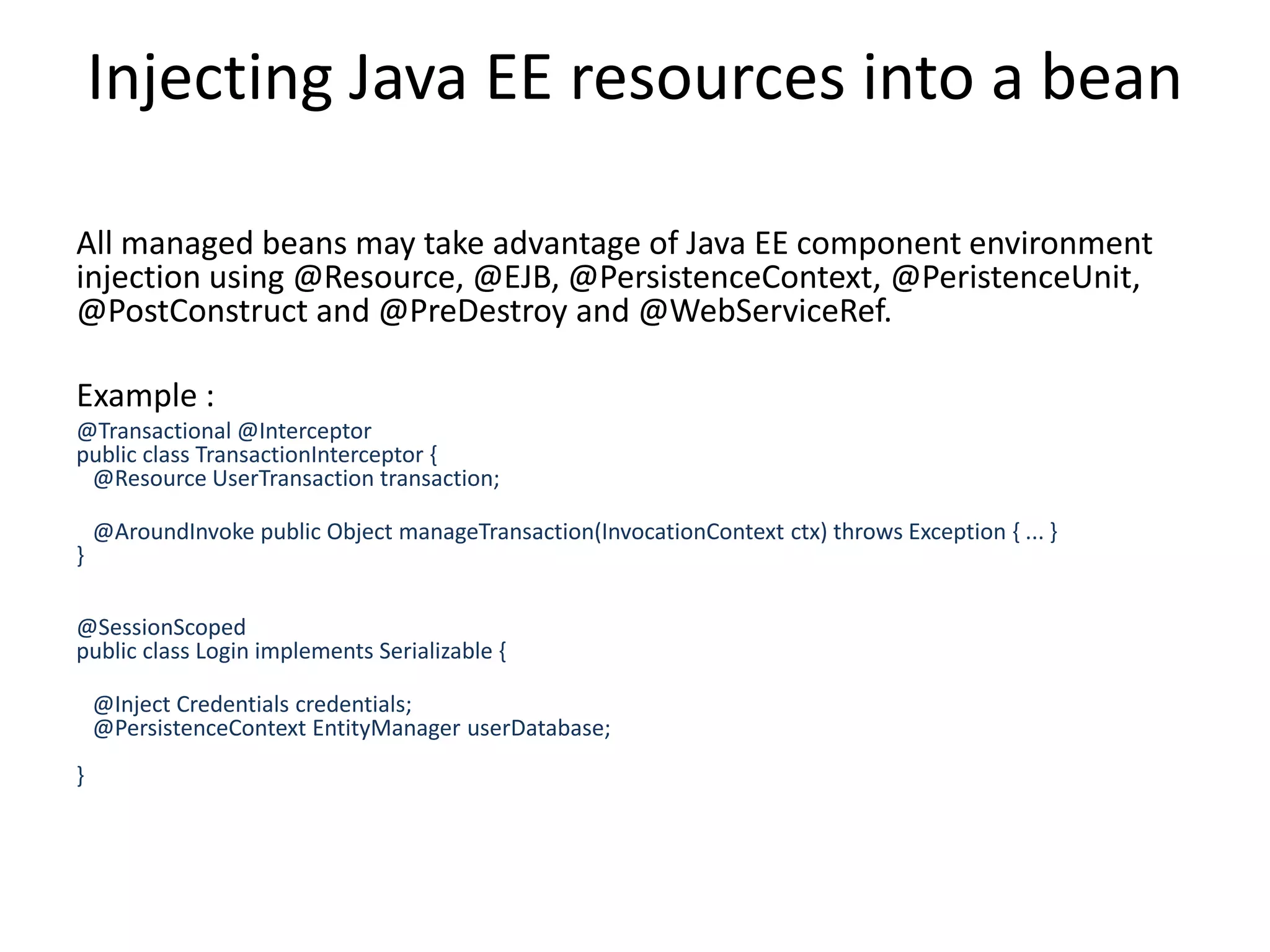
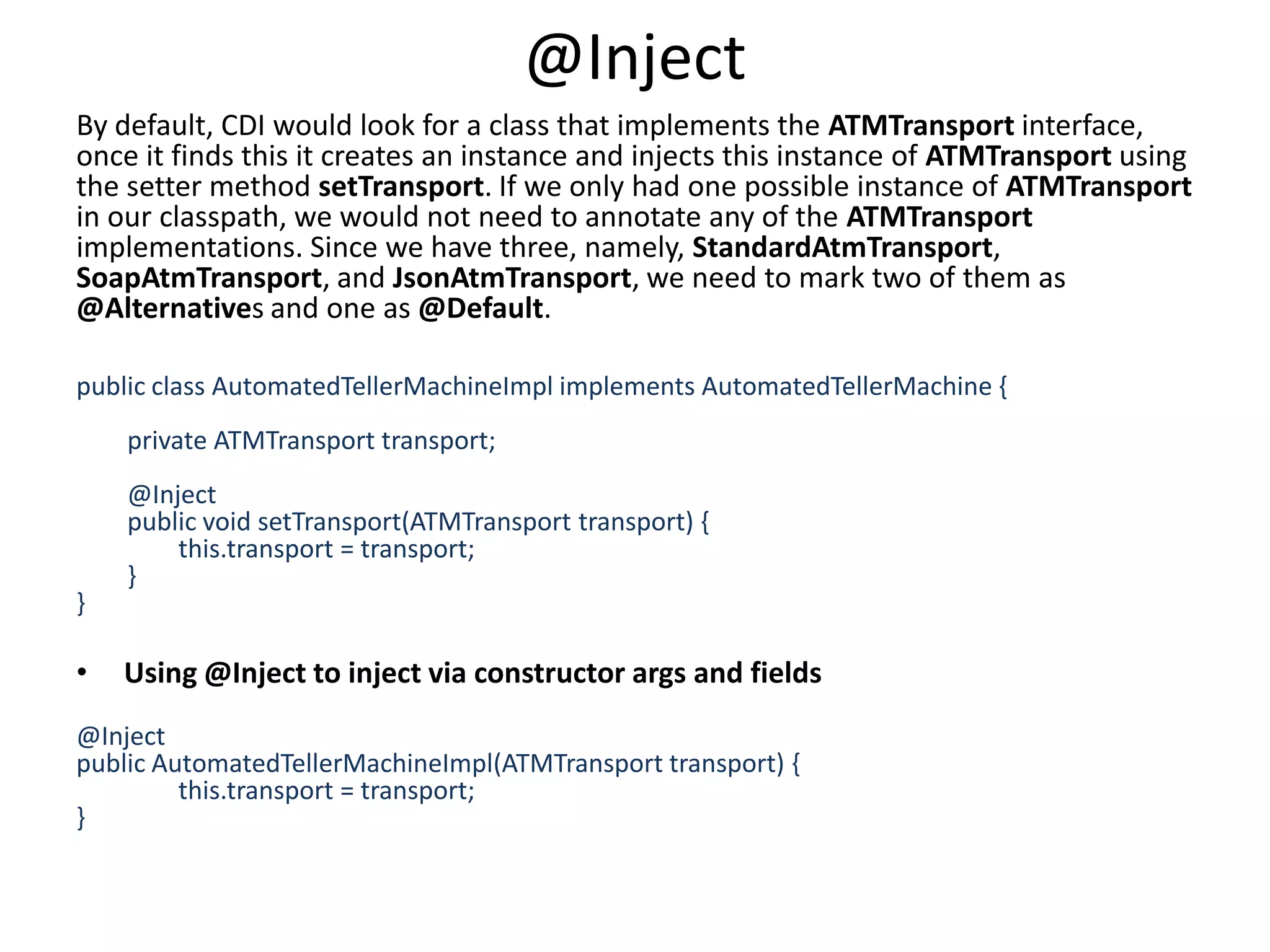
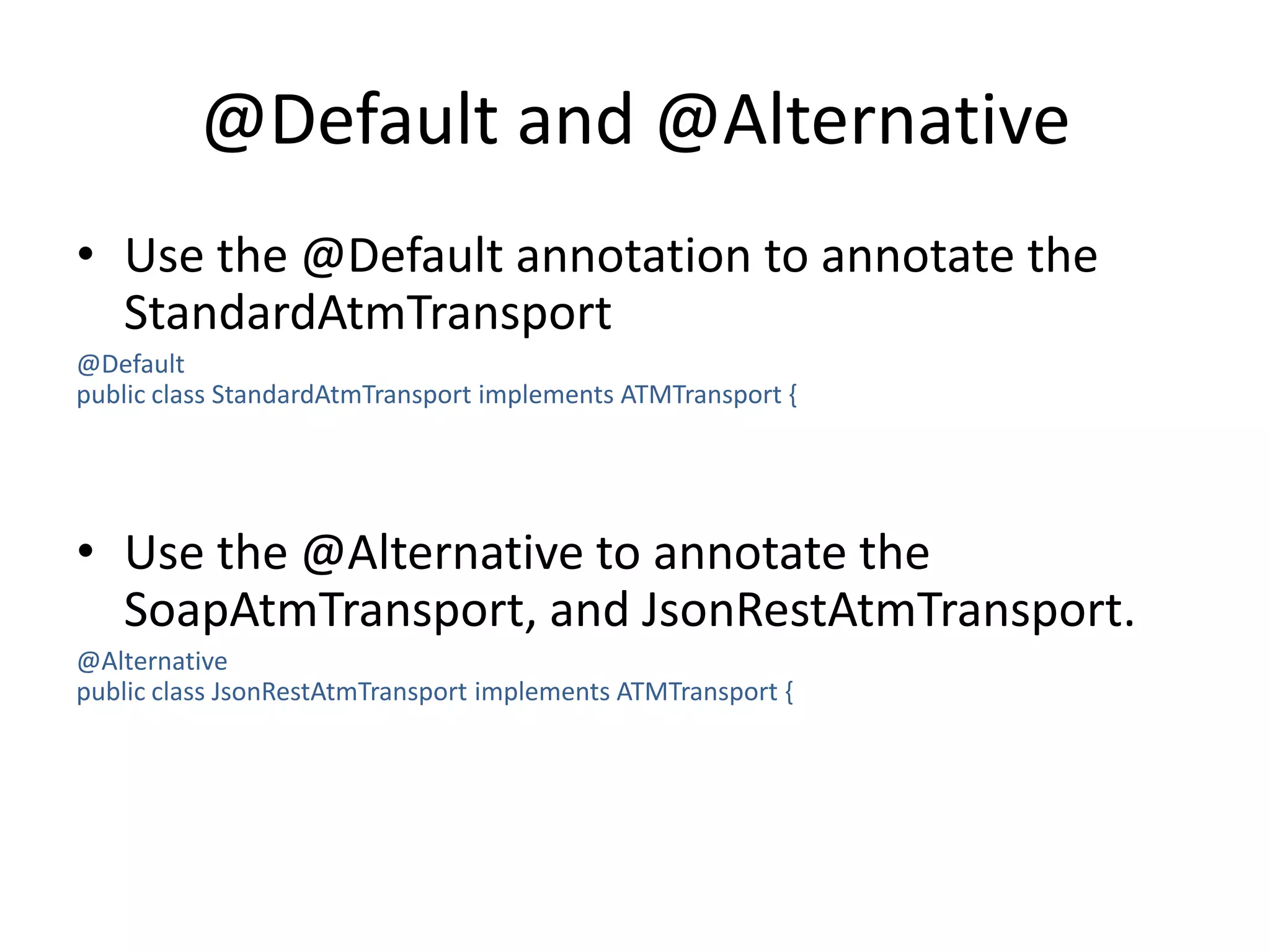
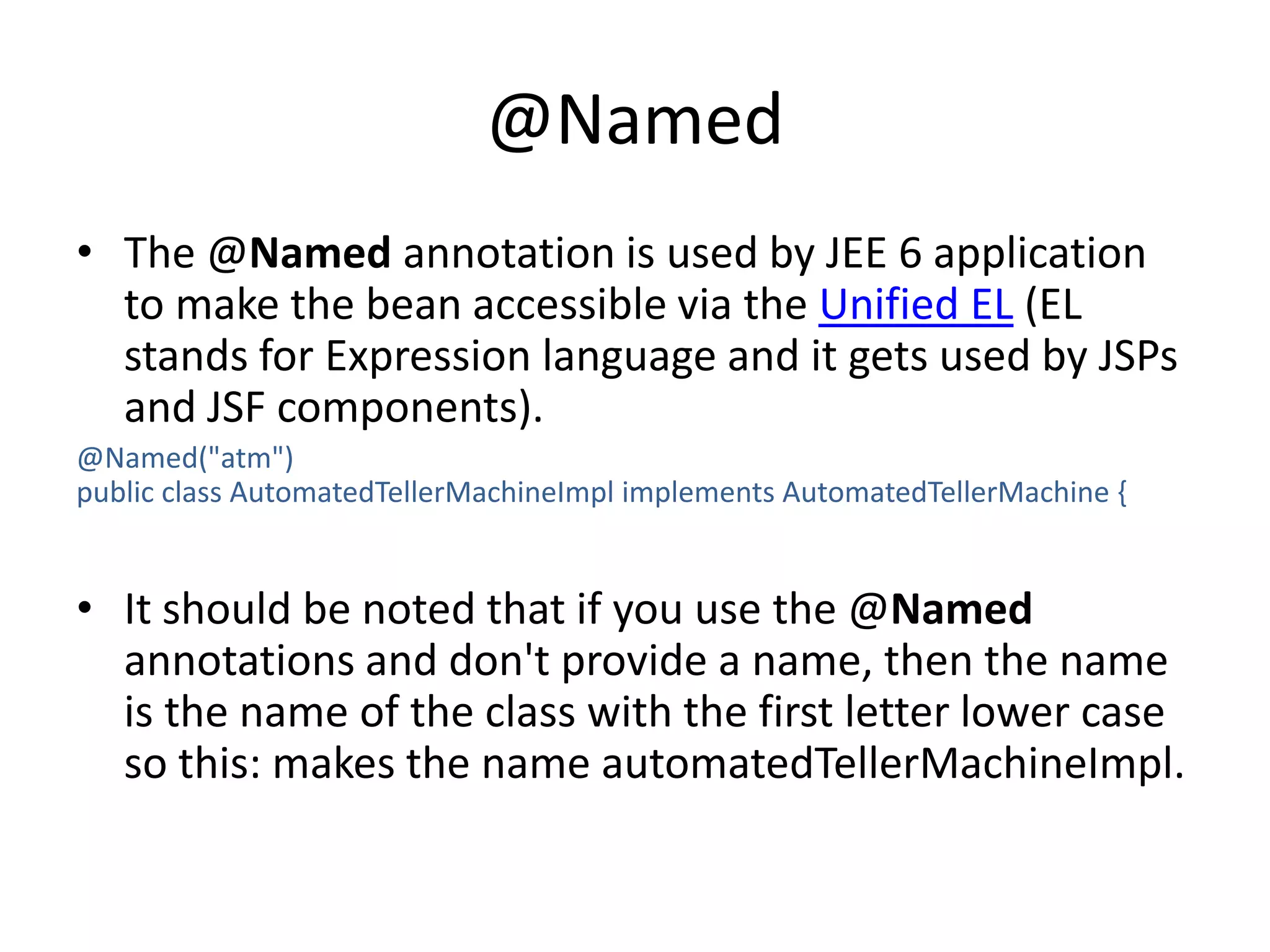
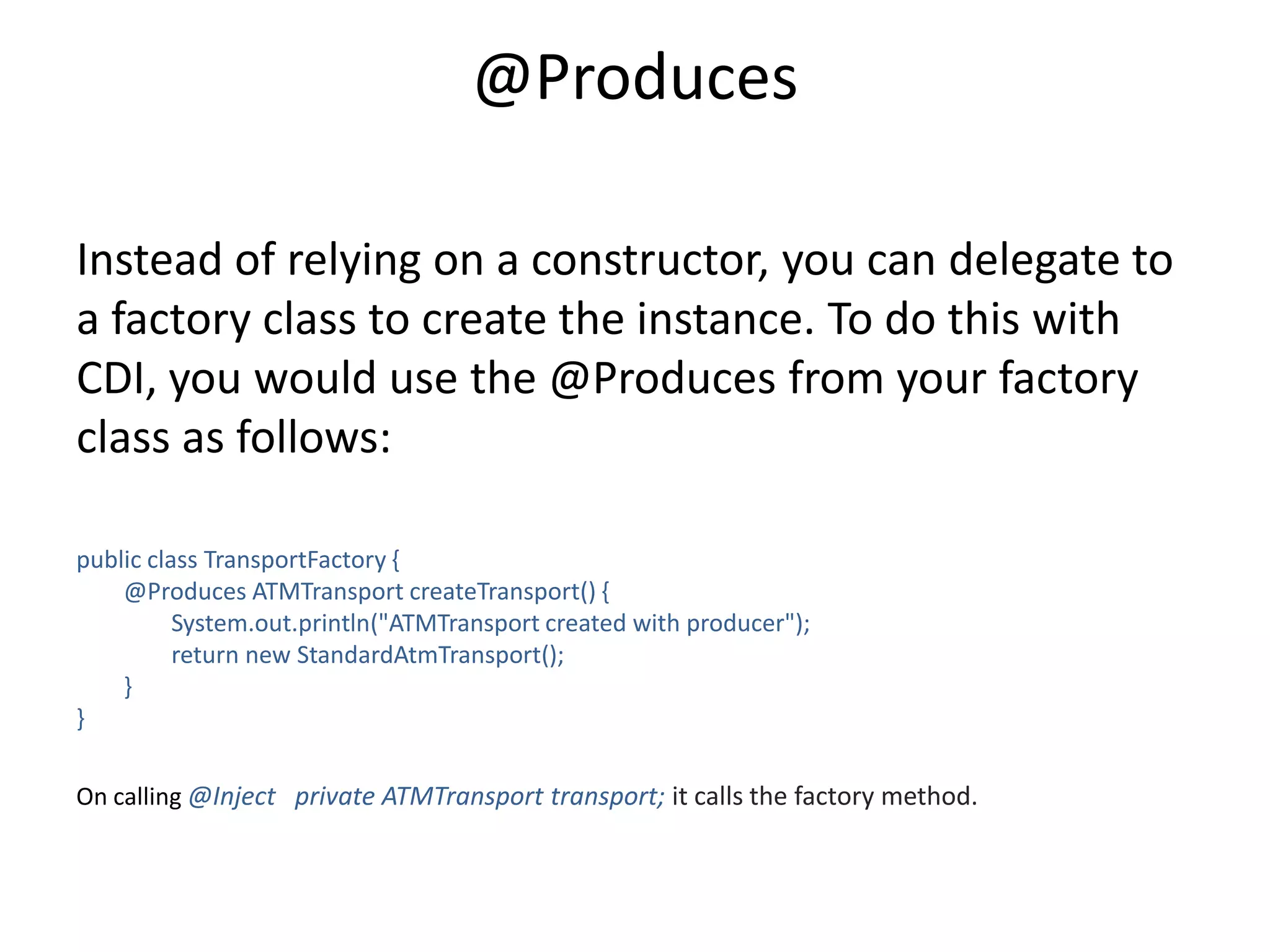
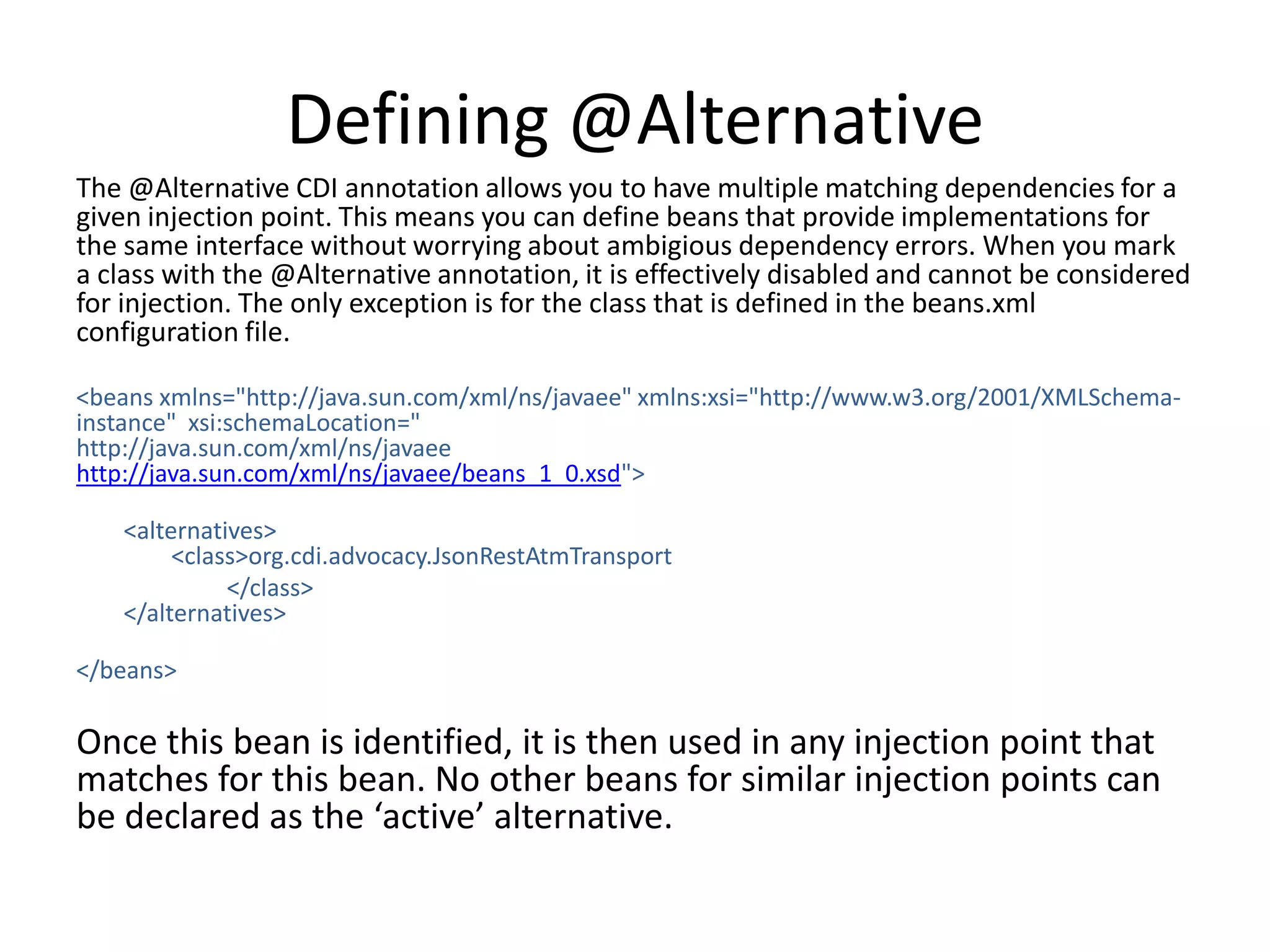
CDI (Contexts and Dependency Injection) is the Java standard for dependency injection and interception. It simplifies and standardizes the API for DI and AOP similar to how JPA did for ORM. CDI uses annotations like @Inject and @Produces to manage dependencies between classes and allows for features like interceptors and decorators. While part of Java EE, CDI can also be used outside of a Java EE container.

![Class uses two qualifiers@SuperFast @StandardFrameRelaySwitchingFlubberpublic class SuperFastAtmTransport implements ATMTransport { public void communicateWithBank(byte[] datapacket) { System.out.println("communicating with bank via the Super Fast transport " ); }}Usage :@Inject @SuperFast @StandardFrameRelaySwitchingFlubberprivate ATMTransport transport;](https://image.slidesharecdn.com/cdi-110803030332-phpapp02/75/J2ee-standards-CDI-11-2048.jpg)