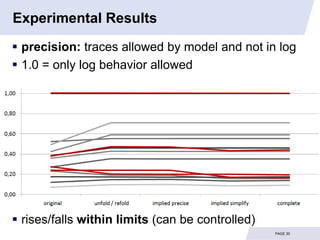
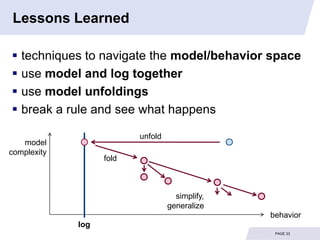
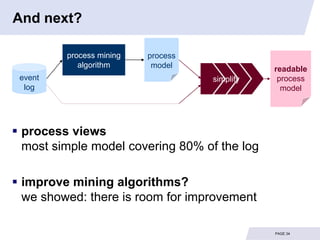
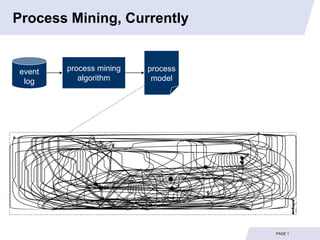
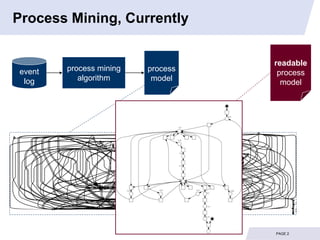
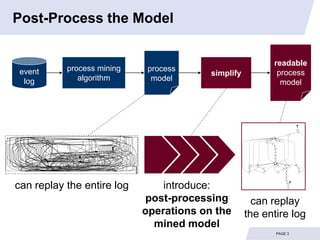
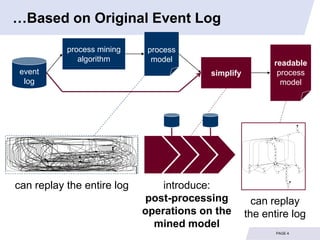
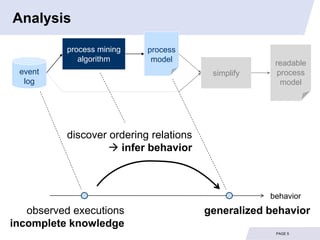
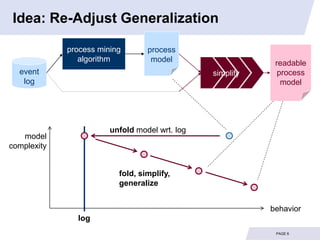
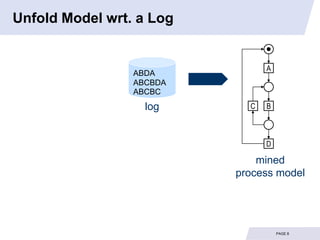
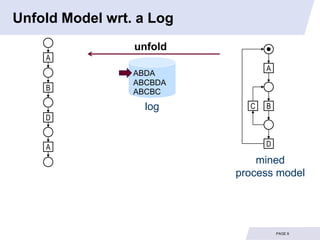
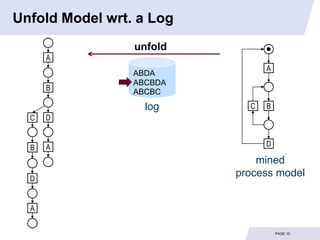
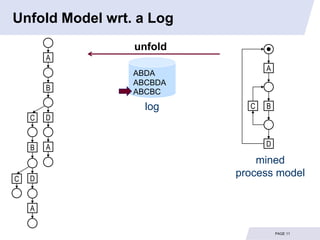
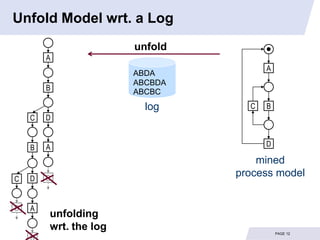
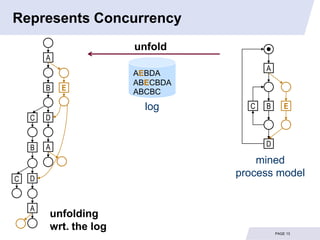
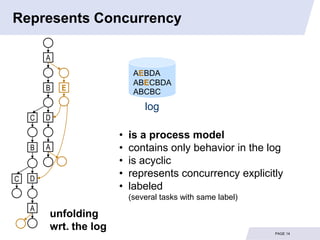
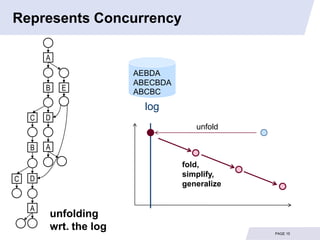
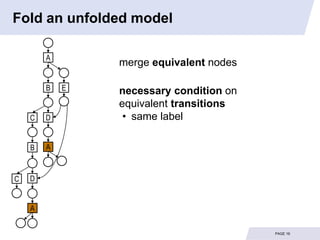
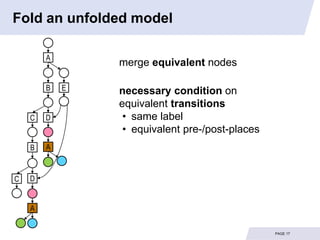
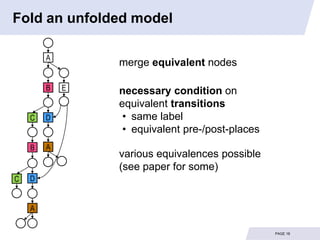
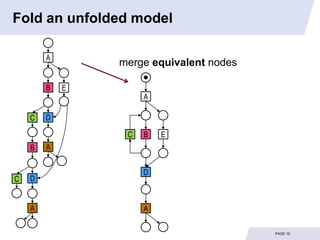
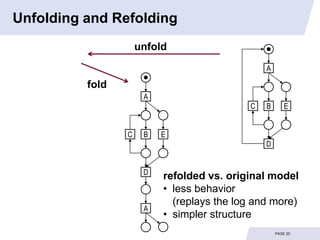
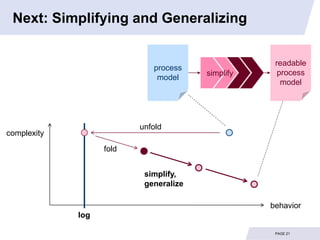
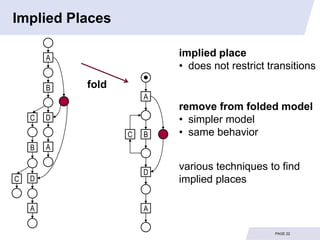
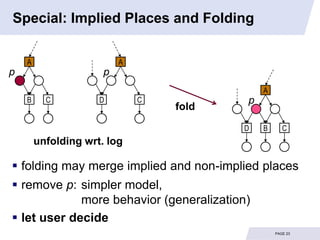
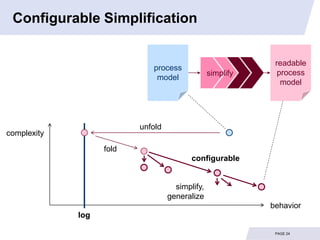
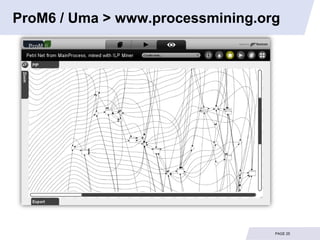
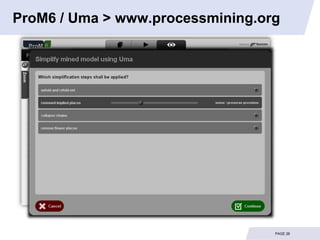
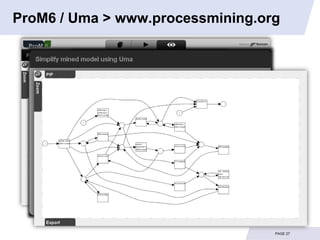
The document describes techniques for simplifying process models mined from event logs to make them more readable and understandable for users. It involves unfolding the mined model based on the event log to represent concurrency explicitly, then refolding and merging equivalent nodes. Implied places that do not restrict behavior can be removed. The resulting model has less complexity but the same behavior as the original model. Experimental results on benchmark logs show the techniques can significantly reduce model complexity while maintaining precision.
![Experimental Results
15 benchmark logs, 6 industrial logs
[www.promtools.org/prom5/]
PAGE 28](https://image.slidesharecdn.com/bpm2011fahlandaalstminesimplify-110901073831-phpapp01/85/Simplifying-Mined-Process-Models-29-320.jpg)
![Experimental Results
15 benchmark logs, 6 industrial logs
[www.promtools.org/prom5/]
model complexity = #arcs / #nodes
9.0
8.0
7.0
6.0
5.0
4.0
3.0
2.0
1.0
0.0
PAGE 29](https://image.slidesharecdn.com/bpm2011fahlandaalstminesimplify-110901073831-phpapp01/85/Simplifying-Mined-Process-Models-30-320.jpg)