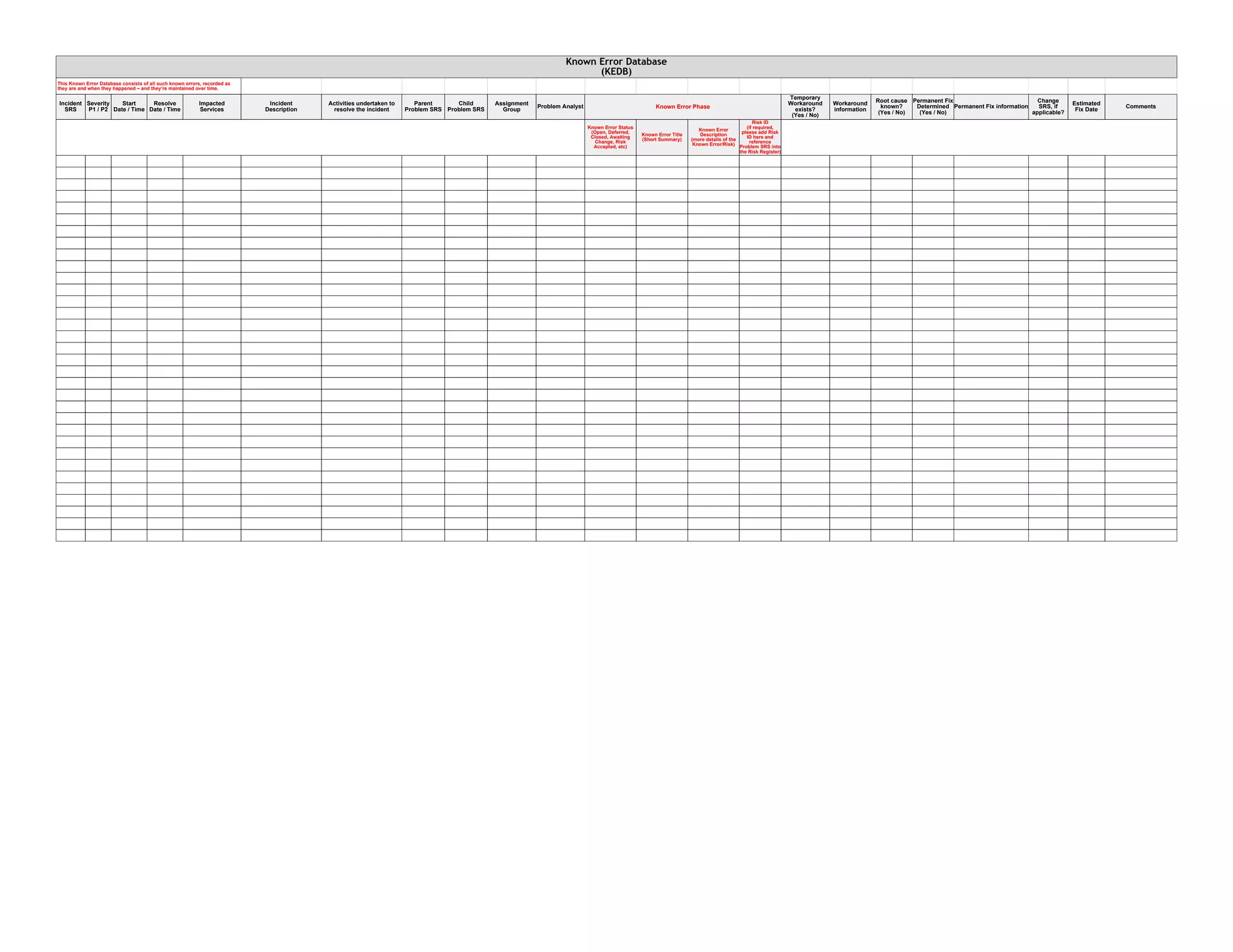
This document is a template for recording known errors and incidents in a database to track their resolution over time. It includes fields for the incident details, affected services, activities to resolve the issue, related problems, assignments, workarounds, root cause, permanent fix, applicable changes, estimated fix date, comments, status, title, description, risk ID, and phase. Maintaining this known error database allows organizations to document errors as they occur and monitor their resolution.