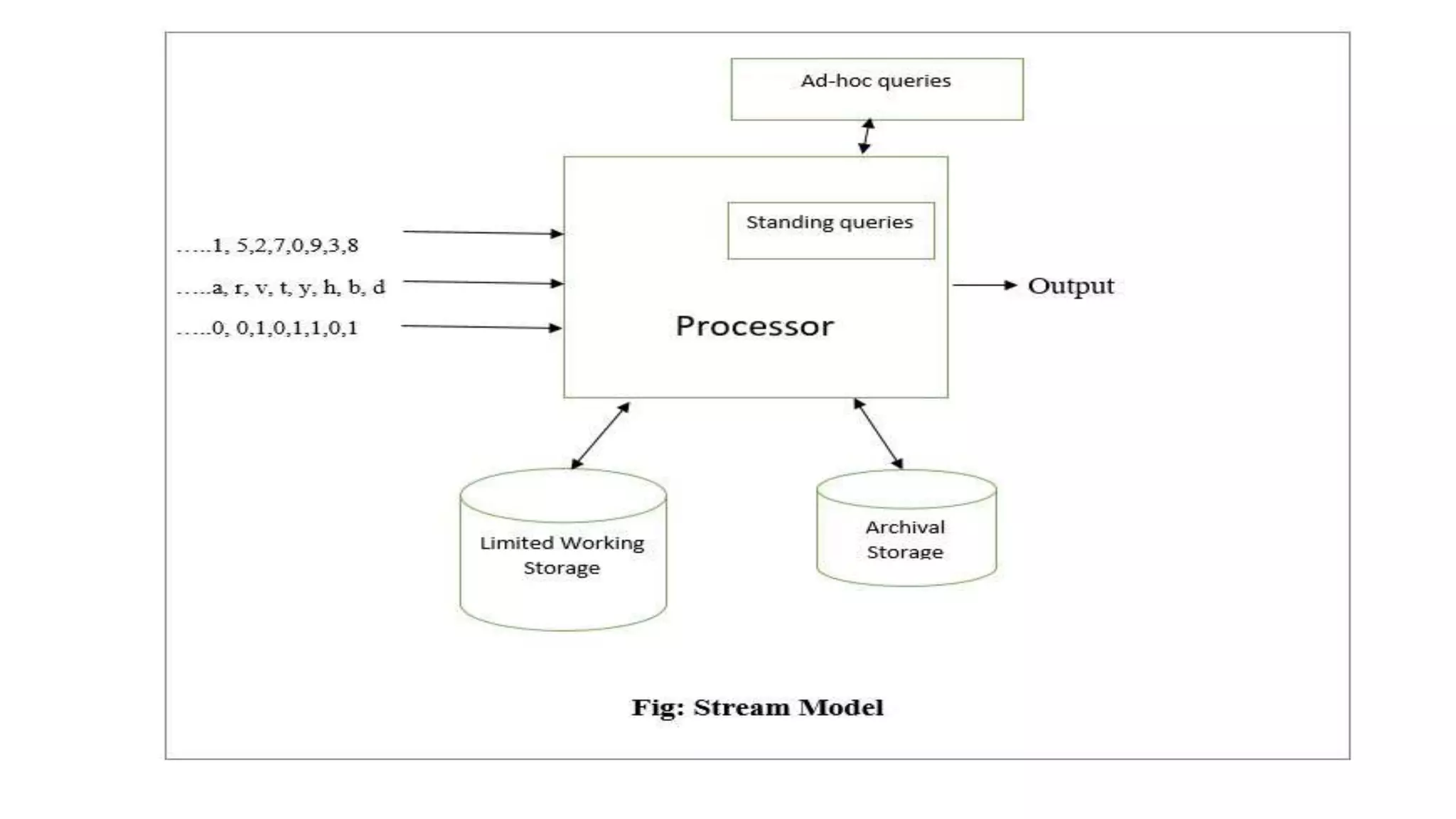
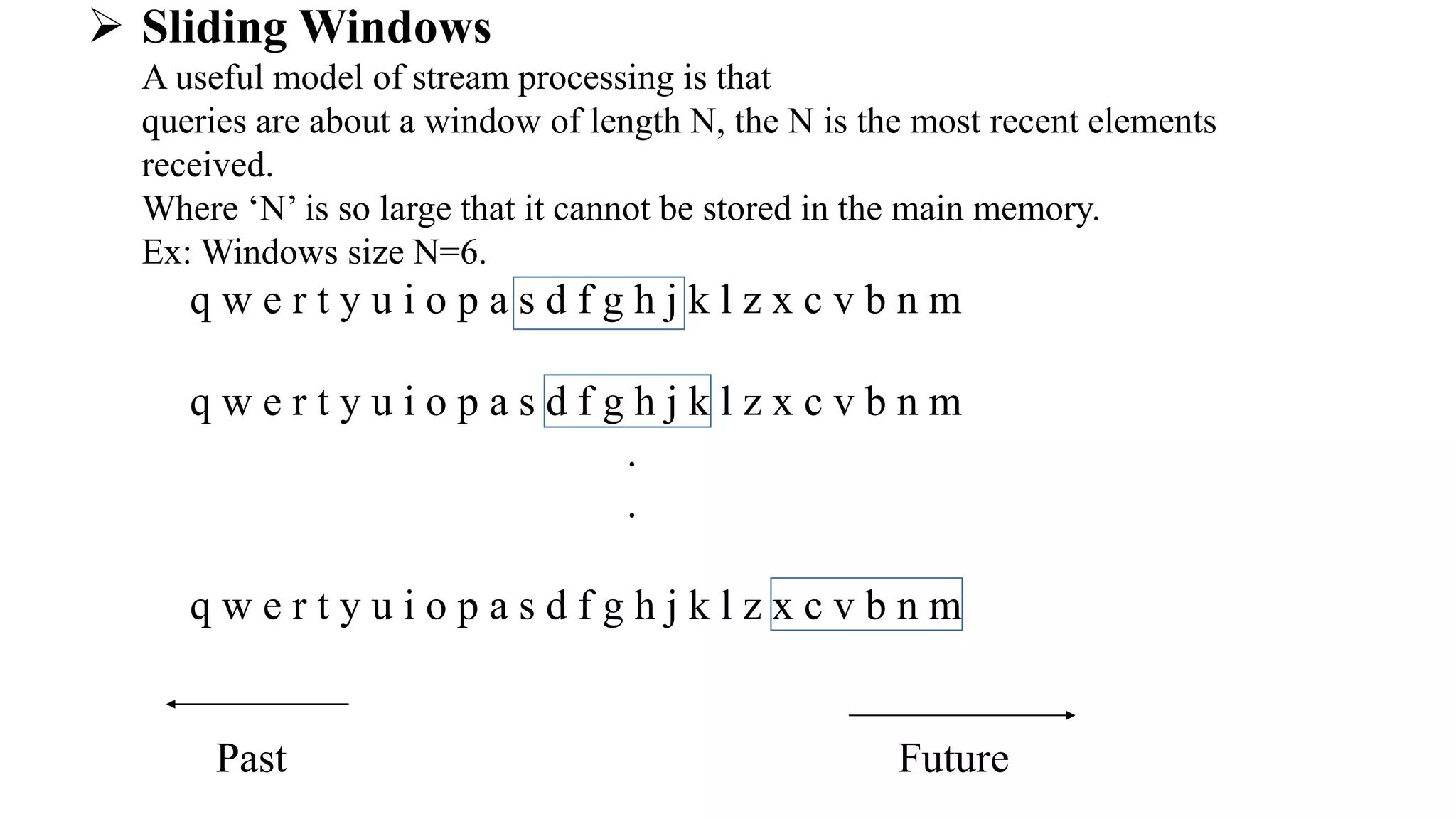
This document discusses mining data streams. It describes how stream management is important when input is controlled externally, unlike in a DBMS where input is controlled by programming staff. It explains the stream model where tuples enter rapidly and the system cannot store the entire stream. Critical calculations must be made about the stream using limited memory. There are two forms of queries: ad-hoc queries asked once and standing queries asked continuously. The document also discusses sliding windows as a model where queries are about the most recent N elements received, where N is too large to store in memory. It provides examples of applications of the stream model like mining query streams and click streams.