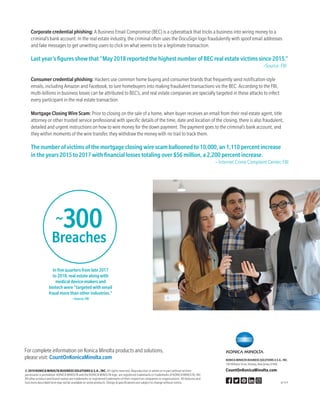
The document outlines significant cybersecurity threats facing real estate companies, noting a rise in attacks such as banking trojans, spyware, ransomware, and business email compromises. It highlights that many real estate businesses are inadequately prepared to fend off these threats, despite a notable increase in awareness and concern about cyberattacks. The FBI reports substantial financial losses and a growing number of incidents related to cyber fraud in the real estate sector.