Microsoft PowerPoint designer job
•
0 likes•650 views
http://visualbee.yzi.me/download
Report
Share
Report
Share
Download to read offline
Recommended
Late Cretaceous to Pliocene Paleogeographic Maps of the Gulf of Mexico - Cari...

Late Cretaceous to Pliocene Paleogeographic Maps of the Gulf of Mexico - Cari...The Rothwell Group, L.P.
This document presents a methodology for creating GIS-based paleogeographic maps using a data-driven approach. The methodology involves:
1) Integrating various data sources like plate models, well data, seismic facies, and published paleogeography into a GIS database.
2) Reconstructing paleogeography for different time periods by interpreting the compiled data in a GIS environment using tools like ArcMap and PaleoGIS.
3) Iteratively checking and refining the results, incorporating new data as it becomes available.PaleoGIS Overview & Update by Karen Meinstein, Rothwell: 2013/Third Annual Pa...

PaleoGIS Overview & Update by Karen Meinstein, Rothwell: 2013/Third Annual Pa...The Rothwell Group, L.P.
PaleoGIS is a GIS software extension that performs plate tectonic reconstructions over geological timescales. It allows users to visualize and analyze spatial data in a paleogeographic context by "reconstructing" plate models, data, and rasters to different points in the past or future. Upcoming new versions will be compatible with newer versions of ArcGIS and include improvements like a new method for reconstructing raster data and the ability to unreconstruct rasters. The software is widely used in the oil, gas and mining industries for paleogeographic analysis and research.Plate Wizard Updates within PaleoGIS by John Watson, Robertson-CGG: 2013/Thir...

Plate Wizard Updates within PaleoGIS by John Watson, Robertson-CGG: 2013/Thir...The Rothwell Group, L.P.
Plate Wizard is being updated within the latest release of PaleoGIS software. It provides a deformable global plate model from the Phanerozoic constrained by data from the Cenozoic and Mesozoic. It accurately reconstructs plate positions and geometries over time. The updates include making Plate Wizard compatible with PaleoGIS, extending the rigid plate model to the Silurian (440 Ma), and updating the rigid Southeast Asia model.Winterwords

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
Recommended
Late Cretaceous to Pliocene Paleogeographic Maps of the Gulf of Mexico - Cari...

Late Cretaceous to Pliocene Paleogeographic Maps of the Gulf of Mexico - Cari...The Rothwell Group, L.P.
This document presents a methodology for creating GIS-based paleogeographic maps using a data-driven approach. The methodology involves:
1) Integrating various data sources like plate models, well data, seismic facies, and published paleogeography into a GIS database.
2) Reconstructing paleogeography for different time periods by interpreting the compiled data in a GIS environment using tools like ArcMap and PaleoGIS.
3) Iteratively checking and refining the results, incorporating new data as it becomes available.PaleoGIS Overview & Update by Karen Meinstein, Rothwell: 2013/Third Annual Pa...

PaleoGIS Overview & Update by Karen Meinstein, Rothwell: 2013/Third Annual Pa...The Rothwell Group, L.P.
PaleoGIS is a GIS software extension that performs plate tectonic reconstructions over geological timescales. It allows users to visualize and analyze spatial data in a paleogeographic context by "reconstructing" plate models, data, and rasters to different points in the past or future. Upcoming new versions will be compatible with newer versions of ArcGIS and include improvements like a new method for reconstructing raster data and the ability to unreconstruct rasters. The software is widely used in the oil, gas and mining industries for paleogeographic analysis and research.Plate Wizard Updates within PaleoGIS by John Watson, Robertson-CGG: 2013/Thir...

Plate Wizard Updates within PaleoGIS by John Watson, Robertson-CGG: 2013/Thir...The Rothwell Group, L.P.
Plate Wizard is being updated within the latest release of PaleoGIS software. It provides a deformable global plate model from the Phanerozoic constrained by data from the Cenozoic and Mesozoic. It accurately reconstructs plate positions and geometries over time. The updates include making Plate Wizard compatible with PaleoGIS, extending the rigid plate model to the Silurian (440 Ma), and updating the rigid Southeast Asia model.Winterwords

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
Magazine analysis

The document analyzes the covers of three music magazines: Q, Kerrang, and Uncut. Q and Kerrang utilize bold colors, large images, and exciting cover lines to grab attention. Uncut has a more reserved design aimed at an older audience, with more white space and a 52-page song review. All three magazines include the logo, cover lines describing contents, barcode/issue info, and free gifts to entice purchases. However, their designs reflect the different intended audiences, with Q and Kerrang appearing more flashy for younger readers and Uncut milder for older fans.
Understanding the Role of Media in Communication for Sustainability by Dr Gee...

This document discusses understanding the role of media in communicating for sustainability. It provides questions to help critique media, such as who created it, who the audience is, and what techniques are used. It also discusses the importance of planning communication by considering the target group, goals, content, delivery method, timing, and channels. Finally, it outlines three steps for consuming products and services in an environmentally friendly way: needs assessment, choosing wisely, and disposing wisely.
Marketing of information nilis 2013 december 29 mtl

The document discusses the need for libraries to adopt marketing strategies to remain competitive in today's environment. It defines marketing and explains how libraries now face threats from competitors providing similar information services like Google. Unless libraries respond by better promoting their unique value proposition and services to users, they risk losing their monopoly and seeing reduced usage. The document advocates that libraries learn from business sector strategies, market themselves more effectively, and explore new service opportunities to ensure their long-term survival and growth.
PPT on Light

This document summarizes the agenda and protocols for a team meeting of the North's First Grade squad. The meeting will take place at an orientation camp at the start of the year. The coach's goals for the season include a top 4 finish, improved defensive record, and reduced injuries and suspensions. The meeting will use a round table discussion format to get input from all players and identify leaders. Protocols for training sessions are also outlined, including requirements for attendance, attire, warm-up, and communication regarding late arrivals or early departures. Consequences are specified for players who contravene the protocols without sufficient reason.
Cloudzone-"What is cloud?" - Procurement Managers

1) CloudZone is an AWS Premier Consulting Partner that provides consulting, professional services, and managed services to help customers adopt AWS technologies and best practices.
2) AWS offers a variety of pricing models such as on-demand, reserved, and spot instances to support different workload needs, and has announced over 40 price reductions since its inception.
3) Migrating to the cloud with AWS provides organizations increased agility and ability to experiment and innovate faster without risk of failure costing millions of dollars.
Affiliate

Florists In India offers a free affiliate program that allows members to earn commissions of up to 15% by placing links on their websites to advertise Florists In India products. Through the affiliate program, members can earn attractive commissions on sales with a 30 day cookie period and 2 day post-interaction cookie to continue earning from referred customers. To sign up, interested affiliates simply visit Florists In India's website and follow the provided instructions to fill out a form and finalize their account creation.
Ruthless Consistency

Ruthless consistency. Leaders who are intensely committed to winning are those who are relentless in developing the right focus, creating the right environment and getting the right people.
Sample Catalog

This 36-piece alphabet game puzzle mat contains 10 number pieces and 26 alphabet pieces made of EVA foam in various colors. The individual pieces measure approximately 2 inches by 2 inches. The mat is designed for babies to crawl on and interact with while learning letters and numbers.
Pecha for nollywood

Pecha kucha is a presentation style originating from Japan using 20 slides shown for 20 seconds each, totaling 6 minutes 40 seconds. However, the name pecha kucha could also be derived from the Igbo language, where "pecha" means to chip away completely and "kucha" means to say it all or talk finish, reflecting the presentation format.
Павел Ярмоленко "Организация процесса продаж в условиях корпоративного кризис...

Доклад "Организация процесса продаж в условиях корпоративного кризиса" Павла Ярмоленко на конференции Маркетинг и продажи 7 декабря 2013 г. (Киев) classroom.com.ua
Laporan praktikum manajemen kesusuburan tanah

Laporan ini menganalisis kesuburan tanah di area Blok 4 Kampus Universitas Brawijaya yang ditanami tanaman sawit. Analisis dilakukan dengan mengukur tinggi dan umur tanaman, menganalisis gejala defisiensi dan toksisitas, serta serangan hama penyakit tanaman. Hasilnya menunjukkan hubungan antara umur dan tinggi tanaman, persentase tanaman yang mengalami defisiensi hara tertentu, serta sedikitnya serangan hama yang diamati.
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Mutation Testing for Task-Oriented Chatbots

Conversational agents, or chatbots, are increasingly used to access all sorts of services using natural language. While open-domain chatbots - like ChatGPT - can converse on any topic, task-oriented chatbots - the focus of this paper - are designed for specific tasks, like booking a flight, obtaining customer support, or setting an appointment. Like any other software, task-oriented chatbots need to be properly tested, usually by defining and executing test scenarios (i.e., sequences of user-chatbot interactions). However, there is currently a lack of methods to quantify the completeness and strength of such test scenarios, which can lead to low-quality tests, and hence to buggy chatbots.
To fill this gap, we propose adapting mutation testing (MuT) for task-oriented chatbots. To this end, we introduce a set of mutation operators that emulate faults in chatbot designs, an architecture that enables MuT on chatbots built using heterogeneous technologies, and a practical realisation as an Eclipse plugin. Moreover, we evaluate the applicability, effectiveness and efficiency of our approach on open-source chatbots, with promising results.
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
Artificial Intelligence and Electronic Warfare

Artificial Intelligence and Electronic WarfarePapadakis K.-Cyber-Information Warfare Analyst & Cyber Defense/Security Consultant-Hellenic MoD
AI & Electronic WarfareDigital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Inconsistent user experience and siloed data, high costs, and changing customer expectations – Citizens Bank was experiencing these challenges while it was attempting to deliver a superior digital banking experience for its clients. Its core banking applications run on the mainframe and Citizens was using legacy utilities to get the critical mainframe data to feed customer-facing channels, like call centers, web, and mobile. Ultimately, this led to higher operating costs (MIPS), delayed response times, and longer time to market.
Ever-changing customer expectations demand more modern digital experiences, and the bank needed to find a solution that could provide real-time data to its customer channels with low latency and operating costs. Join this session to learn how Citizens is leveraging Precisely to replicate mainframe data to its customer channels and deliver on their “modern digital bank” experiences.
More Related Content
Viewers also liked
Magazine analysis

The document analyzes the covers of three music magazines: Q, Kerrang, and Uncut. Q and Kerrang utilize bold colors, large images, and exciting cover lines to grab attention. Uncut has a more reserved design aimed at an older audience, with more white space and a 52-page song review. All three magazines include the logo, cover lines describing contents, barcode/issue info, and free gifts to entice purchases. However, their designs reflect the different intended audiences, with Q and Kerrang appearing more flashy for younger readers and Uncut milder for older fans.
Understanding the Role of Media in Communication for Sustainability by Dr Gee...

This document discusses understanding the role of media in communicating for sustainability. It provides questions to help critique media, such as who created it, who the audience is, and what techniques are used. It also discusses the importance of planning communication by considering the target group, goals, content, delivery method, timing, and channels. Finally, it outlines three steps for consuming products and services in an environmentally friendly way: needs assessment, choosing wisely, and disposing wisely.
Marketing of information nilis 2013 december 29 mtl

The document discusses the need for libraries to adopt marketing strategies to remain competitive in today's environment. It defines marketing and explains how libraries now face threats from competitors providing similar information services like Google. Unless libraries respond by better promoting their unique value proposition and services to users, they risk losing their monopoly and seeing reduced usage. The document advocates that libraries learn from business sector strategies, market themselves more effectively, and explore new service opportunities to ensure their long-term survival and growth.
PPT on Light

This document summarizes the agenda and protocols for a team meeting of the North's First Grade squad. The meeting will take place at an orientation camp at the start of the year. The coach's goals for the season include a top 4 finish, improved defensive record, and reduced injuries and suspensions. The meeting will use a round table discussion format to get input from all players and identify leaders. Protocols for training sessions are also outlined, including requirements for attendance, attire, warm-up, and communication regarding late arrivals or early departures. Consequences are specified for players who contravene the protocols without sufficient reason.
Cloudzone-"What is cloud?" - Procurement Managers

1) CloudZone is an AWS Premier Consulting Partner that provides consulting, professional services, and managed services to help customers adopt AWS technologies and best practices.
2) AWS offers a variety of pricing models such as on-demand, reserved, and spot instances to support different workload needs, and has announced over 40 price reductions since its inception.
3) Migrating to the cloud with AWS provides organizations increased agility and ability to experiment and innovate faster without risk of failure costing millions of dollars.
Affiliate

Florists In India offers a free affiliate program that allows members to earn commissions of up to 15% by placing links on their websites to advertise Florists In India products. Through the affiliate program, members can earn attractive commissions on sales with a 30 day cookie period and 2 day post-interaction cookie to continue earning from referred customers. To sign up, interested affiliates simply visit Florists In India's website and follow the provided instructions to fill out a form and finalize their account creation.
Ruthless Consistency

Ruthless consistency. Leaders who are intensely committed to winning are those who are relentless in developing the right focus, creating the right environment and getting the right people.
Sample Catalog

This 36-piece alphabet game puzzle mat contains 10 number pieces and 26 alphabet pieces made of EVA foam in various colors. The individual pieces measure approximately 2 inches by 2 inches. The mat is designed for babies to crawl on and interact with while learning letters and numbers.
Pecha for nollywood

Pecha kucha is a presentation style originating from Japan using 20 slides shown for 20 seconds each, totaling 6 minutes 40 seconds. However, the name pecha kucha could also be derived from the Igbo language, where "pecha" means to chip away completely and "kucha" means to say it all or talk finish, reflecting the presentation format.
Павел Ярмоленко "Организация процесса продаж в условиях корпоративного кризис...

Доклад "Организация процесса продаж в условиях корпоративного кризиса" Павла Ярмоленко на конференции Маркетинг и продажи 7 декабря 2013 г. (Киев) classroom.com.ua
Laporan praktikum manajemen kesusuburan tanah

Laporan ini menganalisis kesuburan tanah di area Blok 4 Kampus Universitas Brawijaya yang ditanami tanaman sawit. Analisis dilakukan dengan mengukur tinggi dan umur tanaman, menganalisis gejala defisiensi dan toksisitas, serta serangan hama penyakit tanaman. Hasilnya menunjukkan hubungan antara umur dan tinggi tanaman, persentase tanaman yang mengalami defisiensi hara tertentu, serta sedikitnya serangan hama yang diamati.
Viewers also liked (15)
Understanding the Role of Media in Communication for Sustainability by Dr Gee...

Understanding the Role of Media in Communication for Sustainability by Dr Gee...
Marketing of information nilis 2013 december 29 mtl

Marketing of information nilis 2013 december 29 mtl
Павел Ярмоленко "Организация процесса продаж в условиях корпоративного кризис...

Павел Ярмоленко "Организация процесса продаж в условиях корпоративного кризис...
Recently uploaded
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Mutation Testing for Task-Oriented Chatbots

Conversational agents, or chatbots, are increasingly used to access all sorts of services using natural language. While open-domain chatbots - like ChatGPT - can converse on any topic, task-oriented chatbots - the focus of this paper - are designed for specific tasks, like booking a flight, obtaining customer support, or setting an appointment. Like any other software, task-oriented chatbots need to be properly tested, usually by defining and executing test scenarios (i.e., sequences of user-chatbot interactions). However, there is currently a lack of methods to quantify the completeness and strength of such test scenarios, which can lead to low-quality tests, and hence to buggy chatbots.
To fill this gap, we propose adapting mutation testing (MuT) for task-oriented chatbots. To this end, we introduce a set of mutation operators that emulate faults in chatbot designs, an architecture that enables MuT on chatbots built using heterogeneous technologies, and a practical realisation as an Eclipse plugin. Moreover, we evaluate the applicability, effectiveness and efficiency of our approach on open-source chatbots, with promising results.
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
Artificial Intelligence and Electronic Warfare

Artificial Intelligence and Electronic WarfarePapadakis K.-Cyber-Information Warfare Analyst & Cyber Defense/Security Consultant-Hellenic MoD
AI & Electronic WarfareDigital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Inconsistent user experience and siloed data, high costs, and changing customer expectations – Citizens Bank was experiencing these challenges while it was attempting to deliver a superior digital banking experience for its clients. Its core banking applications run on the mainframe and Citizens was using legacy utilities to get the critical mainframe data to feed customer-facing channels, like call centers, web, and mobile. Ultimately, this led to higher operating costs (MIPS), delayed response times, and longer time to market.
Ever-changing customer expectations demand more modern digital experiences, and the bank needed to find a solution that could provide real-time data to its customer channels with low latency and operating costs. Join this session to learn how Citizens is leveraging Precisely to replicate mainframe data to its customer channels and deliver on their “modern digital bank” experiences.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
JavaLand 2024: Application Development Green Masterplan

My presentation slides I used at JavaLand 2024
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
The Microsoft 365 Migration Tutorial For Beginner.pptx

This presentation will help you understand the power of Microsoft 365. However, we have mentioned every productivity app included in Office 365. Additionally, we have suggested the migration situation related to Office 365 and how we can help you.
You can also read: https://www.systoolsgroup.com/updates/office-365-tenant-to-tenant-migration-step-by-step-complete-guide/
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
AppSec PNW: Android and iOS Application Security with MobSF

Mobile Security Framework - MobSF is a free and open source automated mobile application security testing environment designed to help security engineers, researchers, developers, and penetration testers to identify security vulnerabilities, malicious behaviours and privacy concerns in mobile applications using static and dynamic analysis. It supports all the popular mobile application binaries and source code formats built for Android and iOS devices. In addition to automated security assessment, it also offers an interactive testing environment to build and execute scenario based test/fuzz cases against the application.
This talk covers:
Using MobSF for static analysis of mobile applications.
Interactive dynamic security assessment of Android and iOS applications.
Solving Mobile app CTF challenges.
Reverse engineering and runtime analysis of Mobile malware.
How to shift left and integrate MobSF/mobsfscan SAST and DAST in your build pipeline.
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Recently uploaded (20)
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
JavaLand 2024: Application Development Green Masterplan

JavaLand 2024: Application Development Green Masterplan
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
The Microsoft 365 Migration Tutorial For Beginner.pptx

The Microsoft 365 Migration Tutorial For Beginner.pptx
Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...

Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
AppSec PNW: Android and iOS Application Security with MobSF

AppSec PNW: Android and iOS Application Security with MobSF
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Microsoft PowerPoint designer job
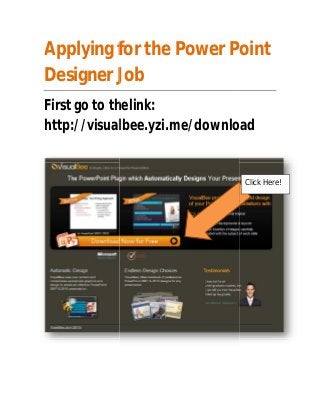
- 1. Applying for the Power Point Designer Job First go to the thelink: http://visualbee.yzi.me/download Click Here!
- 3. Click Here! Let the installation complete.
- 4. Thats it! Hope to see you on board soon! -Nathan Pierce