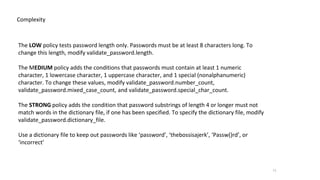
The document provides guidelines for securing a MySQL database server, emphasizing the importance of not allowing direct internet access, maintaining complex password policies, and regularly auditing user accounts. It highlights the use of roles for user privileges, the necessity of backups, and techniques for data encryption and monitoring. Additionally, it mentions best practices for query performance and the need for constant server evaluation to prevent security breaches.










![12
Example
SQL > create user 'Foo'@'%' IDENTIFIED BY RANDOM PASSWORD;
+------+------+----------------------+
| user | host | generated password |
+------+------+----------------------+
| Foo | % | Ld]5/Fkn[Kk29/g/M;>n |
+------+------+----------------------+
1 row in set (0.0090 sec)
Another Example
SQL > ALTER USER 'Foo'@'%' IDENTIFIED BY RANDOM PASSWORD;
+------+------+----------------------+
| user | host | generated password |
+------+------+----------------------+
| Foo | % | !rN<NCxjE5ncC6mB*2:@ |
+------+------+----------------------+
Let server generate password](https://image.slidesharecdn.com/lockingdownyourmysqldatabase-220922194231-54be2b05/85/Locking-Down-Your-MySQL-Database-pptx-12-320.jpg)

![14
[mysqld]
password_history=6
password_reuse_interval=365
Password reuse](https://image.slidesharecdn.com/lockingdownyourmysqldatabase-220922194231-54be2b05/85/Locking-Down-Your-MySQL-Database-pptx-14-320.jpg)
























![41
CREATE TABLE `testx` (
`col` JSON,
CONSTRAINT `myage_inRange`
CHECK (JSON_SCHEMA_VALID('{"type": "object",
"properties": {
"myage": {
"type" : "number",
"minimum": 28,
"maximum": 99
}
},"required": ["myage"]
}', `col`) = 1)
);
mysql> insert into testx values('{"myage":27}');
ERROR 3819 (HY000): Check constraint 'myage_inRange' is
violated.
mysql> insert into testx values('{"myage":97}');
Query OK, 1 row affected (0.02 sec)](https://image.slidesharecdn.com/lockingdownyourmysqldatabase-220922194231-54be2b05/85/Locking-Down-Your-MySQL-Database-pptx-41-320.jpg)