More Related Content
PDF
SCADA Cyber Sec | ISACA 2013 | Patricia Watson PPTX
SANS ICS Security Survey Report 2016 PPTX
Dubai Cyber Security 01 Ics Scada Cyber Security Solutions and Challenges... PDF
ARC's Bob Mick Cyber Security Presentation @ ARC Industry Forum 2010 PDF
PDF
2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabili... PPTX
Mapping the Enterprise Threat, Risk, and Security Control Landscape with Splunk PPTX
Viewers also liked
PPTX
Indonesia National Cyber Security Strategy PDF
Key Findings from the 2015 IBM Cyber Security Intelligence Index PPT
Channel Sales Presentation PDF
Greater China Cyber Threat Landscape - ISC 2016 PPTX
Hackers, Cyber Crime and Espionage PDF
Top Cyber Security Trends for 2016 PPTX
25 Disruptive Technology Trends 2015 - 2016 More from Renny
PPSX
PPSX
PPSX
PPSX
PPSX
PPSX
PPSX
Pictures speak for themselves PPSX
Get to know your inner world PPSX
Looking for something more PPSX
PPSX
PPSX
PPSX
Photos brighten my day... PPSX
PPSX
PPSX
PPSX
Get to know yourself, you'll see the world PPSX
PPSX
PPSX
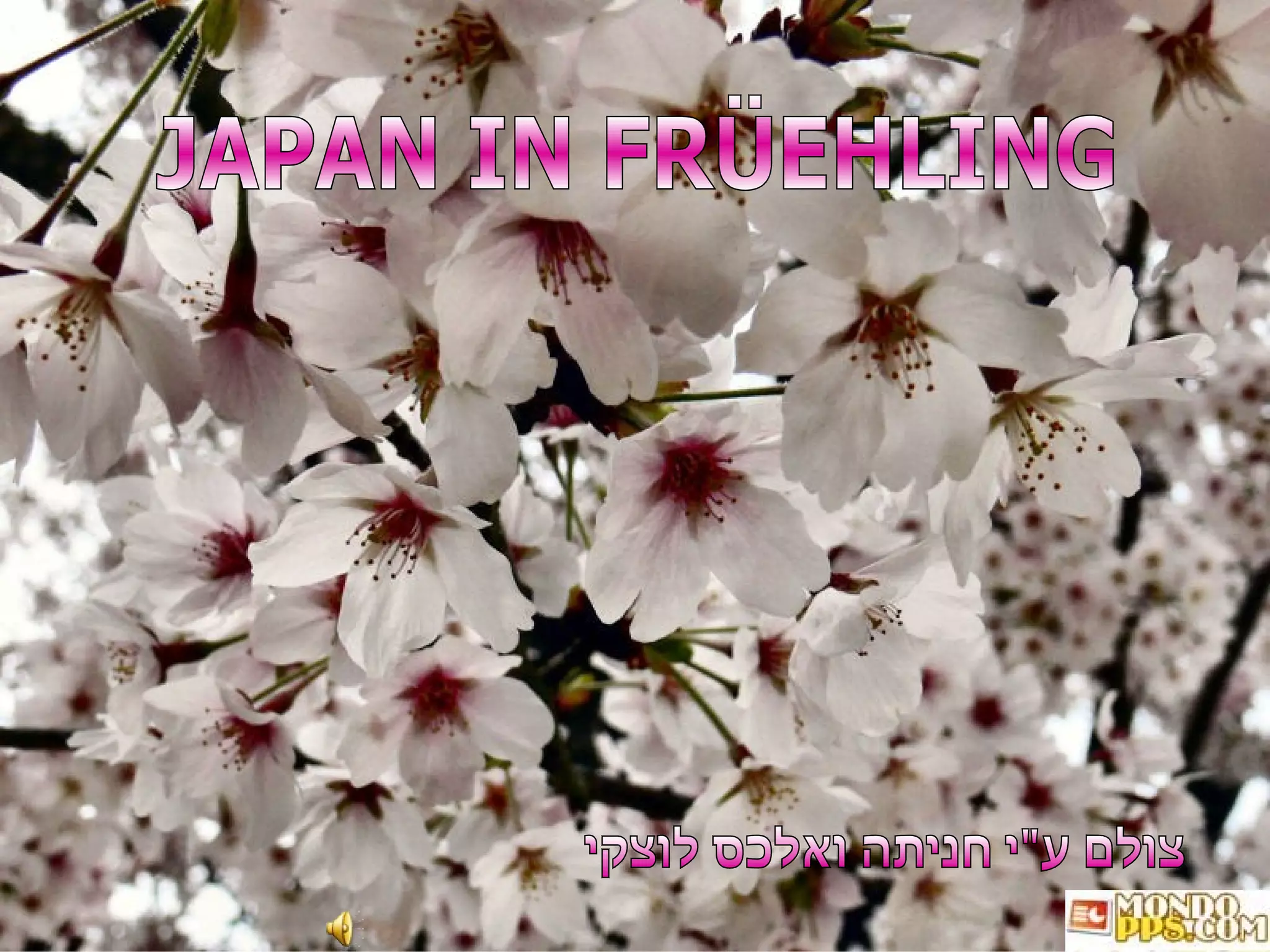
Love you with all my heart Japan In FrüEhling Hh
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
- 31.
- 32.
- 33.
- 34.
- 35.
- 36.
- 37.
- 38.
- 39.
- 40.
- 41.
- 42.
- 43.
- 44.
- 45.