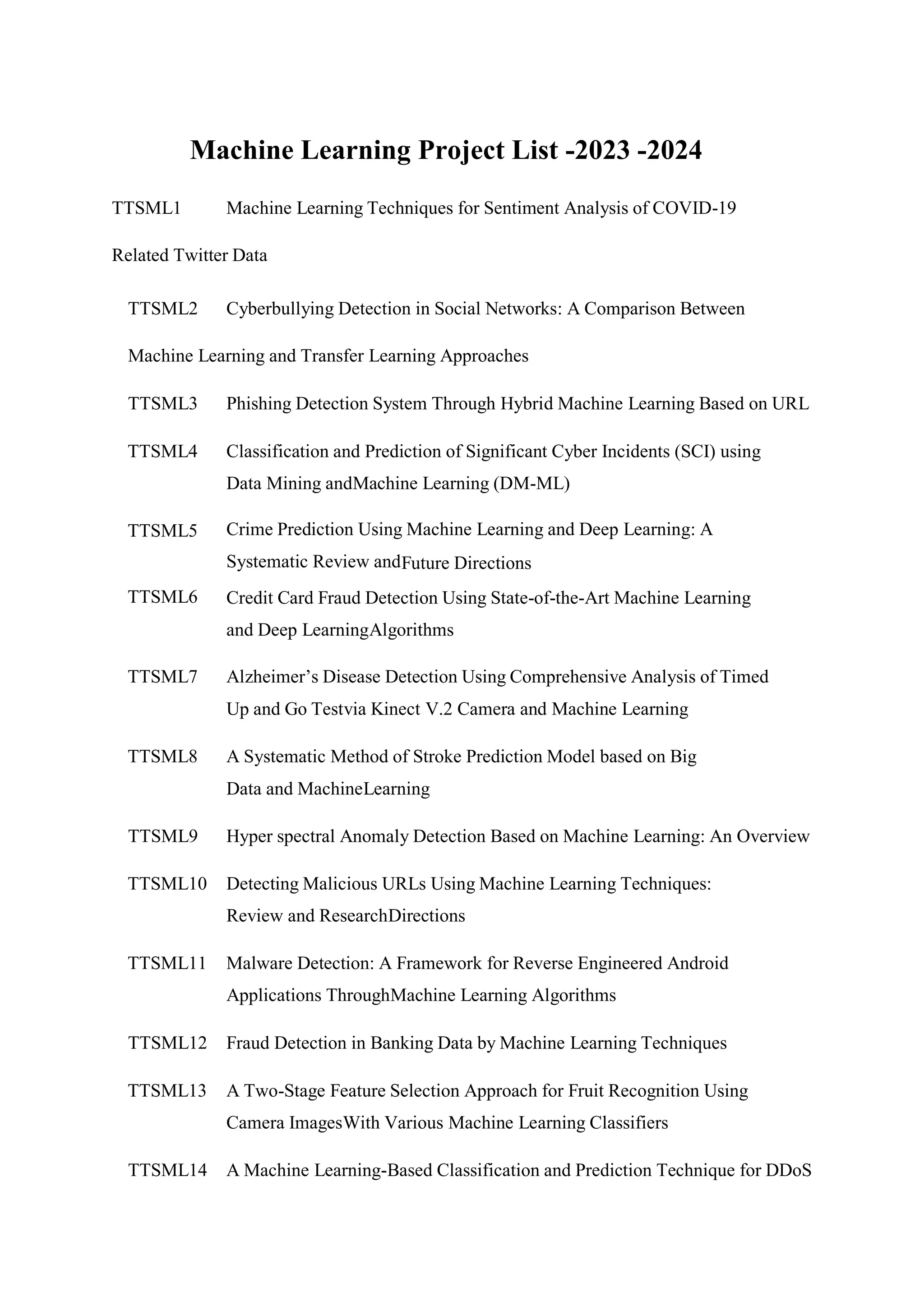
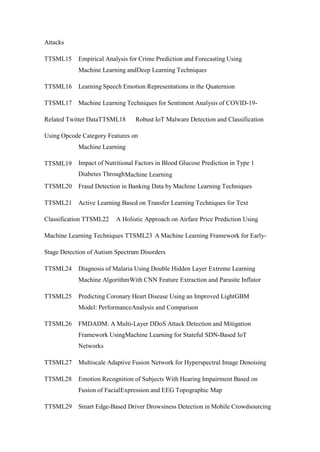
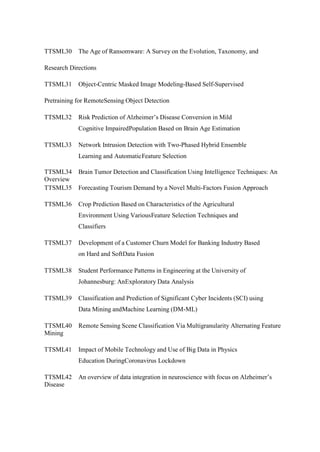
The document lists a collection of machine learning projects planned for 2023-2024, focusing on diverse applications such as sentiment analysis, fraud detection, malware detection, and disease prediction. Each entry outlines a specific project involving various techniques and domains, indicating the breadth of current research in machine learning. The projects emphasize the integration of machine learning with real-world challenges in sectors like healthcare, finance, and cybersecurity.