Java 8 lambda
•Download as PPTX, PDF•
0 likes•24 views
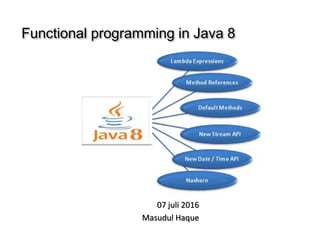
Functional programming in Java 8
Report
Share
Report
Share
Recommended
Java8 training - Class 1

This is a 3 part series on Java8 Features. Drop me an email for a discussion - singh.marut@gmail.com
Code is available at https://github.com/singhmarut/java8training
Videos available at my youtube channel https://www.youtube.com/channel/UCBM4yHwfjQ_syW6Lz8kYpmA
Java8 training - class 3

This is a 3 part series on Java8 Features. Drop me an email for a discussion - singh.marut@gmail.com
https://github.com/singhmarut/java8training
Videos available at my youtube channel https://www.youtube.com/channel/UCBM4yHwfjQ_syW6Lz8kYpmA
Streams or Loops? Java 8 Stream API by Niki Petkov - Proxiad Bulgaria

Presentation from the visit of Proxiad Bulgaria - partner for the Java Course in Hack Bulgaria.
The topic is the new Stream API in Java 8 and the presenter - Nikolay Petkov from Proxiad Bulgaria
Introduction to JavaScript Programming

What is JavaScript?
Interpreted programming or scripting language from Netscape.
Easier to code than the compiled languages like C and C++.
Lightweight and most commonly used script in web pages.
Allow client-side user to interact and create dynamic pages.
Cross-platform and object-oriented scripting language.
Most popular programming language in the world.
High level, dynamic and untyped programming language.
Standardized in the ECMAScript language specification.
Used for shorter programs
Takes longer time to process than compiled languages.
Java 8 Streams And Common Operations By Harmeet Singh(Taara)

In this, we are discuss about Java 8 Streams. Common Operations . Java 8 Streams are huge topic, so i am not cover all the things, but try to cover the basics operations of Streams. Before this, please refer my previous presentation "Functional programming in java 8", because of clear some basic concept for functional programming. For the reference use Java 8 API docs.
Dax Declarative Api For Xml

DAX is a declarative API for processing XML in Java or Javascript that integrates into Cocoon and re-uses important concepts of XPath and XSLT.
Recommended
Java8 training - Class 1

This is a 3 part series on Java8 Features. Drop me an email for a discussion - singh.marut@gmail.com
Code is available at https://github.com/singhmarut/java8training
Videos available at my youtube channel https://www.youtube.com/channel/UCBM4yHwfjQ_syW6Lz8kYpmA
Java8 training - class 3

This is a 3 part series on Java8 Features. Drop me an email for a discussion - singh.marut@gmail.com
https://github.com/singhmarut/java8training
Videos available at my youtube channel https://www.youtube.com/channel/UCBM4yHwfjQ_syW6Lz8kYpmA
Streams or Loops? Java 8 Stream API by Niki Petkov - Proxiad Bulgaria

Presentation from the visit of Proxiad Bulgaria - partner for the Java Course in Hack Bulgaria.
The topic is the new Stream API in Java 8 and the presenter - Nikolay Petkov from Proxiad Bulgaria
Introduction to JavaScript Programming

What is JavaScript?
Interpreted programming or scripting language from Netscape.
Easier to code than the compiled languages like C and C++.
Lightweight and most commonly used script in web pages.
Allow client-side user to interact and create dynamic pages.
Cross-platform and object-oriented scripting language.
Most popular programming language in the world.
High level, dynamic and untyped programming language.
Standardized in the ECMAScript language specification.
Used for shorter programs
Takes longer time to process than compiled languages.
Java 8 Streams And Common Operations By Harmeet Singh(Taara)

In this, we are discuss about Java 8 Streams. Common Operations . Java 8 Streams are huge topic, so i am not cover all the things, but try to cover the basics operations of Streams. Before this, please refer my previous presentation "Functional programming in java 8", because of clear some basic concept for functional programming. For the reference use Java 8 API docs.
Dax Declarative Api For Xml

DAX is a declarative API for processing XML in Java or Javascript that integrates into Cocoon and re-uses important concepts of XPath and XSLT.
Functional programming in java 8 by harmeet singh

Cover Basic concept for Functional Programming in Java. Define new functional interfaces, lambda expressions, how to translate lambda expression, JVM deal with new byte code etc. This is not the perfect slides for functional programming, but trying cover simple basic functional programming.
JavaScript - Chapter 6 - Basic Functions

A JavaScript function is a block of code designed to perform a particular task.
Why Functions?
You can reuse code: Define the code once, and use it many times. You can use the same code many times with different arguments, to produce different results.
Programming with Lambda Expressions in Java 

Slides from conference session at jdays 2013. Covers Lambda expressions in Java 8 and how to use them effectively.
Object Relational Mapping in PHP

"Object Relational Mapping in PHP"
Presentation given to PHPNW on 05/05/09 by Rob Knight
Java 8 Lambda Expressions

Java 8 Lambda Expressions as presented at Hyderabad Scalbility Meetup http://www.meetup.com/hyderabad-scalability/events/219664588/ by Prasad.G
Building Data Mapper PHP5

See all the steps involved to build a fully functional data mapper with object-oriented PHP5 using the power and simplicity of the Standard PHP Library. Based on the early development of a new PHP DataMapper project Vance Lucas started a few months ago as the Model layer for an MVC framework.
Introduction to Java 8

Introduction to functional structures in Java 8 Like Lambda expressions, Default methods, Method references, Stream API etc.
Lessons Learnt With Lambdas and Streams in JDK 8

A number of lessons learnt whilst understanding the realities of using Lambda expressions and the Streams API in JDK 8.
How to debug slow lambda response times

One of the most common performance issues in serverless architectures is elevated latencies from external services, such as DynamoDB, ElasticSearch or Stripe.
In this webinar, we will show you how to quickly identify and debug these problems, and some best practices for dealing with poor performing 3rd party services.
More Related Content
What's hot
Functional programming in java 8 by harmeet singh

Cover Basic concept for Functional Programming in Java. Define new functional interfaces, lambda expressions, how to translate lambda expression, JVM deal with new byte code etc. This is not the perfect slides for functional programming, but trying cover simple basic functional programming.
JavaScript - Chapter 6 - Basic Functions

A JavaScript function is a block of code designed to perform a particular task.
Why Functions?
You can reuse code: Define the code once, and use it many times. You can use the same code many times with different arguments, to produce different results.
Programming with Lambda Expressions in Java 

Slides from conference session at jdays 2013. Covers Lambda expressions in Java 8 and how to use them effectively.
Object Relational Mapping in PHP

"Object Relational Mapping in PHP"
Presentation given to PHPNW on 05/05/09 by Rob Knight
Java 8 Lambda Expressions

Java 8 Lambda Expressions as presented at Hyderabad Scalbility Meetup http://www.meetup.com/hyderabad-scalability/events/219664588/ by Prasad.G
Building Data Mapper PHP5

See all the steps involved to build a fully functional data mapper with object-oriented PHP5 using the power and simplicity of the Standard PHP Library. Based on the early development of a new PHP DataMapper project Vance Lucas started a few months ago as the Model layer for an MVC framework.
What's hot (8)
Similar to Java 8 lambda
Introduction to Java 8

Introduction to functional structures in Java 8 Like Lambda expressions, Default methods, Method references, Stream API etc.
Lessons Learnt With Lambdas and Streams in JDK 8

A number of lessons learnt whilst understanding the realities of using Lambda expressions and the Streams API in JDK 8.
How to debug slow lambda response times

One of the most common performance issues in serverless architectures is elevated latencies from external services, such as DynamoDB, ElasticSearch or Stripe.
In this webinar, we will show you how to quickly identify and debug these problems, and some best practices for dealing with poor performing 3rd party services.
Java gets a closure

Presentation from Krakow Java Developers Day 2011 about future of Java - closures, defender methods etc.
Java 8 Intro - Core Features

This presentaion provides and overview of the new features of Java 8, namely default methods, functional interfaces, lambdas, method references, streams and Optional vs NullPointerException.
This presentation by Arkadii Tetelman (Lead Software Engineer, GlobalLogic) was delivered at Java.io 3.0 conference in Kharkiv on March 22, 2016.
A Brief Conceptual Introduction to Functional Java 8 and its API

A simple introduction to the new functional programming facilities in Java 8, including an overview of the API and classification by use case.
Similar to Java 8 lambda (20)
Advanced Data Science on Spark-(Reza Zadeh, Stanford)

Advanced Data Science on Spark-(Reza Zadeh, Stanford)
A Brief Conceptual Introduction to Functional Java 8 and its API

A Brief Conceptual Introduction to Functional Java 8 and its API
More from Masudul Haque
More from Masudul Haque (6)
Recently uploaded
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
The Metaverse and AI: how can decision-makers harness the Metaverse for their...

The Metaverse is popularized in science fiction, and now it is becoming closer to being a part of our daily lives through the use of social media and shopping companies. How can businesses survive in a world where Artificial Intelligence is becoming the present as well as the future of technology, and how does the Metaverse fit into business strategy when futurist ideas are developing into reality at accelerated rates? How do we do this when our data isn't up to scratch? How can we move towards success with our data so we are set up for the Metaverse when it arrives?
How can you help your company evolve, adapt, and succeed using Artificial Intelligence and the Metaverse to stay ahead of the competition? What are the potential issues, complications, and benefits that these technologies could bring to us and our organizations? In this session, Jen Stirrup will explain how to start thinking about these technologies as an organisation.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
Quantum Computing: Current Landscape and the Future Role of APIs

The current state of quantum computing and the role of APIs to take it mainstream.
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Recently uploaded (20)
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
The Metaverse and AI: how can decision-makers harness the Metaverse for their...

The Metaverse and AI: how can decision-makers harness the Metaverse for their...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Quantum Computing: Current Landscape and the Future Role of APIs

Quantum Computing: Current Landscape and the Future Role of APIs
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
Java 8 lambda
- 1. Functional programming in Java 8 07 juli 2016 Masudul Haque
- 2. Adapt : Learn functional programming
- 3. Java meets functional programming (with lambdas)
- 4. Java is not your grandma’s language anymore!
- 6. Before Lambda List<Employee> employees = ... double highestSalary = 0.0; for (Employee e : employees) { if (e.year == 2016) { if (e.salary > highestSalary) { highestSalary = e.salary; } } } • Client controls iteration • Inherently serial: iterate from beginning to end • Not thread-safe
- 7. After Lambda List<Employee> employees = ... double highestSalary = employees.stream() .filter(Employee e-> e.getYear() == 2016) .map(e -> e.getSalary()) .max(); • More readable • More abstract • Less error-prone • No reliance on mutable state • Easier to make parallel
- 8. What is Lambda? • Lambda expressions represent anonymous functions – Like a method, has a typed argument list, a return type, a set of thrown exceptions, and a body – Not associated with a class List<Employee> employees = ... double highestSalary = employees.stream() .filter(Employee e-> e.getYear() == 2016) .map(e -> e.getSalary()) .max(); Predicate Function
- 9. What is Lambda? List<Employee> employees = ... double highestSalary = employees.stream() .filter(Employee e-> e.getYear() == 2016) .map(e -> e.getSalary()) .max(); • Stream<T> filter(Predicate<? super T> predicate) • Filter objects that match a Predicate object • <R> Stream<R> map(Function<? super T, ? extends R> mapper) • Map objects to another value as specified by a Function object Predicate Function
- 10. What is Functional programming? • Functional languages view programs as an entity— called a function— that accepts inputs and produces output • Functions are connected together by their outputs to other functions’ inputs. • Underlying approach: “Evaluate an expression. Then use the results for something else.”
- 11. Example Runnable r = new Runnable(){ public void run(){ System.out.println("Hello World"); } }; Runnable r =()-> System.out.println("Hello World");
- 12. Stream
- 13. What is Stream? • A Typed Interface. public interface Stream<T> extends BaseStream<T,Stream<T>> • Abstraction for specifying aggregate computations – Not a data structure – Can be infinite • Simplifies the description of aggregate computations – Exposes opportunitires for optimisation – Fusing, laziness and parrallelism
- 14. What is Stream? • What can I do with it? Answer: efficiently process high volumes of data, but also small ones. • What does efficiently mean? Two things: 1. In parallel, to leverage multicore CPU 2. In pipeline, to avoid the computation of intermediate data structures
- 15. Stream Pipeline A stream pipeline consists of three types of things 1. A source 2. Zero or more intermediate operations 3. A terminal operation List<Employee> employees = ... double highestSalary = employees.stream() .filter(Employee e-> e.getYear() == 2016) .map(e -> e.getSalary()) .max(); Intemediate Operation Source Terminal Operation Intemediate Operations
- 16. stream pipeline Stream source Intermediate operations Terminal operation stream stream Examples: IntStream.range(), Arrays.stream() Examples: map(), filter(), distinct(), sorted() Examples: sum(), collect(), forEach(), reduce()
- 17. DoubleStream. of(1.0, 4.0, 9.0) map(Math::sqrt) .peek(System.out:: println) Stream Source (with elements 1.0, 4.0, and 9.0) Intermediate Operation 1 (maps to element values 1.0, 2.0, and 3.0) Intermediate Operation 2 (prints 1.0, 2.0, and 3.0) .sum(); Terminal Operation (returns the sum 6.0) DoubleStream.of(1.0, 4.0, 9.0) .map(Math::sqrt) .peek(System.out::println) .sum();
- 18. Stream.of (1, 2, 3, 4, 5) .map(i -> i * i) .peek(i -> System.out.printf("%d ",i)) .count(); prints: 1 4 9 16 25
- 19. Demo long startTime = System.currentTimeMillis(); long numOfPrimes = LongStream.rangeClosed(2, 10_000_000) .filter(PrimeNumbers::isPrime) .count(); System.out.println(numOfPrimes); long endTime = System.currentTimeMillis(); System.out.printf( " Duration : %f %n ",(endTime - startTime)/1000.0);
- 21. long numOfPrimes =LongStream.rangeClosed(2, 10_000_000) .filter(PrimeNumbers::isPrime) .count(); System.out.println(numOfPrimes); Prints 664579 8.501 seconds
- 22. Parallel code Serial code Let’s flip the switch by calling parallel() function
- 23. long numOfPrimes =LongStream.rangeClosed(2, 10_000_000) .parallel() .filter(PrimeNumbers::isPrime) .count(); System.out.println(numOfPrimes); Prints 664579 2.041 seconds
- 24. Wow! That’s an awesome flip switch!
- 25. Internally, parallel streams make use of fork-join framework
- 26. Q & A
- 27. Contact For any question Email: M.Haque@cimsolutions.nl Follow me in following site: Stackoverflow http://stackoverflow.com/users/1265660/masud Github https://github.com/masudcse05 Blog https://masudulhaque.wordpress.com
