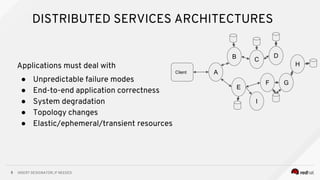
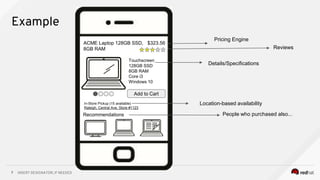
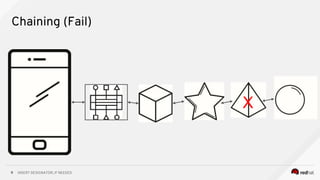
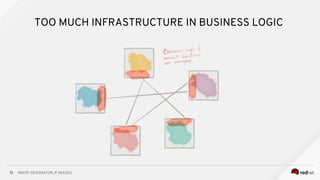
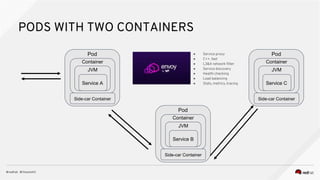
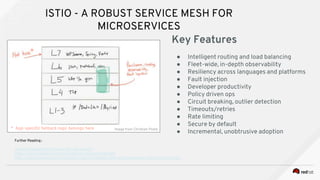
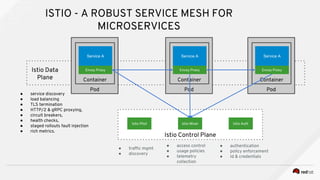
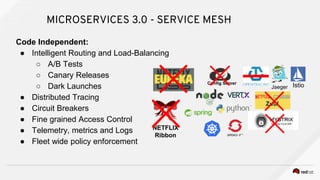
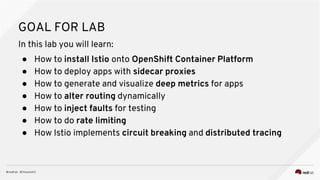
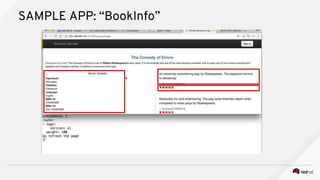
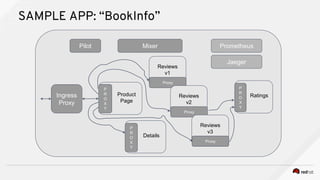
The document discusses distributed applications and microservices architectures. It describes benefits like performance, reliability and resiliency. It also discusses challenges of distributed systems like unpredictable failures and changing topologies. The document introduces Istio, an open source service mesh, that provides features to manage traffic and enforce policies in distributed applications running on Kubernetes. It describes a hands-on lab using Istio to detect and prevent issues in a sample book catalog application with multiple microservices.