Recommended
PDF
DOCX
DOCX
PPTX
PDF
Prislista e print-storbild
PDF
Portrait de Nicolas Bourgeois, Responsable Développement Social Urbain chez P...
PPTX
PDF
Smart target - brosura marketing treninga
PPTX
Unlocking the Power of Facebook Ads
PPS
Cortijo los rosales (cadiz)
PDF
PDF
PDF
PDF
Informe ePyme 2012 Fundetec
PDF
Espejored 56 polanco lomas abr-may 2013
PDF
PDF
PDF
PPTX
Seamless Upgrade to 8.5 Version. Performance Testing Tuning of Ektron & the E...
PDF
Social Media Opportunities
PDF
2014 Cadillac CTS-V Digital Brochure
PDF
Residus de xamota ceràmica_Butlletí_11/13
DOC
116642547 fraktur-basis-kranii
PDF
PDF
PDF
PDF
کاتالوگ گروه شرکت های ساپرا
PDF
PDF
مثلث نو آوری و کارایی سازمان - سه رکن رشد سازمانی.pdf
PDF
More Related Content
PDF
DOCX
DOCX
PPTX
PDF
Prislista e print-storbild
PDF
Portrait de Nicolas Bourgeois, Responsable Développement Social Urbain chez P...
PPTX
PDF
Smart target - brosura marketing treninga
Viewers also liked
PPTX
Unlocking the Power of Facebook Ads
PPS
Cortijo los rosales (cadiz)
PDF
PDF
PDF
PDF
Informe ePyme 2012 Fundetec
PDF
Espejored 56 polanco lomas abr-may 2013
PDF
PDF
PDF
PPTX
Seamless Upgrade to 8.5 Version. Performance Testing Tuning of Ektron & the E...
PDF
Social Media Opportunities
PDF
2014 Cadillac CTS-V Digital Brochure
PDF
Residus de xamota ceràmica_Butlletí_11/13
DOC
116642547 fraktur-basis-kranii
PDF
Similar to KASYS ISMS intro.
PDF
PDF
PDF
کاتالوگ گروه شرکت های ساپرا
PDF
PDF
مثلث نو آوری و کارایی سازمان - سه رکن رشد سازمانی.pdf
PDF
PDF
SAP ERP Presentation for IKCO
PPTX
PDF
DOCX
ODP
زیر ساخت نرم افزاری شرکت توزیع برق مشهد
PDF
PPTX
مبان و مد ر_ت فناور_ اطلاعات
PDF
PDF
PDF
Cloud-ISO17789-user view (part 1)
PDF
آسيب شناسي شركت حساس گمانه شهراز
PDF
PDF
PPTX
KASYS ISMS intro. 1. KASYSKarbord System engineering group co.
سدیدمتسیسارربدکیسندمهروهگ
(سیساک)
شماست فردای فرصت امروز بصیرتToday’s Insight is Tomorrow's Opportunity
Introduction to ISMS
www.Kasys.ir | Info@Kasys.ir | Tel : 88545124-77642966| Fax : 88542264-77643967
2. 2© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 2
سیستم کاربرد مهندسی گروه معرفی(کاسیس)
•سال در سيستم کاربرد مهندسي شرکت1387های حوزه در را خود فعاليت و گرديده تأسيس
،نمود آغاز اطالعات فناوری مختلف های بخش در مميزی و مشاوره ،آموزشي خدمات ارائه مختلف
•ش ،استراتژيک سطح در اطالعات فناوری مختلف خدمات به مشتريان روزافزون نياز به توجه بارکت
از مختلف هایحوزه در اطالعات فناوری مشاوره با مرتبط هایفعاليت سيستم کاربرد مهندسيقبيل
•اطالعات فناوری استراتژيک برنامه تهيه(ITSP)،
•اطالعات فناوری جامع ريزی برنامه(ITMP)،
•بر مبتني اطالعات امنيت مديريت سيستمISMS) ISO27001)،
•بر مبتني اطالعات فناوری خدمات مديريت سيستم(ITSM) ISO20000 , ITIL،
•اطالعات فناوری راهبری چارچوبCOBIT،ISO38500
•مبتني کار و کسب تداوم مديريت(BCM) ISO22301 , ISO25999،
•اساس بر داده مراکز مميزی و طراحي ،مشاورهTIA942 , BICSI
•و...
•راست در و مشتريان به خدمات ارائه سبد تکميل برای و برگزيده اصلي فعاليت عنوان به راايجاد ای
است افزوده خود خدمات مجموعه به نيز را مرتبط افزارهای نرم و تجهيزات ارائه ،خاطر اطمينان..
3. 3© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 3
معرفی:سیس کاربرد مهندسی گروه تجاری همکارانتم
•سال در سيستم کاربرد مهندسي شرکت1391مجوز اخذ به موفقآموزشاز
اطالعات فناوری سازمان(ITC.IR)اطالعات امنيت مديريت سيستم حوزه در
ISMSگرديد
4. 4© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 4
معرفی:سیس کاربرد مهندسی گروه تجاری همکارانتم
•سال در سيستم کاربرد مهندسي شرکت1392مجوز اخذ به موفقخدمات ارائه
مشاورهاطالعات فناوری سازمان از(ITC.IR)امنيت مديريت سيستم حوزه در
اطالعاتISMSگرديد
5. 5© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 5
معرفی:سیس کاربرد مهندسی گروه تجاری همکارانتم
مجوز اخذ به موفق سيستم کاربرد مهندسي شرکتموسسه های دوره برای آموزش
المللي بين آموزشيPECBنماينده تنها عنوان به ًارسم و گرديد ايران دردر ارگان اين
گرديد معرفي ايران
6. 6© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 6
معرفی:کاسیس مشتریان
نمود اشاره زير موارد به توان مي سيستم کاربرد مهم مشتريان جمله از:
•انفورماتيک خدمات ،تک آسيا ،اول همراهبهستان ،پر شرکت ،ملت بانک ،راياندازش
ش ، ايرانيان پاسارگاد ارتباطات ،فجر پتروشيمي ،پرداز رويال ، عالئم هوشمندرکت
فناور و پژوهش مرکز ، گستر رايانه رهياب ،اطالعات فناوری سازمان ،موتور مگای
س لوله ، ميانه خاور واتر تايد ، اصفهان پرديس اطالعات فناوری ،پتروشيميازی
مشهد شهرداری ،جم کياناتک شرکت ،هيرساويژن ،شريف گستر افزار امن ،اهواز،
ژنرات پارس ،ايرانيان اعتماد اعتباری و مالي موسسه ،تهران انفورماتيک خدماتمپنا ور
موسسه ، قم استان مخابرات ،اينترنتي جرايم دادسرای ،کشاورزی جهاد وزارت ،
ايس شرکت ،تعاون توسعه بانک ،مرکزی بانک ،نيرو وزارت ،تبيان فرهنگيشرکت ،اکو
ساز ،ايمن آشنا شرکت ،پارسيان گاز پااليشگاه شرکت ،کيش اول پرداختصدا مان
استانداری ،دارو البرز شرکت ،افرانت شرکت ، ايران اسالمي جمهوری سيمای و
و زيرساخت ارتباطات ،شرکت ، اجتماعي تامين سازمان ،بوشهر..
7. 7© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 7
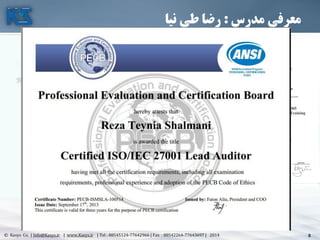
مدرس معرفی:نیا طی رضا
•سيس کاربرد مهندسي شرکت عامل مدير و موسستم
•از بيش15، مشاوره های حوزه در فعاليت سابقه سال
مشاوره و اطالعات فناوری با مرتبط مميزی و آموزش
مديريت
•اطالعات فناوری مديريت ارشد کارشناسي
•مديريت مشاوره ارشد کارشناسي
•رسمي سرمميزISO27001ازBSI
•رسمي سرمميزISO27001ازPECB
•رسمي سرمميزISO9001ازPECB
•تائيد مورد سرمميزQA, DQS,CIS,
•ايران مديريت مشاوران انجمن عضو
•رايانه صنفي نظام سازمان عضو
•و اطالعات فناوری با مرتبط مختلف های دوره مدرس
موسس ،،صنعتي مديريت سازمان در اطالعات امنيته
BRSموسسه ،SGSموسسه ،TUVموسسه ،
Mahanموسسه ،Allianceو...
فعالیت سوابق
•اطالعات فناوری استراتژيک ريزی برنامهITSP,
ITMP
•سازمان فرايندهای بازمهندسيBPR
•م با ارتباط مديريت سيستم سازیپياده و مشاورهشتری
CRM
•سازما منابع مديريت سيستم سازیپياده و مشاورهني
ERP
•سازماني جامع سيستم سازیپياده و مشاورهTotal
Solution
•اطال امنيت مديريت سيستم سازی پياده و مشاورهعات
ISMS
•اطالعات امنيت مديريت سيستم داخلي مميزی
•فناو خدمات مديريت سيستم سازی پياده و مشاورهری
اطالعاتSMS
•فناوری خدمات مديريت سيستم داخلي مميزی
اطالعاتSMS
8. 8© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 8
مدرس معرفی:نیا طی رضا
9. 9© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 9
قرن بیسوادان21نیستند نوشتن و خواندن به قادر که نیستند کسانیکه هستند کسانی بلکهتوانند نمی
در ، بیاموزند دوباره و بریزند دور را کهنه های آموختهآموخته كه ایزمانه و اطالعات انفجار عصرها
اس ما یادگیری سرعت بلكه ،نیست ما هایدانسته میزان است مهم آنچه ،شوندمی كهنه سرعت بهت.
تافلر آلوین
10. 10© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 10
•بين ارز ارزشترين با ،اطالعات دنبال به کالهبرداران ، مجرمان ، امروز دنيای در
نوابغ افراد اين که است اين است دهنده هشدار آنچه ، هستند الملليITنيستند
رسند مي خود اهداف به ها روش ترين ساده با که هستند معمولي مجرمان بلکه
•آمريکا فدرال تجارت کميته(2010)
11. 11© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 11
مدیریت سیستمهای به نیازمند سازمانهای
•دسته،اولصنايعيميباشندکهبهدليلتوليدوارائهخدماتبا
ريسکباال(خطراتزيستمحيطي،خطراتايمني،آسيبهایتجاری،
اطالعاتمحرمانهنظامي،سياسيو....)نيازمندزيرساختهایخاصي
برایحداقلسازیاينخطرهاميباشند.سازمانهایتوليدی،دارو
موادغذاييوبهداشتي،صنايعنظاميو...دراينگروهقرارميگيرند.
•دستهدوم،صنايعوکسبوکارهاييميباشندکهماهيتآنهانيازبه
پاسخگوييسريعبهمشتريانبودهوفاصلهزمانتوليدوارائهخدماتتا
زمانمصرفمحصوالتبسيارکوتاهميباشدولذارضايتمشتریبايددر
محلتوليدتامينگردد.سازمانهاييمانندهتلها،بنگاههایحملو
نقل،رستورانهاو...دراينگروهقرارميگيرند.
12. 12© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 12
مدیریت سیستمهای به نیازمند سازمانهای
•تتهتدستداومتت ترایتب تهتک تندتميباش تاييتوکاره تبتکس و تنايعتص ، تومتس
در و ختود کارفرمايتان و مشتتريان بتا خصتوا بته تجتاری شراکتهای
مشتتری و منتدی سيستتم اثبتات به ملزم منعقده قراردادهای چارچوب
ميباشت الزم الزامات ساير نيز و خدمات و محصوالت کيفيت و گراييند.
و خودرو قطعات کنندگان تامين ، نفتي پيمانکاران...گرو اين درقترار ه
ميگيرند.
•دستهميباشن پيشرو کارهای و کسب و موسسات و شرکتها ، چهارمکه د
بت النفسه في و برده پي مديريتي سيستمهای کاربری اهميت بهدنبتال ه
ميباشند خود سازمانهای در بهبودها.
13. 13© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 13
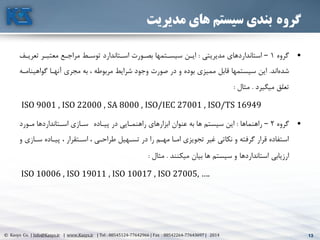
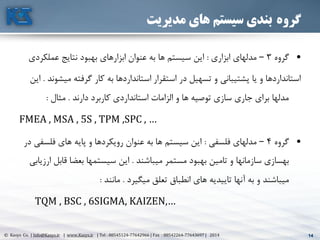
گروهمدیریت های سیستم بندی
•گروه1–مديريتي استانداردهای:تعريت معتبتر مراجتع توستط استتاندارد بصتورت سيستتمها ايتنف
اندشده.گواهي آنهتا مجری به ، مربوطه شرايط وجود صورت در و بوده مميزی قابل سيستمها ايننامته
ميگيرد تعلق.مثال:
ISO 9001 , ISO 22000 , SA 8000 , ISO/IEC 27001 , ISO/TS 16949
•گروه2–راهنماها:پيتاده در راهنمتايي ابزارهای عنوان به ها سيستم اينمتورد استتانداردها ستازی
ستاز پيتاده ، استتقرار ، طراحتي تستهيل در را مهتم امتا تجويزی غير نکاتي و گرفته قرار استفادهو ی
ميکنند بيان ها سيستم و استانداردها ارزيابي.مثال:
ISO 10006 , ISO 19011 , ISO 10017 , ISO 27005, ….
14. 14© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 14
گروهمدیریت های سیستم بندی
•گروه3–ابزاری مدلهای:عملک نتايج بهبود ابزارهای عنوان به ها سيستم اينردی
مي گرفته کار به استانداردها استقرار در تسهيل و پشتيباني يا و استانداردهاشوند.اين
دارند کاربرد استانداردی الزامات و ها توصيه سازی جاری برای مدلها.مثال:
FMEA , MSA , 5S , TPM ,SPC , …
•گروه4–فلسفي مدلهای:فلس های پايه و رويکردها عنوان به ها سيستم ايندر في
ميباشند مستمر بهبود تامين و سازمانها بهسازی.قاب بعضا سيستمها اينارزيابي ل
ميگيرد تعلق انطباق های تاييديه آنها به و ميباشند.مانند:
TQM , BSC , 6SIGMA, KAIZEN,…
15. 15© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 15
رایج استانداردهای
16. 16© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 16
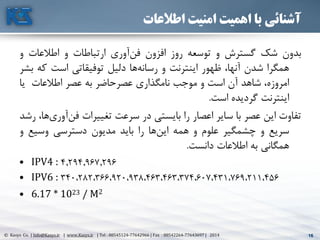
اطالعات امنیت اهمیت با آشنائی
بدونشکگسترشوتوسعهروزافزونآوریفنارتباطاتواطالعاتو
همگراشدن،آنهاظهوراينترنتوهارسانهدليلتوفيقاتياستکهبشر
،امروزهشاهدآناستوموجبنامگذاریعصرحاضربهعصراطالعاتيا
اينترنتگرديدهاست.
تفاوتاينعصرباسايراعصاررابايستيدرسرعتتغييراتآوفن،هاریرشد
سريعوچشمگيرعلوموهمههااينرابايدمديوندسترسيوسيعو
همگانيبهاطالعاتدانست.
• IPV4 : 4.294.967.296
• IPV6 : 340،282،366،920،938،463،463،374،607،431،769،211،456
• 6.17 * 1023 / M2
17. 17© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 17
اطالعات امنیت اهمیت با آشنائی
•از بيش2شودمي نوشته روز هر بالگ پست ميليون!حدا تايم مجله در مقدار اين نوشتن برایقل
770کشدمي طول سال.
•اگربود کشور فيسبوک.بود دنيا بزرگ کشور سومين امروز.
•درشودمي لينکدين وارد جديد کاربر دو ثانيه هر!از بيش رقم اين170رسدمي روز در کاربر هزار.
•هرشودمي زده بوک فيس در اليک ميليارد دو از بيش روز!گي هایگونه مقدار از بيش عدد ايناهي
باشد موجود سياره يک در است ممکن که است!
•بيشاز270شودمي هزينه آنالين دقيقه در دالر هزار!
•بيشاز750کنندمي دنبال را آنالين برند يک حداقل اجتماعي هایشبکه کاربر ميليون!اينحداقل
امريکاست متحده اياالت جمعيت دوبرابر.
•بيشد اجتماعي برندهای طريق از را رويدادها که اندگفته آنالين کاربر ميليارد نيم و يک ازنبال
کنندمي!رقم اين20است جهان جمعيت درصد.
•79ک توصيه بار يک حداقل را کنند مي دنبال که برندی محتوای توييتر کاربران از درصداندرده!
•دراز بيش کاربران ،روز هر مجموع20کنندمي صرف وقت بوک فيس در سال هزار.
•مبادالتمدت ظرف اجتماعي تجارت طريق از5از بيش به آينده سال30شودمي دالر ميليارد!
18. 18© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 18
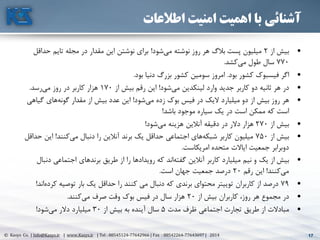
اطالعات امنیت اهمیت با آشنائی
سرعت ،اطالعات دنيای را امروز دنيای ،انديشمندان از برخي همچنين
انددانسته وشتاب.
دهه ويژگي اگر گيتس بيل قول به1980دهه و کيفيت به رويکرد1990
دهه ،است بوده فرآيندها مجدد مهندسي دوران2000دوران بايد را
دانست شتاب.
و شده حياتي بسيار هاسازمان در علم و دانش ،اطالعات توليد طرفي از
باشدمي ساز سرنوشت بسيار سوم هزاره در آنها از نگهداری و حفظ.
19. 19© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 19
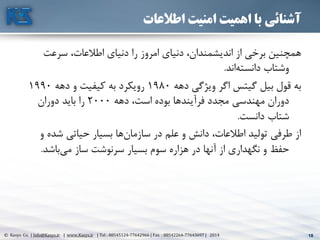
اطالعات امنیت اهمیت با آشنائی
تشک را سازماني و فردی قدرت هایپايه و آورده فراهم را سرمايه ،دانايييل
دهدمي.شودمي برابر دو سال چهار يا سه هر موجود اطالعات.
رقابتي مزيت کننده تعيين دانش يعني آن از گيریبهره و اطالعاتجهان در
است.
و اطالعات رفتن بين از شخصي موارد در حتي و ها سازمان بعضي در اما
قاب غير کار نيروی و زمان صرف به منجر اطالعات ديدن آسيب حتيل
ي حيات موارد برخي در حتي و شودمي آنها به دسترسي جهت تصورک
دهد مي قرار تهديد مورد را سازمان.
20. 20© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 20
اطالعات امنیت اهمیت با آشنائی
21. 21© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 21
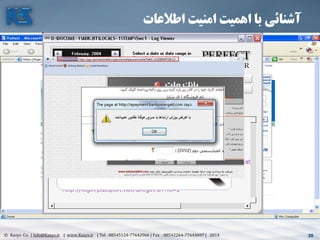
های رمزADOBE(17/08/1392)
•به نزديک2اين از ادوبي کاربری های حساب رفته لو عبور رمزهای از رمز ميليون
بوده قرار:123456
•ًاحتمعبور رمز و کاربری شناسه رفتن لو خبر اين از پيش38کاربری حساب ميليون
ادوبي(Adobe)ايد شنيده را.مشاوره گروه از ،عبور رمز امنيت متخصص يک حال
،استريکچر100ک منتشر را ادوبي کاربران عبور رمزهای ترين استفاده پر از موردرده.
حدود که شد مشخص ناباوری عين در2رمز ،ادوبي کاربران از تن از ميليون
123456بودند کرده انتخاب خود برای را.
•در،پرکاربرد رمزهای دوم رده123456789که طوری به ،داشت قرار500000
بودند گذاشته شان کاربری حساب برای را رمز اين کاربر.های رمزpasswordو
adobe123با ترتيب به هم350000و200000قرار بعدی های رده در کاربر
دارند
22. 22© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 22
22
اطالعات امنیت اهمیت با آشنائی
•شرکت«Sophos»صفحه يک ،کرد اعالم ،امنيتي افزارهاینرم توليدکننده ،
هر اينترنتي4.5ثانيهاز بيش روز هر و گيردمي قرار حمله مورد بار يکه بيستزار
جديد نمونهشودمي کشف حمله و نفوذ هایبرنامه از.
•توسط شده آوری جمع اطالعات اساس برشرکتSymantecبه نزديک ،60
درصدتوسط که هايي سيستم کلStunxnetايران در اند شده واقع حمله مورد
دارند وجود.
23. 23© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 23
اطالعات امنیت اهمیت با آشنائی
• 65% of businesses that lose computing
capabilities for more than one week never
recover and go out of business.
• A Company Denied Access to Mission-Critical
Data For More Than 48 Hours Will Likely Be
Out Of Business With In One Years
24. 24© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 24
اطالعات امنیت اهمیت با آشنائی
•از بيشتر80%شده ديجيتايز اطالعاتارزش با وهارد روی بر سازمان
دارد قرار شخصي فايلهای و افراد های ديسک.
•تنها0.1نسخ ازBackupاند توانستهRestoreشوند.
•سال در2007تنها ،1/2اند بوده حمله معرض در.
•درسال2008،2/3اند بوده حمله معرض در شرکتها.
•تنها0.1اطالعا امنيت کالسيک دانش با کارمنداني شرکتها کل ازت
دارند.
25. 25© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 25
اطالعات امنیت اهمیت با آشنائی
•ها حفرهیامنيتيافزارها نرم در بزرگیاهم پريسازمان تيدارد وجود
•رفتنين کيرویناراضيناش عواقب ويباق ازيدسترس ماندنيبشبکه ه
داشت خواهد بدنبال جدی خطرات
•شود مي اطالعات دادن دست از باعث طبيعي حوادث
•اخت در را آنها يا شده اطالعات رفتن بين از باعث مجاز غير های نفوذيار
دهدمي قرار رقبا
•ا براحتي را سازماني ارزش با اطالعات مخرب های کد ساير و ها ويروسز
برندمي بين
26. 26© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 26
با آشنائیISMS
پاسخاغلبهاسازماندرمواجههباتهديدات،امنيتيخريدمحصوالتامنيتيمانند
فايروالوهایبرنامهضدويروسوبکارگيریآنهادرهایسيستمکامپيوتریاست.
امااستفادهازترينگرانقيمتمحصوالتامنيتيبدونشناختوتحليلدقيقنيازهای
،امنيتياستفادهازهایرويهاستاندارددر،بکارگيریاطمينانازدانشامنيت
اطالعاتنيرویانسانيواستفادهازکنترلسيستمهایامنيتيوبروزرسانيمداوم
اينهاسيستمبهتنهائيکارسازنخواهندبود
27. 27© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 27
امن سیستم!!
د امنيت تکنولوژی و کامپيوتری عمليات بخش مدير ، اسپافورد آقای نظر طبقانشگاه
، شود مي محسوب امن ،واقعي معنای به که سيستمي تنها ، پردو
•، بوده خاموش که است سيستمي
•، شده کشيده برق اتصال از
•،شده داده قرار تيتانيومي صندوق گاو يک داخل
•درباشد شده دفن بتني بونکر يک
•باشد شده محصور زبده محافظين و اعصاب کشنده گاز با آن پيرامون و.
کنم بندی شرط سيستم اين امنيت روی نيستم حاضر شرايط اين با حتي!
اسپافورد گن
پردو دانشگاه امنيت تکنولوژی و کامپيوتری عمليات بخش مدير
28. 28© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 28
اطالعات امنیت اهمیت با آشنائی
•باشدمي کاری غير مقاصد برای ،کاری ساعات در کاربران بودن آنالين زمان سوم يکWebsense-IDC
•80%غيراخالق هایفيلم دانلود ًاخصوص غيرکاری مقاصد برای اينترنت از شرکت پرسنل که اندکرده اعالم هاشرکتاستفاده ي
اندکردهCSI/FBI
•45%است داده رخ مجاز غير های دسترسي ، سازماني درون هاینيروی توسط که اندکرده اعالم هاشرکتCSI/FBI
•حدود در430کاربر ميليونIMفقط که دارد وجود کاری ساعات در25%از استفاده برای مشخصي قوانين هاشرکتIM
دارند.Silicon.com,
•45%توسط شده دانلود های فايلKazaaهستند ويروسيTrusecure,
•73%باشد مي اخالقي غير هایفيلم خصوا در فيلم اشتراک های شبکه در شده جستجو های فيلمPalisade Systems,
•70%است شده گزارش کاری ساعات در دانلودی پورنو مواردSex Tracker
•37%اند بوده اخالقي غير هایسايت بدنبال کاری ساعات در اينترنت کاربرانComScore Networks
•77%دهد مي رخ اداری ساعات در اينترنتي های تلوزيون و ها راديو از استفادهArbitron
•44%کنند مي استفاده کار محل در اينترنتي تلوزيون و راديو از فعالي صورت به پرسنلNielsen NetRating
•99%ولي دارند ويروس آنتي ها شرکت82%اندشده آلوده ها ويروس توسط که اندکرده اعالمCSI/FBI
29. 29© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 29
اطالعات امنیت اهمیت با آشنائی
بنابراينITما هایتوانمندی افزايش و رفاه باعث که نسبتي همان به
ن فلج را کشور يا و ارگان ،سازمان و بوده خطرناک تواندمي شودميمايد.
استف سوء گونه هر از جلوگيری و آنها مديريت و اطالعات حفظ جهت لذااده
هایاستاندارد و دنيا روز های دستاورد آخرين اساس بر بايست مي
نمود اقدام مربوطه.
30. 30© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 30
با آشنائیISMS
حادثه در اما11ا کمتر در سپتامبرز
اطالعاتي دارائي تمامي روز نیم
بازمیگردد
31. 31© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 31
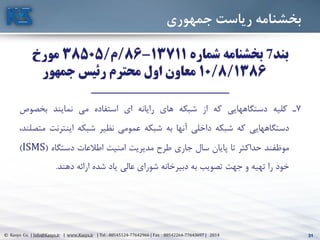
جمهوري رياست بخشنامه
بند7شماره بخشنامه13711-86/م/38505مورخ
10/8/1386جمهور رئیس محترم اول معاون
___________________________________
7تکليهدستگاههاييکهازشبکههایرايانهایاستفادهمينمايندبخصوا
دستگاههاييکهشبکهداخليآنهابهشبکهعمومينظيرشبکهاينترنت،متصلند
موظفندحداکثرتاپايانسالجاریطرحمديريتامنيتاطالعاتدستگاه(ISMS)
خودراتهيهوجهتتصويببهدبيرخانهشورایعالييادشدهارائهدهند.
32. 32© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 32
اطالعات امنیت اهمیت با آشنائی
•ا اطالعات امنيت سيستم يک ايجاد و بررسي امنيت مديريت وظايف از يکيکه ست
باشد سازمان اهداف با متناسب.
•گرفت نظر در را مختلفي عوامل بايد سيستم اين طراحي برای.ارزش محاسبه
تخمي و احتمالي خسارتهای محاسبه و خطرات بررسي ،اقتصادی نظر از اطالعاتن
هزينه-احتم تهديدات بررسي ،اطالعات امنيت سيستم از استفاده سودمندیو الي
سيستمها طراحي برای روش سودمندترين انتخاب و مختلف راهکارهای بررسيی
ميرسد بنظر ضروری اطالعات امنيت
33. 33© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 33
اطالعات امنیت به توجه ضرورت
تمرين
•اط امنيت به مناسب توجه عدم دليل به که نمائيد اشاره مشکالتي به ًالطفبرای العت
است داده رخ شما سازمان
34. 34© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 34
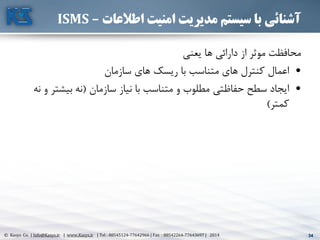
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
يعني ها دارائي از موثر محافظت
•سازمان های ريسک با متناسب های کنترل اعمال
•سازمان نياز با متناسب و مطلوب حفاظتي سطح ايجاد(بيشت نهنه و ر
کمتر)
35. 35© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 35
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
•انگلس کشور در بار اولين اطالعات امنيت حوزه در استاندارد يک ايجاد انديشهتان
گرفت شکل.د اوايل ،آن از ناشي های زيان و امنيتي رخدادهای گسترش پي درهه
90انگلس استاندارد موسسه در اطالعات امنيت یويژه کاری گروه يک ميالدیتان
گرفت شکل.
•سال در گروه اين های فعاليت93اجرايي های دستورالعمل مجموعه تدوين با
نتي به شده آزموده تجارب بهترين از شده برگرفته اطالعات امنيت مديريترسيد جه
استاندارد نسخه اولين انتشار موجب مساله اين وBS 7799سال در95شد.
36. 36© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 36
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
•سرتا در کامپيوتر کاربران نگراني و خبرها تيتر به اطالعات امنيت مرور بهجهان سر
شد تبديل.
•استاندارد بکارگيری با همزمانBS 7799جلوگيری همچنين و سازمانها برخي در
اط امنيت استاندارد يک انتشار برای تقاضا ،کشورها برخي در آن گسترش ازالعات
نظير المللي بين مشخص موسسه يک نظر تحتISOبه منجر و يافت افزايش
«سريع پيگيری»اول بخشBS 7799استاندارد المللي بين موسسه توسطISO
موسسه توسط بار نخستين برای آن انتشار با و شدISOعنوان تحتISO/IEC
17799 : 2000سال دسامبر در2000رسيد خود اوج به.
37. 37© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 37
خانواده با آشنائیISO 27000
•سال در2005اس يک که رسيد نتيجه اين به استاندارد المللي بين موسسهتاندارد
مختلف های حوزه در امنيت برقراری برای جهاني جامعه نياز جوابگوی واحد
باشدنمي.
•مفاهيم و دامنه گسترش و اطالعات امنيت مديريت استاندارد شدن فراگير با،آن
ای مجموعه قالب در را استاندارد اين که رسيدند نتيجه اين به امر متخصصيناز
دهند ارائه مختلف رويکردهای با های استاندارد.سال در نتيجه در2005مجموعه
استاندارد خانوادهISO27000شد ارائه.
•استاندارد خانواده تشکيل به اقدام اينرو ازISO27000مختلف های جنبه که نمود
ميدهد پوشش را امر اين.اند نشده منتشر هنوز استانداردها اين از برخي البتهدر که
يافت خواهد تحقق امر اين نزديک ای آينده.
38. 38© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 38
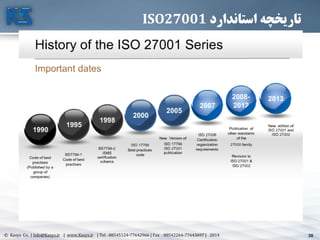
استاندارد تاریخچهISO27001
39. 39© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 39
خانواده با آشنائیISO 27000
•ISO27000خانواده استانداردهای بر مروری و مقدمهISMSمورد رايج واژگان تعريف همراه به
استفاده.
•ISO27001گواهينامه اخذ جهت سازمانها صالحيت احراز منظور به استاندارد الزامات ارائه.
•ISO27002مديريت سيستم کار آييناطالعات امنيت
•ISO27003سازی پياده راهنمایISMS.
•ISO27004اطالعات امنيت مديريت سطح تعيين و گيری اندازه استاندارد.
•ISO27005اطالعات امنيت در ريسک مديريت استاندارد.
•ISO27006گواهينامه دريافت مراحل راهنمای.
•ISO27007بر نظارت و بازرسي راهنمایISMS.
•ISO27011سازی پياده راهنماييISMSمخابرات صنعت در.
•ISO27799سازی پياده راهنمایISMSسالمت حوزه در.
40. 40© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 40
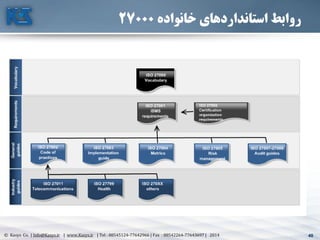
خانواده استانداردهای روابط27000
41. 41© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 41
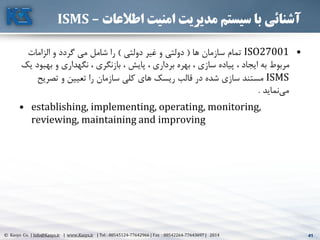
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
•ISO27001ها سازمان تمام(دولتي غير و دولتي)الزامات و گردد مي شامل را
به و نگهداری ، بازنگری ، پايش ، برداری بهره ، سازی پياده ، ايجاد به مربوطيک بود
ISMSتصري و تعيين را سازمان کلي های ريسک قالب در شده سازی مستندح
نمايدمي.
• establishing, implementing, operating, monitoring,
reviewing, maintaining and improving
42. 42© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 42
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
استانداردISO27001يعني خاا مفهوم سه در را اطالعات از حفاظت
.اطالعات بودن بودن محرمانه 1(Confidentiality)
.يکپارچگي يا اطالعات صحت 2(Integrity)
.اطالعات بودن دسترس در 3(Availability)
نمايد مي تعريف.
تبصره:قبيل از خصوصيات ساير اين بر عالوه
•اعتبارAuthenticity،
•پاسخگوييAccountability،
•انکار عدمNon-repudiation
•پذيری اطمينانReliability
باشد مي مدنظر نيز
صحتمحرمانگي
دسترسي قابليت
43. 43© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 43
محرمانگی(Confidentiality)
محافظت سهوی يا و عمدی ، مجاز غير دستکاری از اطالعات اينکه از اطمينان جهت
شوند مي.
نياز که گيرد مي قرار مجازی سازمانهای ،افراد اختيار در فقط اطالعات اينکه وآنها
است شده تاييد اطالعات اين دانستن به.
44. 44© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 44
یکپارچگی(Integrity)
اجازه بدون توانند نمي ها داده:
شوند ايجاد
يابند تغيير
بروند بين از
45. 45© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 45
دستیابی قابلیت(Availability)
•کنتر و اطالعات پردازش جهت استفاده مورد کامپيوتری های سيستم ،اطالعاتل
در اطالعات به نياز زمان در ،اطالعات از حفاظت جهت استفاده مورد امنيتي های
کنند کار کامل طور به و باشند دسترس.
46. 46© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 46
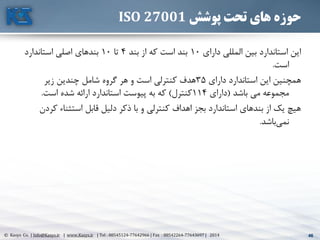
پوشش تحت های حوزهISO 27001
دارای المللي بين استاندارد اين10بند از که است بند4تا10استاندارد اصلي بندهای
است.
دارای استاندارد اين همچنين35زير چندين شامل گروه هر و است کنترلي هدف
باشد مي مجموعه(دارای114کنترل)است شده ارائه استاندارد پيوست به که.
ک استثناء قابل دليل ذکر با و کنترلي اهداف بجز استاندارد بندهای از يک هيچردن
باشدنمي.
47. 47© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 47
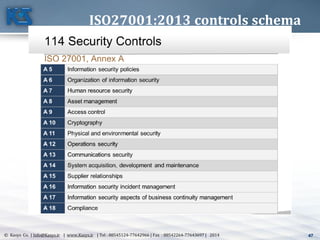
ISO27001:2013 controls schema
48. 48© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 48
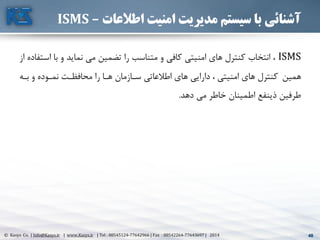
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
ISMSا با و نمايد مي تضمين را متناسب و کافي امنيتي های کنترل انتخاب ،از ستفاده
همينبته و نمتوده محافظتت را هتا ستازمان اطالعاتي های دارايي ، امنيتي های کنترل
دهد مي خاطر اطمينان ذينفع طرفين.
49. 49© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 49
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
ISMSهای سيستم امنيت بتوانند تا دهد مي را امکان اين مديران بهخود
کنند کنترل تجاری و امنيتي های ريسک رساندن حداقل به با را.(PDCA)
در مذکور مشکالت حل راهکار اطالعات امنيت مديريت سيستم
باشد مي اطالعاتي هایسيستم.س بر امنيتي جامع سيستم يکپايه ه
است استوار:
•امنيتي دستورالعملهای و ها سياست
•امنيتي محصوالت و تکنولوژی
•اجرايي عوامل
50. 50© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 50
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
امنیتي دستورالعملهاي و سیاستها:
اطالعاتي هایسيستم از محافظت نحوه برای مرتبط هایبرنامه و طرحهاو
گيرد مي قرار توجه مورد قسمت اين در آنها هایداده.
گرددمي ارائه فني و فنيغير بخش دو در امنيتي استراتژی.
استان انتخاب و مطلوب امنيتي سطوح تعيين شامل غيرفني بخشداردهای
بکارگ برای الزم دستورالعملهای تهيه شامل فني بخش و امنيتيو يری
استراتژيک اهداف به نيل جهت امنيتي سيستم اجزای بر نظارت
باشدمي.
51. 51© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 51
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
امنیتي محصوالت و تکنولوژي:
امني مختلف هایبخش در استفاده مورد ابزارهای تمام شامل قسمت اينتي
باشدمي نظارت و کنترل ، دستورالعملها اعمال برای.محافظ ابزارهایتي
راهکارهای و دسترسي کنترل هایسيستم ، شبکه بر نظارت و
گردندمي مطرح بخش اين در ضدويروس.
52. 52© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 52
اطالعات امنیت مدیریت سیستم با آشنائی–ISMS
اجرايي عوامل:
سيس مديران شامل امنيتي سيستم اجرای و مديريت با مرتبط افرادو هاتم
دارند جای قسمت اين در عادی کاربران و پرسنل ، هاشبکه.عوام اينل
امني دستورالعملهای و سياستها اجرای جهت در ابزارها و تکنولوژی ازتي
کنندمي استفاده.
53. 53© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 53
پوشش تحت های حوزهISO 27001
•تماميالزاماتايناستانداردعموميبودهودرکليه،هاسازمانصرفنظراز،نوع
اندازه،يازمينهفعاليتآنهاقابلاعمالميباشددرصورتامکانهريکازالزامات
ايناستاندارد،بهدليلماهيتونوعفعاليتسازمان،ميتوانآنراناديدهگرفت
•درصورتبروزچنين،استثناييانطباقبااستانداردپذيرفتهنخواهدشدمگراينکه
مشخصشودتاثيریبرتواناييومسئوليتهایسازماندرقبالتامينامنيت
اطالعات(کهبراساسالزاماتامنيتي،قانونيوتشخيصريسکتدوينشاندده)
نخواهدداشت.
•درموردهرگونهاستثناءدرموردکنترلها،سازمانبايدحداکثرميزانقبولريسک
رادرنظرداشتهوهمينطوردرموردارائهمدارکالزمدراينزمينه،تائيدو
پذيرشريسکبوجودآمدهتوسطمسئوالنالزامياست
54. 54© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 54
کاربردISMS
•ISO27001ها سازمان تمام(دولتي غير و دولتي)الزامات و گردد مي شامل را
به و نگهداری ، بازنگری ، پايش ، برداری بهره ، سازی پياده ، ايجاد به مربوطيک بود
ISMSتصري و تعيين را سازمان کلي های ريسک قالب در شده سازی مستندح
نمايدمي.
•مبنای بر اطالعات امنيت مديريت سيستمهادارائي شناسائيم های ريسک وبا رتبط
است شده بنا آن
55. 55© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 55
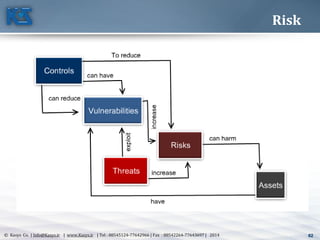
Risk
• Risk is a function of the likelihood of a given threat-
source’s exercising a particular potential vulnerability,
and the resulting impact of that adverse event on the
organization.
56. 56© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 56
ریسک مدیریت(Risk Management)
•پذير آسيب نقاط شناسايي جهت است فرايندی ريسک مديريت(Vulnerability)و
تهديدهای(Threat)اهداف تحقق جهت سازمان نياز مورد اطالعاتي منابع با مرتبط
ت ريسک کاهش جهت پيشگيرانه اقدامات با ارتباط در گيری تصميم و کاریرسيدن ا
اطالعاتي منابع آن ارزش اساس بر ،آن قبول قابل سطح به(.CISA Review Manual 2006)
•ان مي خطر به را اطالعات دارايي که است ضعفي واقع در پذير آسيب نقطه يکدازد.
•دارد را خطر ايجاد پتانسيل که است چيزی تهديد يک.
57. 57© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 57
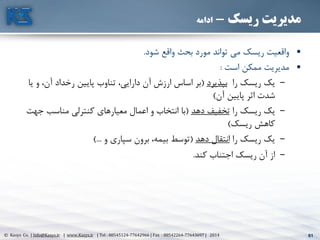
ریسک مدیریت-ادامه
•استف رساني آسيب جهت پذير آسيب نقطه يک از تهديد يک اينکه احتمال،کند اده
کند مي ايجاد را ريسک يک.
•ک مي استفاده پذير آسيب نقطه يک از رساندن آسيب جهت تهديد يک وقتييک ،ند
اثر(Impact)دارد.
•محر و يکپارچگي ،محرمانگي رفتن دست از ،اثر يک ،اطالعات امنيت زمينه درمانگي
شود مي تلقي.
•ها ريسک همه حذف هاو ريسک کليه شناسايي امکان که است تذکر به الزموجود
ندارد.
58. 58© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 58
ریسک مدیریت-ادامه
•ک حوزه آن در دانش دارای که شود مي انجام افراد از تيمي توسط ريسک ارزيابياری
باشند مي خاا.
•صو در يا و کارشناسي نظر اساس بر کيفي تحليل از تواند مي ارزيابي اينوجود رت
نمايد استفاده کمي تحليل از ،گذشته اطالعات و مالي اطالعات.
59. 59© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 59
ریسک مدیریت-ادامه
•است زير موارد بر مشتمل ريسک مديريت فرايند:
–ها دارايي شناسايي،افزارها سخت ،ساختمانها ،افراد شامل آنها ارزش وتخمين
ها داده ،افزارها نرم(غيره و کاغذی يا الکترونيکي)کنندگان تامين ،.
–شامل تهديد ارزيابي:بدخواهانه اقدامات ،تصادفات ،جنگ ،طبيعي اتفاقاتاز
سازمان برون با دورن طرف.
–پذير آسيب نقاط ارزيابيآن قرارگرفتن استفاده مورد احتمال محاسبه و ،.ارزيابي
کنتر ،فيزيکي امنيت ،ها آموزش ،استانداردها ،اجرايي های روش ،ها مشي خطل
فني امنيت ،کيفيت.
60. 60© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 60
ریسک مدیریت-ادامه
•است زير موارد بر مشتمل ريسک مديريت فرايند( :ادامه)
–تهديد يک اثر شدت محاسبهها دارايي روی بر(ا کمي يا کيفي تحليل ازستفاده
کنيد)
–های کنترلکنيد اعمال و انتخاب ،شناسايي را مناسبي.
–مناسبي پاسخب مرتبط هزينه اثربخشي و کارايي گرفتن نظر در با راارزش و آن ا
ببينيد تدارک دارايي آن.
–ارزيابي را کنترلي معيارهای اثربخشيکنيد.ک هزينه که شويد مطمئنها نترل
باشند هم کارا ،کند مي عمل اثربخش طور به که حالي عين در.
61. 61© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 61
ریسک مدیریت-ادامه
•شود واقع بحث مورد تواند مي ريسک واقعيت.
•است ممکن مديريت:
–را ريسک يکبپذيرد(و ،آن رخداد پايين تناوب ،دارايي آن ارزش اساس بريا
آن پايين اثر شدت)
–را ريسک يکدهد تخفيف(ج مناسب کنترلي معيارهای اعمال و انتخاب باهت
ريسک کاهش)
–را ريسک يکدهد انتقال(و سپاری برون ،بيمه توسط)...
–کند اجتناب ريسک آن از.
62. 62© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 62
Risk
63. 63© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 63
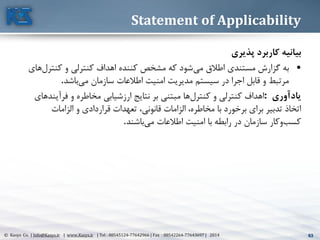
Statement of Applicability
بیانیهپذيري کاربرد
•مي اطالق مستندی گزارش بهکنترل و کنترلي اهداف کننده مشخص که شودهای
مي سازمان اطالعات امنيت مديريت سيستم در اجرا قابل و مرتبطباشد.
يادآوري:کنترل و کنترلي اهداففرآين و مخاطره ارزشيابي نتايج بر مبتني هادهای
،مخاطره با برخورد برای تدبير اتخاذقانوني الزاماتالزامات و قراردادی تعهدات ،
مي اطالعات امنيت با رابطه در سازمان کاروکسبباشند.
64. 64© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 64
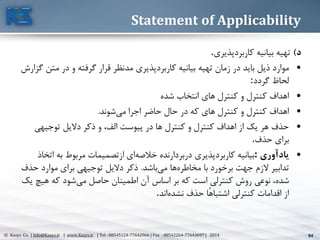
Statement of Applicability
د)کاربرد بيانيه تهيهپذيری.
•کاربرد بيانيه تهيه زمان در بايد ذيل مواردمد پذيریمت در و گرفته قرار نظرگزارش ن
گردد لحاظ:
•شده انتخاب های کنترل و کنترل اهداف
•مي اجرا حاضر حال در که های کنترل و کنترل اهدافشوند.
•الف پيوست در ها کنترل و کنترل اهداف از يک هر حذفتوجيهي داليل ذکر و ،
حذف برای.
•يادآوري:کاربرد بيانيهخالصه دربردارنده پذيریات به مربوط ازتصميمات ایخاذ
مخاطره با برخورد جهت الزم تدابيرمي هاباشد.ح موارد برای توجيهي داليل ذکرذف
شدهمي حاصل اطمينان آن اساس بر که است کنترلي روش نوعي ،هيچ که شوديک
نشده حذف ًاهاشتبا کنترلي اقدامات ازاند.
65. 65© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 65
کاربردISMS
ISMSرود مي شمار به مديريت سيستم از بخشي.
يادآوری:فعاليتت ، ها مشي خط ،ها سياست ، سازماني ساختار ؛ مديريت سيستمهتای
شود مي شامل را فرآيندها و ها رويه ، ها مسئوليت ، ريزی برنامه.
66. 66© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 66
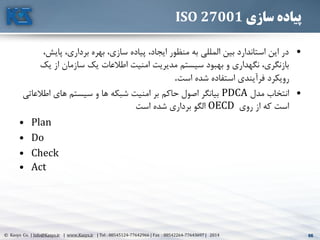
سازی پیادهISO 27001
•پاي ،برداری بهره ،سازی پياده ،ايجاد منظور به المللي بين استاندارد اين در،ش
ي از سازمان يک اطالعات امنيت مديريت سيستم بهبود و نگهداری ،بازنگریک
است شده استفاده فرآيندی رويکرد.
•مدل انتخابPDCAاطال های سيستم و ها شبکه امنيت بر حاکم اصول بيانگرعاتي
روی از که استOECDاست شده برداری الگو
• Plan
• Do
• Check
• Act
67. 67© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 67
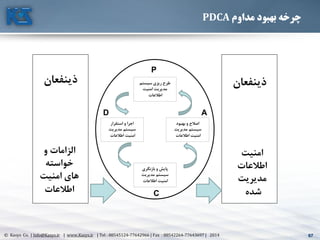
مداوم بهبود چرخهPDCA
ذينفعانذينفعان
و الزامات
خواسته
امنیت هاي
اطالعات
امنیت
اطالعات
مديريت
شده
سیستم ريزي طرح
امنیت مديريت
اطالعات
استقرار و اجرا
سیستممديريت
اطالعات امنیت
بازنگري و پايش
سیستممديريت
اطالعات امنیت
بهبود و اصالح
سیستممديريت
اطالعات امنیت
P
D
C
A
68. 68© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 68
سازی پیادهISO 27001–ریزی برنامه
•مرزهای و کاربرد دامنه تعريفISMSسازمان کار کسب های ويژگي مبنای بر.و ها دارايي ، مکان
فناوری.
•مشي خط تعرفISMSکار و کسب های ويژگي مبنای بر.مکان ، سازمان.آوری فن و ها دارائي.
•سازمان ريسک ارزيابي رويکرد تعريف(ISO/IEC TR13335-3)
•ريسک شناسايي(ها دارائي شناسايي.اموال های تهديد.ه تهديد از ناشي های پذيری آسيبا.
بودن دسترس از ناشي های آسيب.بودن محرمانه.دارائ به دسترسي قابليت و يکپارچگيها ي).
•ريسک ارزيابي و تحليل(امنيتي های نقص بروز احتمال و امنيتي های نقص.)
•ريسک اصالح برای هايي گزينه ارزيابي و شناسائي.
•ريسک اصالح برای ها کنترل و کنترلي اهداف انتخاب.
•پيشنهادی باقيمانده ريسک برای مديريت مصوبه دريافت.
•نمودن عمل و اجرا برای مديريت مجوز دريافتISMS.
•کاربرد قابليت بيانيه تهيه
69. 69© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 69
سازی پیادهISO 27001-اجرا
•ريسک مديريت منظور به ريسک اصالح طرح يک کردن فرمولهISMSمنابع تعيين جهت.
ها الويت و مسئوليتها.
•گ بر در که شده شناسايي کنترلي اهداف به دستيابي منظور به ريسک اصالح طرح اجرایيرنده
کنترلي اهداف تحقق منظور به شده انتخاب های کنترل اجرای مالي مالحظات.
•کنترلي اهداف تحقق منظور به شده انتخاب کنترلهای اجرای.
•به شده انتخاب های کنترل از گروهي يا ها کنترل بخشي اثر گيری اندازه چگونگي تعريفارائه منظور
تجديد قابل و قياس قابل نتايج.
•آگاهي و آموزشي های برنامه اجرا.
•عمليات مديريتISMS. .
•منابع مديريتISMS.
•ها کنترل ديگر و اجرايي های روش اجرا.
70. 70© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 70
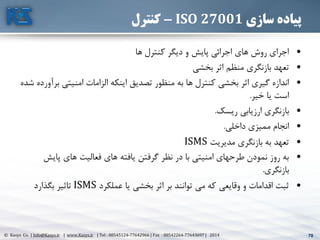
سازی پیادهISO 27001-کنترل
•ها کنترل ديگر و پايش اجرائي های روش اجرای
•بخشي اثر منظم بازنگری تعهد
•ب امنيتي الزامات اينکه تصديق منظور به ها کنترل بخشي اثر گيری اندازهشده رآورده
خير يا است.
•ريسک ارزيابي بازنگری.
•داخلي مميزی انجام.
•مديريت بازنگری به تعهدISMS
•پايش های فعاليت های يافته گرفتن نظر در با امنيتي طرحهای نمودن روز به
بازنگری.
•عملکرد يا بخشي اثر بر توانند مي که وقايعي و اقدامات ثبتISMSبگذارد تاثير
71. 71© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 71
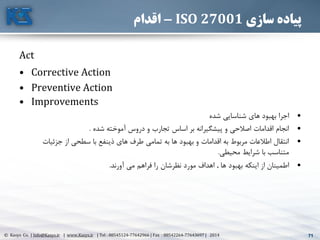
سازی پیادهISO 27001-اقدام
Act
• Corrective Action
• Preventive Action
• Improvements
•شده شناسايي های بهبود اجرا
•شده آموخته دروس و تجارب اساس بر پيشگيرانه و اصالحي اقدامات انجام.
•جزئيات از سطحي با ذينفع های طرف تمامي به ها بهبود و اقدامات به مربوط اطالعات انتقال
محيطي شرايط با متناسب.
•ها بهبود اينکه از اطمينان.آورند مي فراهم را نظرشان مورد اهداف.
72. 72© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 72
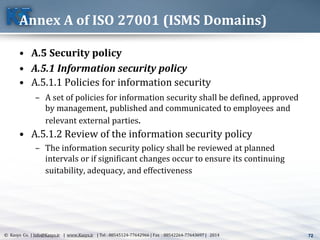
Annex A of ISO 27001 (ISMS Domains)
• A.5 Security policy
• A.5.1 Information security policy
• A.5.1.1 Policies for information security
– A set of policies for information security shall be defined, approved
by management, published and communicated to employees and
relevant external parties.
• A.5.1.2 Review of the information security policy
– The information security policy shall be reviewed at planned
intervals or if significant changes occur to ensure its continuing
suitability, adequacy, and effectiveness
73. 73© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 73
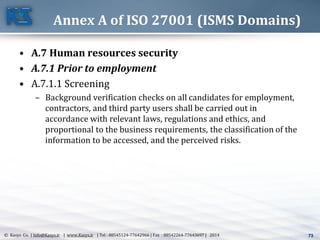
Annex A of ISO 27001 (ISMS Domains)
• A.7 Human resources security
• A.7.1 Prior to employment
• A.7.1.1 Screening
– Background verification checks on all candidates for employment,
contractors, and third party users shall be carried out in
accordance with relevant laws, regulations and ethics, and
proportional to the business requirements, the classification of the
information to be accessed, and the perceived risks.
74. 74© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 74
Annex A of ISO 27001 (ISMS Domains)
• A.7 Human resources security
• A.7.2 During employment
• A.7.2.1 Management responsibilities
– Management shall require employees, contractors and third party
users to apply security in accordance with established policies and
procedures of the organization
• A.7.2.2 Information security awareness, education and
training
– All employees of the organization and, where relevant, contractors
and third party users shall receive appropriate awareness training
and regular updates in organizational policies and procedures, as
relevant for their job function
75. 75© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 75
Annex A of ISO 27001 (ISMS Domains)
• A.7 Human resources security
• A.7.2 During employment
• A.7.2.3 Disciplinary process
– There shall be a formal disciplinary process for employees who
have committed a security breach
76. 76© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 76
Annex A of ISO 27001 (ISMS Domains)
• A.7 Human resources security
• A.7.3 Termination or change of employment
• A.7.3.1 Termination or change of employment responsibilities
– Information security responsibilities and duties that remain valid
after termination or change of employment shall be defined,
communicated to the employee or contractor and enforced.
77. 77© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 77
Annex A of ISO 27001 (ISMS Domains)
• A.8 Asset Management
• A.8.1 Responsibility for assets
• A.8.1.1 Inventory of assets
– Assets associated with information and information processing
facilities shall be identified and an inventory of these assets shall be
drawn up and maintained.
78. 78© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 78
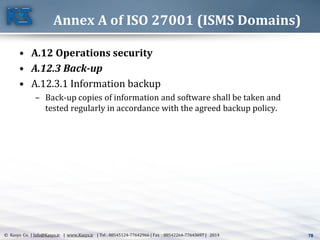
Annex A of ISO 27001 (ISMS Domains)
• A.12 Operations security
• A.12.3 Back-up
• A.12.3.1 Information backup
– Back-up copies of information and software shall be taken and
tested regularly in accordance with the agreed backup policy.
79. 79© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 79
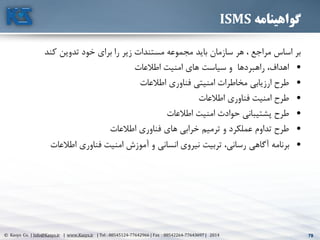
گواهینامهISMS
کند تدوين خود برای را زير مستندات مجموعه بايد سازمان هر ، مراجع اساس بر
•اطالعات امنيت های سياست و راهبردها ،اهداف
•اطالعات فناوری امنيتي مخاطرات ارزيابي طرح
•اطالعات فناوری امنيت طرح
•اطالعات امنيت حوادث پشتيباني طرح
•اطالعات فناوری های خرابي ترميم و عملکرد تداوم طرح
•اطالعات فناوری امنيت آموزش و انساني نيروی تربيت ،رساني آگاهي برنامه
80. 80© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 80
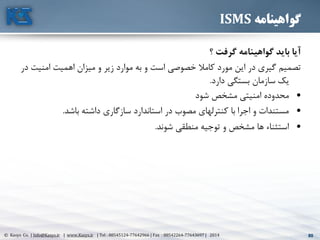
گواهینامهISMS
؟ گرفت گواهینامه بايد آيا
امني اهميت ميزان و زير موارد به و است خصوصي کامال مورد اين در گيری تصميمدر ت
يکدارد بستگي سازمان.
•شود مشخص امنيتي محدوده
•باشد داشته سازگاری استاندارد در مصوب کنترلهای با اجرا و مستندات.
•شوند منطقي توجيه و مشخص ها استثناء.
81. 81© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 81
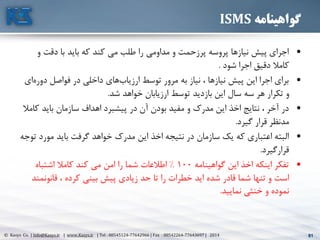
گواهینامهISMS
•و دقت با بايد که کند مي طلب را مداومي و پرزحمت پروسه نيازها پيش اجرای
دقيق کامالشود اجرا.
•دور فواصل در داخلي هایارزياب توسط مرور به نياز ، نيازها پيش اين اجرا برایایه
ارزيابان توسط بازديد اين سال سه هر تکرار وشد خواهد.
•ک بايد سازمان اهداف پيشبرد در آن بودن مفيد و مدرک اين اخذ نتايج ، آخر درامال
مدنظرگيرد قرار.
•مورد بايد گرفت خواهد مدرک اين اخذ نتيجه در سازمان يک که اعتباری البتهتوجه
قرارگيرد.
•گواهينامه اين اخذ اينکه تفکر100%اشتباه کامال کند مي امن را شما اطالعات
تنها و استقانونمن ، کرده بيني پيش زيادی حد تا را خطرات ايد شده قادر شماد
نماييد خنثي و نموده.
82. 82© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 82
Likelihood
Analysis
Risk
Determination
83. 83© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 83
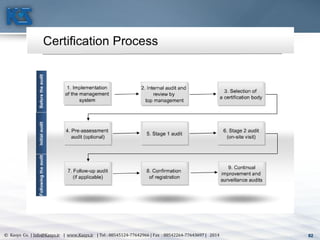
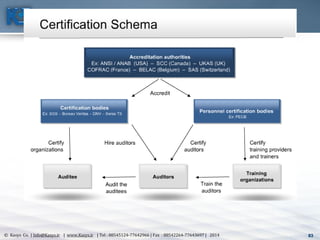
84. 84© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 84
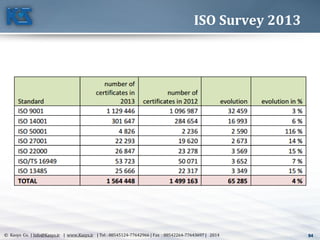
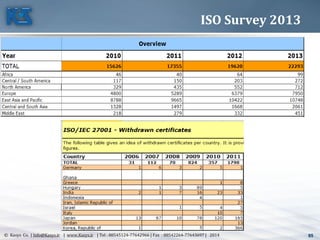
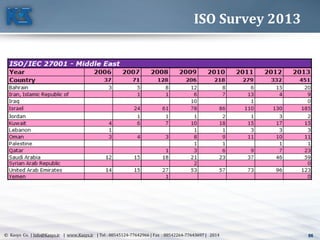
ISO Survey 2013
85. 85© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 85
ISO Survey 2013
86. 86© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 86
ISO Survey 2013
87. 87© Kasys Co. | Info@Kasys.ir | www.Kasys.ir | Tel : 88545124-77642966 | Fax : 88542264-77643697 | 2014 87
گواهینامه نمونه
88. KASYS
Karbord System engineering group co.
سدیدمتسیسارربدکیسندمهروهگ
(سیساک)
شماست فردای فرصت امروز بصیرتToday’s Insight is Tomorrow's Opportunity
Special Thanks for your kind
attentions