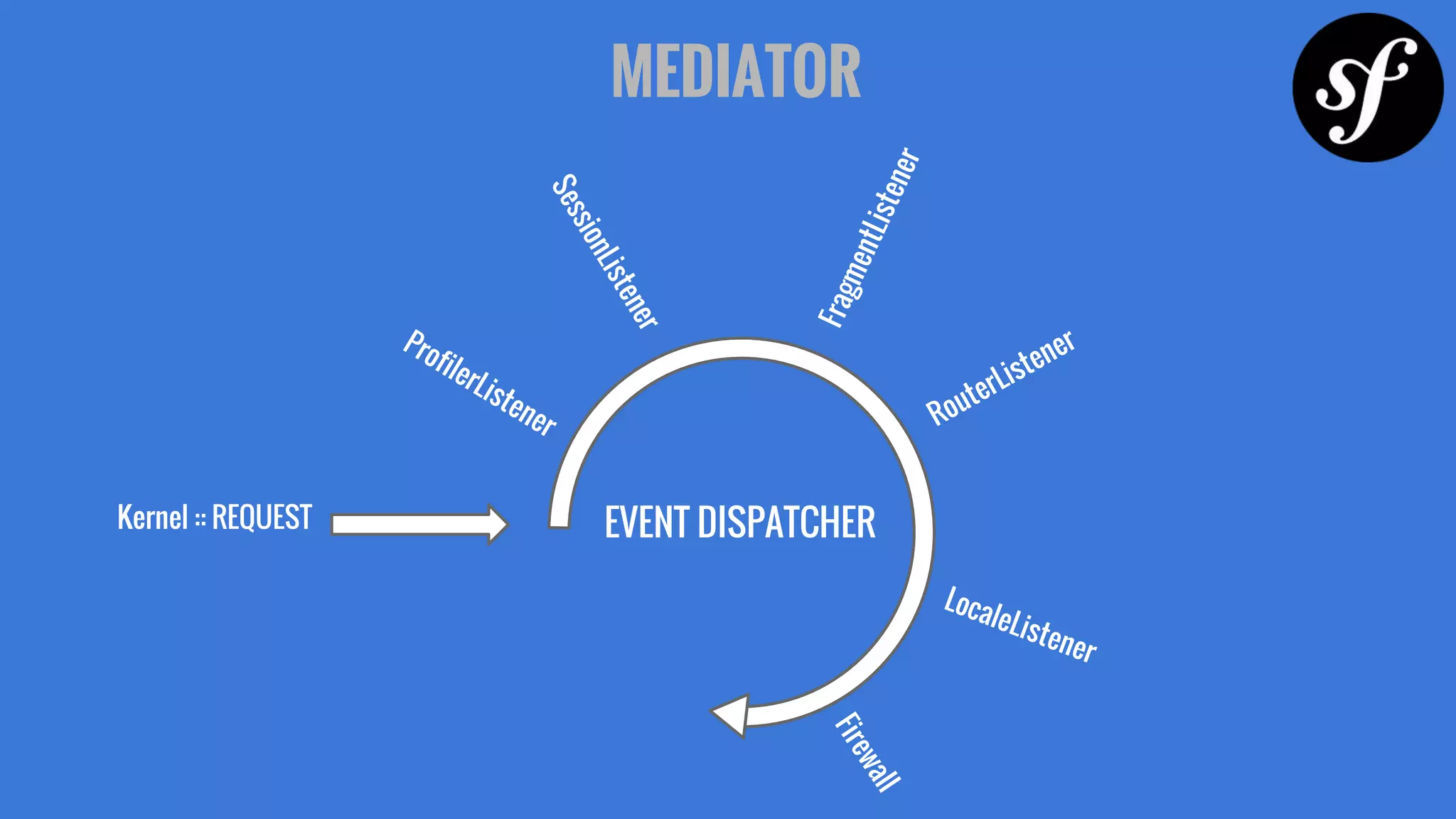
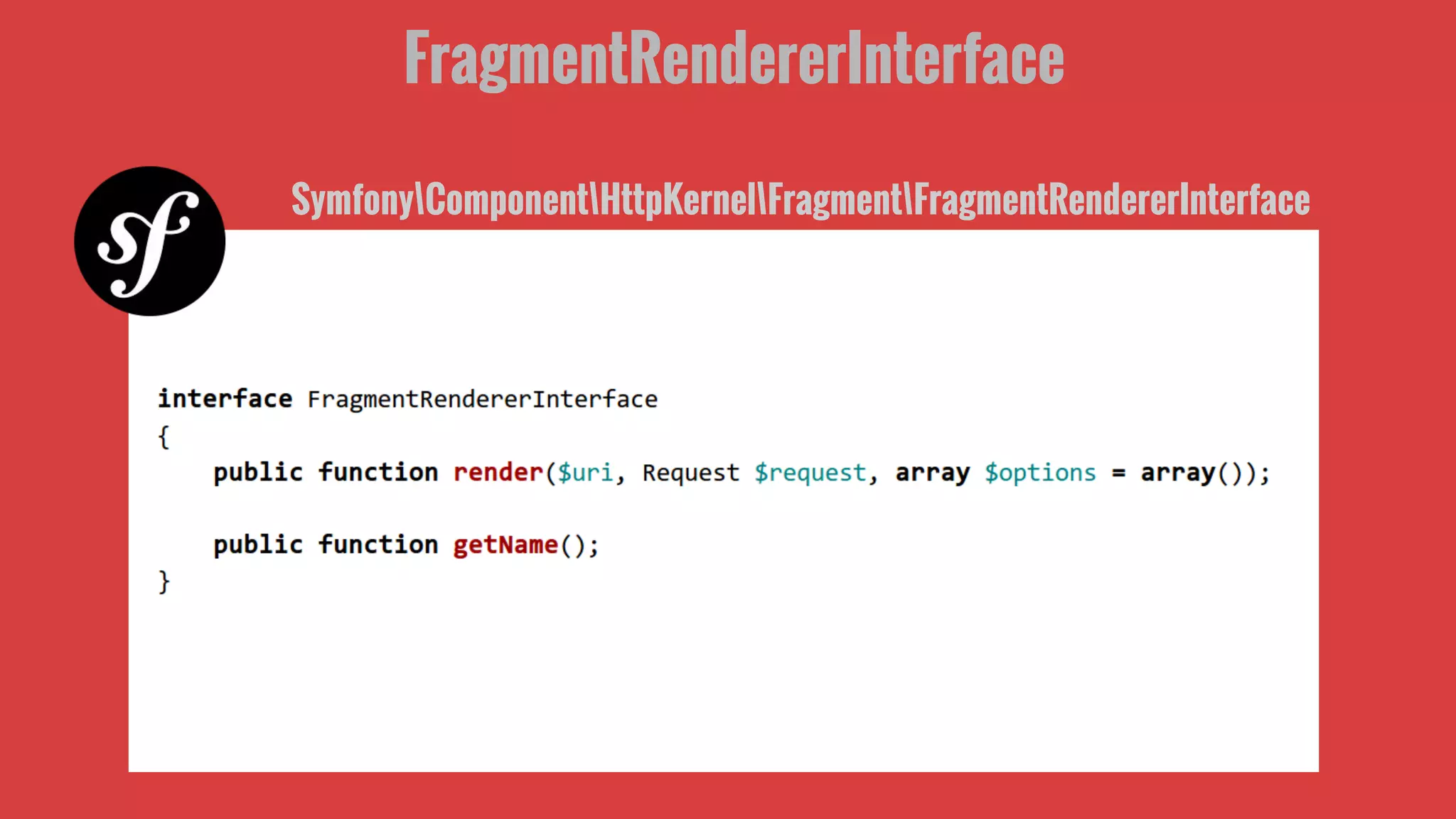
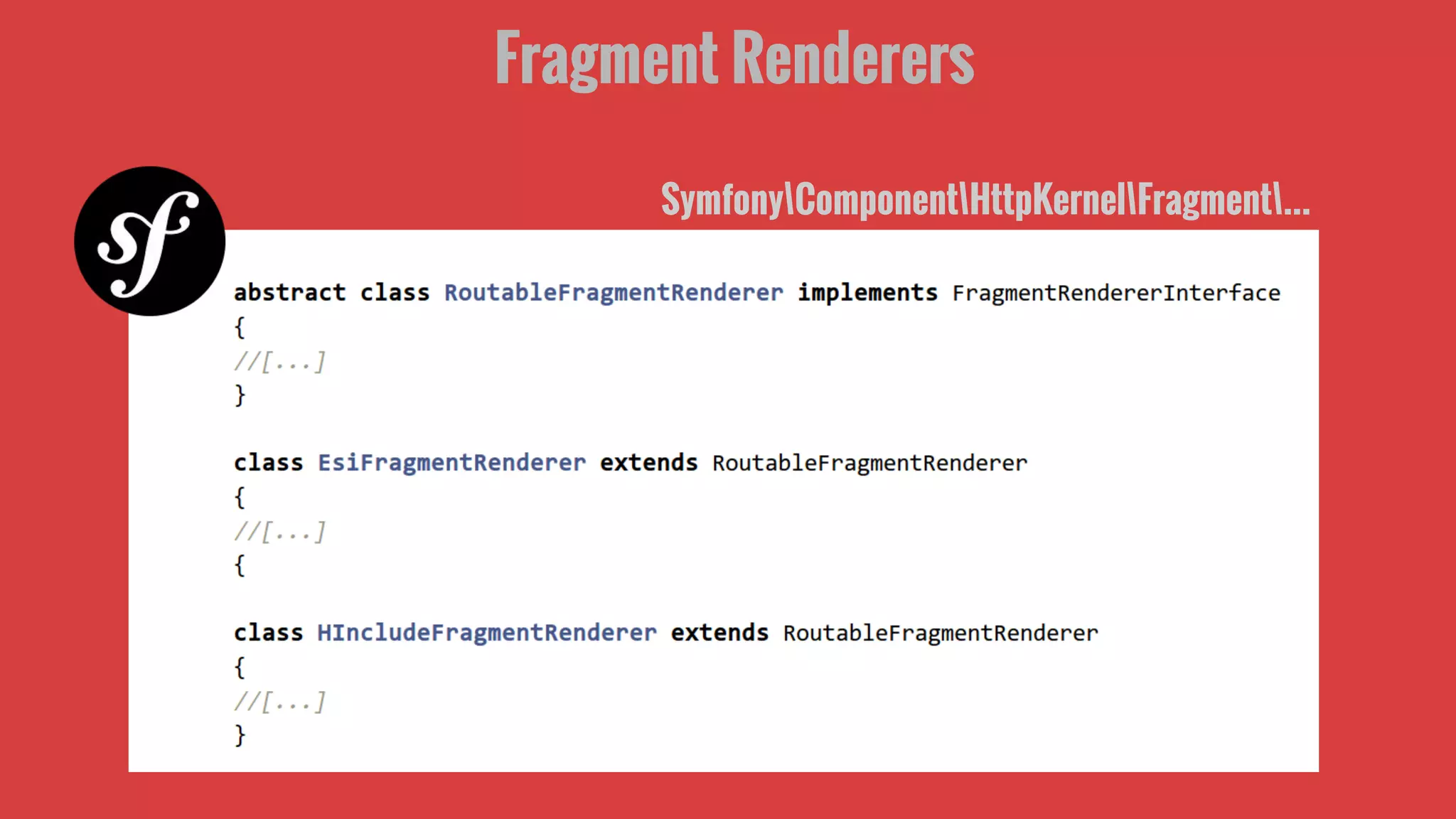
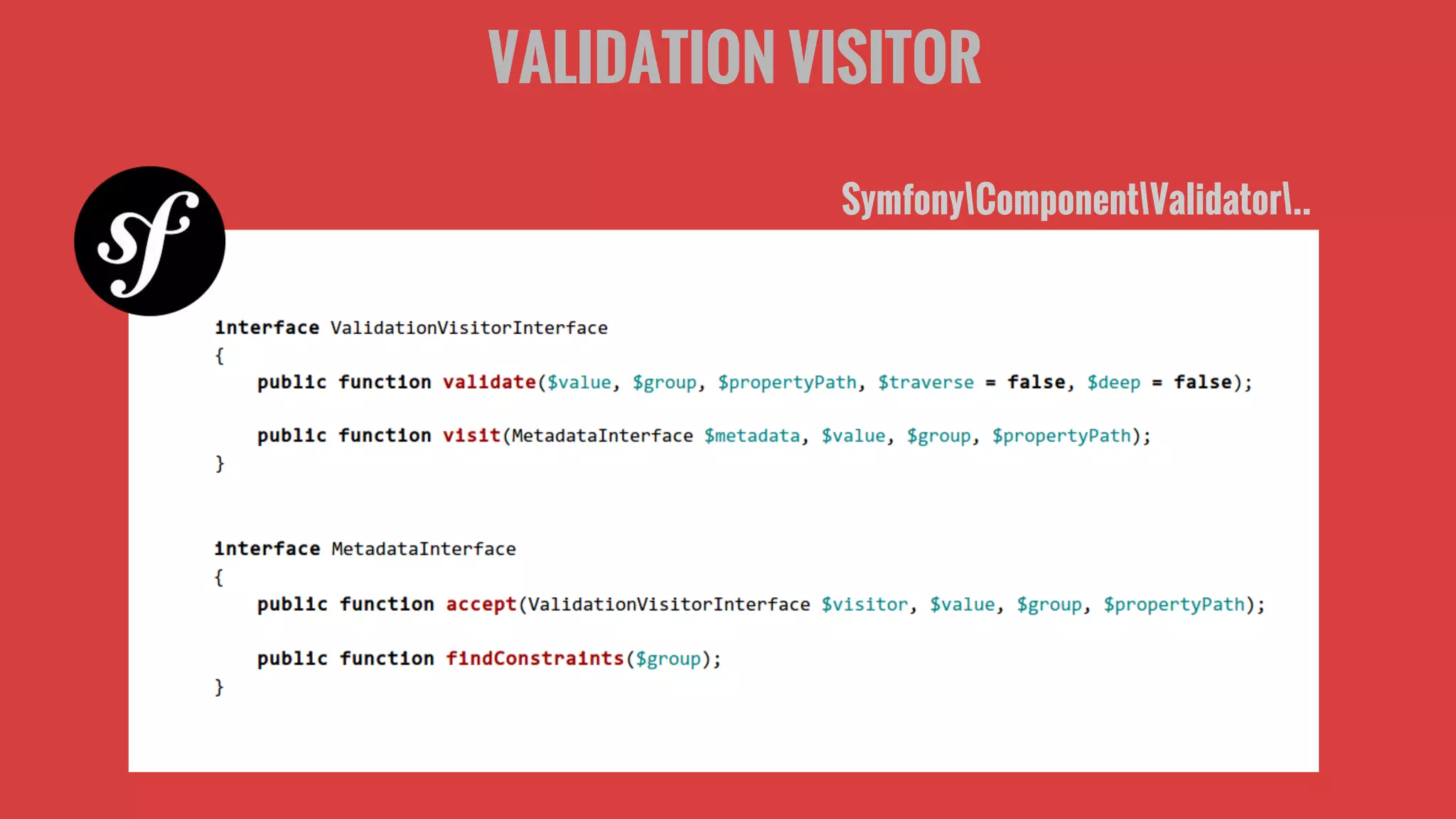
This document discusses various design patterns used in Symfony2 frameworks such as Front Controller, Decorator, Factory Method, Abstract Factory, Builder, Proxy, Mediator, Strategy, Data Mapper, Visitor, and MVC. It also discusses anti-patterns like Design for the Sake of Design, Overengineering, The Blob, Reinventing the Wheel, and Spaghetti Code. The key principles discussed are inversion of control, dependency injection, and decoupling. References for further reading on design patterns, inversion of control, and anti-patterns are also provided.